- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-EVPN VXLAN configuration | 1.21 MB |
Restrictions: Hardware compatibility with EVPN VXLAN
Assignment of traffic to VXLANs
Traffic from the local site to a remote site
Traffic from a remote site to the local site
Centralized EVPN gateway deployment
Distributed EVPN gateway deployment
About distributed EVPN gateway deployment
Hardware compatibility with EVPN multihoming
Hardware compatibility with EVPN multicast
Multicast in single-homed sites
VM reachability information synchronization
Independent BGP neighbor relationship establishment
Restrictions: Hardware compatibility with EVPN gateways
Restrictions and guidelines: EVPN VXLAN configuration
Setting the VXLAN hardware resource mode
Restrictions and guidelines for VXLAN configuration on a VSI
About EVPN instance configuration
Restrictions and guidelines for EVPN instance configuration
Configuring an EVPN instance created in system view
Configuring an EVPN instance created in VSI view
Restrictions and guidelines for EVPN multihoming
Hardware compatibility with EVPN multihoming
Assigning an ESI to an interface
Configuring FRR for EVPN VXLAN
Disabling advertisement of EVPN multihoming routes
Configuring BGP to advertise BGP EVPN routes
Restrictions and guidelines for BGP EVPN route advertisement
Enabling BGP to advertise BGP EVPN routes
Configuring BGP EVPN route settings
Enabling the device to ignore default routes in route recursion
Mapping a static Ethernet service instance to a VSI
Mapping dynamic Ethernet service instances to VSIs
Configuring a centralized EVPN gateway
Restrictions and guidelines for centralized EVPN gateway configuration
Prerequisites for centralized EVPN gateway configuration
Configuring a centralized gateway interface
Setting the static flag for the MAC addresses of centralized gateway interfaces
Configuring a distributed EVPN gateway
Restrictions and guidelines for distributed EVPN gateway configuration
Prerequisites for distributed EVPN gateway configuration
Configuring the traffic forwarding mode for EVPN VXLAN
Configuring an L3 VXLAN ID for a VSI interface
Configuring IP prefix route advertisement
Configuring BGP route exchange between the public instance and VPN instances
Configuring the EVPN global MAC address
Disabling generation of IP prefix advertisement routes for the subnets of a VSI interface
Enabling a distributed EVPN gateway to send RA messages over VXLAN tunnels
Enabling traffic statistics for the VSIs automatically created for L3 VXLAN IDs
Managing remote MAC address entries and remote ARP or ND learning
Disabling remote MAC address learning and remote ARP or ND learning
Disabling MAC address advertisement
Enabling MAC mobility event suppression
Disabling learning of MAC addresses from ARP or ND information
Disabling ARP information advertisement
Enabling ND information advertisement
Enabling ARP mobility event suppression
Enabling ND mobility event suppression
Enabling conversational learning for forwarding entries
About conversational learning for forwarding entries
Restrictions and guidelines for enabling conversational learning for forwarding entries
Enabling conversational learning for remote MAC address entries
Enabling conversational learning for host route FIB entries
Configuring BGP EVPN route redistribution and advertisement
Redistributing MAC/IP advertisement routes into BGP unicast routing tables
Setting the metric of BGP EVPN routes added to a VPN instance's routing table
Enabling BGP EVPN route advertisement to the local site
Enabling ARP or ND flood suppression
Enabling packet statistics for VXLAN tunnels
Testing the connectivity of a VXLAN tunnel
Pinging a VXLAN tunnel destination
Tracing the path to a VXLAN tunnel destination
Enabling SNMP notifications for EVPN
Display and maintenance commands for EVPN
EVPN VXLAN configuration examples
Example: Configuring a centralized EVPN gateway
Example: Configuring distributed EVPN gateways in symmetric IRB mode (IPv4 underlay network)
Example: Configuring distributed EVPN gateways in symmetric IRB mode (IPv6 underlay network)
Example: Configuring distributed IPv4 EVPN gateways in asymmetric IRB mode
Example: Configuring communication between EVPN networks and the public network
Example: Configuring IPv4 EVPN M-LAG with a direct peer link
Example: Configuring IPv4 EVPN M-LAG with a tunnel peer link
Example: Configuring IPv4 EVPN multihoming
Example: Configuring EVPN multicast
EVPN VXLAN overview
EVPN VXLAN uses EVPN routes for automatic VXLAN tunnel establishment and assignment and MAC reachability information advertisement in the control plane and uses VXLAN for forwarding in the data plane.
Restrictions: Hardware compatibility with EVPN VXLAN
EVPN multihoming, EVPN gateways, and EVPN-DCI are not supported by S6800 switches labeled with the following product codes:
· LS-6800-2C.
· LS-6800-32Q.
· LS-6800-4C.
Network model
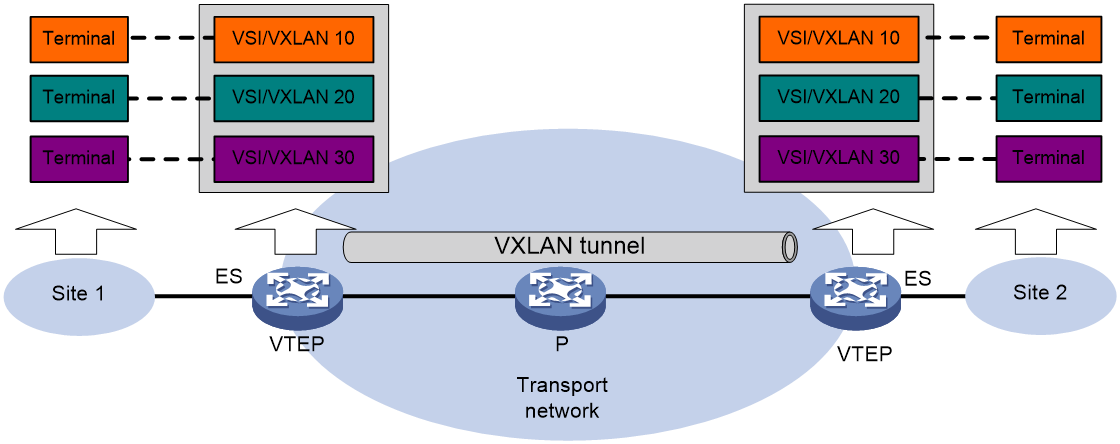
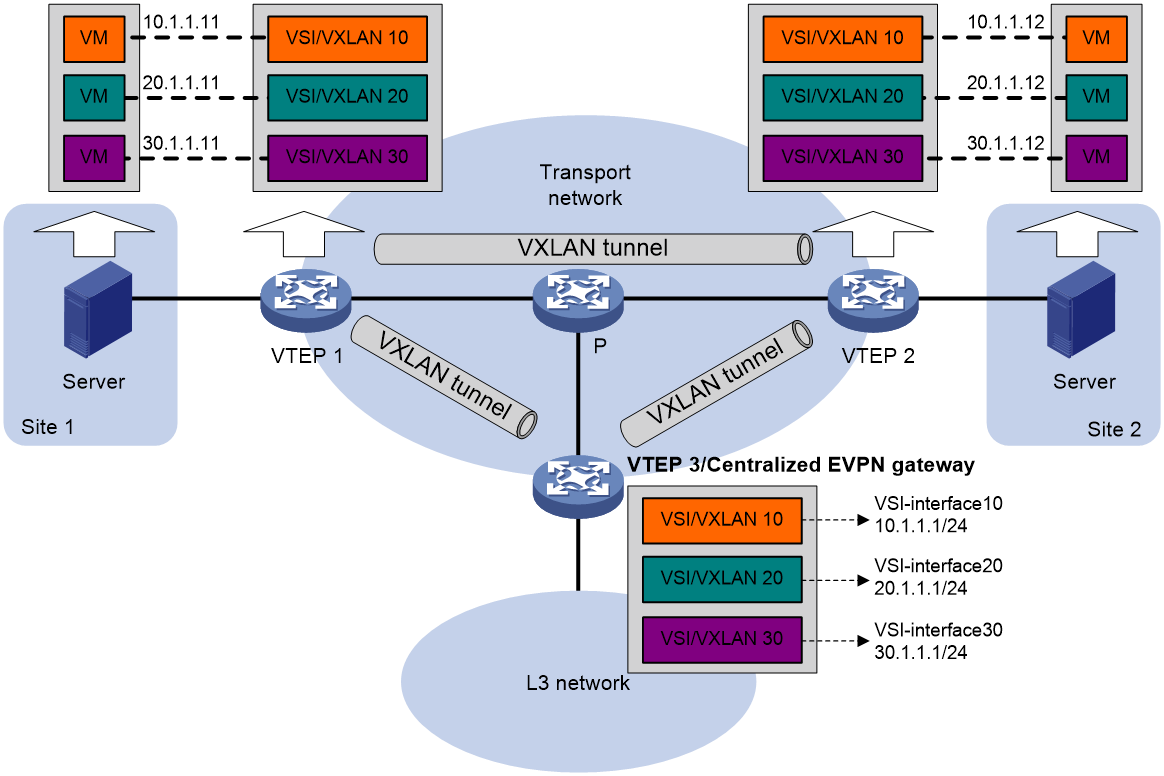
As shown in Figure 1, EVPN uses the VXLAN technology for traffic forwarding in the data plane. The transport edge devices assign user terminals to different VXLANs, and then forward traffic between sites for user terminals by using VXLAN tunnels. The transport edge devices are VXLAN tunnel endpoints (VTEPs).
Supported user terminals include PCs and VMs on servers.
|
|
NOTE: This document uses VMs as examples to describe the mechanisms of EVPN. The mechanisms do not differ between different kinds of user terminals. |
A VTEP uses ESs, VSIs, and VXLAN tunnels to provide VXLAN services:
· Ethernet segment (ES)—An ES is a link that connects a site to a VTEP. Each ES is uniquely identified by an Ethernet segment identifier (ESI).
· VSI—A virtual switch instance is a virtual Layer 2 switched domain. Each VSI provides switching services only for one VXLAN. VSIs learn MAC addresses and forward frames independently of one another. User terminals in different sites have Layer 2 connectivity if they are in the same VXLAN. A VXLAN is identified by a 24-bit VXLAN ID which is also called the virtual network identifier (VNI). A VXLAN corresponds to an EVPN instance.
· VXLAN tunnel—Logical point-to-point tunnels between VTEPs over the transport network. Each VXLAN tunnel can trunk multiple VXLANs.
All VXLAN processing is performed on VTEPs. The ingress VTEP encapsulates VXLAN traffic in the VXLAN, outer UDP, and outer IP headers, and forwards the traffic through VXLAN tunnels. The egress VTEP removes the VXLAN encapsulation and forwards the traffic to the destination. Transport network devices (for example, the P device in Figure 1) forward VXLAN traffic only based on the outer IP header of VXLAN packets.
Configuration automation
If EVPN is used for Layer 2 forwarding, VTEPs use the following BGP EVPN routes to discover VTEP neighbors, establish VXLAN tunnels, and assign the tunnels to VXLANs:
· IMET route—VTEPs advertise the VXLAN IDs they have through IMET routes. If two VTEPs have the same VXLAN ID, they automatically establish a VXLAN tunnel and assign the tunnel to the VXLAN.
· MAC/IP advertisement route—VTEPs advertise local MAC addresses and VXLAN IDs through MAC/IP advertisement routes. If two VTEPs have the same VXLAN ID, they automatically establish a VXLAN tunnel and assign the tunnel to the VXLAN.
If EVPN is used for Layer 3 forwarding, VTEPs use the following BGP EVPN routes to discover VTEP neighbors, establish VXLAN tunnels, and assign the tunnels to VXLANs:
· IMET route—VTEPs advertise the VXLAN IDs they have through IMET routes. If two VTEPs have the same VXLAN ID, they automatically establish a VXLAN tunnel and assign the tunnel to the VXLAN.
· MAC/IP advertisement route and IP prefix advertisement route—In the EVPN gateway deployment, VTEPs advertise MAC/IP advertisement routes or IP prefix advertisement routes with the export targets. When a VTEP receives a route, it compares the export targets of the route with the local import targets. If the route targets match, the VTEP establishes a VXLAN tunnel with the remote VTEP and associates the tunnel with the L3 VXLAN ID of the corresponding VPN instance. For more information about the L3 VXLAN ID, see "Distributed EVPN gateway deployment."
Assignment of traffic to VXLANs
Traffic from the local site to a remote site
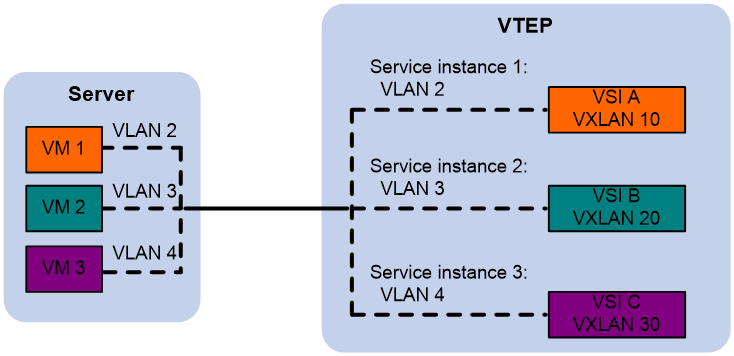
The VTEP uses an Ethernet service instance to match customer traffic on a site-facing interface. The VTEP assigns customer traffic to a VXLAN by mapping the Ethernet service instance to a VSI.
An Ethernet service instance is identical to an attachment circuit (AC) in L2VPN. An Ethernet service instance matches a list of VLANs on a Layer 2 Ethernet interface by using a frame match criterion. The frame match criterion specifies the characteristics of traffic from the VLANs, such as tagging status and VLAN IDs.
As shown in Figure 2, Ethernet service instance 1 matches VLAN 2 and is mapped to VSI A (VXLAN 10). When a frame from VLAN 2 arrives, the VTEP assigns the frame to VXLAN 10, and looks up VSI A's MAC address table for the outgoing interface.
Figure 2 Identifying traffic from the local site
Traffic from a remote site to the local site
When a VXLAN packet arrives at a VXLAN tunnel interface, the VTEP uses the VXLAN ID in the packet to identify its VXLAN.
Layer 2 forwarding
MAC learning
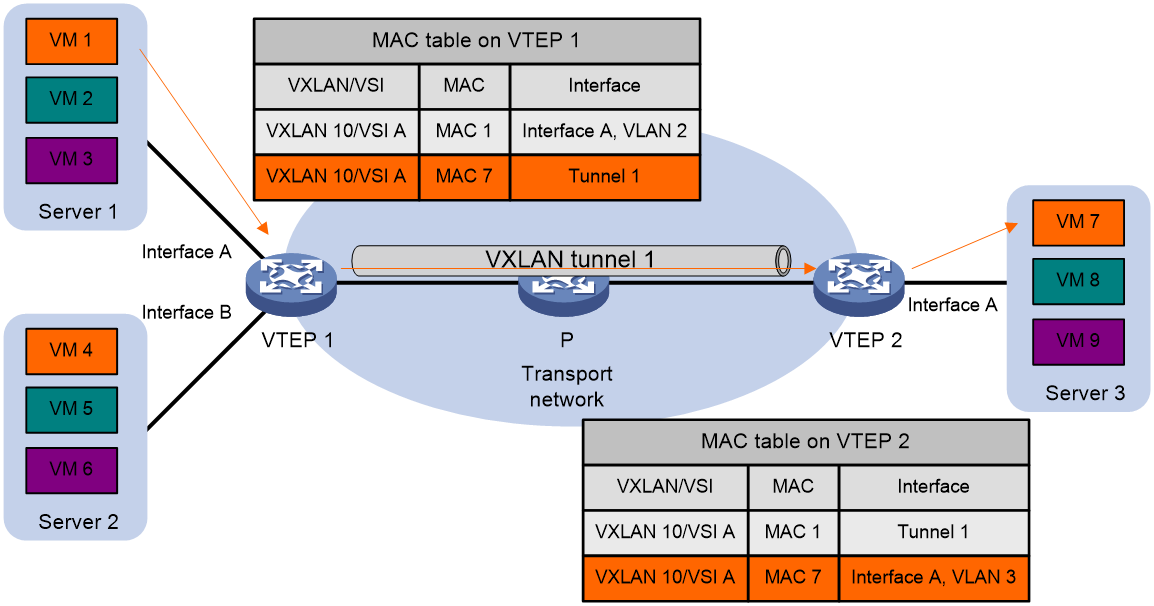
The VTEP performs Layer 2 forwarding based on a VSI's MAC address table. The VTEP learns MAC addresses by using the following methods:
· Local MAC learning—The VTEP automatically learns the source MAC addresses of frames sent from the local site. The outgoing interfaces of local MAC address entries are site-facing interfaces on which the MAC addresses are learned.
· Remote MAC learning—The VTEP uses MP-BGP to advertise local MAC reachability information to remote sites and learn MAC reachability information from remote sites. The outgoing interfaces of MAC address entries advertised from a remote site are VXLAN tunnel interfaces.
Unicast
As shown in Figure 3, the VTEP performs typical Layer 2 forwarding for known unicast traffic within the local site.
As shown in Figure 4, the following process applies to a known unicast frame between sites:
1. The source VTEP encapsulates the Ethernet frame in the VXLAN/UDP/IP header.
In the outer IP header, the source IP address is the source VTEP's VXLAN tunnel source IP address. The destination IP address is the VXLAN tunnel destination IP address.
2. The source VTEP forwards the encapsulated packet out of the outgoing VXLAN tunnel interface found in the VSI's MAC address table.
3. The intermediate transport devices (P devices) forward the packet to the destination VTEP by using the outer IP header.
4. The destination VTEP removes the headers on top of the inner Ethernet frame. It then performs MAC address table lookup in the VXLAN's VSI to forward the frame out of the matching outgoing interface.
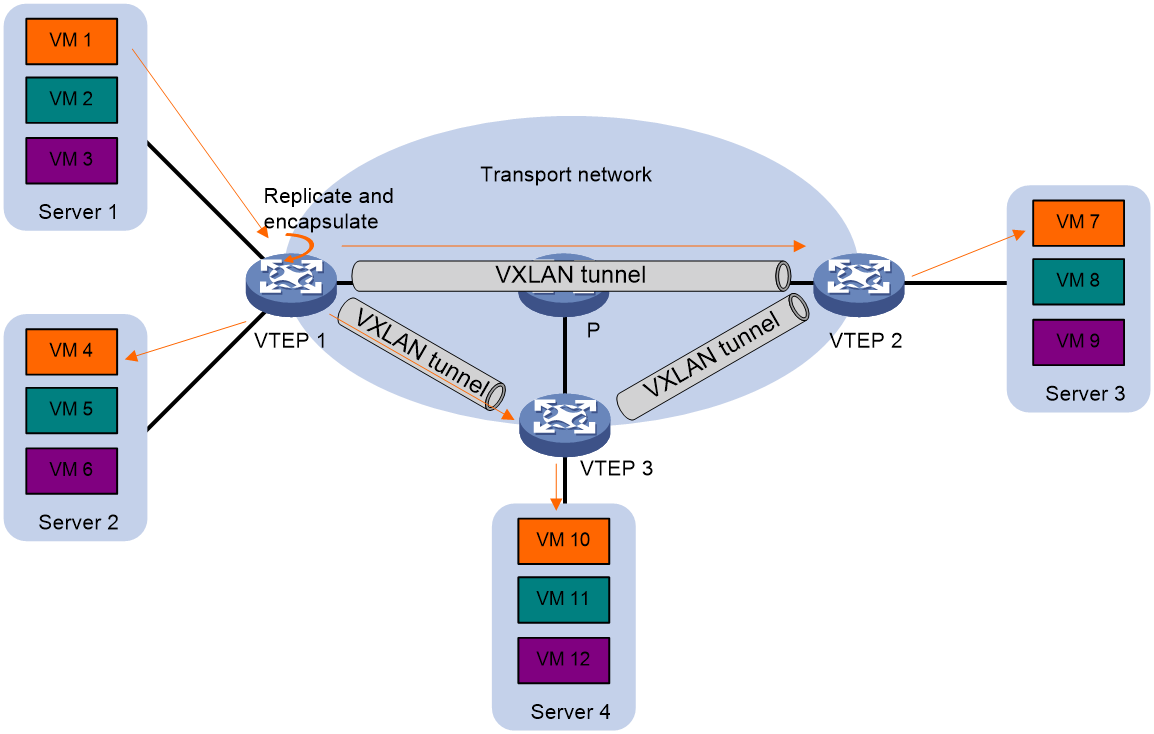
Flood
As shown in Figure 5, a VTEP floods a broadcast, multicast, or unknown unicast frame to all site-facing interfaces and VXLAN tunnels in the VXLAN, except for the incoming interface. The source VTEP replicates the flood frame, and then sends one replica to the destination IP address of each VXLAN tunnel in the VXLAN. Each destination VTEP floods the inner Ethernet frame to all the site-facing interfaces in the VXLAN. To avoid loops, the destination VTEPs do not flood the frame to VXLAN tunnels.
Figure 5 Forwarding of flood traffic
Centralized EVPN gateway deployment
|
IMPORTANT: A centralized EVPN gateway can provide services only for IPv4 sites. |
Centralized EVPN gateway deployment uses one VTEP to provide Layer 3 forwarding for VXLANs. The VTEP uses virtual Layer 3 VSI interfaces as gateway interfaces for VXLANs. Typically, the gateway-collocated VTEP connects to other VTEPs and the external network. To use this design, make sure the gateway has sufficient bandwidth and processing capability.
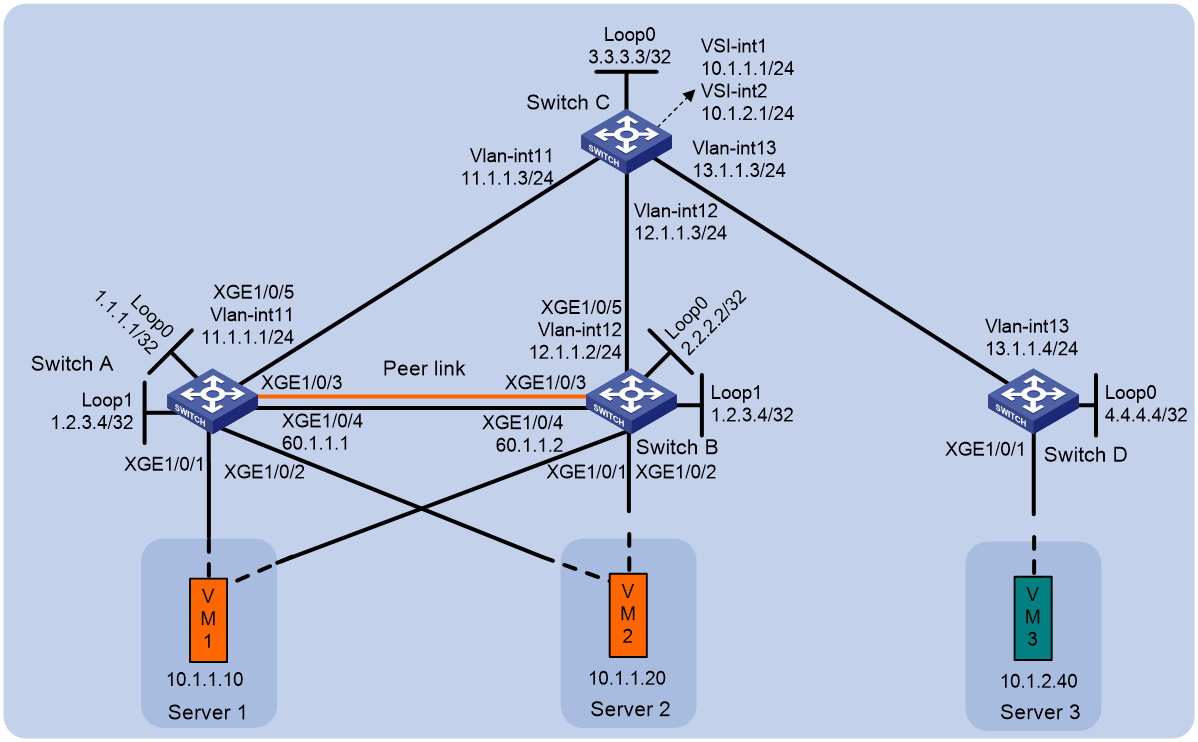
As shown in Figure 6, a VTEP acts as a gateway for VMs in the VXLANs. The VTEP both terminates the VXLANs and performs Layer 3 forwarding for the VMs. The network uses the following process to forward Layer 3 traffic from a VM to the destination:
1. The VM sends an ARP request to obtain the MAC address of the VSI interface that acts as the gateway, and then sends the Layer 3 traffic to the centralized EVPN gateway.
2. The local VTEP looks up the matching VSI's MAC address table and forwards the traffic to the centralized EVPN gateway through a VXLAN tunnel.
3. The centralized EVPN gateway removes the VXLAN encapsulation and forwards the traffic at Layer 3.
4. The centralized EVPN gateway forwards the replies sent by the destination node to the VM based on the ARP entry for the VM.
