- Table of Contents
-
- H3C S6300 Configuration Examples-6W100
- 01-Login Management Configuration Examples
- 02-RBAC Configuration Examples
- 03-Software Upgrade Configuration Examples
- 04-Software Patching Examples
- 05-ISSU Configuration Examples
- 06-Ethernet Link Aggregation Configuration Examples
- 07-Port Isolation Configuration Examples
- 08-Spanning Tree Configuration Examples
- 09-VLAN Configuration Examples
- 10-VLAN Tagging Configuration Examples
- 11-DHCP Snooping Configuration Examples
- 12-Cross-Subnet Dynamic IP Address Allocation Configuration Examples
- 13-IGMP Snooping Configuration Examples
- 14-MLD Snooping Configuration Examples
- 15-IPv6 Multicast VLAN Configuration Examples
- 16-ACL Configuration Examples
- 17-Control Plane-Based QoS Policy Configuration Examples
- 18-Traffic Policing Configuration Examples
- 19-GTS and Rate Limiting Configuration Examples
- 20-Priority and Queue Scheduling Configuration Examples
- 21-Traffic Filtering Configuration Examples
- 22-AAA Configuration Examples
- 23-Port Security Configuration Examples
- 24-Portal Configuration Examples
- 25-SSH Configuration Examples
- 26-IP Source Guard Configuration Examples
- 27-Ethernet OAM Configuration Examples
- 28-CFD Configuration Examples
- 29-DLDP Configuration Examples
- 30-FCoE Configuration Examples
- 31-NTP Configuration Examples
- 32-PTP Configuration Examples
- 33-SNMP Configuration Examples
- 34-NQA Configuration Examples
- 35-Mirroring Configuration Examples
- 36-sFlow Configuration Examples
- 37-OpenFlow Configuration Examples
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-RBAC Configuration Examples | 255.97 KB |
|
|
|
H3C S6300 Switch Series |
|
RBAC Configuration Examples |
|
|
Copyright © 2020 New H3C Technologies Co., Ltd. All rights reserved.
No part of this manual may be reproduced or transmitted in any form or by any means without prior written consent of New H3C Technologies Co., Ltd.
Except for the trademarks of New H3C Technologies Co., Ltd., any trademarks that may be mentioned in this document are the property of their respective owners.
The information in this document is subject to change without notice.
Example: Assigning access permissions to Telnet user through RADIUS server
Configuration restrictions and guidelines
Example: Changing user access permissions by assigning new user roles
Configuration restrictions and guidelines
Assigning user role role1 to the Telnet users
Verifying the access permissions of user role role1
Assigning user role role2 to Telnet user 1
Example: Assigning ACL and QoS access permissions to Telnet users
Configuration restrictions and guidelines
Introduction
This document provides role based access control (RBAC) examples to control access permissions of login users.
Prerequisites
This document is not restricted to specific software or hardware versions.
The configuration examples in this document were created and verified in a lab environment, and all the devices were started with the factory default configuration. When you are working on a live network, make sure you understand the potential impact of every command on your network.
This document assumes that you have basic knowledge of RBAC.
Example: Assigning access permissions to Telnet user through RADIUS server
Network requirements
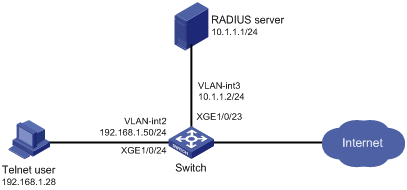
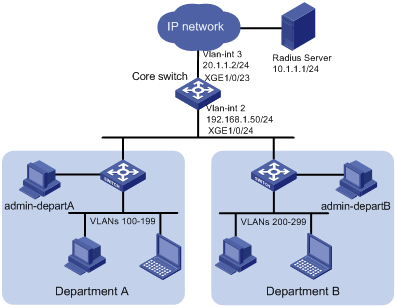
As shown in Figure 1, IMC is the RADIUS server, and the switch uses the RADIUS server to authenticate the Telnet user.
The server assigns the following access permissions to the Telnet user after the user passes authentication:
· Can execute all commands available in ISP domain view.
· Can execute the read and write commands of the ARP and RADIUS features.
· Can create VLANs and execute all commands available in VLAN view.
· Cannot access any VLANs except VLANs 10 to 20.
· Can enter interface view and execute all commands available in interface view.
· Cannot access any interfaces except Ten-GigabitEthernet 1/0/1 to Ten-GigabitEthernet 1/0/3.
Add a user account named telnetuser@bbb on the server for the Telnet user, and specify a password for the account.
Requirements analysis
To meet the network requirements, you must perform the following tasks:
· Add the ARP and RADIUS features to a feature group, so you can manage the features in a centralized manner.
· Create a user role and configure user role rules and resource access policies on the switch, so the user role can have the required access permissions.
· Specify the user role in the Telnet user account on the server, so the server can assign the user role to the Telnet user after the user passes authentication.
Software version used
This configuration example was created and verified on the following product versions:
· S6300-CMW710-R2310.
· IMC PLAT 7.0 (E0202).
· IMC UAM 7.0 (E0202).
Configuration restrictions and guidelines
When you configure RBAC for remote AAA users, follow these guidelines:
· An ISP domain cannot be deleted when it is the default ISP domain. Before you use the undo domain command, change the domain to a non-default ISP domain by using the undo domain default enable command.
· Because RADIUS user authorization information is piggybacked in authentication responses, the authentication and authorization methods must use the same RADIUS scheme.
· You can create multiple rules for a user role. Each rule is uniquely identified by the rule number. A user role can access all commands permitted by the user role rules.
· If two user-defined rules conflict, the rule with the higher number takes effect. For example, the user role can use the tracert command but not the ping command if the user role contains rules configured by using the following commands:
¡ rule 1 permit command ping
¡ rule 2 permit command tracert
¡ rule 3 deny command ping
Configuration procedures
Configuring the switch
1. Configure VLAN settings:
# Create VLAN 2.
<Sysname> system-view
[Sysname] vlan 2
[Sysname-vlan2] quit
# Assign Ten-GigabitEthernet 1/0/24 (the interface connected to the Telnet user) to VLAN 2.
[Sysname] interface ten-gigabitethernet 1/0/24
[Sysname-Ten-GigabitEthernet1/0/24] port access vlan 2
[Sysname-Ten-GigabitEthernet1/0/24] quit
# Assign an IP address to VLAN-interface 2.
[Sysname] interface vlan-interface 2
[Sysname-Vlan-interface2] ip address 192.168.1.50 24
[Sysname-Vlan-interface2] quit
# Create VLAN 3.
[Sysname] vlan 3
[Sysname-vlan3] quit
# Assign Ten-GigabitEthernet 1/0/23 (the interface connected to the RADIUS server) to VLAN 3.
[Sysname] interface ten-gigabitethernet 1/0/23
[Sysname-Ten-GigabitEthernet1/0/23] port access vlan 3
[Sysname-Ten-GigabitEthernet1/0/23] quit
# Assign an IP address to VLAN-interface 3.
[Sysname] interface Vlan-interface 3
[Sysname-Vlan-interface3] ip address 10.1.1.2 24
[Sysname-Vlan-interface3] quit
2. Configure the user login authentication method:
# Enable Telnet server.
[Sysname] telnet server enable
# Enable scheme authentication on user lines VTY 0 through VTY 63.
[Sysname] line vty 0 63
[Sysname-line-vty0-63] authentication-mode scheme
[Sysname-line-vty0-63] quit
3. Configure RADIUS scheme rad:
# Create RADIUS scheme rad and enter RADIUS scheme view.
[Sysname] radius scheme rad
# Specify the primary RADIUS authentication server at 10.1.1.1.
[Sysname-radius-rad] primary authentication 10.1.1.1
# Specify the primary RADIUS accounting server at 10.1.1.1.
[Sysname-radius-rad] primary accounting 10.1.1.1
# Set the authentication shared key to aabbcc in plain text for secure RADIUS communication.
[Sysname-radius-rad] key authentication simple aabbcc
# Set the accounting shared key to aabbcc in plain text for secure RADIUS communication.
[Sysname-radius-rad] key accounting simple aabbcc
[Sysname-radius-rad] quit
4. Configure ISP domain bbb:
# Create ISP domain bbb and enter ISP domain view.
[Sysname] domain bbb
# Configure authentication, authorization, and accounting methods for the login users in the ISP domain.
[Sysname-isp-bbb] authentication login radius-scheme rad
[Sysname-isp-bbb] authorization login radius-scheme rad
[Sysname-isp-bbb] accounting login radius-scheme rad
[Sysname-isp-bbb] quit
5. Configure feature group fgroup1:
# Create feature group fgroup1 and enter feature group view.
[Sysname] role feature-group name fgroup1
# Assign the ARP and RADIUS features to the feature group.
[Sysname-featuregrp-fgroup1] feature arp
[Sysname-featuregrp-fgroup1] feature radius
[Sysname-featuregrp-fgroup1] quit
6. Configure user role role1:
# Create user role role1 and enter user role view.
[Sysname] role name role1
# Configure rule 1 to permit the user role to access all commands in ISP domain view.
[Sysname-role-role1] rule 1 permit command system-view ; domain *
# Configure rule 2 to permit the user role to access all read and write commands of the features in feature group fgroup1.
[Sysname-role-role1] rule 2 permit read write feature-group fgroup1
# Configure rule 3 to permit the user role to create VLANs.
[Sysname-role-role1] rule 3 permit command system-view ; vlan *
# Configure rule 4 to permit the user role to enter interface view and execute all commands available in interface view.
[Sysname-role-role1] rule 4 permit command system-view ; interface *
# Enter user role VLAN policy view, and permit the user role to access only VLANs 10 through 20.
[Sysname-role-role1] vlan policy deny
[Sysname-role-role1-vlanpolicy] permit vlan 10 to 20
[Sysname-role-role1-vlanpolicy] quit
# Enter user role interface policy view, and permit the user role to access only interfaces Ten-GigabitEthernet 1/0/1 through Ten-GigabitEthernet 1/0/3.
[Sysname-role-role1] interface policy deny
[Sysname-role-role1-ifpolicy] permit interface ten-gigabitethernet 1/0/1 to ten-gigabitethernet 1/0/3
[Sysname-role-role1-ifpolicy] quit
[Sysname-role-role1] quit
Configuring the RADIUS server
1. Add the switch to IMC as an access device:
a. Click the User tab.
b. From the navigation tree, select User Access Policy > Access Device Management > Access Device.
c. Click Add.
The Add Access Device page appears.
d. In the Access Configuration area, configure the following parameters, as shown in Figure 2:
- Enter 1812 in the Authentication Port field, and enter 1813 in the Accounting Port field.
- Enter aabbcc in the Shared Key and Confirm Shared Key fields.
- Select Device Management Service from the Service Type list.
- Select H3C(Comware) from the Access Device Type list.
- Use the default values for other parameters.