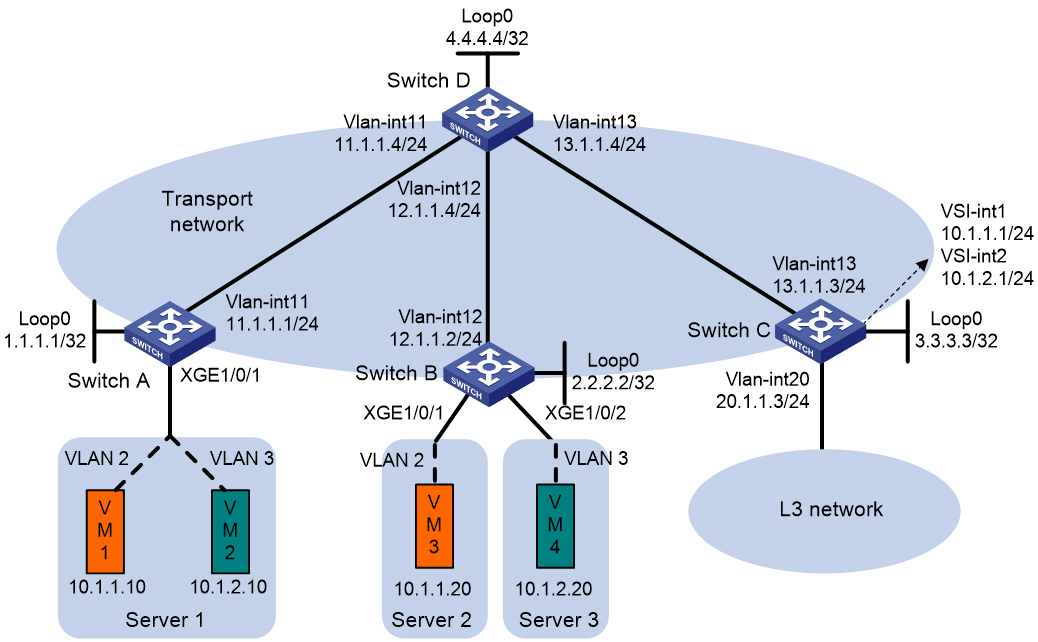
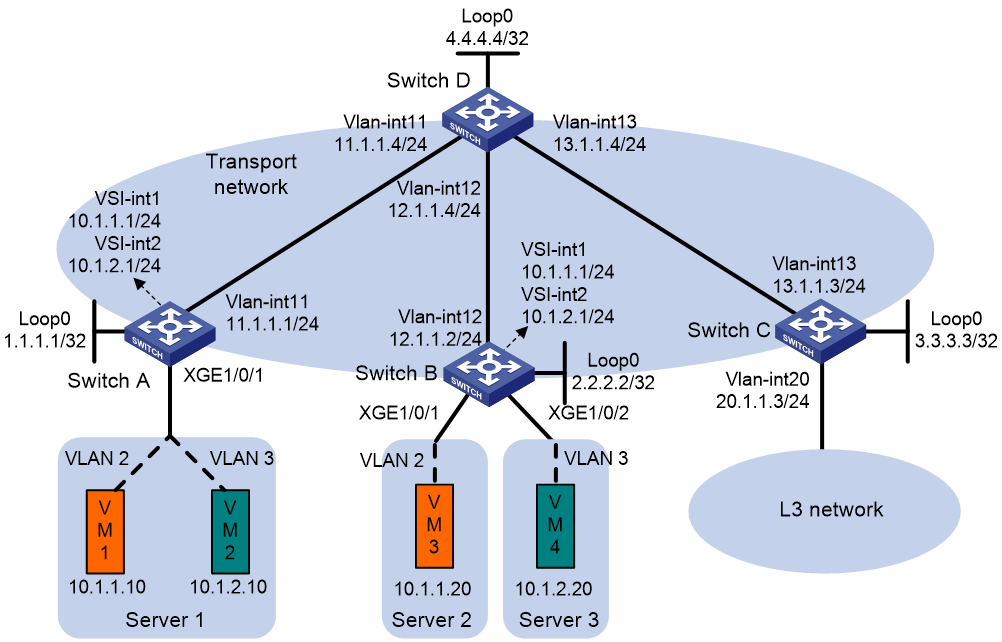
Figure 6 Example of centralized EVPN gateway deployment
Distributed EVPN gateway deployment
|
IMPORTANT: A distributed EVPN gateway can provide services for IPv4 and IPv6 sites. This section uses IPv4 sites as examples to describe the Layer 3 forwarding process of EVPN networks. The Layer 3 forwarding process does not differ between IPv4 and IPv6 sites. |
About distributed EVPN gateway deployment
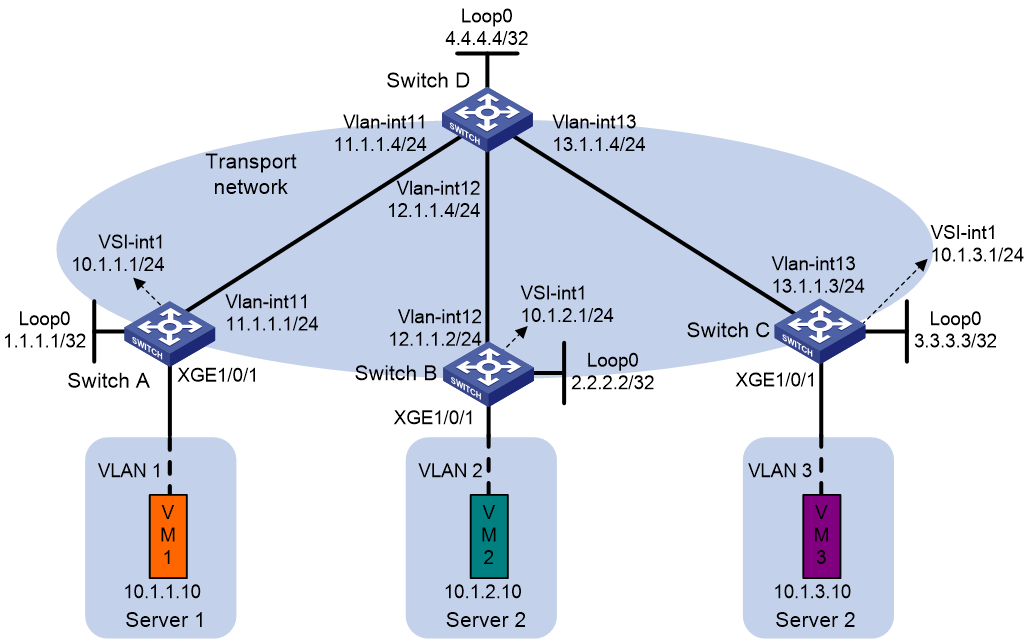
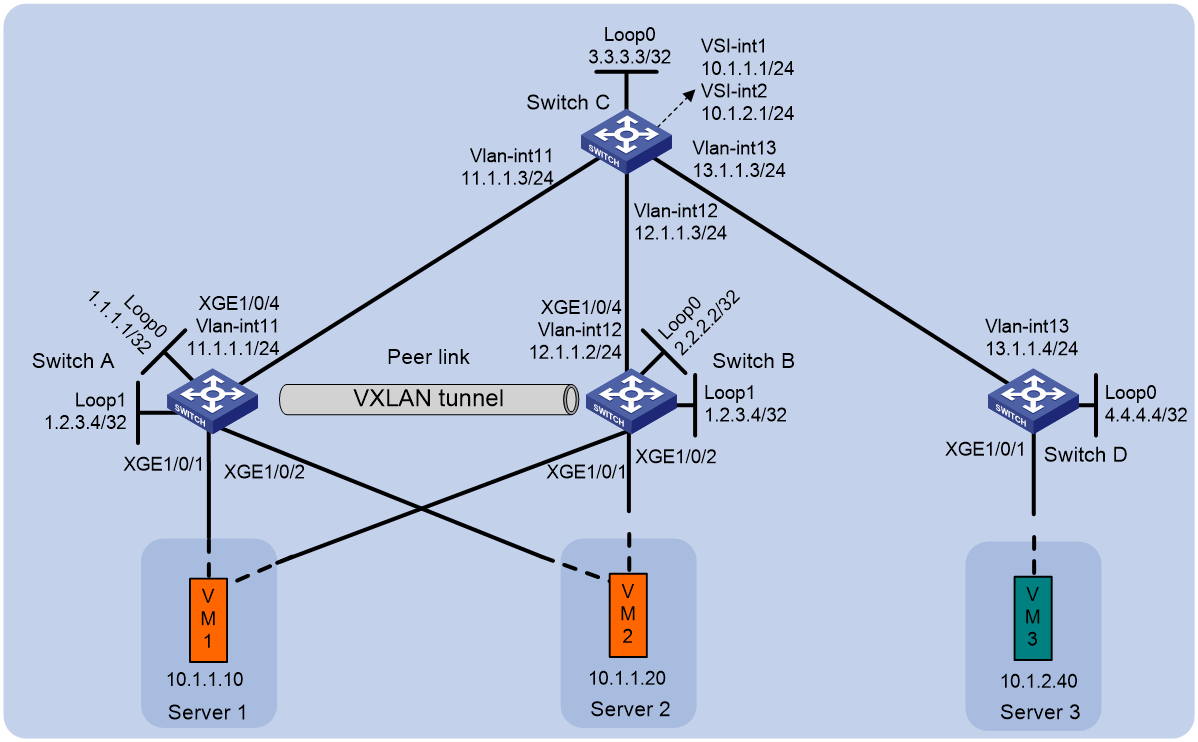
As shown in Figure 7, each site's VTEP acts as a gateway to perform Layer 3 forwarding for the VXLANs of the local site. A VTEP acts as a border gateway to the Layer 3 network for the VXLANs.
Figure 7 Distributed EVPN gateway placement design
A distributed EVPN gateway supports the following traffic forwarding modes:
· Asymmetric IRB—The ingress gateway performs Layer 2 and Layer 3 lookups and the egress gateway performs only Layer 2 forwarding.
· Symmetric IRB—Both the ingress and egress gateways perform Layer 2 and Layer 3 lookups.
Symmetric IRB
Basic concepts
Symmetric IRB introduces the following concepts:
· L3 VXLAN ID—Also called L3 VNI. An L3 VXLAN ID identifies the traffic of a routing domain where devices have Layer 3 reachability. An L3 VXLAN ID is associated with one VPN instance. Distributed EVPN gateways use VPN instances to isolate traffic of different services on VXLAN tunnel interfaces.
· Router MAC address—Each distributed EVPN gateway has a unique router MAC address used for inter-gateway forwarding. The MAC addresses in the inner Ethernet header of VXLAN packets are router MAC addresses of distributed EVPN gateways.
VSI interfaces
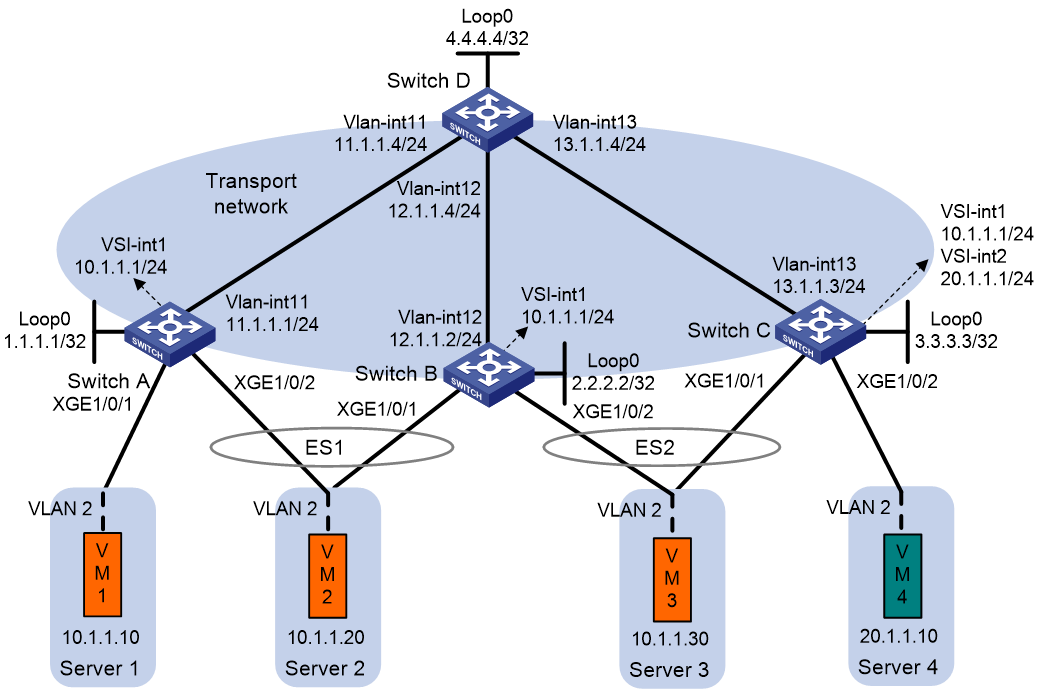
As shown in Figure 8, each distributed EVPN gateway has the following types of VSI interfaces:
· VSI interface as a gateway interface of a VXLAN—The VSI interface acts as the gateway interface for VMs in a VXLAN. The VSI interface is associated with a VSI and a VPN instance. On different distributed EVPN gateways, the VSI interface of a VXLAN use the same IP address to provide services.
· VSI interface associated with an L3 VXLAN ID—The VSI interface is associated with a VPN instance and assigned an L3 VXLAN ID. VSI interfaces associated with the same VPN instance share an L3 VXLAN ID.
A border gateway only has VSI interfaces that are associated with an L3 VXLAN ID.
Figure 8 Example of distributed EVPN gateway deployment
Layer 3 forwarding entry learning
A distributed EVPN gateway forwards Layer 3 traffic based on FIB entries generated from BGP EVPN routes and ARP information.
A VTEP advertises an external route imported in the EVPN address family through MP-BGP. A remote VTEP adds the route to the FIB table of a VPN instance based on the L3 VXLAN ID carried in the route. In the FIB entry, the outgoing interface is a VXLAN tunnel interface, and the next hop is the peer VTEP address in the NEXT_HOP attribute of the route.
A VTEP has the following types of ARP information:
· Local ARP information—ARP information of VMs in the local site. The VTEP snoops GARP packets, RARP packets, and ARP requests for the gateway MAC address to learn the ARP information of the senders and generates ARP entries and FIB entries. In an ARP or FIB entry, the outgoing interface is the site-facing interface where the packet is received, and the VPN instance is the instance associated with the corresponding VSI interface.
· Remote ARP information—ARP information of VMs in remote sites. Each VTEP uses MP-BGP to advertise its local ARP information with L3 VXLAN IDs in routes to remote sites. A VTEP generates only FIB entries for the remote ARP information. A FIB entry contains the following information:
¡ Outgoing interface: VSI interface associated with the L3 VXLAN ID.
¡ Next hop: Peer VTEP address in the NEXT_HOP attribute of the route.
¡ VPN instance: VPN instance associated with the L3 VXLAN ID.
The VTEP then creates an ARP entry for the next hop in the FIB entry.
Traffic forwarding
A distributed EVPN gateway can work in one of the following mode:
· Switching and routing mode—Forwards Layer 2 traffic based on the MAC address table and forwards Layer 3 traffic based on the FIB table. In this mode, you need to enable ARP flood suppression on the distributed EVPN gateway to reduce flooding.
· Routing mode— Forwards both Layer 2 and Layer 3 traffic based on the FIB table. In this mode, you need to enable local proxy ARP on the distributed EVPN gateway.
For more information about MAC address table-based Layer 2 forwarding, see "Unicast."
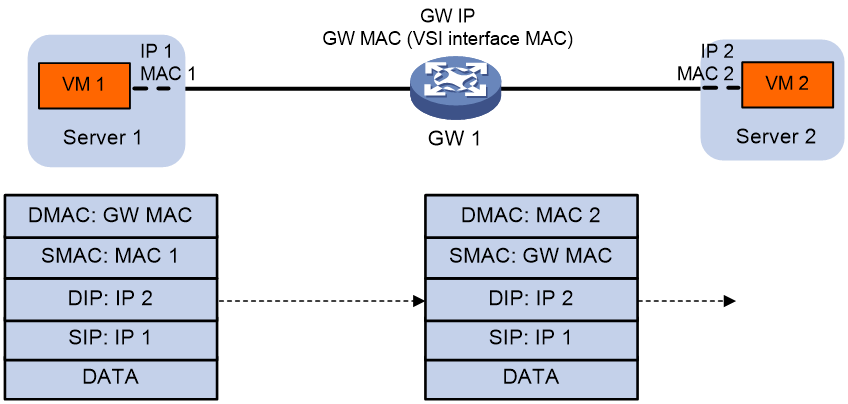
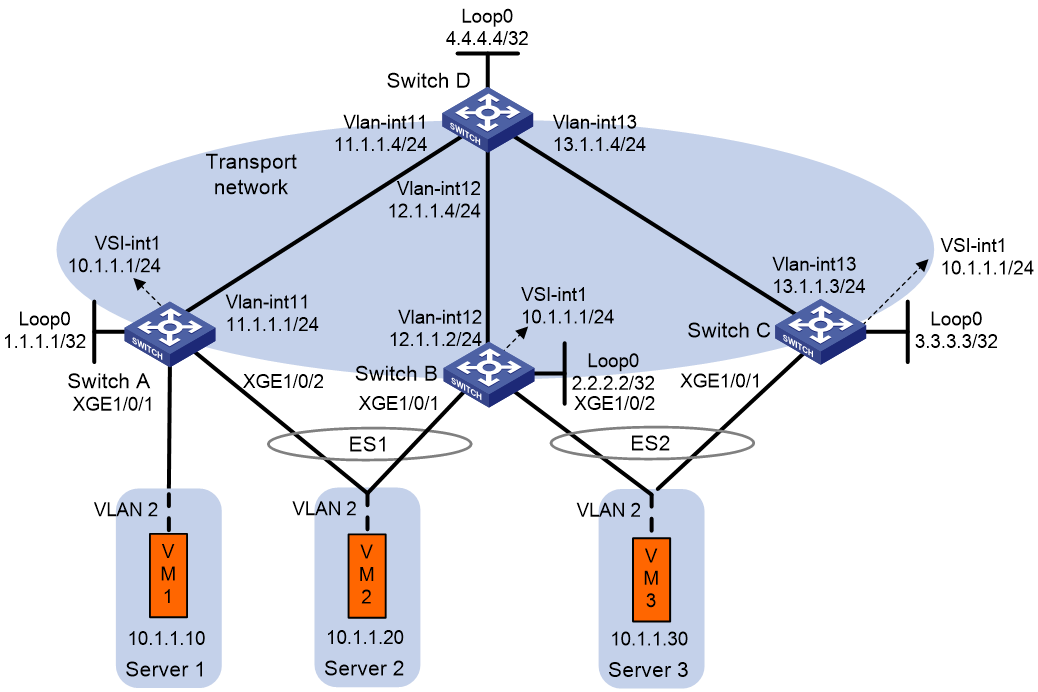
Figure 9 shows the intra-site Layer 3 forwarding process.
1. The source VM sends an ARP request to obtain the MAC address of the destination VM.
2. The gateway replies to the source VM with the MAC address of the VSI interface associated with the source VM's VSI.
3. The source VM sends a Layer 3 packet to the gateway.
4. The gateway looks up the FIB table of the VPN instance associated with the source VM's VSI and finds the matching outgoing site-facing interface.
5. The gateway processes the Ethernet header of the Layer 3 packet as follows:
¡ Replaces the destination MAC address with the destination VM's MAC address.
¡ Replaces the source MAC address with the VSI interface's MAC address.
6. The gateway forwards the Layer 3 packet to the destination VM.
Figure 9 Intra-site Layer 3 forwarding
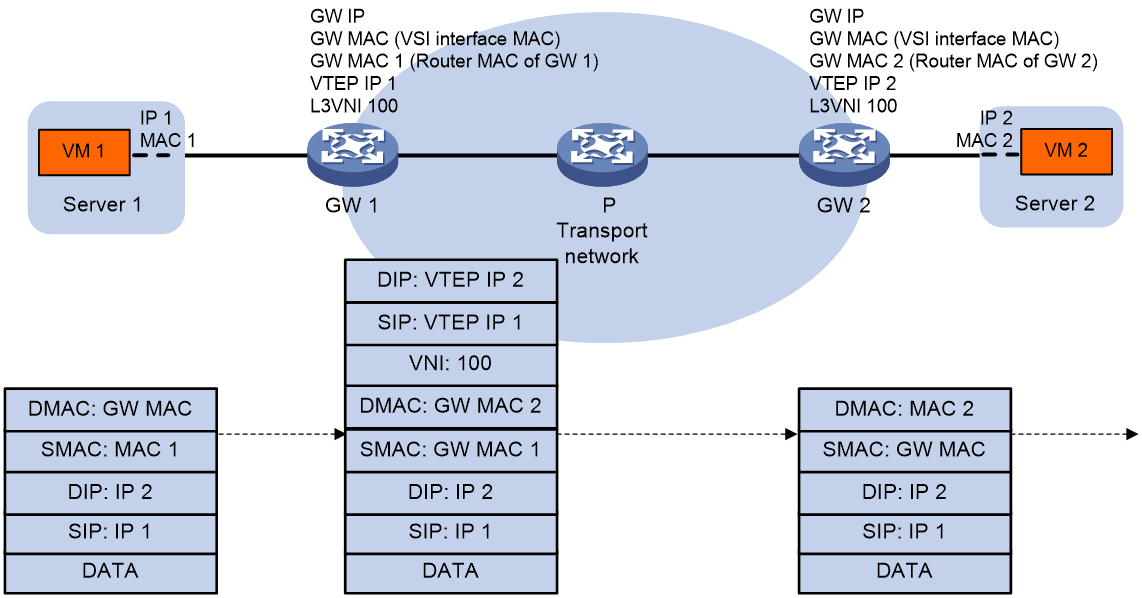
Figure 10 shows the inter-site Layer 3 forwarding process.
1. The source VM sends an ARP request to obtain the MAC address of the destination VM.
2. The gateway replies to the source VM with the MAC address of the VSI interface associated with the source VM's VSI.
3. The source VM sends a Layer 3 packet to the gateway.
4. The gateway looks up the FIB table of the VPN instance associated with the source VM's VSI and finds the matching outgoing VSI interface.
5. The gateway processes the Ethernet header of the Layer 3 packet as follows:
¡ Replaces the destination MAC address with the destination gateway's router MAC address.
¡ Replaces the source MAC address with its own router MAC address.
6. The gateway adds VXLAN encapsulation to the Layer 3 packet and forwards the packet to the destination gateway. The encapsulated VXLAN ID is the L3 VXLAN ID of the corresponding VPN instance.
7. The destination gateway identifies the VPN instance of the packet based on the L3 VXLAN ID and removes the VXLAN encapsulation. Then the gateway forwards the packet based on the matching ARP entry.
Figure 10 Inter-site Layer 3 forwarding
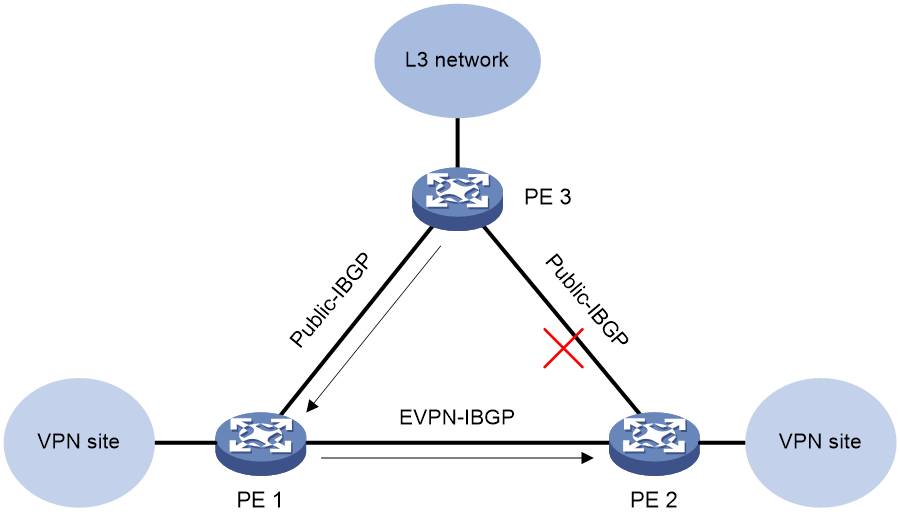
Communication between private and public networks
A distributed EVPN gateway uses the public instance to perform Layer 3 forwarding for the public network and to enable communication between private and public networks. The public instance is similar to a VPN instance. A distributed EVPN gateway processes traffic of the public instance in the same way it does for a VPN instance. For the public instance to work correctly, you must configure an RD, an L3 VXLAN ID, and route targets for it. If a VSI interface is not associated with any VPN instance, the VSI interface belongs to the public instance.
Asymmetric IRB
VSI interfaces
Asymmetric IRB uses the same distributed EVPN gateway deployment as symmetric IRB.
As shown in Figure 8, each distributed EVPN gateway has the following types of VSI interfaces:
· VSI interface as a gateway interface of a VXLAN—The VSI interface is associated with a VSI and a VPN instance. On different distributed EVPN gateways, the VSI interface of a VXLAN must use different IP addresses to provide services.
· VSI interface associated with an L3 VXLAN ID—The VSI interface acts as the gateway for VMs in a VXLAN to communicate with the external network through the border gateway. The VSI interface is associated with a VPN instance and assigned an L3 VXLAN ID. VSI interfaces associated with the same VPN instance share an L3 VXLAN ID.
A border gateway only has VSI interfaces that are associated with an L3 VXLAN ID.
Layer 3 forwarding
Asymmetric IRB supports only Layer 3 forwarding in the same VXLAN on distributed EVPN gateways.
After a distributed EVPN gateway learns ARP information about local VMs, it advertises the information to other distributed EVPN gateways through MAC/IP advertisement routes. Other distributed EVPN gateways generate FIB entries based on the advertised ARP information.
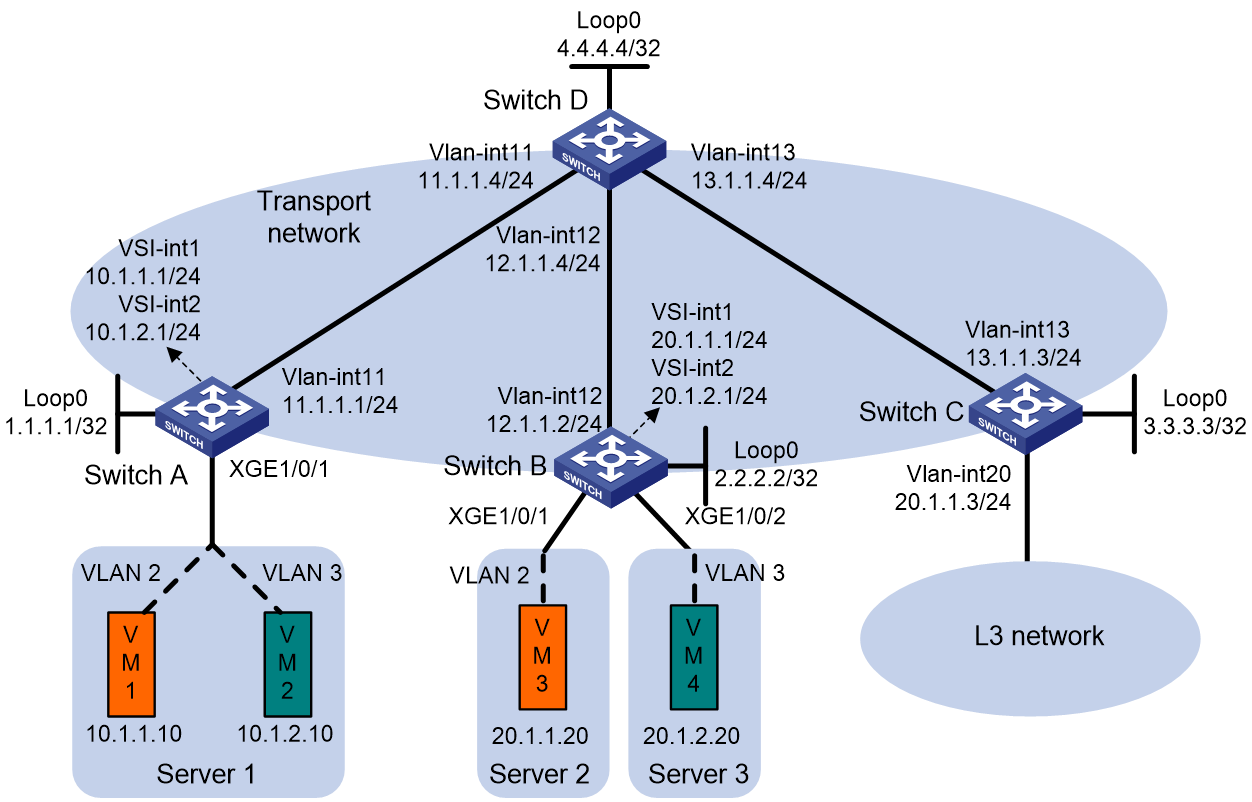
As shown in Figure 11, VM 1 and VM 2 belong to VXLAN 10 and they can reach each other at Layer 3 through the distributed EVPN gateways. The distributed EVPN gateways use the following process to perform Layer 3 forwarding in asymmetric IRB mode when VM 1 sends a packet to VM 2:
1. After GW 1 receives the packet from VM 1, it finds that the destination MAC address is itself. Then, GW 1 removes the Layer 2 frame header and looks up the FIB table for the destination IP address.
2. GW 1 matches the packet to the FIB entry generated based on the ARP information of VM 2.
3. GW 1 encapsulates the packet source and destination MAC addresses as the MAC addresses of GW 1 and VM 2, respectively. Then, GW 1 adds VXLAN encapsulation to the packet and forwards the packet to GW 2 through a VXLAN tunnel.
4. GW 2 removes the VXLAN encapsulation from the packet, and performs Layer 2 forwarding in VXLAN 10 by looking up the MAC address table for the destination MAC address.
5. GW 2 forwards the packet to VM 2 based on the MAC address table lookup result.
Figure 11 Layer 3 forwarding in the same VXLAN (asymmetric IRB)
EVPN VXLAN multihoming
About EVPN multihoming
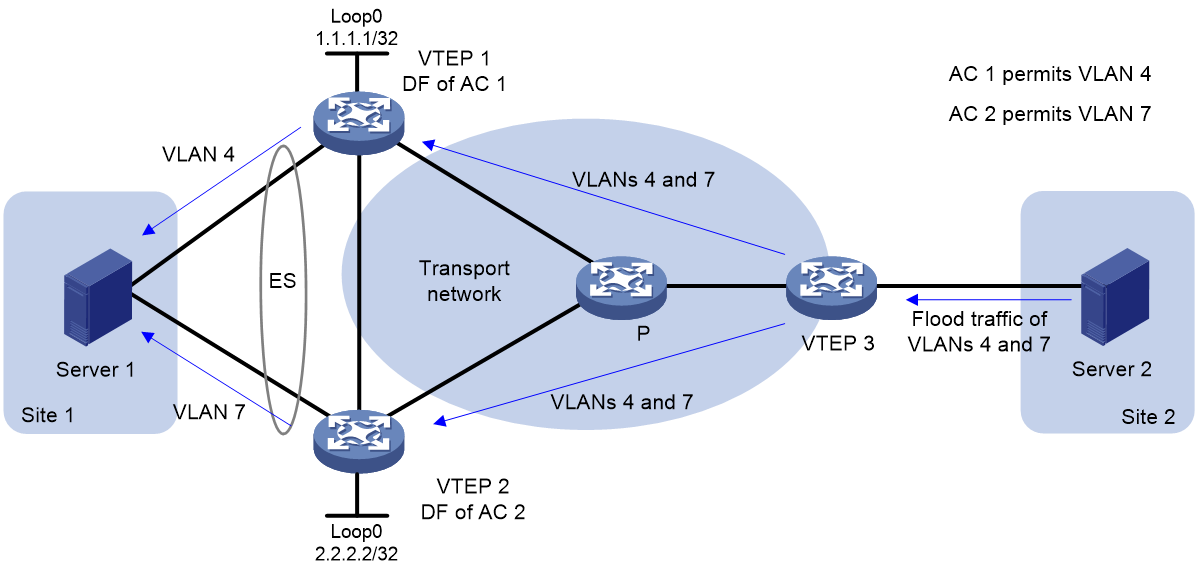
As shown in Figure 12, EVPN supports deploying multiple VTEPs at a site for redundancy and high availability. On the redundant VTEPs, Ethernet links connected to the site form an Ethernet segment (ES) that is uniquely identified by an Ethernet segment identifier (ESI).
Hardware compatibility with EVPN multihoming
EVPN multihoming is not supported by the S6800 switches labeled with the following product codes:
· LS-6800-2C.
· LS-6800-32Q.
· LS-6800-4C.
DF election
To prevent redundant VTEPs from sending duplicate flood traffic to a multihomed site, a designated forwarder (DF) is elected from the VTEPs for each AC to forward flood traffic to the AC. VTEPs that fail the election are assigned the backup designated forwarder (BDF) role. BDFs of an AC do not forward flood traffic to the AC.
A remote VTEP takes part in the DF election of a multihomed site. Redundant VTEPs of the site send Ethernet segment routes to the remote VTEP to advertise ES and VTEP IP mappings. Then, the VTEPs select a DF for each AC based on the ES and VTEP IP mappings by using the following procedure:
2. Divide the lowest VLAN ID permitted on an AC by the number of the redundant VTEPs, and match the reminder to the sequence numbers of IP addresses.
3. Assign the DF role to the VTEP that uses the IP address with the matching sequence number.
The following uses AC 1 in Figure 13 as an example to explain the DF election procedure:
1. VTEP 1 and VTEP 2 send Ethernet segment routes to VTEP 3.
2. Sequence numbers 0 and 1 are assigned to IP addresses 1.1.1.1 and 2.2.2.2 in the Ethernet segment routes, respectively.
3. The VTEPs divide 4 (the lowest VLAN ID permitted by AC 1) by 2 (the number of redundant VTEPs), and match the reminder 0 to the sequence numbers of the IP addresses.
4. The DF role is assigned to VTEP 1 at 1.1.1.1.
Split horizon
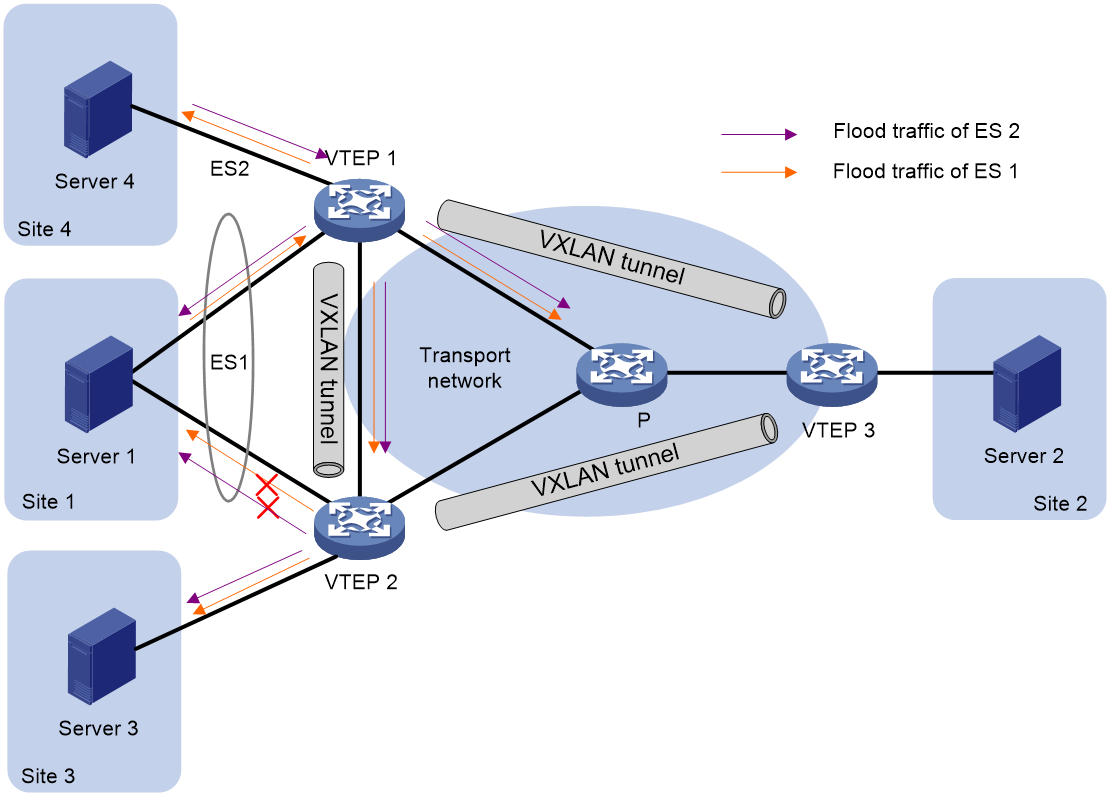
In a multihomed site, a VTEP forwards multicast, broadcast, and unknown unicast frames received from ACs out of all site-facing interfaces and VXLAN tunnels in the corresponding VXLAN, except for the incoming interface. As a result, the other VTEPs at the site receive these flood frames and forward them to site-facing interfaces, which causes duplicate floods and loops. EVPN introduces split horizon to resolve this issue. Split horizon disables a VTEP from forwarding flood traffic received from another local VTEP to site-facing interfaces if an ES on that local VTEP has the same ESI as these interfaces. As shown in Figure 14, both VTEP 1 and VTEP 2 have ES 1. When receiving flood traffic from VTEP 1, VTEP 2 does not forward the traffic to interfaces with ESI 1.
Redundancy mode
The device supports the all-active redundancy mode of EVPN multihoming. This mode allows all redundant VTEPs at a multihomed site to forward broadcast, multicast, and unknown unicast traffic.
· For flood frames received from remotes sites, a VTEP forwards them to the ACs of which it is the DF.
· For flood frames received from the local site, a VTEP forwards them out of all site-facing interfaces and VXLAN tunnels in the corresponding VXLAN, except for the incoming interfaces. For flood frames to be sent out of a VXLAN tunnel interface, a VTEP replicates each flood frame and sends one replica to all the other VTEPs in the corresponding VXLAN.
IP aliasing
In all-active redundancy mode, all redundant VTEPs of an ES advertise the ES to remote VTEPs through MP-BGP. IP aliasing allows a remote VTEP to add the IP addresses of all the redundant VTEPs as the next hops for the MAC or ARP information received from one of these VTEPs. This mechanism creates ECMP routes between the remote VTEP and the redundant VTEPs.
EVPN VXLAN multicast
EVPN supports multicast forwarding. In an EVPN network, VTEPs create and maintain multicast forwarding entries based on received IGMP membership reports and leave group messages to reduce IGMP floods.
Hardware compatibility with EVPN multicast
EVPN multicast is not supported by the S6800 switches labeled with the following product codes:
· LS-6800-2C.
· LS-6800-32Q.
· LS-6800-4C.
Multicast in single-homed sites
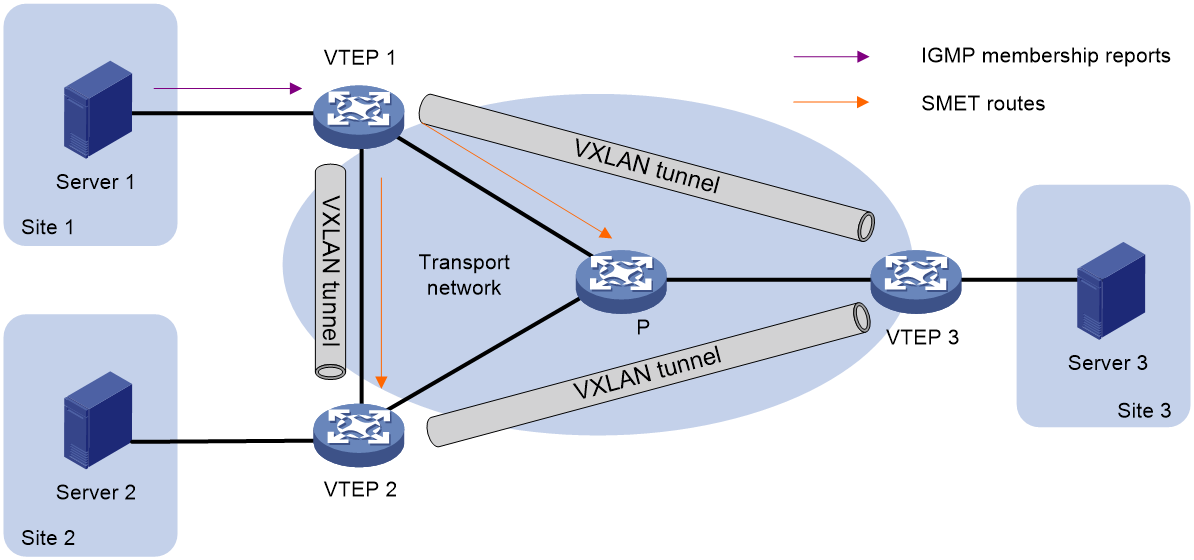
As shown in Figure 15, VTEPs at single-homed sites create multicast forwarding entries by using the following procedure:
1. VTEP 1 receives the IGMP membership report sent by Server 1.
2. VTEP 1 creates a multicast forwarding entry and advertises information about the multicast group to VTEP 2 and VTEP 3 through an SMET route.
3. VTEP 2 and VTEP 3 create multicast forwarding entries based on the SMET route. The next hop in the entries is VTEP 1.
Figure 15 Multicast in single-homed sites
Multicast in multihomed sites
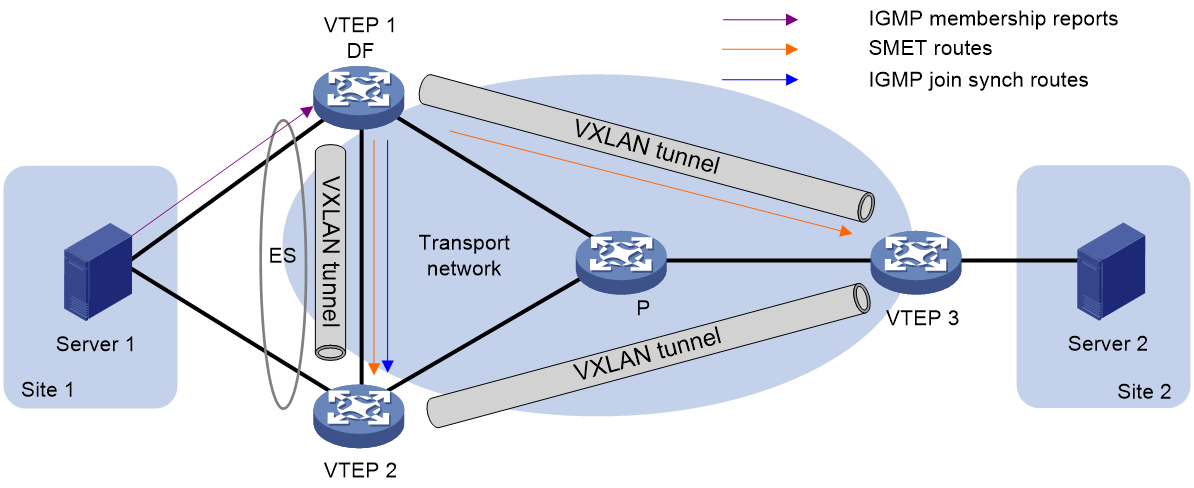
The IGMP membership reports and leave group messages sent from a multihomed site are received by multiple VTEPs. To ensure consistency of multicast forwarding entries, redundant VTEPs advertise IGMP join synch and leave synch routes to synchronize multicast information for each ES.
As shown in Figure 16, if the DF receives the first membership report for an IGMP multicast group, the following route advertisement and withdrawal process takes place:
1. VTEP 1 (DF) receives an IGMP membership report.
2. VTEP 1 sends an SMET route to VTEP 2 and VTEP 3, and sends an IGMP join synch route to VTEP 2.
3. An IGMP leave group message is sent from Site 1, and one of the following processes occurs:
¡ If VTEP 1 (DF) receives the message, it sends an IGMP leave synch route to VTEP 2 and withdraws the SMET route and IGMP join synch route that it has advertised.
¡ If VTEP 2 (BDF) receives the message, it sends an IGMP leave synch route to VTEP 1. Then VTEP 1 withdraws the SMET route and IGMP join synch route that it has advertised.
As shown in Figure 16, if the BDF receives the first membership report for an IGMP multicast group, the following route advertisement and withdrawal process takes place:
1. VTEP 2 (BDF) receives an IGMP membership report.
2. VTEP 2 sends an IGMP join synch route to VTEP 1 (DF).
3. VTEP 1 sends an SMET route to VTEP 2 and VTEP 3.
4. An IGMP leave group message is sent from Site 1, and one of the following processes occurs:
¡ If VTEP 1 (DF) receives the message, it sends an IGMP leave synch route to VTEP 2, and VTEP 2 withdraws the IGMP join synch route that it has advertised. Then, VTEP 1 withdraws the SMET route that it has advertised.
¡ If VTEP 2 (BDF) receives the message, it sends an IGMP leave synch route to VTEP 1 and withdraws the IGMP join synch route that it has advertised. Then, VTEP 1 withdraws the SMET route that it has advertised.
Figure 16 Multicast in multihomed sites
ARP and ND flood suppression
ARP or ND flood suppression reduces ARP request broadcasts or ND request multicasts by enabling the VTEP to reply to ARP or ND requests on behalf of VMs.
As shown in Figure 17, this feature snoops ARP or ND requests, ARP or ND responses, and BGP EVPN routes to populate the ARP or ND flood suppression table with local and remote MAC addresses. If an ARP or ND request has a matching entry, the VTEP replies to the request on behalf of the VM. If no match is found, the VTEP floods the request to both local and remote sites.
Figure 17 ARP and ND flood suppression
The following uses ARP flood suppression as an example to explain the flood suppression workflow:
1. VM 1 sends an ARP request to obtain the MAC address of VM 7.
2. VTEP 1 creates a suppression entry for VM 1, floods the ARP request in the VXLAN, and sends the suppression entry to VTEP 2 and VTEP 3 through BGP EVPN.
3. VTEP 2 and VTEP 3 de-encapsulate the ARP request and broadcast the request in the local site.
4. VM 7 sends an ARP reply.
5. VTEP 2 creates a suppression entry for VM 7, forwards the ARP reply to VTEP 1, and sends the suppression entry to VTEP 1 and VTEP 3 through BGP EVPN.
6. VTEP 1 de-encapsulates the ARP reply and forwards the ARP reply to VM 1.
7. VM 4 sends an ARP request to obtain the MAC address of VM 1.
8. VTEP 1 creates a suppression entry for VM 4 and replies to the ARP request.
9. VM 10 sends an ARP request to obtain the MAC address of VM 1.
10. VTEP 3 creates a suppression entry for VM 10 and replies to the ARP request.
MAC mobility
MAC mobility refers to that a VM or host moves from one ES to another. The source VTEP is unaware of the MAC move event. To notify other VTEPs of the change, the destination VTEP advertises a MAC/IP advertisement route for the MAC address. The source VTEP withdraws the old route for the MAC address after receiving the new route. The MAC/IP advertisement route has a sequence number that increases when the MAC address moves. The sequence number identifies the most recent move if the MAC address moves multiple times.
EVPN M-LAG
|
|
NOTE: EVPN distributed relay supports only IPv4 sites. |
About EVPN M-LAG
As shown in Figure 18, EVPN multichassis link aggregation (M-LAG) virtualizes two VTEPs or EVPN gateways into one M-LAG system through M-LAG to avoid single points of failure. The VTEPs or EVPN gateways are called M-LAG member devices. For more information about M-LAG, see Layer 2—LAN Switching Configuration Guide.
Figure 18 EVPN M-LAG
VM reachability information synchronization
To ensure VM reachability information consistency in the M-LAG system, the M-LAG member devices synchronize MAC address entries and ARP or ND information with each other through a peer link. The peer link can be an Ethernet aggregate link or a VXLAN tunnel, which are referred to as direct peer link and tunnel peer link, respectively.
|
IMPORTANT: The VXLAN tunnel that acts as the peer link is automatically associated with all VXLANs on each M-LAG member device. |
Virtual VTEP address
The M-LAG member devices use a virtual VTEP address to set up VXLAN tunnels with remote VTEPs or EVPN gateways.
Independent BGP neighbor relationship establishment
The M-LAG member devices use different BGP peer addresses to establish neighbor relationships with remote devices. For load sharing and link redundancy, a neighbor sends traffic destined for the virtual VTEP address to both of the M-LAG member devices through ECMP routes of the underlay network.
Site-facing link redundancy
|
IMPORTANT: This mechanism ensures service continuity in case of site-facing AC failure. |
As shown in Figure 18, a VM accesses the EVPN network through multiple Ethernet links that connect to the VTEPs. On each VTEP, all site-facing Ethernet links are assigned to a Layer 2 aggregation group for high availability. On the corresponding Layer 2 aggregate interfaces, Ethernet service instances are configured as ACs of VXLANs to match customer traffic.
Link redundancy mechanism for a direct peer link
If the peer link is an Ethernet aggregate link, each VTEP in the M-LAG system creates dynamic ACs on the peer-link interface by using one of the following methods:
· Creation based on site-facing ACs—When a site-facing AC is created, a VTEP automatically creates an AC on the peer-link interface. The automatically created AC uses the same traffic match criterion as the site-facing AC and is mapped to the same VSI as the site-facing AC.
· Creation based on VXLAN IDs—When a VXLAN is created, a VTEP automatically creates an AC on the peer-link interface. The automatically created AC uses a frame match criterion generated based on the VXLAN ID and is mapped to the VSI of the VXLAN.
When a site-facing AC goes down, traffic that a remote device sends to the AC is forwarded to the other M-LAG member device through the peer link. The other M-LAG member device identifies the VSI of the traffic and forwards the traffic to the destination.
Link redundancy mechanism for a tunnel peer link
If a site-facing AC on an M-LAG member device is down, traffic received from a VXLAN tunnel and destined for the AC will be encapsulated into VXLAN packets. The VXLAN ID belongs to the VXLAN that is associated with the VSI of the site-facing AC. The M-LAG member device forwards the VXLAN packets through the tunnel peer link to the peer M-LAG member device. The peer M-LAG member device assigns the traffic to the correct VSI based on the VXLAN ID in the received packets.
Configuring EVPN VXLAN
EVPN VXLAN tasks at a glance
To configure EVPN VXLAN, perform the following tasks:
1. Setting the VXLAN hardware resource mode
2. Configuring a VXLAN on a VSI
b. (Optional.) Configuring VSI parameters
3. Configuring an EVPN instance
4. (Optional.) Configuring EVPN multihoming
a. Assigning an ESI to an interface
b. (Optional.) Setting the DF election delay
c. (Optional.) Configuring FRR for EVPN VXLAN
d. Disabling advertisement of EVPN multihoming routes
5. Configuring BGP to advertise BGP EVPN routes
a. Enabling BGP to advertise BGP EVPN routes
b. (Optional.) Configuring BGP EVPN route settings
c. (Optional.) Enabling the device to ignore default routes in route recursion
d. (Optional.) Maintaining BGP sessions
7. Configuring an EVPN gateway
Choose one of the following tasks:
¡ Configuring a centralized EVPN gateway
¡ Configuring a distributed EVPN gateway
8. (Optional.) Managing remote MAC address entries and remote ARP or ND learning
¡ Disabling remote MAC address learning and remote ARP or ND learning
¡ Disabling MAC address advertisement
¡ Enabling MAC mobility event suppression
¡ Disabling learning of MAC addresses from ARP or ND information
¡ Disabling ARP information advertisement
¡ Enabling ND information advertisement
¡ Enabling ARP mobility event suppression
¡ Enabling ND mobility event suppression
9. (Optional.) Enabling conversational learning for forwarding entries
To save device hardware resources, remote MAC entries, host route FIB entries, and remote ARP entries are issued to the hardware only when the entries are required for packet forwarding.