Figure 2 Adding an access device
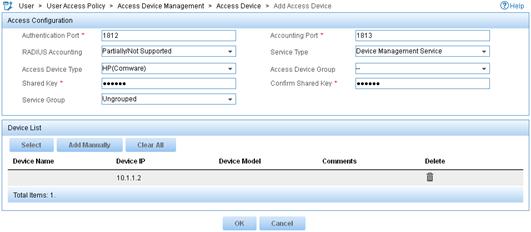
e. In the Device List area, click Select or Add Manually to add the switch (10.1.1.2) to IMC as an access device.
f. Click OK.
2. Add a device management user:
a. Click the User tab.
b. From the navigation tree, select Access User > Device User.
c. Click Add.
The Add Device User page appears.
d. In the Basic Information of Device User area, configure the following parameters, as shown in Figure 3:
- Enter telnetuser@bbb in the Account Name field.
- Enter a password in the User Password and Confirm Password fields.
- Select Telnet from the Service Type list.
- Enter role1 in the Role Name field.
Figure 3 Adding a device management user
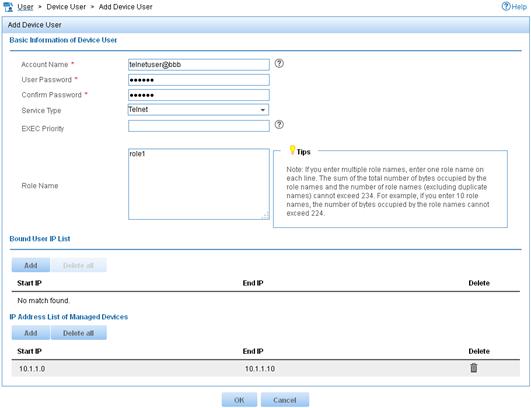
e. In the IP Address List of Managed Devices area, click Add to specify the IP address subnet in the range of 10.1.1.0 to 10.1.1.10.
f. Click OK.
Verifying the configuration
1. Display information about user role role1.
[Sysname] display role name role1
Role: role1
Description:
VLAN policy: deny
Permitted VLANs: 10 to 20
Interface policy: deny
Permitted interfaces: Ten-GigabitEthernet1/0/1 to Ten-GigabitEthernet1/0/3
VPN instance policy: permit (default)
-------------------------------------------------------------------
Rule Perm Type Scope Entity
-------------------------------------------------------------------
1 permit command system-view ; domain *
2 permit RW- feature-group fgroup1
3 permit command system-view ; vlan *
4 permit command system-view ; interface *
R:Read W:Write X:Execute
2. Verify that you can Telnet to the switch.
C:\Documents and Settings\user> telnet 192.168.1.50
******************************************************************************
* Copyright (c) 2010-2014 Hewlett-Packard Development Company,L.P. *
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
******************************************************************************
login: telnetuser@bbb
Password:
<Sysname>
3. Verify that you have the access permissions of user role role1:
# Verify that you can execute all commands available in ISP domain view.
<Sysname> system-view
[Sysname] domain abc
[Sysname-isp-abc] authentication login radius-scheme abc
[Sysname-isp-abc] quit
# Verify that you can execute the read and write commands of the ARP and RADIUS features. For example, configure a RADIUS scheme.
[Sysname] radius scheme rad
[Sysname-radius-rad] primary authentication 2.2.2.2
[Sysname-radius-rad] display radius scheme rad
[Sysname-radius-rad] quit
# Verify that you can access only VLANs 10 to 20. For example, create VLANs 10 and 30.
[Sysname] vlan 10
[Sysname-vlan10] quit
[Sysname] vlan 30
Permission denied.
# Verify that you can access interfaces Ten-GigabitEthernet 1/0/1 to Ten-GigabitEthernet 1/0/3. For example, configure Ten-GigabitEthernet 1/0/1.
[Sysname] interface ten-gigabitethernet 1/0/1
[Sysname-Ten-GigabitEthernet1/0/1] speed auto
[Sysname-Ten-GigabitEthernet1/0/1] quit
# Verify that you cannot access any interface except Ten-GigabitEthernet 1/0/1 to Ten-GigabitEthernet 1/0/3. For example, enter the view of Ten-GigabitEthernet 1/0/6.
[Sysname] interface ten-gigabitethernet 1/0/6
Permission denied.
Configuration files
#
telnet server enable
#
vlan 2 to 3
#
interface Vlan-interface2
ip address 192.168.1.50 255.255.255.0
#
interface Vlan-interface3
ip address 10.1.1.2 255.255.255.0
#
interface Ten-GigabitEthernet1/0/23
port access vlan 3
#
interface Ten-GigabitEthernet1/0/24
port access vlan 2
#
line vty 0 63
authentication-mode scheme
user-role network-operator
#
radius scheme rad
primary authentication 10.1.1.1
primary accounting 10.1.1.1
key authentication cipher $c$3$JzDegvL0G5KZIcJhzscTHLA4WasBVh0UOw==
key accounting cipher $c$3$CdejNYYxvjW0Y+Zydi4rZgBwjYb4h6LKmg==
#
domain bbb
authentication login radius-scheme rad
authorization login radius-scheme rad
accounting login radius-scheme rad
#
role feature-group name fgroup1
feature arp
feature radius
#
role name role1
rule 1 permit command system-view ; domain *
rule 2 permit read write feature-group fgroup1
rule 3 permit command system-view ; vlan *
rule 4 permit command system-view ; interface *
vlan policy deny
permit vlan 10 to 20
interface policy deny
permit interface Ten-GigabitEthernet1/0/1 to Ten-GigabitEthernet1/0/3
#
Example: Changing user access permissions by assigning new user roles
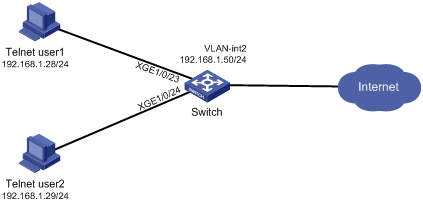
Network requirements
As shown in Figure 4, add two user accounts telnetuser1 and telnetuser2 on the switch for Telnet user 1 and Telnet user 2, respectively. Set both the users' passwords to aabbcc in plain text.