¡ Enabling conversational learning for remote MAC address entries
¡ Enabling conversational learning for host route FIB entries
10. (Optional.) Configuring BGP EVPN route redistribution and advertisement
¡ Redistributing MAC/IP advertisement routes into BGP unicast routing tables
¡ Setting the metric of BGP EVPN routes added to a VPN instance's routing table
¡ Enabling BGP EVPN route advertisement to the local site
11. (Optional.) Maintaining and optimizing an EVPN network
¡ Disabling flooding for a VSI
¡ Enabling ARP or ND flood suppression
¡ Enabling packet statistics for VXLAN tunnels
¡ Testing the connectivity of a VXLAN tunnel
¡ Enabling SNMP notifications for EVPN
12. (Optional.) Configuring EVPN M-LAG
Perform this task to virtualize two VTEPs or EVPN gateways into one M-LAG system to avoid single points of failure.
Restrictions: Hardware compatibility with EVPN gateways
EVPN gateways are not supported by S6800 switches labeled with the following product codes:
· LS-6800-2C.
· LS-6800-32Q.
· LS-6800-4C.
Restrictions and guidelines: EVPN VXLAN configuration
Make sure the following VXLAN tunnels are not associated with the same VXLAN when they have the same tunnel destination IP address:
· A VXLAN tunnel automatically created by EVPN.
· A manually created VXLAN tunnel.
For more information about manual tunnel configuration, see VXLAN Configuration Guide.
As a best practice to ensure correct traffic forwarding, configure the same MAC address for all VSI interfaces on an EVPN gateway.
If two tiers of spine devices act as RRs in the transport network, execute the peer route-update-interval command to speed up network convergence after device or link failure occurs. For more information about this command, see BGP commands in Layer 3—IP Routing Command Reference.
In an EVPN multicast network, do not configure one of the following features for one VSI and the other feature for another VSI:
· Layer 2 multicast MAC forwarding mode.
· Layer 2 multicast IP forwarding mode or Layer 3 multicast.
When you configure EVPN gateways, follow these restrictions and guidelines:
|
Device role |
Configuration |
Restrictions and guidelines |
|
EVPN gateway |
Ethernet service instance and access mode |
· Use the Ethernet access mode if an Ethernet service instance uses the encapsulation untagged criterion. · Use the VLAN access mode if an Ethernet service instance uses the encapsulation s-vid { vlan-id [ only-tagged ] | vlan-id-list } criterion. |
|
Priority trust mode |
An EVPN gateway processes the DSCP precedence in frames received from an AC as follows: · For Layer 3 forwarding, the gateway always uses the DSCP precedence for priority mapping, regardless of whether you configure the qos trust dscp command on the incoming interface. · For Layer 2 forwarding, the gateway uses the DSCP precedence for priority mapping only when the qos trust dscp command is configured on the incoming interface. |
|
|
PBR |
A PBR policy cannot match VXLAN packets by the source and destination IP addresses in the outer IP header on a Layer 3 interface (VSI interfaces not included). To match VXLAN packets by the source and destination IP addresses in the outer IP header, apply a PBR policy to a VSI interface. |
|
|
VTEP |
PBR |
On a Layer 3 interface, a PBR policy cannot match VXLAN packets by the source and destination IP addresses in the outer IP header. |
|
Border gateway (S6800 and S6860 switch series) |
ACL |
An ACL applied to a Layer 3 Ethernet interface or Layer 3 aggregate interface matches packets on both the interface and its subinterfaces. For more information about ACLs, see ACL and QoS Configuration Guide. |
|
QoS |
· A QoS policy applied to a Layer 3 Ethernet interface also takes effect on its subinterfaces if the QoS policy does not contain inner and outer VLAN ID match criteria. For more information about QoS policies, see ACL and QoS Configuration Guide. · If a QoS policy is applied to an interface other than a Layer 3 Ethernet interface, the inner and outer VLAN ID match criteria in the QoS policy cannot match untagged packets that are forwarded at Layer 3. |
|
|
PBR |
A PBR policy applied to a Layer 3 Ethernet interface or Layer 3 aggregate interface takes effect on both the interface and its subinterfaces. For more information about PBR, see Layer 3—IP Routing Configuration Guide. |
|
|
Storm suppression |
Broadcast, multicast, or unknown unicast storm suppression configured on a Layer 3 Ethernet interface takes effect on both the interface and its subinterfaces. For more information about storm suppression, see Layer 2—LAN Switching Configuration Guide. |
|
|
MAC address assignment |
Do not use the mac-address command to assign MAC addresses to the following interfaces: · Layer 3 Ethernet interfaces. · Layer 3 Ethernet subinterfaces. · Layer 3 aggregate interfaces. · Layer 3 aggregate subinterfaces. |
|
|
ARP |
You cannot execute the arp mode uni command on interfaces of a Layer 3 border gateway. For more information about this command, see ARP commands in Layer 3—IP Services Command Reference. |
In border hardware resource mode, the device cannot transparently forward VXLAN packets without encapsulating them.
In border hardware resource mode, if you modify the MAC address of a Layer 3 interface acting as a VXLAN tunnel source interface, the device cannot decapsulate or forward the untagged packets received from the related VXLAN tunnel. To avoid this issue, modify the MAC address for the subinterfaces of the VXLAN tunnel source interface instead.
Setting the VXLAN hardware resource mode
About the VXLAN hardware resource mode
Set the hardware resource mode for VXLAN based on the role of the device.
· l2gw—Applies to VTEPs that perform only Layer 2 forwarding.
· l3gw8k, l3gw16k, l3gw24k, l3gw32k, or l3gw40k—Applies to VXLAN IP gateways.
· border8k, border16k, border24k, border28k, border32k, or border40k—Applies to Layer 3 border gateways that provide access to external networks.
Hardware and feature compatibility
This feature is not supported by S6800 switches labeled with the following product codes:
· LS-6800-2C.
· LS-6800-32Q.
· LS-6800-4C.
Restrictions and guidelines
For the hardware resource mode to take effect, you must reboot the device.
Procedure
1. Enter system view.
system-view
2. Set the VXLAN hardware resource mode.
hardware-resource vxlan { border8k | border16k | border24k | border28k | border32k | border40k | l2gw | l3gw8k | l3gw16k | l3gw24k | l3gw32k | l3gw40k }
By default, the VXLAN hardware resource mode is l2gw.
For more information about this command, see VXLAN Command Reference.
The S6800 switch series does not support the border28k keyword.
The S6860 switch series does not support the border8k, border16k, border32k, border40k, l3gw32k, or l3gw40k keyword.
Configuring a VXLAN on a VSI
Restrictions and guidelines for VXLAN configuration on a VSI
For more information about the VXLAN commands in this task, see VXLAN Command Reference.
Creating a VXLAN on a VSI
1. Enter system view.
system-view
2. Enable L2VPN.
l2vpn enable
By default, L2VPN is disabled.
3. Create a VSI and enter VSI view.
vsi vsi-name
4. Enable the VSI.
undo shutdown
By default, a VSI is enabled.
5. Create a VXLAN and enter VXLAN view.
vxlan vxlan-id
You can create only one VXLAN on a VSI. The VXLAN ID must be unique for each VSI.
Configuring VSI parameters
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Configure a VSI description.
description text
By default, a VSI does not have a description.
4. Set the MTU for the VSI.
mtu size
The default MTU is 1500 bytes for a VSI.
5. Set the maximum bandwidth for known unicast traffic of the VSI.
bandwidth bandwidth
By default, the maximum bandwidth is not limited for known unicast traffic of a VSI.
6. Set the broadcast, unknown multicast, or unknown unicast restraint bandwidth for the VSI.
restrain { broadcast | multicast | unknown-unicast } bandwidth
By default, a VSI's broadcast restraint bandwidth, unknown multicast restraint bandwidth, and unknown unicast restraint bandwidth are not set.
7. Enable MAC address learning for the VSI.
mac-learning enable
By default, MAC address learning is enabled for a VSI.
Configuring an EVPN instance
About EVPN instance configuration
If a VXLAN requires only Layer 2 connectivity, you do not need to associate a VPN instance with it. The BGP EVPN routes advertised by a VTEP carry the RD and route targets configured for the EVPN instance associated with the VXLAN.
Use one of the following methods to create an EVPN instance:
· Create an EVPN instance in system view—You can bind an EVPN instance created in system view to multiple VSIs to simplify configuration.
· Create an EVPN instance on a VSI—An EVPN instance created in VSI view is automatically bound with the VSI.
Restrictions and guidelines for EVPN instance configuration
You can bind a VSI only to one EVPN instance.
If you have created an EVPN instance in VSI view for a VSI, you cannot bind the VSI to an EVPN instance created in system view. If you have bound a VSI to an EVPN instance created in system view, you cannot create an EVPN instance in VSI view for the VSI.
Configuring an EVPN instance created in system view
1. Enter system view.
system-view
2. Create an EVPN instance and enter its view.
evpn instance instance-name
3. Configure an RD for the EVPN instance.
route-distinguisher route-distinguisher
By default, no RD is configured for an EVPN instance.
4. Configure route targets for the EVPN instance.
vpn-target vpn-target&<1-8> [ both | export-extcommunity | import-extcommunity ]
By default, an EVPN instance does not have route targets.
Make sure the following requirements are met:
¡ The import targets of the EVPN instance do not match the export targets of the VPN instance associated with the VXLAN or the public instance.
¡ The export targets of the EVPN instance do not match the import targets of the VPN instance associated with the VXLAN or the public instance.
For more information about VPN instance configuration and public instance configuration, see "Configuring an L3 VXLAN ID for a VSI interface."
5. Return to system view.
quit
6. Enter VSI view.
vsi vsi-name
7. Bind the VSI to the EVPN instance.
evpn encapsulation vxlan binding instance instance-name vsi-tag { tag-id | auto-vxlan }
By default, a VSI is not bound to an EVPN instance created in system view.
Configuring an EVPN instance created in VSI view
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Create an EVPN instance and enter EVPN instance view.
evpn encapsulation vxlan
4. Configure an RD for the EVPN instance.
route-distinguisher { route-distinguisher | auto [ router-id ] }
By default, no RD is configured for an EVPN instance.
5. Configure route targets for the EVPN instance.
vpn-target { vpn-target&<1-8> | auto } [ both | export-extcommunity | import-extcommunity ]
By default, an EVPN instance does not have route targets.
Make sure the following requirements are met:
¡ The import targets of the EVPN instance do not match the export targets of the VPN instance associated with the VXLAN or the public instance.
¡ The export targets of the EVPN instance do not match the import targets of the VPN instance associated with the VXLAN or the public instance.
For more information about VPN instance configuration and public instance configuration, see "Configuring an L3 VXLAN ID for a VSI interface."
Configuring EVPN multihoming
Restrictions and guidelines for EVPN multihoming
In a multihomed site, AC configuration and VXLAN IDs must be consistent on redundant VTEPs of the same ES. For each VXLAN ID, you must configure unique RDs for the EVPN instance of VSIs on the redundant VTEPs. You must configure different RDs for the VPN instances and the public instance that use the same VXLAN IP gateway.
IRF and EVPN multihoming are mutually exclusive. Do not configure them together on the device.
Hardware compatibility with EVPN multihoming
EVPN multihoming is not supported by the S6800 switches labeled with the following product codes:
· LS-6800-2C.
· LS-6800-32Q.
· LS-6800-4C.
Assigning an ESI to an interface
About this task
An ESI uniquely identifies an ES. The links on interfaces with the same ESI belong to the same ES. Traffic of the ES can be distributed among the links for load sharing.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
¡ Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
¡ Enter Layer 2 aggregate interface view.
interface bridge-aggregation interface-number
3. Assign an ESI to the interface.
esi esi-id
By default, no ESI is assigned to an interface.
Setting the DF election delay
About this task
The DF election can be triggered by site-facing interface status changes, redundant VTEP membership changes, and interface ESI changes. To prevent frequent DF elections from degrading network performance, set the DF election delay. The DF election delay defines the minimum interval allowed between two DF elections.
Procedure
1. Enter system view.
system-view
2. Set the DF election delay.
evpn multihoming timer df-delay delay-value
By default, the DF election delay is 3 seconds.
Configuring FRR for EVPN VXLAN
About this task
Local FRR enables two VTEPs at a multihomed EVPN VXLAN network site to set up a bypass VXLAN tunnel between them. This feature helps reduce the traffic loss caused by AC failure.
Procecure
1. Enter system view.
system-view
2. Enable local FRR globally for EVPN VXLAN.
evpn multihoming vxlan-frr local
By default, local FRR is disabled globally for EVPN VXLAN.
Disabling advertisement of EVPN multihoming routes
About this task
EVPN multihoming routes include Ethernet auto-discovery routes and Ethernet segment routes.
In a multihomed EVPN network, perform this task on a redundant VTEP before you reboot it. This operation allows other VTEPs to refresh their EVPN routing table to prevent traffic interruption caused by the reboot.
Restrictions and guidelines
Do not perform this task on VTEPs at a multihomed EVPN VXLAN site if EVPN forwards multicast traffic based on SMET, IGMP join sync, and IGMP leave sync routes. Violation of this restriction might cause multicast forwarding errors.
Procedure
1. Enter system view.
system-view
2. Disable advertisement of EVPN multihoming routes and withdraw the EVPN multihoming routes that have been advertised to remote sites.
evpn multihoming advertise disable
By default, the device advertises EVPN multihoming routes.
Configuring BGP to advertise BGP EVPN routes
Restrictions and guidelines for BGP EVPN route advertisement
For more information about BGP commands in this task, see Layer 3—IP Routing Command Reference.
Enabling BGP to advertise BGP EVPN routes
1. Enter system view.
system-view
2. Configure a global router ID.
router id router-id
By default, no global router ID is configured.
3. Enable a BGP instance and enter BGP instance view.
bgp as-number [ instance instance-name ]
By default, BGP is disabled and no BGP instances exist.
4. Specify remote VTEPs as BGP peers.
peer { group-name | ipv4-address [ mask-length ] } as-number as-number
5. Create the BGP EVPN address family and enter BGP EVPN address family view.
address-family l2vpn evpn
6. Enable BGP to exchange BGP EVPN routes with a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] } enable
By default, BGP does not exchange BGP EVPN routes with peers.
Configuring BGP EVPN route settings
Configuring BGP EVPN to advertise default routes
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. Advertise a default route to a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] | ipv6-address [ prefix-length ] } default-route-advertise { ipv4 | ipv6 } vpn-instance vpn-instance-name
By default, no default route is advertised to any peers or peer groups.
Configuring attributes of BGP EVPN routes
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. Permit the local AS number to appear in routes from a peer or peer group and set the number of appearances.
peer { group-name | ipv4-address [ mask-length ] } allow-as-loop [ number ]
By default, the local AS number is not allowed in routes from peers.
5. Configure the device to not change the next hop of routes advertised to an EBGP peer or peer group.
peer { group-name | ipv4-address [ mask-length ] | ipv6-address [ prefix-length ] } next-hop-invariable
By default, the device uses its address as the next hop of routes advertised to EBGP peers.
6. Advertise the COMMUNITY attribute to a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] } advertise-community
By default, the device does not advertise the COMMUNITY attribute to peers or peer groups.
7. Remove the default-gateway extended community attribute from the EVPN gateway routes advertised to a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] } default-gateway no-advertise
By default, EVPN gateway routes advertised to peers and peer groups contain the default-gateway extended community attribute.
8. Configure the device to advertise BGP routes with the lowest priority to peers. Choose one of the following options:
¡ Configure the device to advertise BGP routes with the lowest priority to a peer within a specified period of time after the peer goes down.
advertise lowest-priority on-peer-up duration seconds
¡ Configure the device to advertise BGP routes with the lowest priority to peers within a specified period of time after the BGP process restarts because of a device reboot.
advertise lowest-priority on-startup duration seconds
By default, the device does not change the priority of the BGP routes advertised to peers.
To set the priority of BGP routes to the lowest, the device sets the local preference and MED value of the BGP routes to 0 and 4294967295, respectively. To restore the original priority of the BGP routes during the specified duration, execute the reset bgp advertise lowest-priority command in user view.
Configuring optimal BGP EVPN route selection
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. (Optional.) Set the optimal route selection delay timer.
route-select delay delay-value
By default, the optimal route selection delay timer is 0 seconds, which means optimal route selection is not delayed.
Configuring BGP route reflection
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. Configure the device as an RR and specify a peer or peer group as its client.
peer { group-name | ipv4-address [ mask-length ] } reflect-client
By default, no RR or client is configured.
5. (Optional.) Enable BGP EVPN route reflection between clients.
reflect between-clients
By default, BGP EVPN route reflection between clients is enabled.
6. (Optional.) Configure the cluster ID of the RR.
reflector cluster-id { cluster-id | ipv4-address }
By default, an RR uses its own router ID as the cluster ID.
7. (Optional.) Create a reflection policy for the RR to filter reflected BGP EVPN routes.
rr-filter ext-comm-list-number
By default, an RR does not filter reflected BGP EVPN routes.
8. (Optional.) Enable the RR to change the attributes of routes to be reflected.
reflect change-path-attribute
By default, an RR cannot change the attributes of routes to be reflected.
Configuring the route server feature
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. Configure the device as a route server and specify a peer or peer group as a client.
peer { group-name | ipv4-address [ mask-length ] | ipv6-address [ prefix-length ] } route-server-client [ external ]
By default, neither the route server nor the client is configured.
The packets advertised to the clients does not carry the AS number of the route server. To avoid peer establishment failures, execute the peer ignore-first-as command on the clients.
Filtering BGP EVPN routes
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. Apply a routing policy to routes received from or advertised to a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] } route-policy route-policy-name { export | import }
By default, no routing policies are applied to routes received from or advertised to peers or peer groups.
5. Configure Layer 2 ACL-based route filtering.
¡ Filter routes for a peer or peer group by using a Layer 2 ACL.
peer { group-name | ipv4-address [ mask-length ] | ipv6-address [ prefix-length ] } filter-policy { mac-acl-number | name mac-acl-name } { export | import }
¡ Filter all advertised routes.
filter-policy { mac-acl-number | name mac-acl-name } export
¡ Filter all received routes.
filter-policy { mac-acl-number | name mac-acl-name } import
By default, Layer 2 ACL-based route filtering is not configured for a peer or peer group.
In a Layer 2 ACL, only the rule [ rule-id ] { deny | permit } dest-mac dest-address dest-mask rule is used to filter MAC/IP advertisement routes that carry the specified MAC addresses. The other rules in a Layer 2 ACL do not take effect in routing filtering.
6. Enable route target filtering for BGP EVPN routes.
policy vpn-target
By default, route target filtering is enabled for BGP EVPN routes.
7. Enable the device to filter advertised objects based on the first AS number in EBGP routes.
peer-as-check enable
By default, the device advertises a received EBGP route to all BGP peers except the peer that sends the EBGP route.
After you execute this command, the device checks the first AS number in the AS_Path attribute of an EBGP route when advertising the EBGP route to EBGP peers. The device will not advertise the EBGP route to the EBGP peers in that AS.
Configuring the BGP Additional Paths feature
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. Configure the BGP Additional Paths capabilities.
peer { group-name | ipv4-address [ mask-length ] | ipv6-address [ prefix-length ] } additional-paths { receive | send } *
By default, no BGP Additional Paths capabilities are configured.
5. Set the maximum number of Add-Path optimal routes that can be advertised to a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] | ipv6-address [ prefix-length ] } advertise additional-paths best number
By default, a maximum of one Add-Path optimal route can be advertised to a peer or peer group.
6. Set the maximum number of Add-Path optimal routes that can be advertised to all peers.
additional-paths select-best best-number
By default, a maximum of one Add-Path optimal route can be advertised to all peers.
Enabling the device to ignore default routes in route recursion
About this task
By default, the device selects a default route to forward traffic if only the default route is obtained after BGP route recursion. If the default route does not point to the desired next hop, traffic forwarding will fail.
To resolve this issue, enable the device to ignore default routes in route recursion. If only the default route is obtained after route recursion is performed for a BGP route, that BGP route becomes invalid, and other BGP routes with the same prefix are selected for forwarding.
Enable this feature if multiple links exist between the device and a destination IP address. If one of the links fail, traffic will be switched to the other available links instead of being incorrectly forwarded based on a default route.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. Enable the device to ignore default routes in route recursion.
nexthop recursive-lookup default-route ignore [ route-policy route-policy-name ]
By default, the device can select a default route for forwarding after performing route recursion.
|
CAUTION: After you execute this command, VXLAN tunnels might be reestablished, and transient VXLAN traffic loss might occur. As a best practice, enable BGP EVPN route reception and advertisement again after you execute this command. |
Maintaining BGP sessions
Perform the following tasks in user view:
· Reset BGP sessions of the BGP EVPN address family.
reset bgp [ instance instance-name ] { as-number | ipv4-address [ mask-length ] | all | external | group group-name | internal } l2vpn evpn
· Soft-reset BGP sessions of the BGP EVPN address family.
refresh bgp [ instance instance-name ] { ipv4-address [ mask-length ] | all | external | group group-name | internal } { export | import } l2vpn evpn
Mapping ACs to a VSI
Mapping a static Ethernet service instance to a VSI
About this task
A static Ethernet service instance matches a list of VLANs on a site-facing interface by using a frame match criterion. The VTEP assigns traffic from the VLANs to a VXLAN by mapping the Ethernet service instance to a VSI. The VSI performs Layer 2 forwarding for the VLANs based on its MAC address table.
For more information about the VXLAN commands in this task, see VXLAN Command Reference.
Restrictions and guidelines
You can create static Ethernet service instances on both a Layer 2 aggregate interface and its member ports and map the Ethernet service instances to VSIs. However, the Ethernet service instances on the aggregation member ports are down. For the Ethernet service instances to come up, you must remove the aggregation member ports from the aggregation group.
If an Ethernet service instance matches both inner and outer VLAN IDs on an interface, do not configure any other Ethernet service instances to match the same outer VLAN ID on that interface.
For information about the frame match criterion configuration restrictions and guidelines of Ethernet service instances, see VXLAN Command Reference.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
¡ Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
¡ Enter Layer 2 aggregate interface view.
interface bridge-aggregation interface-number
3. Create an Ethernet service instance and enter Ethernet service instance view.
service-instance instance-id
4. Choose one option to configure a frame match criterion.
¡ Match frames with the specified outer VLAN tags.
encapsulation s-vid vlan-id [ only-tagged ]
encapsulation s-vid vlan-id-list
¡ Match frames with the specified inner and outer VLAN tags.
encapsulation s-vid vlan-id-list c-vid vlan-id-list
encapsulation s-vid vlan-id c-vid { vlan-id-list | all }
¡ Match any VLAN tagged or untagged frames.
encapsulation { tagged | untagged }
¡ Match frames that do not match any other service instance on the interface.
encapsulation default
An interface can contain only one Ethernet service instance that uses the encapsulation default criterion.
An Ethernet service instance that uses the encapsulation default criterion matches any frames if it is the only instance on the interface.
By default, an Ethernet service instance does not contain a frame match criterion.
5. Map the Ethernet service instance to a VSI.
xconnect vsi vsi-name [ access-mode { ethernet | vlan } ] [ track track-entry-number&<1-3> ]
By default, an Ethernet service instance is not mapped to any VSI.
Mapping dynamic Ethernet service instances to VSIs
About this task
The 802.1X or MAC authentication feature can use the authorization VSI, the guest VSI, the Auth-Fail VSI, and the critical VSI to control the access of users to network resources. When assigning a user to a VSI, 802.1X or MAC authentication sends the VXLAN feature the VSI information and the user's access information, including access interface, VLAN, and MAC address. Then the VXLAN feature creates a dynamic Ethernet service instance for the user and maps it to the VSI. For more information about 802.1X authentication and MAC authentication, see Security Configuration Guide.
A dynamic Ethernet service instance supports the following traffic match modes:
· VLAN-based mode—Matches frames by VLAN ID.
· MAC-based mode—Matches frames by VLAN ID and source MAC address.
By default, dynamic Ethernet service instances use VLAN-based traffic match mode. To use MAC-based traffic match mode for dynamic Ethernet service instances, you must enable MAC authentication or 802.1X authentication that uses MAC-based access control.
Restrictions and guidelines for dynamic Ethernet service instance mappings
Dynamic Ethernet service instances cannot be created on member ports of a Layer 2 aggregation group.
Configuring the VLAN-based traffic match mode
To use the VLAN-based traffic match mode, configure 802.1X authentication or MAC authentication and perform one of the following tasks:
· Configure the guest VSI, Auth-Fail VSI, or critical VSI on the 802.1X- or MAC authentication-enabled interface.
· Issue an authorization VSI to an 802.1X or MAC authentication user from a remote AAA server.
Then, the device will automatically create a dynamic Ethernet service instance for the 802.1X or MAC authentication user and map the Ethernet service instance to a VSI.
For more information about configuring 802.1X authentication and MAC authentication, see Security Configuration Guide.
Configuring the MAC-based traffic match mode
1. Enter system view.
system-view
2. Enter interface view.
¡ Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
¡ Enter Layer 2 aggregate interface view.
interface bridge-aggregation interface-number
3. Enable MAC-based traffic match mode for dynamic Ethernet service instances on the interface.
mac-based ac
By default, VLAN-based traffic match mode is used for dynamic Ethernet service instances.
For more information about this command, see VXLAN Command Reference.
4. Enable MAC authentication or 802.1X authentication that uses MAC-based access control.
To use the MAC-based traffic match mode, configure MAC authentication or 802.1X authentication that uses MAC-based access control and perform one of the following tasks:
¡ Configure the guest VSI, Auth-Fail VSI, or critical VSI on the 802.1X- or MAC authentication-enabled interface.
¡ Issue an authorization VSI to an 802.1X or MAC authentication user from a remote AAA server.
Then, the device will automatically create a dynamic Ethernet service instance for the 802.1X or MAC authentication user and map the Ethernet service instance to a VSI.
For more information about configuring 802.1X authentication and MAC authentication, see Security Configuration Guide.
Configuring a centralized EVPN gateway
Restrictions and guidelines for centralized EVPN gateway configuration
If an EVPN network contains a centralized EVPN gateway, you must enable ARP or ND flood suppression on VTEPs. Typically remote ARP or ND learning is disabled in an EVPN network. When ARP or ND requests for the gateway MAC address are sent to the centralized EVPN gateway through VXLAN tunnels, the gateway does not respond to the requests. If ARP or ND flood suppression is disabled on VTEPs, VMs cannot obtain the MAC address of the gateway.
Prerequisites for centralized EVPN gateway configuration
Before you configure a centralized EVPN gateway, set the VXLAN hardware resource mode to Layer 3 gateway.
Configuring a centralized gateway interface
1. Enter system view.
system-view
2. Create a VSI interface and enter VSI interface view.
interface vsi-interface vsi-interface-id
For more information about this command, see VXLAN Command Reference.
3. Assign an IP address to the VSI interface.
ip address ip-address { mask | mask-length } [ sub ]
By default, no IP address is assigned to a VSI interface.
4. Return to system view.
quit
5. Enter VSI view.
vsi vsi-name
6. Specify the VSI interface as the gateway interface for the VSI.
gateway vsi-interface vsi-interface-id
By default, no gateway interface is specified for a VSI.
For more information about this command, see VXLAN Command Reference.
Setting the static flag for the MAC addresses of centralized gateway interfaces
About this task
In a network with a centralized EVPN gateway deployed, a VTEP considers a MAC address move occurs if an endpoint uses a MAC address identical to that of a centralized gateway interface. As a result, the VTEP overwrites the MAC address entry created for the centralized gateway interface with that created for the endpoint, and errors will occur in traffic forwarding.
To resolve this issue, set the static flag for the MAC addresses of centralized gateway interfaces on the centralized EVPN gateway. When advertising those MAC addresses through MAC/IP advertisement routes, the centralized EVPN gateway will set the static flag bit to 1 in the MAC mobility extended community. If an endpoint accesses the network with a MAC address identical to that of a centralized gateway interface, the endpoint's MAC address entry will not overwrite the entry for the centralized gateway interface.
Procedure
1. Enter system view.
system-view
2. Set the static flag for the MAC addresses of centralized gateway interfaces.
evpn route gateway-mac unmovable
By default, the static flag is not set for the MAC addresses of centralized gateway interfaces.
Configuring a distributed EVPN gateway
Restrictions and guidelines for distributed EVPN gateway configuration
When you configure VSI interfaces on a distributed EVPN gateway, follow these restrictions and guidelines:
· Do not assign reserved MAC addresses to VSI interfaces.
· You must assign the same MAC address to the VSI interfaces with L3 VXLAN IDs associated.
· On distributed EVPN gateways, you must assign the same MAC address and IP address to the VSI interfaces that act as the gateway for the same VXLAN.
· If a distributed EVPN gateway is connected to an IPv6 site, make sure the VSI interfaces with L3 VXLAN IDs associated use the same link-local address.
As a best practice, do not use ARP flood suppression and local proxy ARP or ND flood suppression and local ND proxy together on distributed EVPN gateways. If both ARP flood suppression and local proxy ARP are enabled on a distributed EVPN gateway, only local proxy ARP takes effect. If both ND flood suppression and local ND proxy are enabled on a distributed EVPN gateway, only local ND proxy takes effect.
On a distributed EVPN gateway, make sure the VSI interfaces configured with L3 VXLAN IDs use the same MAC address. To modify the MAC address of a VSI interface, use the mac-address command.
Prerequisites for distributed EVPN gateway configuration
Before you configure a distributed EVPN gateway, set the VXLAN hardware resource mode to Layer 3 gateway.
For a VXLAN to access the external network, specify the VXLAN's VSI interface on the border gateway as the next hop on distributed EVPN gateways by using one of the following methods:
· Configure a static route.
· Configure a routing policy, and apply the policy by using the apply default-next-hop or apply next-hop command. For more information about configuring routing policies, see routing policy configuration in Layer 3—IP Routing Configuration Guide.
Configuring the traffic forwarding mode for EVPN VXLAN
Restrictions and guidelines
The asymmetric IRB mode is supported only on distributed EVPN gateways. The mode takes effect only on Layer 3 traffic forwarded in the same VXLAN. In addition, the same VSI interface on different distributed EVPN gateways must have different IP addresses.
Procedure
1. Enter system view.
system-view
2. Configure the traffic forwarding mode for EVPN VXLAN. Choose one of the following options:
¡ Enable asymmetric IRB mode.
evpn irb asymmetric [ route-policy route-policy-name ]
¡ Enable symmetric IRB mode.
undo evpn irb asymmetric
By default, a distributed EVPN gateway forwards EVPN VXLAN traffic in symmetric IRB mode.
Configuring a VSI interface
About this task
To save Layer 3 interface resources on a distributed EVPN gateway, multiple VSIs can share one VSI interface. You can assign multiple IP addresses to the VSI interface for the VSIs to use as gateway addresses.
When VSIs share a VSI interface, you must specify the subnet of each VSI for the VSI interface to identify the VSI of a packet. The subnets must be unique.
Procedure
1. Enter system view.
system-view
2. Create a VSI interface and enter VSI interface view.
interface vsi-interface vsi-interface-id
For more information about this command, see VXLAN Command Reference.
3. Assign an IP address to the VSI interface.
IPv4:
ip address ip-address { mask | mask-length } [ sub ]
IPv6:
See IPv6 basics in Layer 3—IP Services Configuration Guide.
By default, no IP address is assigned to a VSI interface.
4. Assign a MAC address to the VSI interface.
mac-address mac-address
The default MAC address of VSI interfaces is the same as the default MAC address of Layer 3 Ethernet interfaces.
To ensure correct forwarding after VM migration, you must assign the same MAC address to the VSI interfaces of a VXLAN on all distributed gateways.
5. Specify the VSI interface as a distributed gateway.
distributed-gateway local
By default, a VSI interface is not a distributed gateway.
For more information about this command, see VXLAN Command Reference.
6. (Optional.) Enable local proxy ARP or local ND proxy.
IPv4:
local-proxy-arp enable [ ip-range startIP to endIP ]
By default, local proxy ARP is disabled.
For more information about the command, see proxy ARP commands in Layer 3—IP Services Command Reference.
IPv6:
local-proxy-nd enable
By default, local ND proxy is disabled.
For more information about the commands, see IPv6 basic commands Layer 3—IP Services Command Reference.
7. Return to system view.
quit
8. Enter VSI view.
vsi vsi-name
9. Specify the VSI interface as the gateway interface for the VSI.
gateway vsi-interface vsi-interface-id
By default, no gateway interface is specified for a VSI.
For more information about this command, see VXLAN Command Reference.
10. Assign a subnet to the VSI.
gateway subnet { ipv4-address wildcard-mask | ipv6-address prefix-length }
By default, no subnet exists on a VSI.
For more information about this command, see VXLAN Command Reference.
Configuring an L3 VXLAN ID for a VSI interface
Restrictions and guidelines for L3 VXLAN ID configuration
The L3 VXLAN ID of a VSI interface cannot be the same as the VXLAN ID specified by using the mapping vni command. For more information about this command, see "Configuring EVPN-DCI."
Configuring an L3 VXLAN ID for the VSI interface of a VPN instance
1. Enter system view.
system-view
2. Configure a VPN instance:
a. Create a VPN instance and enter VPN instance view.
ip vpn-instance vpn-instance-name
b. Configure an RD for the VPN instance.
route-distinguisher route-distinguisher
By default, no RD is configured for a VPN instance.
c. Configure route targets for the VPN instance.
vpn-target { vpn-target&<1-8> [ both | export-extcommunity | import-extcommunity ]
By default, a VPN instance does not have route targets.
d. (Optional.) Apply an export routing policy to the VPN instance.
export route-policy route-policy
By default, no export routing policy is applied to a VPN instance.
The specified export routing policy is used to filter the BGP EVPN routes advertised for the VPN instance.
e. (Optional.) Apply an import routing policy to the VPN instance.
import route-policy route-policy
By default, no import routing policy is applied to a VPN instance. The VPN instance accepts a route when the export route targets of the route match local import route targets.
The specified import routing policy is used to filter the BGP EVPN routes redistributed to the VPN instance.
3. Configure EVPN on the VPN instance:
a. Enter VPN instance EVPN view.
address-family evpn
b. Configure route targets for EVPN on the VPN instance.
vpn-target vpn-target&<1-8> [ both | export-extcommunity | import-extcommunity ]
By default, EVPN does not have route targets on a VPN instance.
Make sure the following requirements are met:
- The import targets of EVPN do not match the export targets of the VPN instance.
- The export targets of EVPN do not match the import targets of the VPN instance.
c. (Optional.) Apply an export routing policy to EVPN on the VPN instance.
export route-policy route-policy
By default, no export routing policy is applied to EVPN on a VPN instance.
d. (Optional.) Apply an import routing policy to EVPN on the VPN instance.
import route-policy route-policy
By default, no import routing policy is applied to EVPN on a VPN instance. The VPN instance accepts a route when the route targets of the route match local import route targets.
4. Execute the following commands in sequence to return to system view.
a. quit
b. quit
5. Create a VSI interface and enter VSI interface view.
interface vsi-interface vsi-interface-id
6. Associate the VSI interface with the VPN instance.
ip binding vpn-instance vpn-instance-name
By default, a VSI interface is not associated with a VPN instance. The interface is on the public network.
7. Configure an L3 VXLAN ID for the VSI interface.
l3-vni vxlan-id
By default, no L3 VXLAN ID is configured for a VSI interface.
A VPN instance can have only one L3 VXLAN ID. If multiple L3 VXLAN IDs are configured for a VPN instance, the VPN instance uses the lowest one. To view the L3 VXLAN ID of a VPN instance, use the display evpn routing-table command.
Configuring an L3 VXLAN ID for the VSI interface of the public instance
1. Enter system view.
system-view
2. Create the public instance and enter its view.
ip public-instance
For more information about this command, see MPLS L3VPN commands in MPLS Command Reference.
3. Configure an RD for the public instance.
route-distinguisher route-distinguisher
By default, no RD is configured for the public instance.
4. Configure an L3 VXLAN ID for the public instance.
l3-vni vxlan-id
By default, the public instance does not have an L3 VXLAN ID.
The public instance can have only one L3 VXLAN ID. To modify the L3 VXLAN ID for the public instance, you must first delete the original L3 VXLAN ID.
5. (Optional.) Configure route targets for the public instance.
vpn-target vpn-target&<1-8> [ both | export-extcommunity | import-extcommunity ]
By default, the public instance does not have route targets.
6. Enter IPv4 address family view, IPv6 address family view, or EVPN view.
¡ Enter IPv4 address family view.
address-family ipv4
For more information about this command, see MPLS L3VPN commands in MPLS Command Reference.
¡ Enter IPv6 address family view.
address-family ipv6
For more information about this command, see MPLS L3VPN commands in MPLS Command Reference.
¡ Enter EVPN view.
address-family evpn
7. Configure route targets for the IPv4 address family, IPv6 address family, or EVPN.
vpn-target vpn-target&<1-8> [ both | export-extcommunity | import-extcommunity ]
By default, the IPv4 address family, IPv6 address family, and EVPN do not have route targets on the public instance.
Make sure the following requirements are met:
¡ The import targets of an EVPN instance do not match the export targets of the public instance.
¡ The export targets of an EVPN instance do not match the import targets of the public instance.
8. Execute the following commands in sequence to return to system view.
a. quit
b. quit
9. Enter VSI interface view.
interface vsi-interface vsi-interface-id
10. Configure an L3 VXLAN ID for the VSI interface.
l3-vni vxlan-id
By default, no L3 VXLAN ID is configured for a VSI interface.
Of the VSI interfaces associated with the public instance, a minimum of one VSI interface must use the same L3 VXLAN ID as the public instance.
Configuring IP prefix route advertisement
About this task
If IGP routes are imported to the BGP-VPN IPv4 or IPv6 unicast address family and the corresponding VPN instance has an L3 VXLAN ID, the device advertises the imported routes as IP prefix advertisement routes.
If IGP routes are imported to the BGP IPv4 or IPv6 unicast address family and the public instance has an L3 VXLAN ID, the device advertises the imported routes as IP prefix advertisement routes.
A VTEP compares the export route targets of received IP prefix advertisement routes with the import route targets configured for the IPv4 address family or IPv6 address family on a VPN instance or the public instance. If the route targets match, the VTEP accepts the routes and adds the routes to the routing table of the VPN instance or public instance.
Restrictions and guidelines
This feature is supported only by distributed EVPN gateway deployment.
For more information about the BGP commands in this task, see Layer 3—IP Routing Command Reference.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP address family view.
¡ Enter BGP IPv4 unicast address family view.
address-family ipv4 [ unicast ]
¡ Execute the following commands in sequence to enter BGP-VPN IPv4 unicast address family view.
ip vpn-instance vpn-instance-name
address-family ipv4 [ unicast ]
¡ Enter BGP IPv6 unicast address family view.
address-family ipv6 [ unicast ]
¡ Execute the following commands in sequence to enter BGP-VPN IPv6 unicast address family view.
ip vpn-instance vpn-instance-name
address-family ipv6 [ unicast ]
4. Enable BGP to redistribute routes from an IGP protocol.
import-route protocol [ { process-id | all-processes } [ allow-direct | med med-value | route-policy route-policy-name ] * ]
By default, BGP does not redistribute IGP routes.
5. (Optional.) Enable default route redistribution into the BGP routing table.
default-route imported
By default, default route redistribution into the BGP routing table is disabled.
6. (Optional.) Configure ECMP VPN route redistribution:
a. Return to BGP instance view.
quit
b. Enter BGP EVPN address family view.
address-family l2vpn evpn
c. Enable ECMP VPN route redistribution.
vpn-route cross multipath
By default, ECMP VPN route redistribution is disabled. If multiple routes have the same prefix and RD, BGP only imports the optimal route into the EVPN routing table.
ECMP VPN route redistribution enables BGP to import all routes that have the same prefix and RD into the EVPN routing table.
Configuring BGP route exchange between the public instance and VPN instances
About this task
By default, the BGP routes of one VPN instance are isolated from those of another VPN instance. If inter-VPN route exchange is required and the routes of a VPN instance must be hidden, configure other VPN instances to advertise routes of that VPN instance.
Figure 19 BGP route exchange between the public instance and VPN instances
As shown in Figure 19, PE 1 and PE 2 set up public IBGP sessions with PE 3, and the public instance and VPN instances exchange routes to enable communication between the public network and the VPN sites. PE 1 and PE 2 set up BGP EVPN IBGP peer relationships with each other to exchange VPN instance routes. When all links operate correctly, PE 2 receives the public routes advertised by PE 3 and redistributes the routes to the local VPN site. When the link between PE 2 and PE 3 fails, perform the following tasks for PE 1 to reoriginate the public routes in a specified VPN instance and advertise them to PE 2:
1. Configure route targets for the public instance on PE 1. Make sure the route targets match those of the VPN instance to redistribute public routes.
2. Execute the route-replicate enable command on PE 1 to redistribute the BGP routes of the public instance to the target VPN instance.
3. Execute the advertise route-reoriginate command on PE 1 to enable reoriginating the BGP routes of other VPN instances in the target VPN instance. This command enables reoriginating BGP routes based on only the BGP routes that match the route targets of the target VPN instance. The VPN instance does not reoriginate BGP routes based on the redistributed local routes, such as the IGP routes redistributed by using the import-route command.
4. Execute the peer advertise vpn-reoriginate ibgp command on PE 1 to advertised reoriginated routes to IBGP peer PE 2.
Restrictions and guidelines
You must use the peer advertise vpn-reoriginate ibgp command in combination with the advertise route-reoriginate command. If you execute only the peer advertise vpn-reoriginate ibgp command, it does not take effect.
In BGP-VPN IPv4 unicast address family view, the advertise route-reoriginate command enables reoriginating IPv4 unicast routes. In BGP-VPN IPv6 unicast address family view, the advertise route-reoriginate command enables reoriginating IPv6 unicast routes.
For more information about the advertise route-reoriginate and route-replicate enable commands, see MPLS L3VPN commands in MPLS Command Reference.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. (Optional.) Enable BGP route replication between public and VPN instances.
route-replicate enable
By default, BGP route replication between public and VPN instances is disabled
4. Enter BGP address family view.
¡ Execute the following commands in sequence to enter BGP-VPN IPv4 unicast address family view.
ip vpn-instance vpn-instance-name
address-family ipv4 [ unicast ]
¡ Execute the following commands in sequence to enter BGP-VPN IPv6 unicast address family view.
ip vpn-instance vpn-instance-name
address-family ipv6 [ unicast ]
5. Enable reoriginating BGP routes for a VPN instance based on the BGP routes received from other VPN instances.
advertise route-reoriginate [ route-policy route-policy-name ] [ replace-rt ]
By default, a VPN instance does not reoriginate BGP unicast routes for the BGP routes of other VPN instances.
This command enables reoriginating BGP routes based on only the BGP routes that match the route targets of the current VPN instance. The VPN instance does not reoriginate BGP routes based on the redistributed local routes.
6. (Optional.) Enable advertising the IP prefix advertisement routes reoriginated for a VPN instance to an IBGP peer or peer group.
a. Return to BGP instance view.
quit
quit
b. Enter BGP EVPN address family view.
address-family l2vpn evpn
c. Enable advertising the IP prefix advertisement routes reoriginated for a VPN instance to an IBGP peer or peer group.
peer { group-name | ipv4-address [ mask-length ] } advertise vpn-reoriginate ibgp
By default, the device does not advertise the IP prefix advertisement routes reoriginated for a VPN instance to IBGP peers or peer groups.
Configuring the EVPN global MAC address
About this task
The EVPN global MAC address is used only by VSI interfaces associated with an L3 VXLAN ID. For such a VSI interface, the MAC address assigned to it by using the mac-address command takes precedence over the EVPN global MAC address.
A distributed EVPN gateway selects the lowest-numbered VSI interface that is associated with an L3 VXLAN ID as its router MAC address. In an M-LAG system, distributed EVPN gateways that act as M-LAG member devices might use different router MAC addresses, which causes forwarding errors. To resolve this problem, you can configure the same EVPN global MAC address on the gateways.
Restrictions and guidelines
Configure the same EVPN global MAC address on the M-LAG member devices of an M-LAG system. Make sure the EVPN global MAC address of an M-LAG system is unique in the local data center and the remote data centers connected to the local data center through DCI tunnels.
As a best practice, use one of the following methods to configure the EVPN global MAC address on an M-LAG system:
· Use the default MAC address of a Layer 3 Ethernet interface on an M-LAG member device as the EVPN global MAC address. As a best practice, use this method.
· Use an available unicast MAC address in the range of 0001-0001-0001 to 0001-0001-FFFE as the EVPN global MAC address.
For a VSI interface associated with an L3 VXLAN ID, the MAC address assigned to it by using the mac-address command takes precedence over the EVPN global MAC address.
Procedure
1. Enter system view.
system-view
2. Configure the EVPN global MAC address.
evpn global-mac mac-address
By default, no EVPN global MAC address is configured.
Disabling generation of IP prefix advertisement routes for the subnets of a VSI interface
About this task
A distributed VXLAN IP gateway by default generates IP prefix advertisement routes for the subnets of VSI interfaces and advertises these routes to remote VTEPs. The remote VTEPs advertise these routes to their local sites. To disable advertisement of these routes to remote sites, you can disable generation of IP prefix advertisement routes for the subnets of VSI interfaces.
Restrictions and guidelines
This feature takes effect only on a VSI interface that provides distributed VXLAN IP gateway service (configured by using the distributed-gateway local command). It does not take effect on VSI interfaces that provide centralized VXLAN IP gateway service. The device only generates MAC/IP advertisement routes for VSI interfaces that provide centralized VXLAN IP gateway service.
Procedure
1. Enter system view.
system-view
2. Enter VSI interface view.
interface vsi-interface vsi-interface-id
3. Disable generation of IP prefix advertisement routes for the subnets of the VSI interface.
ip-prefix-route generate disable
By default, the device generates IP prefix advertisement routes for the subnets of a VSI interface that provides distributed VXLAN IP gateway service.
Enabling a distributed EVPN gateway to send RA messages over VXLAN tunnels
About this task
By default, a distributed EVPN gateway drops the RS messages received from VXLAN tunnels and periodically advertises RA messages only to the local site. As a result, a distributed EVPN gateway does not send RA messages over VXLAN tunnels, and remote gateways cannot update information about the gateway based on RA messages. To resolve the issue, perform this task to enable distributed EVPN gateways to reply to remote RS messages with RA messages and periodically advertise RA messages over VXLAN tunnels.
Restrictions and guidelines
You can configure RA message tunneling for VSI interfaces globally or on a per-VSI interface basis. The global configuration takes effect on all VSI interfaces. The interface-specific configuration takes precedence over the global configuration on a VSI interface.
Globally enabling VSI interfaces to send RA messages over VXLAN tunnels
1. Enter system view.
system-view
2. Globally enable VSI interfaces to send RA messages over VXLAN tunnels.
ipv6 nd ra tunnel-broadcast global enable
By default, VSI interfaces do not send RA messages over VXLAN tunnels.
Enabling a VSI interface to send RA messages over VXLAN tunnels
1. Enter system view.
system-view
2. Enter VSI interface view.
interface vsi-interface vsi-interface-id
3. Enable the VSI interface to send RA messages over VXLAN tunnels.
ipv6 nd ra tunnel-broadcast enable
By default, a VSI interface uses the global RA message tunneling configuration.
Enabling traffic statistics for the VSIs automatically created for L3 VXLAN IDs
About this task
If you configure an L3 VXLAN ID on a distributed EVPN gateway, the gateway automatically creates a VSI for the L3 VXLAN ID. You cannot enter the view of such a VSI to configure settings on it.
This task enables the device to collect incoming and outgoing traffic statistics for the automatically created VSIs. You can use the display l2vpn vsi verbose command to view the traffic statistics and use the reset l2vpn statistics vsi command to clear the traffic statistics.
Procedure
1. Enter system view.
system-view
2. Enable traffic statistics for the VSIs that are automatically created for L3 VXLAN IDs.
l2vpn statistics vsi l3-vni
By default, the traffic statistics feature is disabled for the VSIs that are automatically created for L3 VXLAN IDs.
Enabling the device to advertise ARP information for the distributed EVPN gateway interfaces through MAC/IP advertisement routes
About this task
If a distributed EVPN gateway has downstream VTEPs attached, the gateway advertises ARP information for gateway interfaces through IP prefix advertisement routes. Because the VTEPs do not have gateway configuration, they cannot learn the ARP information for the gateway interfaces or forward traffic to the gateway. For the VTEPs to learn ARP information for the gateway interfaces, enable the distributed EVPN gateway to advertise ARP information for the gateway interfaces through MAC/IP advertisement routes.
Procedure
1. Enter system view.
system-view
2. Enable the device to advertise ARP information for the distributed EVPN gateway interfaces through MAC/IP advertisement routes.
evpn mac-ip advertise distributed-gateway
By default, the device does not advertise ARP information for the distributed EVPN gateway interfaces through MAC/IP advertisement routes.
Managing remote MAC address entries and remote ARP or ND learning
Disabling remote MAC address learning and remote ARP or ND learning
About this task
By default, the device learns MAC information, ARP information, and ND information of remote user terminals from packets received on VXLAN tunnel interfaces. The automatically learned remote MAC, ARP, and ND information might conflict with the remote MAC, ARP, and ND information advertised through BGP. As a best practice to avoid the conflicts, disable remote MAC address learning and remote ARP or ND learning on the device.
For more information about the VXLAN commands in this task, see VXLAN Command Reference.
Procedure
1. Enter system view.
system-view
2. Disable remote MAC address learning.
vxlan tunnel mac-learning disable
By default, remote MAC address learning is enabled.
3. Disable remote ARP learning.
vxlan tunnel arp-learning disable
By default, remote ARP learning is enabled.
4. Disable remote ND learning.
vxlan tunnel nd-learning disable
By default, remote ND learning is enabled.
Disabling MAC address advertisement
About this task
The MAC information and ARP or ND information advertised by the VTEP overlap. To avoid duplication, disable MAC address advertisement and withdraw the MAC addresses advertised to remote VTEPs.
Procedure (EVPN instance view)
1. Enter system view.
system-view
2. Enter EVPN instance view.
evpn instance instance-name
3. Disable MAC address advertisement and withdraw advertised MAC addresses.
mac-advertising disable
By default, MAC address advertisement is enabled.
Procedure (VSI EVPN instance view)
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Enter VSI EVPN instance view.
evpn encapsulation vxlan
4. Disable MAC address advertisement and withdraw advertised MAC addresses.
mac-advertising disable
By default, MAC address advertisement is enabled.