Configure the switch to meet the following requirements:
· The Telnet users are authenticated on the switch in ISP domain bbb.
· User role role1 is assigned to the Telnet users after they pass authentication.
User role role1 has the following access permissions:
· Can execute all commands that start with the display keyword.
· Can create VLANs.
· Can access only VLANs 10 to 15.
· Can access only interface Ten-GigabitEthernet 1/0/1.
Telnet user 1 requires adding the following access permissions:
· Can access VLANs 16 to 20.
· Can access interfaces Ten-GigabitEthernet 1/0/2 to Ten-GigabitEthernet 1/0/3.
Requirements analysis
To meet the network requirements, you must perform the following tasks:
· Create a user role and configure user role rules and resource access policies, so the user role can have the additional access permissions of Telnet user 1.
· Assign the user role to Telnet user 1, so the user can have the additional access permissions at the next login.
Software version used
This configuration example was created and verified on S6300-CMW710-R2310.
Configuration restrictions and guidelines
When you assign another user role to a user, follow these restrictions and guidelines:
· You can create multiple rules for a user role. Each rule is uniquely identified by the rule number. A user role can access all commands permitted by the user role rules.
· If two user-defined rules conflict, the rule with the higher number takes effect. For example, the user role can use the tracert command but not the ping command if the user role contains rules configured by using the following commands:
¡ rule 1 permit command ping
¡ rule 2 permit command tracert
¡ rule 3 deny command ping
· You can assign multiple user roles to a user. The user can use the collection of items and resources accessible to any user role assigned to it.
· If you assign a new user role to a user when the user is online, the assignment does not take effect on the user at the current login. The user obtains the user role the next time it logs in to the switch.
Configuration procedures
Assigning user role role1 to the Telnet users
1. Configure VLAN settings:
# Create VLAN 2.
<Sysname> system-view
[Sysname] vlan 2
[Sysname-vlan2] quit
# Assign interfaces Ten-GigabitEthernet 1/0/23 and Ten-GigabitEthernet 1/0/24 (the interfaces connected to the Telnet users) to VLAN 2.