Enabling MAC mobility event suppression
About this task
On an EVPN VXLAN network, misconfiguration of MAC addresses might cause two sites to contain the same MAC address. In this condition, VTEPs at the two sites constantly synchronize and update EVPN MAC entries and determine that MAC mobility events occur. As a result, an inter-site loop might occur, and the bandwidth is occupied by MAC entry synchronization traffic. To eliminate loops and suppress those MAC mobility events, enable MAC mobility event suppression on the VTEPs. This feature allows a MAC address to move a specified number of times (the MAC mobility suppression threshold) from a site within a MAC mobility detection cycle. If a MAC address moves more than the MAC mobility suppression threshold, the VTEP at the site will suppress the last MAC move to the local site and will not advertise information about the MAC address.
Restrictions and guidelines
After you execute the undo evpn route mac-mobility suppression command or the suppression time expires, a VTEP acts as follows:
· Advertises MAC address entries immediately for the suppressed MAC address entries that have not aged out.
· Relearns the MAC addresses for the suppressed MAC address entries that have aged out and advertises the MAC address entries.
If both MAC address entry conflicts and ARP entry conflicts exist for a MAC address, you must enable both MAC mobility event suppression and ARP mobility event suppression. If you enable only MAC mobility event suppression, the system cannot suppress MAC mobility events for the MAC address.
Procedure
1. Enter system view.
system-view
2. Enable MAC mobility event suppression.
evpn route mac-mobility suppression [ detect-cycle detect-time | detect-threshold move-times | suppression-time [ suppression-time | permanent ] ] *
By default, MAC mobility event suppression is disabled.
Disabling learning of MAC addresses from ARP or ND information
About this task
The MAC information and ARP or ND information advertised by a remote VTEP overlap. To avoid duplication, disable the learning of MAC addresses from ARP or ND information. EVPN will learn remote MAC addresses only from the MAC information advertised from remote sites.
Procedure (EVPN instance view)
1. Enter system view.
system-view
2. Enter EVPN instance view.
evpn instance instance-name
3. Disable the EVPN instance from learning MAC addresses from ARP information.
arp mac-learning disable
By default, an EVPN instance learns MAC addresses from ARP information.
4. Disable the EVPN instance from learning MAC addresses from ND information.
nd mac-learning disable
By default, an EVPN instance learns MAC addresses from ND information.
Procedure (VSI EVPN instance view)
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Enter VSI EVPN instance view.
evpn encapsulation vxlan
4. Disable the EVPN instance from learning MAC addresses from ARP information.
arp mac-learning disable
By default, an EVPN instance learns MAC addresses from ARP information.
5. Disable the EVPN instance from learning MAC addresses from ND information.
nd mac-learning disable
By default, an EVPN instance learns MAC addresses from ND information.
Disabling ARP information advertisement
About this task
In an EVPN network with distributed gateways, you can disable ARP information advertisement for a VXLAN to save resources if all its user terminals use the same EVPN gateway device. The EVPN instance of the VXLAN will stop advertising ARP information through MAC/IP advertisement routes and withdraw advertised ARP information. When ARP information advertisement is disabled, user terminals in other VXLANs still can communicate with that VXLAN through IP prefix advertisement routes.
Procedure (EVPN instance view)
1. Enter system view.
system-view
2. Enter EVPN instance view.
evpn instance instance-name
3. Disable ARP information advertisement for the EVPN instance.
arp-advertising disable
By default, ARP information advertisement is enabled for an EVPN instance.
Procedure (VSI EVPN instance view)
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Enter VSI EVPN instance view.
evpn encapsulation vxlan
4. Disable ARP information advertisement for the EVPN instance.
arp-advertising disable
By default, ARP information advertisement is enabled for an EVPN instance.
Enabling ND information advertisement
About this task
In an EVPN network with distributed gateways, you can disable ND information advertisement for a VXLAN to save resources if all its user terminals use the same EVPN gateway device. The EVPN instance of the VXLAN will stop advertising ND information through MAC/IP advertisement routes and withdraw advertised ND information. When ND information advertisement is disabled, user terminals in other VXLANs still can communicate with that VXLAN through IP prefix advertisement routes.
Procedure (EVPN instance view)
1. Enter system view.
system-view
2. Enter EVPN instance view.
evpn instance instance-name
3. Enable ND information advertisement for the EVPN instance.
nd-advertising enable
By default, ND information advertisement is enabled for an EVPN instance.
Procedure (VSI EVPN instance view)
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Enter VSI EVPN instance view.
evpn encapsulation vxlan
4. Enable ND information advertisement for the EVPN instance.
nd-advertising disable
By default, ND information advertisement is enabled for an EVPN instance.
Disabling the VSI interface on a centralized EVPN gateway from learning ARP or ND information across subnets
About this task
On an EVPN VXLAN network deployed with a centralized EVPN gateway, VM 1 and VM 2 belong to the same VXLAN in subnet 10.1.1.0/24. The gateway interface is VSI-interface 1 and the gateway is connected to external Layer 3 network 10.1.2.0/24. The VTEP to which VM 2 is attached is configured with ARP or ND flood suppression. The IP address of VM 2 is mistakenly configured as an IP address in subnet 10.1.2.0/24 (for example, 10.1.2.2). In this situation, the VTEP connected to VM 2 advertises MAC/IP advertisement routes that contain ARP or ND information to the gateway. The IP address and MAC address in the routes are the IP address and MAC address of VM 2, respectively. The gateway learns the ARP or ND information and issues the information to the forwarding table. When VM 1 visits 10.1.2.2 in the external network, the gateway will forward the traffic to VM 2. As a result, VM 1 cannot visit 10.1.2.2.
To resolve the above issue, perform this task on the VSI interface to disable the VSI interface from learning ARP or ND information across subnets from MAC/IP advertisement routes.
Procedure
1. Enter system view.
system-view
2. Enter VSI interface view on a centralized EVPN gateway.
interface vsi-interface vsi-interface-id
For more information about this command, see VXLAN Command Reference.
3. Disable the VSI interface from learning ARP or ND information that does not belong to its subnet from MAC/IP advertisement routes.
evpn span-segment { arp-learning | nd-learning } disable
By default, the VSI interface on a centralized EVPN gateway learns ARP or ND information that does not belong to its subnet from MAC/IP advertisement routes.
Enabling ARP mobility event suppression
About this task
On an EVPN VXLAN network, misconfiguration of IP addresses might cause two sites to contain the same IP address. In this condition, VTEPs at the two sites constantly synchronize and update EVPN ARP entries and determine that ARP mobility events occur. As a result, an inter-site loop might occur, and the bandwidth is occupied by ARP entry synchronization traffic. To eliminate loops and suppress those ARP mobility events, enable ARP mobility event suppression on the VTEPs. This feature allows an IP address to move a specified number of times (the ARP mobility suppression threshold) from a site within an ARP mobility detection cycle. If an IP address moves more than the ARP mobility suppression threshold, the VTEP at the site will suppress the last ARP move to the local site and will not advertise ARP information for the IP address.
Restrictions and guidelines
ARP mobility event suppression takes effect only on an EVPN VXLAN network configured with distributed VXLAN IP gateways.
After you execute the undo evpn route arp-mobility suppression command or the suppression time expires, a VTEP acts as follows:
· Advertises ARP information immediately for the suppressed ARP entries that have not aged out.
· Relearns ARP information for the suppressed ARP entries that have aged out and advertises the ARP information.
If both MAC address entry conflicts and ARP entry conflicts exist for a MAC address, you must enable both MAC mobility event suppression and ARP mobility event suppression. If you enable only MAC mobility event suppression, the system cannot suppress MAC mobility events for the MAC address.
Procedure
1. Enter system view.
system-view
2. Enable ARP mobility event suppression.
evpn route arp-mobility suppression [ detect-cycle detect-time | detect-threshold move-times | suppression-time [ suppression-time | permanent ] ] *
By default, ARP mobility event suppression is disabled.
Enabling ND mobility event suppression
About this task
On an EVPN VXLAN network, misconfiguration of IP addresses might cause two sites to contain the same IP address. In this condition, VTEPs at the two sites constantly synchronize and update EVPN ND entries and determine that ND mobility events occur. As a result, an inter-site loop might occur, and the bandwidth is occupied by ND entry synchronization traffic. To eliminate loops and suppress those ND mobility events, enable ND mobility event suppression on the VTEPs. This feature allows an IP address to move a specified number of times (the ND mobility suppression threshold) from a site within an ND mobility detection cycle. If an IP address moves more than the ND mobility suppression threshold, the VTEP at the site will suppress the last ND move to the local site and will not advertise ND information for the IP address.
Restrictions and guidelines
After you execute the undo evpn route nd-mobility suppression command or the suppression time expires, a VTEP acts as follows:
· Advertises ND information immediately for the suppressed ND entries that have not aged out.
· Relearns ND information for the suppressed ND entries that have aged out and advertises the ND information.
ND mobility event suppression takes effect only on the following EVPN VXLAN networks:
· EVPN VXLAN network enabled with ND flood suppression.
· EVPN VXLAN network configured with distributed VXLAN IP gateways.
If both MAC address entry conflicts and ND entry conflicts exist for a MAC address, you must enable both MAC mobility event suppression and ND mobility event suppression. If you enable only MAC mobility event suppression, the system cannot suppress MAC mobility events for the MAC address.
Procedure
1. Enter system view.
system-view
2. Enable ND mobility event suppression.
evpn route nd-mobility suppression [ detect-cycle detect-time | detect-threshold move-times | suppression-time [ suppression-time | permanent ] ] *
By default, ND mobility event suppression is disabled.
Enabling ARP request proxy
About this task
ARP request proxy allows a VSI interface to send an ARP request sourced from itself when the VTEP forwards an ARP request. This feature helps resolve certain communication issues.
In an EVPN VXLAN network, VM 1 and VM 2 are attached to VTEP 1 and VTEP 2, respectively, and the VMs are in the same subnet. The gateway interfaces of VM 1 and VM 2 are VSI-interface 1 on VTEP 1 and VSI-interface 2 on VTEP 2, respectively. The following conditions exist on the VTEPs:
· The VTEPs have established BGP EVPN neighbor relationships.
· EVPN is disabled from learning MAC addresses from ARP information.
· MAC address advertisement is disabled, and advertised MAC addresses are withdrawn.
· Remote-MAC address learning is disabled.
· Local proxy ARP is enabled on the VSI interfaces.
· The VSI interfaces use different IP addresses and MAC addresses.
In this network, when VM 1 attempts to communicate with VM 2, the following procedure occurs:
1. VM 1 sends an ARP request.
2. VTEP 1 learns the MAC address of VM 1 from the ARP request, replies to VM 1 on behalf of VM 2, and sends an ARP request to obtain the MAC address of VM 2.
3. VTEP 2 forwards the ARP request, and VM 2 replies to VTEP 1.
4. VTEP 2 forwards the ARP reply sent by VM 2 without learning the MAC address of VM 2 because EVPN is disabled from learning MAC addresses from ARP information.
5. VTEP 1 does not learn the MAC address of VM 2 because remote-MAC address learning is disabled.
As a result, VM 1 fails to communicate with VM 2.
For VM 1 to communicate with VM 2, enable ARP request proxy on VSI-interface 2 of VTEP 2. When receiving the ARP request sent by VTEP 1, VTEP 2 forwards it and sends an ARP request sourced from VSI-interface 2 simultaneously, and VM 2 replies to both ARP requests. Then, VTEP 2 learns the MAC address of VM 2 from the ARP reply destined from VSI-interface 2 and advertises the MAC address to VTEP 1 through BGP EVPN routes. In this way, VTEP 1 obtains the MAC address of VM 2, and VM 1 and VM 2 can communicate.
Procedure
1. Enter system view.
system-view
2. Enter VSI interface view.
interface vsi-interface vsi-interface-id
3. Enable ARP request proxy.
arp proxy-send enable
By default, ARP request proxy is disabled on VSI interfaces.
Enabling ND request proxy
About this task
ND request proxy allows a VSI interface to send an ND request sourced from itself when the VTEP forwards an ND request. This feature helps resolve certain communication issues.
In an EVPN VXLAN network, VM 1 and VM 2 are attached to VTEP 1 and VTEP 2, respectively, and the VMs are in the same subnet. The gateway interfaces of VM 1 and VM 2 are VSI-interface 1 on VTEP 1 and VSI-interface 2 on VTEP 2, respectively. The following conditions exist on the VTEPs:
· The VTEPs have established BGP EVPN neighbor relationships.
· EVPN is disabled from learning MAC addresses from ND information.
· MAC address advertisement is disabled, and advertised MAC addresses are withdrawn.
· Remote-MAC address learning is disabled.
· Local proxy ND is enabled on the VSI interfaces.
· The VSI interfaces use different IP addresses and MAC addresses.
In this network, when VM 1 attempts to communicate with VM 2, the following process occurs:
1. VM 1 sends an NS packet.
2. VTEP 1 learns the MAC address of VM 1 from the NS packet, replies to VM 1 on behalf of VM 2, and sends an NS packet to obtain the MAC address of VM 2.
3. VTEP 2 forwards the NS packet, and VM 2 replies to VTEP 1.
4. VTEP 2 forwards the NA packet sent by VM 2 without learning the MAC address of VM 2 because EVPN is disabled from learning MAC addresses from ND information.
5. VTEP 1 does not learn the MAC address of VM 2 because remote-MAC address learning is disabled.
As a result, VM 1 fails to communicate with VM 2.
For VM 1 to communicate with VM 2, enable NS packet proxy on VSI-interface 2 of VTEP 2. When receiving the NS packet sent by VTEP 1, VTEP 2 forwards it and sends an NS packet sourced from VSI-interface 2 simultaneously, and VM 2 replies to both NS packets. Then, VTEP 2 learns the MAC address of VM 2 from the NA packet sent to VSI-interface 2 and advertises the MAC address to VTEP 1 through BGP EVPN routes. In this way, VTEP 1 obtains the MAC address of VM 2, and VM 1 and VM 2 can communicate.
Procedure
1. Enter system view.
system-view
2. Enter VSI interface view.
interface vsi-interface vsi-interface-id
3. Enable ND request proxy.
ipv6 nd proxy-send enable
By default, ND request proxy is disabled on VSI interfaces.
Enabling conversational learning for forwarding entries
About conversational learning for forwarding entries
Perform the tasks in this section to issue forwarding entries to the hardware only when the entries are required for packet forwarding. The on-demand mechanism saves the device hardware resources.
The forwarding entries in this section include remote MAC address entries, host route FIB entries, and remote ARP entries.
Restrictions and guidelines for enabling conversational learning for forwarding entries
Perform the tasks in this section only on an EVPN network.
Enabling conversational learning for remote MAC address entries
About this task
By default, the device issues a remote MAC address entry to the hardware after the remote MAC address is advertised to the local site by BGP EVPN routes. This feature enables the device to issue a remote MAC address entry to the hardware only when the entry is required for packet forwarding. This feature saves hardware resources on the device.
With this feature enabled, the device generates a blackhole MAC address entry for an unknown MAC address if receiving 50 frames destined for that MAC address within the MAC aging time. Those blackhole MAC address entries age out when the MAC aging timer expires. After a blackhole MAC address entry ages out, the device can forward the traffic destined for the MAC address. For more information about the MAC aging time and blackhole MAC address entries, see MAC address table configuration in Layer 2—LAN Switching Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable conversational learning for remote MAC address entries.
mac-address forwarding-conversational-learning
By default, conversational learning is disabled for remote MAC address entries.
Enabling conversational learning for host route FIB entries
About this task
By default, the device issues a host route FIB entry to the hardware after the entry is generated. This feature enables the device to issue a host route FIB entry to the hardware only when the entry is required for packet forwarding. This feature saves hardware resources on the device.
Restrictions and guidelines
Set an appropriate aging timer for host route FIB entries according to your network. A much longer or shorter aging timer will degrade the device performance.
· If the aging timer is too long, the device will save many outdated host route FIB entries and fail to accommodate the most recent network changes. These entries cannot be used for correct packet forwarding and exhaust FIB resources.
· If the aging timer is too short, the device will delete the valid host route FIB entries that can still be effective for packet forwarding. As a result, FIB entry flapping will occur, and the device performance will be affected.
With conversational learning enabled for host route FIB entries, the device periodically sends ARP requests to learn the host route for an IP address if the following conditions exist:
· Incoming packets are destined for the IP address, and the IP address matches a direct route.
· The device does not have a host route for the IP address.
Before the probe node ages out, if the device has not learned a host route after receiving 50 packets destined for that IP address, the device adds a blackhole route for the IP address. The device retains the blackhole route until the probe node ages out or it learns a host route for the IP address.
Procedure
1. Enter system view.
system-view
2. Enable conversational learning for host route FIB entries.
ip forwarding-conversational-learning [ aging aging-time ]
By default, conversational learning is disabled for host route FIB entries.
Configuring BGP EVPN route redistribution and advertisement
Redistributing MAC/IP advertisement routes into BGP unicast routing tables
About this task
This task enables the device to redistribute received MAC/IP advertisement routes that contain ARP or ND information into a BGP unicast routing table.
· If you perform this task for the BGP IPv4 or IPv6 unicast address family, the device will redistribute the routes into the BGP IPv4 or IPv6 unicast routing table. In addition, the device will advertise the routes to the local site.
· If you perform this task for the BGP-VPN IPv4 or IPv6 unicast address family, the device will redistribute the routes into the BGP-VPN IPv4 or IPv6 unicast routing table of the corresponding VPN instance. To advertise the routes to the local site, you must configure the advertise l2vpn evpn command.
Procedure (BGP instance view)
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP IPv4 or IPv6 unicast address family view.
address-family { ipv4 | ipv6 }
4. Redistribute MAC/IP advertisement routes that contain ARP or ND information into the BGP IPv4 or IPv6 unicast routing table.
import evpn mac-ip
By default, MAC/IP advertisement routes that contain ARP or ND information are not redistributed into the BGP IPv4 or IPv6 unicast routing table.
Procedure (BGP-VPN instance view)
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP-VPN instance view.
ip vpn-instance vpn-instance-name
4. Enter BGP-VPN IPv4 or IPv6 unicast address family view.
address-family { ipv4 | ipv6 }
5. Redistribute MAC/IP advertisement routes that contain ARP or ND information into the BGP-VPN IPv4 or IPv6 unicast routing table.
import evpn mac-ip
By default, MAC/IP advertisement routes that contain ARP or ND information are not redistributed into the BGP-VPN IPv4 or IPv6 unicast routing table.
Setting the metric of BGP EVPN routes added to a VPN instance's routing table
About this task
After you perform this task, the device sets the metric of a BGP EVPN route added to a VPN instance's routing table to the metric of the IGP route pointing to the next hop in the original BGP EVPN route.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. Set the metric of a BGP EVPN route added to a VPN instance's routing table to the metric of the IGP route pointing to the next hop in the original BGP EVPN route.
igp-metric inherit
By default, the device sets the metric to 0 when adding BGP EVPN routes a VPN instance's routing table.
Enabling BGP EVPN route advertisement to the local site
About this task
This feature enables the device to advertise BGP EVPN routes to the local site after the device adds the routes to the routing table of a VPN instance. The BGP EVPN routes here are IP prefix advertisement routes and MAC/IP advertisement routes that contain ARP or ND information.
Procedure (IPv4)
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP-VPN instance view.
ip vpn-instance vpn-instance-name
4. Enter BGP-VPN IPv4 unicast address family view.
address-family ipv4 [ unicast ]
5. Enable BGP EVPN route advertisement to the local site.
advertise l2vpn evpn
By default, BGP EVPN route advertisement to the local site is enabled.
Procedure (IPv6)
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP-VPN instance view.
ip vpn-instance vpn-instance-name
4. Enter BGP-VPN IPv6 unicast address family view.
address-family ipv6 [ unicast ]
5. Enable BGP EVPN route advertisement to the local site.
advertise l2vpn evpn
By default, BGP EVPN route advertisement to the local site is enabled.
Disabling flooding for a VSI
About this task
By default, the VTEP floods broadcast, unknown unicast, and unknown multicast frames received from the local site to the following interfaces in the frame's VXLAN:
· All site-facing interfaces except for the incoming interface.
· All VXLAN tunnel interfaces.
When receiving broadcast, unknown unicast, and unknown multicast frames on VXLAN tunnel interfaces, the device floods the frames to all site-facing interfaces in the frames' VXLAN.
To confine a kind of flood traffic, disable flooding for that kind of flood traffic on the VSI bound to the VXLAN.
You can use selective flood to exclude a remote MAC address from the remote flood suppression done by using the flooding disable command. The VTEP will flood the frames destined for the specified MAC address to remote sites when floods are confined to the local site.
For more information about the VXLAN commands in this task, see VXLAN Command Reference.
Procedure
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Disable flooding for the VSI.
flooding disable { all | { broadcast | unknown-multicast | unknown-unicast } * } [ all-direction | dci ]
By default, flooding is enabled for a VSI.
If VXLAN-DCI is configured, flood traffic is also sent out of VXLAN-DCI tunnel interfaces. To confine flood traffic to the site-facing interfaces and VXLAN tunnels within a data center, you can specify the dci keyword to disable flooding only to VXLAN-DCI tunnel interfaces.
The all-direction keyword disables flooding traffic received from an AC or VXLAN tunnel interface to any other ACs and VXLAN tunnel interfaces of the same VSI. If VXLAN-DCI is configured, this keyword also disables flooding between VXLAN tunnel interfaces and VXLAN-DCI tunnel interfaces.
4. (Optional.) Enable selective flood for a MAC address.
selective-flooding mac-address mac-address
Enabling ARP or ND flood suppression
About this task
Use ARP or ND flood suppression to reduce ARP request broadcasts or ND request multicasts.
The aging timer is fixed at 25 minutes for ARP or ND flood suppression entries. If the flooding disable command is configured, set the MAC aging timer to a higher value than the aging timer for ARP or ND flood suppression entries on all VTEPs. This setting prevents the traffic blackhole that occurs when a MAC address entry ages out before its ARP or ND flood suppression entry ages out. To set the MAC aging timer, use the mac-address timer command.
When remote ARP or ND learning is disabled for VXLANs, the device does not use ARP or ND flood suppression entries to respond to ARP or ND requests received on VXLAN tunnels.
To delete ARP flood suppression entries, use the reset arp suppression vsi command instead of the reset arp command. For more information about the reset arp suppression vsi command, see VXLAN Command Reference. For more information about the reset arp command, see ARP commands in Layer 3—IP Services Command Reference.
To delete ND flood suppression entries, use the reset ipv6 nd suppression vsi command instead of the reset ipv6 neighbors command. For more information about the reset ipv6 nd suppression vsi command, see VXLAN Command Reference. For more information about the reset ipv6 neighbors command, see IPv6 basics commands in Layer 3—IP Services Command Reference.
Enabling ARP flood suppression
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Enable ARP flood suppression.
arp suppression enable
By default, ARP flood suppression is disabled.
For more information about this command, see VXLAN Command Reference.
Enabling ND flood suppression
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Enable ND flood suppression.
ipv6 nd suppression enable
By default, ND flood suppression is disabled.
For more information about this command, see VXLAN Command Reference.
Enabling packet statistics for VXLAN tunnels
About this task
Perform this task to enable packet statistics globally for automatically created VXLAN tunnels.
To display the packet statistics for a VXLAN tunnel, use the display interface tunnel command in any view.
To clear the packet statistics for a VXLAN tunnel, use the reset counters interface tunnel command in user view.
Procedure
1. Enter system view.
system-view
2. Enable packet statistics for automatically created VXLAN tunnels.
tunnel statistics vxlan auto
By default, the packet statistics feature is disabled for automatically created VXLAN tunnels.
For more information about this command, see VXLAN Command Reference.
Testing the connectivity of a VXLAN tunnel
Enabling overlay OAM
About this task
You must enable overlay OAM on the tunnel destination device for a VXLAN tunnel before you can use the ping vxlan or tracert vxlan command to test reachability of the VXLAN tunnel on the tunnel source device.
Restrictions and guidelines
To specify the -r 3 parameter in the ping vxlan or tracert vxlan command on the tunnel source device, you must also enable overlay OAM on the tunnel source device.
Procedure
1. Enter system view.
system-view
2. Enable overlay OAM.
overlay oam enable
By default, overlay OAM is disabled.
Pinging a VXLAN tunnel destination
About this task
Perform this task to test the connectivity of a VXLAN tunnel in an EVPN VXLAN network when the tunnel has traffic loss or interruption issues. The process of a ping VXLAN operation is as follows:
1. The tunnel source VTEP sends VXLAN-encapsulated VXLAN echo requests to the tunnel destination VTEP.
2. The tunnel destination VTEP responds with VXLAN echo replies.
3. The tunnel source VTEP outputs packet statistics and the test result based on the received VXLAN echo replies.
Restrictions and guidelines
Before you perform this task on the tunnel source device, you must enable overlay OAM on the tunnel destination device by using the overlay oam enable command.
The VTEP can distribute VXLAN echo requests among multiple paths to the destination based on the source UDP port. When a VXLAN tunnel has multiple paths on the transport network, you can configure load sharing parameters to ensure accuracy of the test result. You can use one of the following methods to configure source UDP ports for VXLAN echo requests:
· Specify a source UDP port range. The device will send VXLAN echo requests sourced from each UDP port in the UDP port range. You need to execute the ping vxlan command only once.
· Specify load balancing parameters such as source and destination MAC addresses, source and destination IP addresses, and protocol for the VTEP to calculate a source UDP port number. You need to execute the ping vxlan command multiple times to test connectivity of all paths.
The load balancing parameters change only the source UDP port number of VXLAN echo requests. Other fields of the requests will not be changed.
If you specify the vxlan-source-udpport vxlan-source-udpport [ end-vxlan-src-udpport ] parameters, the number of VXLAN echo requests sourced from each UDP port in the UDP port range is determined by the -c count parameter.