[Sysname] interface ten-gigabitethernet 1/0/23
[Sysname-Ten-GigabitEthernet1/0/23] port access vlan 2
[Sysname-Ten-GigabitEthernet1/0/23] quit
[Sysname] interface ten-gigabitethernet 1/0/24
[Sysname-Ten-GigabitEthernet1/0/24] port access vlan 2
[Sysname-Ten-GigabitEthernet1/0/24] quit
# Assign an IP address to VLAN-interface 2.
[Sysname] interface vlan-interface 2
[Sysname-Vlan-interface2] ip address 192.168.1.50 24
[Sysname-Vlan-interface2] quit
2. Configure the user login authentication method:
# Enable Telnet server.
[Sysname] telnet server enable
# Enable scheme authentication on user lines VTY 0 through VTY 63.
[Sysname] line vty 0 63
[Sysname-line-vty0-63] authentication-mode scheme
[Sysname-line-vty0-63] quit
3. Configure ISP domain bbb:
# Create ISP domain bbb and enter ISP domain view.
[Sysname] domain bbb
# Configure the authentication and authorization methods for the login users in the ISP domain.
[Sysname-isp-bbb] authentication login local
[Sysname-isp-bbb] authorization login local
[Sysname-isp-bbb] quit
4. Configure device management users telnetuser1 and telnetuser2:
# Create device management user telnetuser1 and enter local user view.
[Sysname] local-user telnetuser1 class manage
# Set the password to aabbcc in plain text.
[Sysname-luser-manage-telnetuser1] password simple aabbcc
# Specify the service type as Telnet.
[Sysname-luser-manage-telnetuser1] service-type telnet
[Sysname-luser-manage-telnetuser1] quit
# Create device management user telnetuser2 and enter local user view.
[Sysname] local-user telnetuser2 class manage
# Set the password to aabbcc in plain text.
[Sysname-luser-manage-telnetuser2] password simple aabbcc
# Specify the service type as Telnet.
[Sysname-luser-manage-telnetuser2] service-type telnet
[Sysname-luser-manage-telnetuser2] quit
5. Configure user role role1:
# Create user role role1 and enter user role view.
[Sysname] role name role1
# Configure rule 1 to permit the user role to access all commands that start with the display keyword.
[Sysname-role-role1] rule 1 permit command display *
# Configure rule 2 to permit the user role to access VLAN view.
[Sysname-role-role1] rule 2 permit command system-view ; vlan *
# Configure rule 3 to permit the user role to enter interface view and execute all commands available in interface view.
[Sysname-role-role1] rule 3 permit command system-view ; interface *
# Enter user role VLAN policy view, and allow the user role to access only VLANs 10 to 15.
[Sysname-role-role1] vlan policy deny
[Sysname-role-role1-vlanpolicy] permit vlan 10 to 15
[Sysname-role-role1-vlanpolicy] quit
# Enter user role interface policy view, and allow the user role to access only interface Ten-GigabitEthernet 1/0/1.
[Sysname-role-role1] interface policy deny
[Sysname-role-role1-ifpolicy] permit interface ten-gigabitethernet 1/0/1
[Sysname-role-role1-ifpolicy] quit
[Sysname-role-role1] quit
6. Authorize user role role1 to the device management users:
# Enter the view of telnetuser1.
[Sysname] local-user telnetuser1 class manage
# Assign user role role1 to telnetuser1.
[Sysname-luser-manage-telnetuser1] authorization-attribute user-role role1
# Remove the default user role network-operator from telnetuser1.
[Sysname-luser-manage-telnetuser1] undo authorization-attribute user-role network-operator
[Sysname-luser-manage-telnetuser1] quit
# Enter the view of telnetuser2.
[Sysname] local-user telnetuser2 class manage
# Assign user role role1 to telnetuser2.
[Sysname-luser-manage-telnetuser2] authorization-attribute user-role role1
# Remove the default user role network-operator from telnetuser2.
[Sysname-luser-manage-telnetuser2] undo authorization-attribute user-role network-operator
[Sysname-luser-manage-telnetuser2] quit
Verifying the access permissions of user role role1
1. Display information about user role role1.
[Sysname] display role name role1
Role: role1
Description:
VLAN policy: deny
Permitted VLANs: 10 to 15
Interface policy: deny
Permitted interfaces: Ten-GigabitEthernet1/0/1
VPN instance policy: permit (default)
-------------------------------------------------------------------
Rule Perm Type Scope Entity
-------------------------------------------------------------------
1 permit command display *
2 permit command system-view ; vlan *
3 permit command system-view ; interface *
R:Read W:Write X:Execute
2. Verify that you can Telnet to the switch. This example uses the user account telnetuser1@bbb.
C:\Documents and Settings\user> telnet 192.168.1.50
******************************************************************************
* Copyright (c) 2010-2014 Hewlett-Packard Development Company,L.P. *
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
******************************************************************************
login: telnetuser1@bbb
Password:
<Sysname>
3. Verify that you have the access permissions of user role role1:
# Verify that you can configure VLANs 10 to 15. For example, create VLAN 15.
<Sysname> system-view
[Sysname] vlan 15
[Sysname-vlan15] quit
# Verify that you cannot access any other VLAN except VLANs 10 to 15. For example, create VLAN 20.
[Sysname] vlan 20
Permission denied.
# Verify that you can access interface Ten-GigabitEthernet 1/0/1.
[Sysname] interface ten-gigabitethernet 1/0/1
[Sysname-Ten-GigabitEthernet1/0/1] speed auto
[Sysname-Ten-GigabitEthernet1/0/1] quit
Assigning user role role2 to Telnet user 1
1. Configure user role role2:
# Create user role role2 and enter user role view.
[Sysname] role name role2
# Configure rule 1 to permit the user role to enter interface view and execute all commands available in interface view.
[Sysname-role-role2] rule 1 permit command system-view ; interface *
# Enter user role VLAN policy view, and allow the user role to access only VLANs 16 to 20.
[Sysname-role-role2] vlan policy deny
[Sysname-role-role2-vlanpolicy] permit vlan 16 to 20
[Sysname-role-role2-vlanpolicy] quit
# Enter user role interface policy view, and allow the user role to access only interfaces Ten-GigabitEthernet 1/0/2 to Ten-GigabitEthernet 1/0/3.
[Sysname-role-role2] interface policy deny
[Sysname-role-role2-ifpolicy] permit interface ten-gigabitethernet 1/0/2 to ten-gigabitethernet 1/0/3
[Sysname-role-role2-ifpolicy] quit
[Sysname-role-role2] quit
2. Authorize user role role2 to telnetuser1:
# Enter the view of telnetuser1.
[Sysname] local-user telnetuser1 class manage
# Assign user role role2 to telnetuser1.
[Sysname-luser-manage-telnetuser1] authorization-attribute user-role role2
[Sysname-luser-manage-telnetuser1] quit
Verifying the configuration
1. Display information about user role role2.
[Sysname] display role name role2
Role: role2
Description:
VLAN policy: deny
Permitted VLANs: 16 to 20
Interface policy: deny
Permitted interfaces: Ten-GigabitEthernet1/0/2 to Ten-GigabitEthernet1/0/3
VPN instance policy: permit (default)
-------------------------------------------------------------------
Rule Perm Type Scope Entity
-------------------------------------------------------------------
1 permit command system-view ; interface *
R:Read W:Write X:Execute
2. Verify that you can Telnet to the switch.
C:\Documents and Settings\user> telnet 192.168.1.50
******************************************************************************
* Copyright (c) 2010-2014 Hewlett-Packard Development Company,L.P. *
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
******************************************************************************
login: telnetuser1@bbb
Password:
<Sysname>
3. Verify that you have the access permissions of user role role2:
# Verify that you can access VLANs 16 to 20. For example, create VLAN 16.
<Sysname> system-view
[Sysname] vlan 16
[Sysname-vlan16] quit
# Verify that you can access interfaces Ten-GigabitEthernet 1/0/2 and Ten-GigabitEthernet 1/0/3. For example, configure Ten-GigabitEthernet 1/0/2.
[Sysname] interface ten-gigabitethernet 1/0/2
[Sysname-Ten-GigabitEthernet1/0/2] speed auto
[Sysname-Ten-GigabitEthernet1/0/2] quit
# Verify that you cannot access any other interface except interfaces Ten-GigabitEthernet 1/0/1 to Ten-GigabitEthernet 1/0/3. For example, enter the view of Ten-GigabitEthernet 1/0/5.
[Sysname] interface ten-gigabitethernet 1/0/5
Permission denied.