Procedure
Execute the following command in any view.
ping vxlan [ -a inner-src-address | -c count | -m interval | -r reply-mode | -t timeout | -tos tos-value ] * vxlan-id vxlan-id tunnel-source source-address tunnel-destination dest-address [ destination-udpport dest-port ] [ vxlan-source-address vxlan-source-address ] [ load-balance { vxlan-source-udpport vxlan-source-udpport [ end-vxlan-src-udpport ] | source-address lb-src-address destination-address lb-dest-address protocol { udp | lb-protocol-id } source-port lb-src-port destination-port lb-dest-port source-mac lb-source-mac destination-mac lb-destination-mac } ]
For more information about this command, see VXLAN Command Reference.
Tracing the path to a VXLAN tunnel destination
About this task
Perform this task to locate failed nodes on the path for a VXLAN tunnel that has traffic loss or interruption issues in an EVPN VXLAN network. The process of a tracert VXLAN operation is as follows:
1. The tunnel source VTEP sends VXLAN-encapsulated VXLAN echo requests to the tunnel destination VTEP. The TTL in the IP header of the requests is set to 1.
2. The first hop on the path responds to the tunnel source VTEP with a TTL-expired ICMP error message.
3. The tunnel source VTEP sends VXLAN echo requests with the TTL set to 2.
4. The second hop responds with a TTL-expired ICMP error message.
5. This process continues until a VXLAN echo request reaches the tunnel destination VTEP or the maximum TTL value is reached. If a VXLAN echo request reaches the tunnel destination VTEP, the tunnel destination VTEP sends a VXLAN echo reply to the tunnel source VTEP.
6. The tunnel source VTEP outputs packet statistics and the test result based on the received ICMP error messages and whether a VXLAN echo reply is received.
Restrictions and guidelines
Before you perform this task on the tunnel source device, you must enable overlay OAM on the tunnel destination device by using the overlay oam enable command.
The VTEP can distribute VXLAN echo requests among multiple paths to the destination based on the source UDP port. When a VXLAN tunnel has multiple paths on the transport network, you can configure load sharing parameters to ensure accuracy of the test result. You can use one of the following methods to configure source UDP ports for VXLAN echo requests:
· Specify a source UDP port range. The device will send VXLAN echo requests sourced from each UDP port in the UDP port range. You need to execute the ping vxlan command only once.
· Specify load balancing parameters such as source and destination MAC addresses, source and destination IP addresses, and protocol for the VTEP to calculate a source UDP port number. You need to execute the ping vxlan command multiple times to test connectivity of all paths.
The load balancing parameters change only the source UDP port number of VXLAN echo requests. Other fields of the requests will not be changed.
Procedure
Execute the following command in any view.
tracert vxlan [ -a inner-src-address | -h ttl-value | -r reply-mode | -t timeout ] * vxlan-id vxlan-id tunnel-source source-address tunnel-destination dest-address [ destination-udpport dest-port ] [ vxlan-source-address vxlan-source-address ] [ load-balance { vxlan-source-udpport vxlan-source-udpport | source-address lb-src-address destination-address lb-dest-address protocol { udp | lb-protocol-id } source-port lb-src-port destination-port lb-dest-port source-mac lb-source-mac destination-mac lb-destination-mac } ]
For more information about this command, see VXLAN Command Reference.
Enabling SNMP notifications for EVPN
About this task
If SNMP notifications are enabled for EVPN, a MAC mobility suppression notification is sent to SNMP module after the MAC mobility suppression threshold is reached. For SNMP notifications to be sent correctly, you must also configure SNMP on the device. For more information about SNMP configuration, see Network Management and Monitoring Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable SNMP notifications for EVPN.
snmp-agent trap enable evpn [ mac-mobility-suppression ]
By default, SNMP notifications are disabled for EVPN.
Configuring EVPN M-LAG
About this task
EVPN M-LAG virtualizes two VTEPs or EVPN gateways into one M-LAG system to avoid single points of failure. The VTEPs or EVPN gateways use a virtual VTEP address to establish VXLAN tunnels to remote devices.
An AC that is attached to only one of the VTEPs in an M-LAG system is called a single-homed AC. To ensure that the traffic of a single-homed AC is forwarded to its attached VTEP, specify the IP addresses of the VTEPs in the M-LAG system by using the evpn m-lag local command. After you configure this command, each VTEP in an M-LAG system changes the next hop of the routes for single-homed ACs to its local VTEP IP address when advertising the routes. When a VTEP receives BGP EVPN routes from the peer VTEP IP address specified by using this command, it does not set up a VXLAN tunnel to the peer VTEP.
You must execute the evpn m-lag local command if single-homed ACs are attached to an M-LAG system that uses a direct peer link. You do not need to execute this command on an M-LAG system that uses a tunnel peer link. In such an M-LAG system, a VTEP uses the source IP address of the peer link as the next hop of routes for single-homed ACs to ensure correct traffic forwarding.
Restrictions and guidelines
EVPN M-LAG restrictions and guidelines
When you configure EVPN M-LAG, follow these restrictions and guidelines:
· In an M-LAG system, M-LAG member devices must have the same EVPN configuration.
· Do not configure overlapping outer VLAN IDs for Ethernet service instances of different VSIs.
· For an M-LAG member device to re-establish VXLAN tunnels, you must execute the address-family l2vpn evpn command in BGP instance view after you perform one of the following tasks:
¡ Modify the virtual VTEP address.
¡ Enable or disable EVPN M-LAG.
· You must execute the undo mac-address static source-check enable command on the Layer 2 aggregate interfaces or Layer 2 Ethernet interfaces that act as peer-link interfaces and on transport-facing physical interfaces.
· You cannot specify a secondary IP address of an interface as the virtual VTEP address.
· To ensure nonstop traffic forwarding, configure route backup on an EVPN M-LAG system. When the upstream link on one M-LAG member device fails, upstream traffic is switched to the other M-LAG member device through the backup route.
· If the traffic outgoing interface for a VXLAN tunnel is an M-LAG interface, do not assign the M-LAG interface to a VLAN that matches an Ethernet service instance on the peer link.
· Make sure the peer-link interfaces and the interfaces with single-homed ACs configured have the same link type.
· If the M-LAG system is formed by two distributed EVPN gateways, use the evpn global-mac command to configure the same EVPN global MAC address on the distributed EVPN gateways.
· Use a direct link between the M-LAG member devices as the keepalive link. Do not use the keep link for any other purposes. Make sure the M-LAG member devices have Layer 2 and Layer 3 connectivity to each other over the keepalive link.
· Do not use VSI interface 0 as a gateway interface.
· When you bulk shut down physical interfaces on an M-LAG member device for service changes or hardware replacement, shut down the physical interfaces used for keepalive detection prior to the physical member ports of the peer-link interface. If you fail to do so, link flapping will occur on the member ports of M-LAG interfaces.
· If an M-LAG system is attached to a large number of servers whose NICs operate in active/standby mode, take the size of the traffic sent among those servers into account when you determine the bandwidth of the peer link.
· Three VXLAN tunnels are set up between an M-LAG system and a peer VTEP. When the peer VTEP sends multicast, broadcast, or unknown unicast traffic (flood traffic) to the M-LAG system, the M-LAG member devices receive three identical flood flows and drop two of them. If the M-LAG member devices have learned the destination MAC address of the flood flow, the flood flows ought to be dropped will be unicasted, and the VMs attached to the M-LAG system will receive duplicate packets.
· If the peer link or an AC forwards both overlay and underlay traffic, the peer-link interface or the site-facing interface that hosts the AC might reflect back received packets. To resolve this issue, assign the peer-link interface or site-facing interface to a port isolation group to disable it from reflecting packets back. This issue does not apply to the S6800 switches labeled with product codes LS-6800-32Q, LS-6800-2C, LS-6800-4C, LS-6800-54QF, and LS-6800-54QT.
If a direct peer link is used, follow these restrictions:
· If the frame match criteria of dynamic ACs on the peer link are created based on site-facing Ethernet service instances, you can configure only the following criteria for site-facing Ethernet service instances:
¡ encapsulation s-vid { vlan-id | vlan-id-list }
¡ encapsulation untagged
In addition, you must set the access mode to VLAN for the site-facing Ethernet service instances.
· You must configure VLAN access mode for the site-facing Ethernet service instances when the frame match criteria of dynamic ACs on the peer link are created based on VXLAN IDs. You can configure only the encapsulation s-vid { vlan-id | vlan-id-list } c-vid { vlan-id-list | all } criterion for site-facing Ethernet service instances to match double-tagged packets. You can configure only the encapsulation s-vid { vlan-id | vlan-id-list } [ only-tagged ] criterion for site-facing Ethernet service instances to match single-tagged packets. If you configure any other criterion, traffic sent over the peer link will carry incorrect VLAN IDs.
· Make sure the following settings are consistent on the M-LAG member devices:
¡ Ethernet service instances and their match criterion on the M-LAG interfaces in the same M-LAG group or single-homed site-facing interfaces.
¡ VXLAN IDs of VSIs.
In addition, the Ethernet service instances must be created manually.
· As a best practice, do not redistribute external routes on the M-LAG member devices.
Forwarding entry configuration restrictions and guidelines
The VTEPs in an M-LAG system synchronize local and remote MAC address entries with each other over the peer link. However, they do not synchronize MAC address entry deletions. When you delete a MAC address entry from one VTEP, the other VTEP retains the entry that contains the same MAC address until the entry ages out.
At an IPv6 site, if you enable ND flood suppression on the VTEPs in an M-LAG system, both VTEPs reply with NA packets when one of the VTEPs receives an NS packet on an M-LAG interface.
If a route reflector reflects routes between the VTEPs in an M-LAG system, after you execute the evpn m-lag local command on both VTEPs or execute the undo evpn m-lag local command on one of the VTEPs, also execute the following commands on the VTEPs:
· reset arp.
· reset arp suppression vsi.
· reset ipv6 neighbors.
· reset ipv6 nd suppression vsi.
These commands clear ARP- and ND-related entries on the VTEPs to ensure correct forwarding.
Prerequisites
In addition to EVPN M-LAG configuration, you must configure the following settings:
· Configure other M-LAG and EVPN settings depending on your network. For information about M-LAG configuration, see Layer 2—LAN Switching Configuration Guide.
· Use the m-lag mad exclude interface command to exclude the following interfaces:
¡ Set the default M-LAG MAD action to NONE by using the m-lag mad default-action none command.
¡ Do not configure the M-LAG MAD action on the VLAN interfaces of the VLANs to which the M-LAG interfaces and peer-link interfaces belong. These interfaces will not be shut down by M-LAG MAD.
¡ If you use a direct peer link, add the uplink Layer 3 interfaces, VLAN interfaces, and physical interfaces to the list of included interfaces by using the m-lag mad include interface command. These interfaces will be shut down by M-LAG MAD. This restriction does not apply to a tunnel peer link.
¡ Do not configure the M-LAG MAD action on the interfaces used by EVPN, including the VSI interfaces, interfaces that provide BGP peer addresses, and interfaces used for setting up the keepalive link. These interfaces will not be shut down by M-LAG MAD.
¡ Do not configure the M-LAG MAD action on the interface that provides the IP address specified by using the evpn m-lag group command. These interfaces will not be shut down by M-LAG MAD.
· Execute the m-lag restore-delay command to set the data restoration interval to a value equal to or larger than 300 seconds.
· You must disable spanning tree on the Layer 2 Ethernet interface that acts as the physical traffic outgoing interface of a VXLAN tunnel. If you enable spanning tree on that interface, the upstream device will falsely block the interfaces connected to the M-LAG member devices.
· As a best practice, set the PVID to 4094 on the peer-link interfaces. If you fail to do so, an M-LAG member device might set the outer VLAN ID matched by an AC to the PVID of its peer-link interface. This error will affect forwarding of the underlay traffic whose VLAN ID is VXLAN ID%4094 + 1.
If you use a tunnel peer link, you must also complete the following tasks:
· Manually create the VXLAN tunnel interface and configure it as the peer-link interface. An automatically created VXLAN tunnel cannot be used as a peer link.
· Use the m-lag mad exclude interface command to exclude VXLAN tunnel interfaces and their traffic outgoing interfaces from the MAD shutdown action by M-LAG before you configure them as peer-link interfaces. If you have configured the VXLAN tunnel interfaces as peer-link interfaces before excluding them and their traffic outgoing interfaces from the MAD shutdown action, you must first remove the peer-link interface configuration. After the VXLAN tunnel interfaces and their traffic outgoing interfaces come up, exclude the interfaces from the MAD shutdown action by M-LAG. Then, configure the VXLAN tunnel interfaces as peer-link interfaces.
· The source address of the peer-link VXLAN tunnel must be the address used by the device to establish BGP peer relationships with other devices.
· As a best practice, use different physical interfaces as the traffic outgoing interfaces of the peer-link VXLAN tunnel and non-peer-link VXLAN tunnels.
· To prioritize transmission of M-LAG protocol packets on the peer link, use the tunnel tos command on the peer-link VXLAN tunnel interface to set a high ToS value for tunneled packets.
· Specify the virtual VTEP address and the source address of the tunnel peer link as the IP addresses of different loopback interfaces. Configure a routing protocol to advertise the IP addresses.
· Use the reserved vxlan command to specify a reserved VXLAN to forward M-LAG protocol packets. The M-LAG member devices in an M-LAG system must have the same reserved VXLAN.
Procedure (IPv4)
1. Enter system view.
system-view
2. Enable EVPN M-LAG and specify the virtual VTEP address.
evpn m-lag group virtual-vtep-ipv4
By default, EVPN M-LAG is disabled.
To modify the virtual VTEP address, you must first delete the original virtual VTEP address.
3. Specify the IP addresses of the VTEPs in the M-LAG system.
evpn m-lag local local-ipv4-address remote remote-ipv4-address
By default, the IP addresses of the VTEPs in an M-LAG system are not specified.
Make sure the IP address of the local VTEP belongs to a local interface. Make sure the local VTEP IP address and peer VTEP IP address are reversed on the VTEPs in the M-LAG system.
4. (Optional.) Enable the device to create frame match criteria based on VXLAN IDs for the dynamic ACs on the peer link.
l2vpn m-lag peer-link ac-match-rule vxlan-mapping
By default, on an EVPN M-LAG system that uses a direct peer link, dynamic ACs on the peer link use frame match criteria that are identical to those of site-facing ACs.
If you do not execute this command, do not configure overlapping outer VLAN IDs for Ethernet service instances of different VSIs.
If you execute this command, do not create VXLANs with IDs larger than 16000000.
Procedure (IPv6)
1. Enter system view.
system-view
2. Enable EVPN M-LAG and specify the virtual VTEP address.
evpn m-lag group virtual-vtep-ipv6
By default, EVPN M-LAG is disabled.
To modify the virtual VTEP address, you must first delete the original virtual VTEP address.
3. Specify the IP addresses of the VTEPs in the M-LAG system.
evpn m-lag local local-ipv6-address remote remote-ipv6-address
By default, the IP addresses of the VTEPs in an M-LAG system are not specified.
Make sure the IP address of the local VTEP belongs to a local interface. Make sure the local VTEP IP address and peer VTEP IP address are reversed on the VTEPs in the M-LAG system.
4. (Optional.) Enable the device to create frame match criteria based on VXLAN IDs for the dynamic ACs on the peer link.
l2vpn m-lag peer-link ac-match-rule vxlan-mapping
By default, on an EVPN M-LAG system that uses a direct peer link, dynamic ACs on the peer link use frame match criteria that are identical to those of site-facing ACs.
If you do not execute this command, do not configure overlapping outer VLAN IDs for Ethernet service instances of different VSIs.
If you execute this command, do not create VXLANs with IDs larger than 16000000.
Display and maintenance commands for EVPN
|
IMPORTANT: The S6800 switches labeled with product codes LS-6800-32Q, LS-6800-2C, and LS-6800-4C do not support the following commands: · display evpn es · display evpn route { igmp-js | igmp-ls | smet } [ local | remote ] [ vsi vsi-name ] [ count ] · display l2vpn forwarding evpn split-horizon |
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display BGP peer group information. |
display bgp [ instance instance-name ] group l2vpn evpn [ group-name group-name ] |
|
Display BGP EVPN routes. |
display bgp [ instance instance-name ] l2vpn evpn [ peer ipv4-address { advertised-routes | received-routes } [ statistics ] | [ route-distinguisher route-distinguisher | route-type { auto-discovery | es | igmp-ls | igmp-js | imet | ip-prefix | mac-ip | s-pmsi | smet } ] * [ { evpn-route route-length | evpn-prefix } [ advertise-info | as-path | cluster-list | community | ext-community ] | { ipv4-address | ipv6-address | mac-address } [ verbose ] ] | statistics ] display bgp [ instance instance-name ] l2vpn evpn [ route-distinguisher route-distinguisher ] [ statistics ] community [ community-number&<1-32> | aa:nn&<1-32> ] [ internet | no-advertise | no-export | no-export-subconfed ] [ whole-match ] display bgp [ instance instance-name ] l2vpn evpn [ route-distinguisher route-distinguisher ] [ statistics ] community-list { basic-community-list-number | adv-community-list-number | comm-list-name } [ whole-match ] display bgp [ instance instance-name ] l2vpn evpn [ route-distinguisher route-distinguisher ] [ statistics ] ext-community [ rt route-target | soo site-of-origin]&<1-32> [ whole-match ] |
|
Display BGP peer or peer group information. |
display bgp [ instance instance-name ] peer l2vpn evpn [ ipv4-address mask-length | { ipv4-address | group-name group-name } log-info | [ ipv4-address ] verbose ] |
|
Display information about BGP update groups. |
display bgp [ instance instance-name ] update-group l2vpn evpn [ ipv4-address ] |
|
Display information about IPv4 peers that are automatically discovered through BGP. |
display evpn auto-discovery { { imet | mac-ip } [ mpls | vxlan ] [ peer ip-address ] [ vsi vsi-name ] | macip-prefix [ nexthop next-hop ] [ count ] } |
|
Display M-LAG-synchronized MAC address entries. |
display evpn m-lag synchronized-mac [ vsi vsi-name ] [ count ] |
|
Display EVPN ES information. |
display evpn es { local [ vsi vsi-name | xconnect-group group-name ] [ esi esi-id ] [ verbose ] | remote [ vsi vsi-name | xconnect-group group-name ] [ esi esi-id ] [ nexthop next-hop ] } |
|
Display EVPN instance information. |
display evpn instance [ name instance-name | vsi vsi-name ] vxlan |
|
Display EVPN ARP entries. |
display evpn route arp [ local | remote ] [ public-instance | vpn-instance vpn-instance-name ] [ count ] |
|
Display ARP flood suppression entries. |
display evpn route arp suppression [ mpls | vxlan ] [ local | remote ] [ vsi vsi-name ] [ count ] |
|
Display EVPN ARP mobility information. |
display evpn route arp-mobility [ public-instance | vpn-instance vpn-instance-name ] [ ip ip-address ] |
|
Display EVPN multicast routes. |
display evpn route { igmp-js | igmp-ls | smet } [ local | remote ] [ vsi vsi-name ] [ count ] |
|
Display EVPN MAC address entries. |
display evpn route mac [ mpls | vxlan ] [ local | remote ] [ vsi vsi-name ] [ count ] |
|
Display EVPN MAC mobility information. |
display evpn [ ipv6 ] route mac-mobility [ vsi vsi-name ] [ mac-address mac-address ] |
|
Display EVPN ND entries. |
display evpn route nd [ local | remote ] [ public-instance | vpn-instance vpn-instance-name ] [ count ] |
|
Display EVPN ND flood suppression entries. |
display evpn route nd suppression [ local | remote ] [ vsi vsi-name ] [ count ] |
|
Display EVPN ND mobility information. |
display evpn route nd-mobility [ public-instance | vpn-instance vpn-instance-name ] [ ipv6 ipv6-address ] |
|
Display the routing table for a VPN instance. |
display evpn routing-table [ ipv6 ] { public-instance | vpn-instance vpn-instance-name } [ count ] |
|
Display site-facing interfaces excluded from traffic forwarding by split horizon. |
display l2vpn forwarding evpn split-horizon { ac interface interface-type interface-number | ac interface interface-type interface-number service-instance instance-id | tunnel tunnel-number } slot slot-number |
|
Cancel ARP mobility event suppression. |
reset evpn route arp-mobility suppression [ public-instance | vpn-instance vpn-instance-name [ ip ip-address ] ] |
|
Cancel MAC mobility event suppression. |
reset evpn route mac-mobility suppression [ vsi vsi-name [ mac mac-address ] ] |
|
Cancel ND mobility event suppression. |
reset evpn route nd-mobility suppression [ public-instance | vpn-instance vpn-instance-name [ ipv6 ipv6-address ] ] |
|
Display ARP gateway protection configuration for Ethernet service instances. |
display arp filter source service-instance [ interface interface-type interface-number [ service-instance instance-id ] ] [ slot slot-number ] |
|
|
NOTE: For more information about the display bgp group, display bgp peer, and display bgp update-group commands, see BGP commands in Layer 3—IP Routing Command Reference. |
EVPN VXLAN configuration examples
Example: Configuring a centralized EVPN gateway
Network configuration
As shown in Figure 20:
· Configure VXLAN 10 and VXLAN 20 on Switch A, Switch B, and Switch C to provide connectivity for the VMs in the VXLANs across the network sites.
· Configure Switch C as a centralized IPv4 EVPN gateway to provide gateway services and access to the connected Layer 3 network.
· Configure Switch D as an RR to reflect BGP EVPN routes between Switch A, Switch B, and Switch C.
|
|
NOTE: This example provides configuration of IPv4 sites over an IPv4 underlay network. The configuration procedure does not differ between IPv4 and IPv6 sites or underlay networks. |
Procedure
1. Set the VXLAN hardware resource mode on Switch C and reboot the switch for the mode to take effect.
<SwitchC> system-view
[SwitchC] hardware-resource vxlan l3gw16k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchC] quit
<SwitchC> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
2. On VM 1 and VM 3, specify 10.1.1.1 as the gateway address. On VM 2 and VM 4, specify 10.1.2.1 as the gateway address. (Details not shown.)
3. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 20. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D) for them to reach one another. (Details not shown.)
4. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC address and ARP learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] arp suppression enable
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] arp suppression enable
[SwitchA-vsi-vpnb] evpn encapsulation vxlan
[SwitchA-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchA-vsi-vpnb] vxlan 20
[SwitchA-vsi-vpnb-vxlan-20] quit
[SwitchA-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 200
[SwitchA-bgp-default] peer 4.4.4.4 as-number 200
[SwitchA-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 2000 to match VLAN 3.
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 2000
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] encapsulation s-vid 3
# Map Ethernet service instance 2000 to VSI vpnb.
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] xconnect vsi vpnb
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] quit
[SwitchA-Ten-GigabitEthernet1/0/1] quit
5. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC address and ARP learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] arp suppression enable
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] arp suppression enable
[SwitchB-vsi-vpnb] evpn encapsulation vxlan
[SwitchB-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchB-vsi-vpnb] vxlan 20
[SwitchB-vsi-vpnb-vxlan-20] quit
[SwitchB-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchB] bgp 200
[SwitchB-bgp-default] peer 4.4.4.4 as-number 200
[SwitchB-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchB-Ten-GigabitEthernet1/0/1] quit
# On Ten-GigabitEthernet 1/0/2, create Ethernet service instance 2000 to match VLAN 3.
[SwitchB] interface ten-gigabitethernet 1/0/2
[SwitchB-Ten-GigabitEthernet1/0/2] service-instance 2000
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] encapsulation s-vid 3
# Map Ethernet service instance 2000 to VSI vpnb.
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] xconnect vsi vpnb
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] quit
[SwitchB-Ten-GigabitEthernet1/0/2] quit
6. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Disable remote MAC address and ARP learning.
[SwitchC] vxlan tunnel mac-learning disable
[SwitchC] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] evpn encapsulation vxlan
[SwitchC-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] evpn encapsulation vxlan
[SwitchC-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchC-vsi-vpnb] vxlan 20
[SwitchC-vsi-vpnb-vxlan-20] quit
[SwitchC-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchC] bgp 200
[SwitchC-bgp-default] peer 4.4.4.4 as-number 200
[SwitchC-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Create VSI-interface 1 and assign the interface an IP address. The IP address will be used as the gateway address for VXLAN 10.
[SwitchC] interface vsi-interface 1
[SwitchC-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchC-Vsi-interface1] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] gateway vsi-interface 1
[SwitchC-vsi-vpna] quit
# Create VSI-interface 2 and assign the interface an IP address. The IP address will be used as the gateway address for VXLAN 20.
[SwitchC] interface vsi-interface 2
[SwitchC-Vsi-interface2] ip address 10.1.2.1 255.255.255.0
[SwitchC-Vsi-interface2] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] gateway vsi-interface 2
[SwitchC-vsi-vpnb] quit
7. Configure Switch D:
# Establish BGP connections with other transport network switches.
<SwitchD> system-view
[SwitchD] bgp 200
[SwitchD-bgp-default] group evpn
[SwitchD-bgp-default] peer 1.1.1.1 group evpn
[SwitchD-bgp-default] peer 2.2.2.2 group evpn
[SwitchD-bgp-default] peer 3.3.3.3 group evpn
[SwitchD-bgp-default] peer evpn as-number 200
[SwitchD-bgp-default] peer evpn connect-interface loopback 0
# Configure BGP to advertise BGP EVPN routes, and disable route target filtering for BGP EVPN routes.
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer evpn enable
[SwitchD-bgp-default-evpn] undo policy vpn-target
# Configure Switch D as an RR.
[SwitchD-bgp-default-evpn] peer evpn reflect-client
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
Verifying the configuration
1. Verify the EVPN gateway settings on Switch C:
# Verify that Switch C has advertised MAC/IP advertisement routes and IMET routes for the gateways and received MAC/IP advertisement routes and IMET routes from Switch A and Switch B. (Details not shown.)