Configuration files
#
telnet server enable
#
vlan 2
#
interface Vlan-interface2
ip address 192.168.1.50 255.255.255.0
#
interface Ten-GigabitEthernet1/0/23
port access vlan 2
#
interface Ten-GigabitEthernet1/0/24
port access vlan 2
#
line vty 0 63
authentication-mode scheme
user-role network-operator
#
domain bbb
authentication login local
authorization login local
#
role name role1
rule 1 permit command display *
rule 2 permit command system-view ; vlan *
rule 3 permit command system-view ; interface *
vlan policy deny
permit vlan 10 to 15
interface policy deny
permit interface Ten-GigabitEthernet1/0/1
#
role name role2
rule 1 permit command system-view ; interface *
vlan policy deny
permit vlan 16 to 20
interface policy deny
permit interface Ten-GigabitEthernet1/0/2 to Ten-GigabitEthernet1/0/3
#
local-user telnetuser1 class manage
password hash $h$6$kZw1rKFsAY4lhgUz$+teVLy8gmKN4Mr00VWgXQTB8ai94gKHlrys5OkytGf4
kT+nz5X1ZGASjc282CYAR6A1upH2jbmRoTcfDzZ9Gmw==
service-type telnet
authorization-attribute user-role role1
authorization-attribute user-role role2
#
local-user telnetuser2 class manage
password hash TPcgyTQJZShe$h$6$vaSj2xKc8yFiNdfQ$Jzb3PXo2lt4jk KSZqJUVhjP634Wol/
Qx8TLU748IHoeui0w5n/XRzpNqbNnpxikym39gGJCwYw==
service-type telnet
authorization-attribute user-role role1
#
Example: Assigning ACL and QoS access permissions to Telnet users
Network requirements
As shown in Figure 5, the core switch is an H3C S6300 switch, and IMC is the RADIUS server. Users in Department A are in VLANs 100 to 199, and users in Department B are in VLANs 200 to 299. Users in the two departments cannot reach each other at Layer 2.
Add Telnet user accounts admin-departA@bbb and admin-departB@bbb on the RADIUS server for the network administrators in Department A and Department B, respectively.
The core switch uses the RADIUS server to authenticate the network administrators in ISP domain bbb.
The server authorizes the following access permissions to admin-departA after it passes authentication:
· Can access all commands of the ACL and QoS features.
· Cannot access any interface.
· Can access only VLANs 100 to 199.
The server authorizes the following access permissions to admin-departB after it passes authentication:
· Can access all commands of the ACL and QoS features.
· Cannot access any interface.
· Can access only VLANs 200 to 299.
Requirements analysis
To meet the network requirements, you must perform the following tasks:
· Create a user role and configure user role rules and resource access policies on the core switch for each administrator, so the user roles can have the required access permissions.
· Specify the correct user role in each Telnet user account on the server, so the server can assign the correct user role to each administrator.
Software version used
This configuration example was created and verified on the following product versions:
· S6300-CMW710-R2310.
· IMC PLAT 7.0 (E0202).
· IMC UAM 7.0 (E0202).
Configuration restrictions and guidelines
Because RADIUS user authorization information is piggybacked in authentication responses, the authentication and authorization methods must use the same RADIUS scheme.
Configuration procedures
Configuring the core switch
1. Configure VLAN settings:
# Create VLAN 2.
<Sysname> system-view
[Sysname] vlan 2
[Sysname-vlan2] quit
# Assign Ten-GigabitEthernet 1/0/24 (the interface connected to the Telnet users) to VLAN 2.
[Sysname] interface ten-gigabitethernet 1/0/24
[Sysname-Ten-GigabitEthernet1/0/24] port access vlan 2
[Sysname-Ten-GigabitEthernet1/0/24] quit
# Assign an IP address to VLAN-interface 2.
[Sysname] interface vlan-interface 2
[Sysname-Vlan-interface2] ip address 192.168.1.50 24
[Sysname-Vlan-interface2] quit
# Create VLAN 3.
[Sysname] vlan 3
[Sysname-vlan3] quit
# Assign Ten-GigabitEthernet 1/0/23 (the interface connected to the RADIUS server) to VLAN 3.
[Sysname] interface ten-gigabitethernet 1/0/23
[Sysname-Ten-GigabitEthernet1/0/23] port access vlan 3
[Sysname-Ten-GigabitEthernet1/0/23] quit
# Assign an IP address to VLAN-interface 3.
[Sysname] interface vlan-interface 3
[Sysname-Vlan-interface3] ip address 20.1.1.2 24
[Sysname-Vlan-interface3] quit
2. Configure the user login authentication method:
# Enable Telnet server.
[Sysname] telnet server enable
# Enable scheme authentication on user lines VTY 0 through VTY 63.
[Sysname] line vty 0 63
[Sysname-line-vty0-63] authentication-mode scheme
[Sysname-line-vty0-63] quit
3. Configure RADIUS scheme rad:
# Create RADIUS scheme rad and enter RADIUS scheme view.
[Sysname] radius scheme rad
# Specify the primary RADIUS authentication server at 10.1.1.1.
[Sysname-radius-rad] primary authentication 10.1.1.1
# Specify the primary RADIUS accounting server at 10.1.1.1.
[Sysname-radius-rad] primary accounting 10.1.1.1
# Set the authentication shared key to aabbcc in plain text for secure RADIUS communication.
[Sysname-radius-rad] key authentication simple aabbcc
# Set the accounting shared key to aabbcc in plain text for secure RADIUS communication.
[Sysname-radius-rad] key accounting simple aabbcc
[Sysname-radius-rad] quit
4. Configure ISP domain bbb:
# Create ISP domain bbb and enter ISP domain view.
[Sysname] domain bbb
# Configure authentication, authorization, and accounting methods for the login users in the ISP domain.
[Sysname-isp-bbb] authentication login radius-scheme rad
[Sysname-isp-bbb] authorization login radius-scheme rad
[Sysname-isp-bbb] accounting login radius-scheme rad
[Sysname-isp-bbb] quit
5. Configure user role departA-resource:
# Create user role departA-resource and enter user role view.
[Sysname] role name departA-resource
# Configure rule 1 to permit the user role to access all commands of the QoS feature.
[Sysname-role-departA-resource] rule 1 permit read write execute feature qos
# Configure rule 2 to permit the user role to access all commands of the ACL feature.
[Sysname-role-departA-resource] rule 2 permit read write execute feature acl
# Enter user role VLAN policy view, and permit the user role to access only VLANs 100 to 199.
[Sysname-role-departA-resource] vlan policy deny
[Sysname-role-departA-resource-vlanpolicy] permit vlan 100 to 199
[Sysname-role-departA-resource-vlanpolicy] quit
6. Configure user role departB-resource:
# Create user role departB-resource and enter user role view.
[Sysname] role name departB-resource
# Configure rule 1 to permit the user role to access all commands of the QoS feature.
[Sysname-role-departB-resource] rule 1 permit read write execute feature qos
# Configure rule 2 to permit the user role to access all commands of the ACL feature.
[Sysname-role-departB-resource] rule 2 permit read write execute feature acl
# Enter user role VLAN policy view, and permit the user role to access only VLANs 200 to 299.
[Sysname-role-departB-resource] vlan policy deny
[Sysname-role-departB-resource-vlanpolicy] permit vlan 200 to 299
[Sysname-role-departB-resource-vlanpolicy] quit
Configuring the RADIUS server
1. Add the core switch to IMC as an access device:
a. Click the User tab.
b. From the navigation tree, select User Access Policy > Access Device Management > Access Device.
c. Click Add.
The Add Access Device page appears.
d. In the Access Configuration area, configure the following parameters:
- Enter 1812 in the Authentication Port field, and enter 1813 in the Accounting Port field.
- Enter aabbcc in the Shared Key and Confirm Shared Key fields.
- Select Device Management Service from the Service Type list.
- Select H3C(General) from the Access Device Type list.
- Use the default values for other parameters.
e. In the Device List area, click Select or Add Manually to add the core switch (20.1.1.2) to IMC as an access device.
f. Click OK.
2. Add a device management user:
a. Click the User tab.
b. From the navigation tree, select Access User > Device User.
c. Click Add.
The Add Device User page appears.
d. In the Basic Information of Device User area, configure the following parameters, as shown in Figure 6:
- Enter admin-departA@bbb in the Account Name field.
- Enter a password in the User Password and Confirm Password fields.
- Select Telnet from the Service Type list.
- Enter departA-resource in the Role Name field.
Figure 6 Adding a device management user
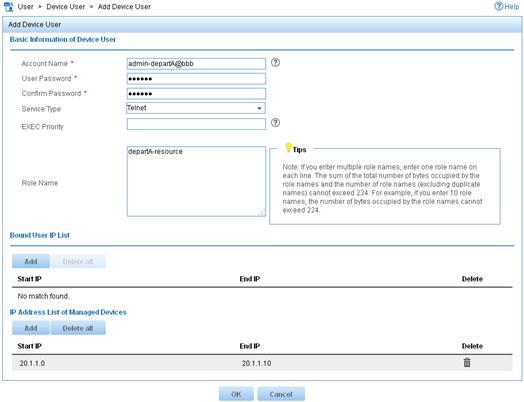
e. In the IP Address List of Managed Devices area, click Add to specify the IP address subnet in the range of 20.1.1.0 to 20.1.1.10.
f. Click OK.
The device user list displays the added user.
g. Click Add.
The Add Device User page appears.
h. In the Basic Information of Device User area, configure the following parameters, as shown in Figure 7:
- Enter admin-departB@bbb in the Account Name field.
- Enter a password in the User Password and Confirm Password fields.
- Select Telnet from the Service Type list.
- Enter departB-resource in the Role Name field.
Figure 7 Adding a device management user
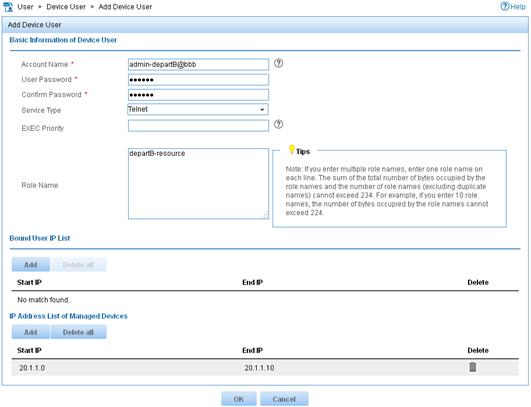
i. In the IP Address List of Managed Devices area, click Add to specify the IP address subnet in the range of 20.1.1.0 to 20.1.1.10.
j. Click OK.
Verifying the configuration
1. Verify that the user roles are correctly configured:
# Display information about user role departA-resource.
[Sysname] display role name departA-resource
Role: departA-resource
Description:
VLAN policy: deny
Permitted VLANs: 100 to 199
Interface policy: deny
VPN instance policy: permit (default)
-------------------------------------------------------------------
Rule Perm Type Scope Entity
-------------------------------------------------------------------
1 permit RWX feature qos
2 permit RWX feature acl
R:Read W:Write X:Execute
# Display information about user role departB-resource.
[Sysname] display role name departB-resource
Role: departB-resource
Description:
VLAN policy: deny
Permitted VLANs: 200 to 299
Interface policy: deny
VPN instance policy: permit (default)
-------------------------------------------------------------------
Rule Perm Type Scope Entity
-------------------------------------------------------------------
1 permit RWX feature qos
2 permit RWX feature acl
R:Read W:Write X:Execute
2. Verify that you can Telnet to the core switch by using the account admin-departA@bbb from Department A:
C:\Documents and Settings\user> telnet 192.168.1.50
******************************************************************************
* Copyright (c) 2010-2014 Hewlett-Packard Development Company,L.P. *
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
******************************************************************************
login: admin-departA@bbb
Password:
<Sysname>
3. Verify that you have the access permission of user role departA-resource:
a. Verify that you can use all commands of the QoS and ACL features:
# Create IPv4 advanced ACL 3000 and enter ACL view.
<Sysname> system-view
[Sysname] acl number 3000
# Create an IPv4 advanced ACL rule to permit outbound FTP packets.
[Sysname-acl-adv-3000] rule permit tcp destination-port eq ftp-data
[Sysname-acl-adv-3000] quit
# Create traffic class 1 and enter traffic class view.
[Sysname] traffic classifier 1
# Define a match criterion for traffic class 1 to match the advanced ACL 3000.
[Sysname-classifier-1] if-match acl 3000
[Sysname-classifier-1] quit
# Create traffic behavior 1 and enter traffic behavior view.
[Sysname] traffic behavior 1
# Set the CIR of the CAR action to 2000 kbps.
[Sysname-behavior-1] car cir 2000
[Sysname-behavior-1] quit
# Create QoS policy 1, and associate traffic class 1 with traffic behavior 1 in the QoS policy.
[Sysname] qos policy 1
[Sysname-qospolicy-1] classifier 1 behavior 1
[Sysname-qospolicy-1] quit
b. Verify that you can access VLANs 100 through 199. For example, apply QoS policy 1 to the incoming traffic of VLANs 100 through 107.
[Sysname] qos vlan-policy 1 vlan 100 to 107 inbound
c. Verify that you cannot access any other VLANs except VLANs 100 through 199. For example, apply QoS policy 1 to the incoming traffic of VLANs 200 through 207.
[Sysname] qos vlan-policy 1 vlan 200 to 207 inbound
Permission denied.
4. Verify that you can Telnet to the core switch by using the account admin-departB@bbb from Department B. (Details not shown.)
5. Verify that you have the access permission of user role departB-resource:
a. Verify that you can use all commands of the QoS and ACL features:
# Create IPv4 advanced ACL 3001 and enter ACL view.
<Sysname> system-view
[Sysname] acl number 3001
# Create an IPv4 advanced ACL rule to permit outbound FTP packets.
[Sysname-acl-adv-3001] rule permit tcp destination-port eq ftp-data
[Sysname-acl-adv-3001] quit
# Create traffic class 2 and enter traffic class view.
[Sysname] traffic classifier 2
# Define a match criterion for traffic class 2 to match the advanced ACL 3001.
[Sysname-classifier-2] if-match acl 3001
[Sysname-classifier-2] quit
# Create traffic behavior 2 and enter traffic behavior view.
[Sysname] traffic behavior 2
# Set the CIR of the CAR action to 2000 kbps.
[Sysname-behavior-2] car cir 2000
[Sysname-behavior-2] quit
# Create QoS policy 2, and associate traffic class 2 with traffic behavior 2 in the QoS policy.
[Sysname] qos policy 2
[Sysname-qospolicy-2] classifier 2 behavior 2
[Sysname-qospolicy-2] quit
b. Verify that you can access VLANs 200 through 299. For example, apply QoS policy 2 to the incoming traffic of VLANs 200 through 207.
[Sysname] qos vlan-policy 2 vlan 200 to 207 inbound
c. Verify that you cannot access any other VLANs except VLANs 200 through 299. For example, apply QoS policy 2 to the incoming traffic of VLANs 100 through 107.
[Sysname] qos vlan-policy 2 vlan 100 to 107 inbound
Permission denied.
Configuration files
#
telnet server enable
#
vlan 2 to 3
#
interface Vlan-interface2
ip address 192.168.1.50 255.255.255.0
#
interface Vlan-interface3
ip address 20.1.1.2 255.255.255.0
#
interface Ten-GigabitEthernet1/0/23
port access vlan 3
#
interface Ten-GigabitEthernet1/0/24
port access vlan 2
#
line vty 0 63
authentication-mode scheme
user-role network-operator
#
radius scheme rad
primary authentication 10.1.1.1
primary accounting 10.1.1.1
key authentication cipher $c$3$JzDegvL0G5KZIcJhzscTHLA4WasBVh0UOw==
key accounting cipher $c$3$CdejNYYxvjW0Y+Zydi4rZgBwjYb4h6LKmg==
#
domain bbb
authentication login radius-scheme rad
authorization login radius-scheme rad
accounting login radius-scheme rad
#
role name departA-resource
rule 1 permit read write execute feature qos
rule 2 permit read write execute feature acl
vlan policy deny
permit vlan 100 to 199
interface policy deny
#
role name departB-resource
rule 1 permit read write execute feature qos
rule 2 permit read write execute feature acl
vlan policy deny
permit vlan 200 to 299
interface policy deny
#
Related documentation
· H3C S6300 Switch Series Fundamentals Configuration Guide-Release 23xx
· H3C S6300 Switch Series Fundamentals Command Reference-Release 23xx