# Verify that the VXLAN tunnel interfaces are up on Switch C.
[SwitchC] display interface tunnel
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 3.3.3.3, destination 2.2.2.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 7 bytes/sec, 56 bits/sec, 0 packets/sec
Input: 10 packets, 980 bytes, 0 drops
Output: 85 packets, 6758 bytes, 0 drops
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 3.3.3.3, destination 1.1.1.1
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 1 bytes/sec, 8 bits/sec, 0 packets/sec
Last 300 seconds output rate: 9 bytes/sec, 72 bits/sec, 0 packets/sec
Input: 277 packets, 20306 bytes, 0 drops
Output: 1099 packets, 85962 bytes, 0 drops
# Verify that the VSI interfaces are up on Switch C.
[SwitchC] display interface vsi-interface brief
Brief information on interfaces in route mode:
Link: ADM - administratively down; Stby - standby
Protocol: (s) - spoofing
Interface Link Protocol Primary IP Description
Vsi1 UP UP 10.1.1.1
Vsi2 UP UP 10.1.2.1
# Verify that the VXLAN tunnels have been assigned to the VXLANs, and that the VSI interfaces are the gateway interfaces of their respective VXLANs.
[SwitchC] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 1
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
Tunnel1 0x5000001 UP Auto Disabled
VSI Name: vpnb
VSI Index : 1
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 2
VXLAN ID : 20
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
Tunnel1 0x5000001 UP Auto Disabled
# Verify that Switch C has created EVPN ARP entries for the VMs.
[SwitchC] display evpn route arp
Flags: D - Dynamic B - BGP L - Local active
G - Gateway S - Static M - Mapping I - Invalid
Public instance Interface: Vsi-interface1
IP address MAC address Router MAC VSI index Flags
10.1.1.1 0003-0003-0003 - 0 GL
10.1.1.10 0000-1234-0001 - 0 B
10.1.1.20 0000-1234-0003 - 0 B
Public instance Interface: Vsi-interface2
IP address MAC address Router MAC VSI index Flags
10.1.2.1 0005-0005-0005 - 1 GL
10.1.2.10 0000-1234-0002 - 1 B
10.1.2.20 0000-1234-0004 - 1 B
# Verify that Switch C has created FIB entries for the VMs.
[SwitchC] display fib 10.1.1.10
Destination count: 1 FIB entry count: 1
Flag:
U:Usable G:Gateway H:Host B:Blackhole D:Dynamic S:Static
R:Relay F:FRR
Destination/Mask Nexthop Flag OutInterface/Token Label
10.1.1.10/32 10.1.1.10 UH Vsi1 Null
2. Verify that VM 1, VM 2, VM 3, and VM 4 can communicate with one another.
Example: Configuring distributed EVPN gateways in symmetric IRB mode (IPv4 underlay network)
Network configuration
As shown in Figure 21:
· Configure VXLAN 10 and VXLAN 20 on Switch A and Switch B to provide connectivity for the VMs in the VXLANs across the network sites.
· Configure Switch A and Switch B as distributed EVPN gateways to provide gateway services in symmetric IRB mode. Configure Switch C as a border gateway to provide access to the connected Layer 3 network.
· Configure Switch D as an RR to reflect BGP EVPN routes between Switch A, Switch B, and Switch C.
|
|
NOTE: This example provides configuration of IPv4 sites. The configuration procedure does not differ between IPv4 and IPv6 sites. |
Procedure
1. Set the VXLAN hardware resource mode:
# Set the VXLAN hardware resource mode on Switch A and Switch B and reboot the switches for the mode to take effect. This step uses Switch A as an example.
<SwitchA> system-view
[SwitchA] hardware-resource vxlan l3gw16k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchA] quit
<SwitchA> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
# Set the VXLAN hardware resource mode on Switch C and reboot the switch for the mode to take effect.
<SwitchC> system-view
[SwitchC] hardware-resource vxlan border24k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchC] quit
<SwitchC> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
2. On VM 1 and VM 3, specify 10.1.1.1 as the gateway address. On VM 2 and VM 4, specify 10.1.2.1 as the gateway address. (Details not shown.)
3. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 21. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D) for them to reach one another. (Details not shown.)
4. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] evpn encapsulation vxlan
[SwitchA-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchA-vsi-vpnb] vxlan 20
[SwitchA-vsi-vpnb-vxlan-20] quit
[SwitchA-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 200
[SwitchA-bgp-default] peer 4.4.4.4 as-number 200
[SwitchA-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 2000 to match VLAN 3.
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 2000
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] encapsulation s-vid 3
# Map Ethernet service instance 2000 to VSI vpnb.
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] xconnect vsi vpnb
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] quit
[SwitchA-Ten-GigabitEthernet1/0/1] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchA] ip vpn-instance l3vpna
[SwitchA-vpn-instance-l3vpna] route-distinguisher 1:1
[SwitchA-vpn-instance-l3vpna] address-family ipv4
[SwitchA-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchA-vpn-ipv4-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] address-family evpn
[SwitchA-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchA-vpn-evpn-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchA-Vsi-interface1] mac-address 1-1-1
[SwitchA-Vsi-interface1] distributed-gateway local
[SwitchA-Vsi-interface1] local-proxy-arp enable
[SwitchA-Vsi-interface1] quit
# Configure VSI-interface 2.
[SwitchA] interface vsi-interface 2
[SwitchA-Vsi-interface2] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface2] ip address 10.1.2.1 255.255.255.0
[SwitchA-Vsi-interface2] mac-address 2-2-2
[SwitchA-Vsi-interface2] distributed-gateway local
[SwitchA-Vsi-interface2] local-proxy-arp enable
[SwitchA-Vsi-interface2] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchA] interface vsi-interface 3
[SwitchA-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface3] l3-vni 1000
[SwitchA-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] gateway vsi-interface 1
[SwitchA-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] gateway vsi-interface 2
[SwitchA-vsi-vpnb] quit
5. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] evpn encapsulation vxlan
[SwitchB-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchB-vsi-vpnb] vxlan 20
[SwitchB-vsi-vpnb-vxlan-20] quit
[SwitchB-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchB] bgp 200
[SwitchB-bgp-default] peer 4.4.4.4 as-number 200
[SwitchB-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchB-Ten-GigabitEthernet1/0/1] quit
# On Ten-GigabitEthernet 1/0/2, create Ethernet service instance 2000 to match VLAN 3.
[SwitchB] interface ten-gigabitethernet 1/0/2
[SwitchB-Ten-GigabitEthernet1/0/2] service-instance 2000
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] encapsulation s-vid 3
# Map Ethernet service instance 2000 to VSI vpnb.
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] xconnect vsi vpnb
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] quit
[SwitchB-Ten-GigabitEthernet1/0/2] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchB] ip vpn-instance l3vpna
[SwitchB-vpn-instance-l3vpna] route-distinguisher 1:2
[SwitchB-vpn-instance-l3vpna] address-family ipv4
[SwitchB-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchB-vpn-ipv4-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] address-family evpn
[SwitchB-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchB-vpn-evpn-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchB] interface vsi-interface 1
[SwitchB-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchB-Vsi-interface1] mac-address 1-1-1
[SwitchB-Vsi-interface1] distributed-gateway local
[SwitchB-Vsi-interface1] local-proxy-arp enable
[SwitchB-Vsi-interface1] quit
# Configure VSI-interface 2.
[SwitchB] interface vsi-interface 2
[SwitchB-Vsi-interface2] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface2] ip address 10.1.2.1 255.255.255.0
[SwitchB-Vsi-interface2] mac-address 2-2-2
[SwitchB-Vsi-interface2] distributed-gateway local
[SwitchB-Vsi-interface2] local-proxy-arp enable
[SwitchB-Vsi-interface2] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchB] interface vsi-interface 3
[SwitchB-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface3] l3-vni 1000
[SwitchB-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] gateway vsi-interface 1
[SwitchB-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] gateway vsi-interface 2
[SwitchB-vsi-vpnb] quit
6. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Set the VXLAN hardware resource mode.
[SwitchC] hardware-resource vxlan border8k
# Disable remote MAC address learning and remote ARP learning.
[SwitchC] vxlan tunnel mac-learning disable
[SwitchC] vxlan tunnel arp-learning disable
# Configure BGP to advertise BGP EVPN routes.
[SwitchC] bgp 200
[SwitchC-bgp-default] peer 4.4.4.4 as-number 200
[SwitchC-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchC] ip vpn-instance l3vpna
[SwitchC-vpn-instance-l3vpna] route-distinguisher 1:3
[SwitchC-vpn-instance-l3vpna] address-family ipv4
[SwitchC-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchC-vpn-ipv4-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] address-family evpn
[SwitchC-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchC-vpn-evpn-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchC] interface vsi-interface 3
[SwitchC-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchC-Vsi-interface3] l3-vni 1000
[SwitchC-Vsi-interface3] quit
# Configure a default route. The next hop is the IP address of a device in the Layer 3 network.
[SwitchC] ip route-static vpn-instance l3vpna 0.0.0.0 0 20.1.1.100
# Import the default route to the BGP IPv4 unicast routing table of VPN instance l3vpna.
[SwitchC] bgp 200
[SwitchC-bgp-default] ip vpn-instance l3vpna
[SwitchC-bgp-default-l3vpna] address-family ipv4 unicast
[SwitchC-bgp-default-ipv4-l3vpna] default-route imported
[SwitchC-bgp-default-ipv4-l3vpna] import-route static
[SwitchC-bgp-default-ipv4-l3vpna] quit
[SwitchC-bgp-default-l3vpna] quit
[SwitchC-bgp-default] quit
# Associate VLAN-interface 20 with VPN instance l3vpna.
[SwitchC] interface vlan-interface 20
[SwitchC-Vlan-interface20] ip binding vpn-instance l3vpna
[SwitchC-Vlan-interface20] ip address 20.1.1.3 24
[SwitchC-Vlan-interface20] quit
7. Configure Switch D:
# Establish BGP connections with other transport network switches.
<SwitchD> system-view
[SwitchD] bgp 200
[SwitchD-bgp-default] group evpn
[SwitchD-bgp-default] peer 1.1.1.1 group evpn
[SwitchD-bgp-default] peer 2.2.2.2 group evpn
[SwitchD-bgp-default] peer 3.3.3.3 group evpn
[SwitchD-bgp-default] peer evpn as-number 200
[SwitchD-bgp-default] peer evpn connect-interface loopback 0
# Configure BGP to advertise BGP EVPN routes, and disable route target filtering for BGP EVPN routes.
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer evpn enable
[SwitchD-bgp-default-evpn] undo policy vpn-target
# Configure Switch D as an RR.
[SwitchD-bgp-default-evpn] peer evpn reflect-client
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
Verifying the configuration
1. Verify the distributed EVPN gateway settings on Switch A:
# Verify that Switch A has advertised the IP prefix advertisement routes for the gateways and the MAC/IP advertisement routes and IMET routes for each VSI. Verify that Switch A has received the IP prefix advertisement routes for the gateways and the MAC/IP advertisement routes and IMET routes for each VSI from Switch B. (Details not shown.)
# Verify that the VXLAN tunnel interfaces are up on Switch A. (This example uses Tunnel 0.)
[SwitchA] display interface tunnel 0
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.1.1.1, destination 2.2.2.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 9 packets, 882 bytes, 0 drops
Output: 9 packets, 882 bytes, 0 drops
# Verify that the VSI interfaces are up on Switch A. (This example uses VSI-interface 1.)
[SwitchA] display interface vsi-interface brief
Brief information on interfaces in route mode:
Link: ADM - administratively down; Stby - standby
Protocol: (s) - spoofing
Interface Link Protocol Primary IP Description
Vsi1 UP UP 10.1.1.1
Vsi2 UP UP 10.1.2.1
# Verify that the VXLAN tunnels have been assigned to the VXLANs, and that the VSI interfaces are the gateway interfaces of their respective VXLANs.
[SwitchA] display l2vpn vsi verbose
VSI Name: Auto_L3VNI1000_3
VSI Index : 1
VSI State : Down
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 3
VXLAN ID : 1000
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 1
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000001 Up Auto Disabled
Tunnel1 0x5000002 Up Auto Disabled
ACs:
AC Link ID State Type
XGE1/0/1 srv1000 0 Up Manual
VSI Name: vpnb
VSI Index : 2
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 2
VXLAN ID : 20
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000001 Up Auto Disabled
Tunnel1 0x5000002 Up Auto Disabled
ACs:
AC Link ID State Type
XGE1/0/1 srv2000 0 Up Manual
# Verify that Switch A has created ARP entries for the VMs. (Details not shown.)
# Verify that Switch A has created EVPN ARP entries for the local VMs.
[SwitchA] display evpn route arp
Flags: D - Dynamic B - BGP L - Local active
G - Gateway S - Static M - Mapping I - Invalid
VPN instance: l3vpna Interface: Vsi-interface1
IP address MAC address Router MAC VSI Index Flags
10.1.1.1 0001-0001-0001 a0ce-7e40-0400 0 GL
10.1.1.10 0000-1234-0001 a0ce-7e40-0400 0 DL
10.1.2.10 0000-1234-0002 a0ce-7e40-0400 0 DL
10.1.1.20 0000-1234-0003 a0ce-7e40-0400 0 B
10.1.2.20 0000-1234-0004 a0ce-7e40-0400 0 B
2. Verify that VM 1, VM 2, VM 3, and VM 4 can communicate with one another. (Details not shown.)
Example: Configuring distributed EVPN gateways in symmetric IRB mode (IPv6 underlay network)
Network configuration
As shown in Figure 22:
· Configure VXLAN 10 and VXLAN 20 on Switch A and Switch B to provide connectivity for the VMs in the VXLANs across the network sites.
· Configure Switch A and Switch B as distributed EVPN gateways to provide gateway services in symmetric IRB mode. Configure Switch C as a border gateway to provide access to the connected Layer 3 network.
· Configure Switch D as an RR to reflect BGP EVPN routes between Switch A, Switch B, and Switch C.
|
|
NOTE: This example provides configuration of IPv6 sites. The configuration procedure does not differ between IPv4 and IPv6 sites. |
Procedure
1. Set the VXLAN hardware resource mode:
# Set the VXLAN hardware resource mode on Switch A and Switch B and reboot the switches for the mode to take effect. This step uses Switch A as an example.
<SwitchA> system-view
[SwitchA] hardware-resource vxlan l3gw16k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchA] quit
<SwitchA> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
# Set the VXLAN hardware resource mode on Switch C and reboot the switch for the mode to take effect.
<SwitchC> system-view
[SwitchC] hardware-resource vxlan border24k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchC] quit
<SwitchC> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
2. On VM 1 and VM 3, specify 11::1 as the gateway address. On VM 2 and VM 4, specify 12::1 as the gateway address. (Details not shown.)
3. Configure IPv6 addresses and unicast routing settings:
# Assign IPv6 addresses to interfaces, as shown in Figure 22. (Details not shown.)
# Configure OSPFv3 on all transport network switches (Switches A through D) for them to reach one another. (Details not shown.)
4. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC address learning and remote ND learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel nd-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] evpn encapsulation vxlan
[SwitchA-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchA-vsi-vpnb] vxlan 20
[SwitchA-vsi-vpnb-vxlan-20] quit
[SwitchA-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 200
[SwitchA-bgp-default] router-id 1.1.1.1
[SwitchA-bgp-default] peer 4::4 as-number 200
[SwitchA-bgp-default] peer 4::4 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 4::4 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 2000 to match VLAN 3.
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 2000
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] encapsulation s-vid 3
# Map Ethernet service instance 2000 to VSI vpnb.
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] xconnect vsi vpnb
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] quit
[SwitchA-Ten-GigabitEthernet1/0/1] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchA] ip vpn-instance l3vpna
[SwitchA-vpn-instance-l3vpna] route-distinguisher 1:1
[SwitchA-vpn-instance-l3vpna] address-family ipv6
[SwitchA-vpn-ipv6-l3vpna] vpn-target 2:2
[SwitchA-vpn-ipv6-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] address-family evpn
[SwitchA-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchA-vpn-evpn-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface1] ipv6 address 11::1 64
[SwitchA-Vsi-interface1] mac-address 1-1-1
[SwitchA-Vsi-interface1] distributed-gateway local
[SwitchA-Vsi-interface1] local-proxy-nd enable
[SwitchA-Vsi-interface1] quit
# Configure VSI-interface 2.
[SwitchA] interface vsi-interface 2
[SwitchA-Vsi-interface2] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface2] ipv6 address 12::1 64
[SwitchA-Vsi-interface2] mac-address 2-2-2
[SwitchA-Vsi-interface2] distributed-gateway local
[SwitchA-Vsi-interface2] local-proxy-nd enable
[SwitchA-Vsi-interface2] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchA] interface vsi-interface 3
[SwitchA-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface3] ipv6 address auto link-local
[SwitchA-Vsi-interface3] l3-vni 1000
[SwitchA-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] gateway vsi-interface 1
[SwitchA-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] gateway vsi-interface 2
[SwitchA-vsi-vpnb] quit
5. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC address learning and remote ND learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel nd-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] evpn encapsulation vxlan
[SwitchB-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchB-vsi-vpnb] vxlan 20
[SwitchB-vsi-vpnb-vxlan-20] quit
[SwitchB-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchB] bgp 200
[SwitchB-bgp-default] router-id 2.2.2.2
[SwitchB-bgp-default] peer 4::4 as-number 200
[SwitchB-bgp-default] peer 4::4 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 4::4 enable
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchB-Ten-GigabitEthernet1/0/1] quit
# On Ten-GigabitEthernet 1/0/2, create Ethernet service instance 2000 to match VLAN 3.
[SwitchB] interface ten-gigabitethernet 1/0/2
[SwitchB-Ten-GigabitEthernet1/0/2] service-instance 2000
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] encapsulation s-vid 3
# Map Ethernet service instance 2000 to VSI vpnb.
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] xconnect vsi vpnb
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] quit
[SwitchB-Ten-GigabitEthernet1/0/2] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchB] ip vpn-instance l3vpna
[SwitchB-vpn-instance-l3vpna] route-distinguisher 1:2
[SwitchB-vpn-instance-l3vpna] address-family ipv6
[SwitchB-vpn-ipv6-l3vpna] vpn-target 2:2
[SwitchB-vpn-ipv6-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] address-family evpn
[SwitchB-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchB-vpn-evpn-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchB] interface vsi-interface 1
[SwitchB-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface1] ipv6 address 11::1 64
[SwitchB-Vsi-interface1] mac-address 1-1-1
[SwitchB-Vsi-interface1] distributed-gateway local
[SwitchB-Vsi-interface1] local-proxy-nd enable
[SwitchB-Vsi-interface1] quit
# Configure VSI-interface 2.
[SwitchB] interface vsi-interface 2
[SwitchB-Vsi-interface2] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface2] ipv6 address 12::1 64
[SwitchB-Vsi-interface2] mac-address 2-2-2
[SwitchB-Vsi-interface2] distributed-gateway local
[SwitchB-Vsi-interface2] local-proxy-nd enable
[SwitchB-Vsi-interface2] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchB] interface vsi-interface 3
[SwitchB-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface3] ipv6 address auto link-local
[SwitchB-Vsi-interface3] l3-vni 1000
[SwitchB-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] gateway vsi-interface 1
[SwitchB-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] gateway vsi-interface 2
[SwitchB-vsi-vpnb] quit
6. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Disable remote MAC address learning and remote ND learning.
[SwitchC] vxlan tunnel mac-learning disable
[SwitchC] vxlan tunnel nd-learning disable
# Configure BGP to advertise BGP EVPN routes.
[SwitchC] bgp 200
[SwitchC-bgp-default] router-id 3.3.3.3
[SwitchC-bgp-default] peer 4::4 as-number 200
[SwitchC-bgp-default] peer 4::4 connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 4::4 enable
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchC] ip vpn-instance l3vpna
[SwitchC-vpn-instance-l3vpna] route-distinguisher 1:3
[SwitchC-vpn-instance-l3vpna] address-family ipv6
[SwitchC-vpn-ipv6-l3vpna] vpn-target 2:2
[SwitchC-vpn-ipv6-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] address-family evpn
[SwitchC-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchC-vpn-evpn-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchC] interface vsi-interface 3
[SwitchC-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchC-Vsi-interface3] ipv6 address auto link-local
[SwitchC-Vsi-interface3] l3-vni 1000
[SwitchC-Vsi-interface3] quit
# Configure a default route. The next hop is the IP address of a device in the Layer 3 network.
[SwitchC] ipv6 route-static vpn-instance l3vpna :: 0 20::100
# Import the default route to the BGP IPv6 unicast routing table of VPN instance l3vpna.
[SwitchC] bgp 200
[SwitchC-bgp-default] ip vpn-instance l3vpna
[SwitchC-bgp-default-l3vpna] address-family ipv6 unicast
[SwitchC-bgp-default-ipv6-l3vpna] default-route imported
[SwitchC-bgp-default-ipv6-l3vpna] import-route static
[SwitchC-bgp-default-ipv6-l3vpna] quit
[SwitchC-bgp-default-l3vpna] quit
[SwitchC-bgp-default] quit
# Associate VLAN-interface 20 with VPN instance l3vpna and assign an IPv6 address to the interface.
[SwitchC] interface vlan-interface 20
[SwitchC-Vlan-interface20] ip binding vpn-instance l3vpna
[SwitchC-Vlan-interface20] ipv6 address 20::1 64
[SwitchC-Vlan-interface20] quit
7. Configure Switch D:
# Establish BGP connections with other transport network switches.
<SwitchD> system-view
[SwitchD] bgp 200
[SwitchD-bgp-default] router-id 4.4.4.4
[SwitchD-bgp-default] group evpn
[SwitchD-bgp-default] peer 1::1 group evpn
[SwitchD-bgp-default] peer 2::2 group evpn
[SwitchD-bgp-default] peer 3::3 group evpn
[SwitchD-bgp-default] peer evpn as-number 200
[SwitchD-bgp-default] peer evpn connect-interface loopback 0
# Configure BGP to advertise BGP EVPN routes, and disable route target filtering for BGP EVPN routes.
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer evpn enable
[SwitchD-bgp-default-evpn] undo policy vpn-target
# Configure Switch D as an RR.
[SwitchD-bgp-default-evpn] peer evpn reflect-client
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
Verifying the configuration
1. Verify the distributed EVPN gateway settings on Switch A:
# Verify that Switch A has advertised the IP prefix advertisement routes for the gateways and the MAC/IP advertisement routes and IMET routes for each VSI. Verify that Switch A has received the IP prefix advertisement routes for the gateways and the MAC/IP advertisement routes and IMET routes for each VSI from Switch B. (Details not shown.)
# Verify that the VXLAN tunnel interfaces are up on Switch A. (This example uses Tunnel 0.)
[SwitchA] display interface tunnel 0
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1::1, destination 2::2
Tunnel protocol/transport UDP_VXLAN/IPv6
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VSI interfaces are up on Switch A. (This example uses VSI-interface 1.)
[SwitchA] display ipv6 interface vsi-interface brief
*down: administratively down
(s): spoofing
Interface Physical Protocol IPv6 Address
Vsi1 UP UP 11::1
Vsi2 UP UP 12::1
# Verify that the VXLAN tunnels have been assigned to the VXLANs, and that the VSI interfaces are the gateway interfaces of their respective VXLANs.
[SwitchA] display l2vpn vsi verbose
VSI Name: Auto_L3VNI1000_3
VSI Index : 1
VSI State : Down
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 3
VXLAN ID : 1000
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 1
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000001 Up Auto Disabled
Tunnel1 0x5000002 Up Auto Disabled
ACs:
AC Link ID State Type
XGE1/0/1 srv1000 0 Up Manual
VSI Name: vpnb
VSI Index : 2
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 2
VXLAN ID : 20
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000001 Up Auto Disabled
Tunnel1 0x5000002 Up Auto Disabled
ACs:
AC Link ID State Type
XGE1/0/1 srv2000 0 Up Manual
# Verify that Switch A has created EVPN ND entries for the local VMs.
[SwitchA] display evpn route nd
Flags: D - Dynamic B - BGP L - Local active
G - Gateway S - Static M - Mapping I - Invalid
VPN instance: l3vpna Interface: Vsi-interface1
IPv6 address : 11::1
MAC address : 0001-0001-0001 Router MAC : 06dc-93de-0100
VSI index : 0 Flags : GL
IPv6 address : 11::7
MAC address : 06dc-98ca-0206 Router MAC : 06dc-93de-0100
VSI index : 0 Flags : DL
IPv6 address : 11::8
MAC address : 06dc-a8dd-0506 Router MAC : 06dc-a235-0400
VSI index : 0 Flags : B
VPN instance: l3vpna Interface: Vsi-interface2
IPv6 address : 12::1
MAC address : 0002-0002-0002 Router MAC : 06dc-93de-0100
VSI index : 1 Flags : GL
IPv6 address : 12::7
MAC address : 06dc-9ca0-0306 Router MAC : 06dc-93de-0100
VSI index : 1 Flags : DL
IPv6 address : 12::8
MAC address : 06dc-ad91-0606 Router MAC : 06dc-a235-0400
VSI index : 1 Flags : B
2. Verify that VM 1, VM 2, VM 3, and VM 4 can communicate with one another. (Details not shown.)
Example: Configuring distributed IPv4 EVPN gateways in asymmetric IRB mode
Network configuration
As shown in Figure 23:
· Configure VXLAN 10 and VXLAN 20 on Switch A and Switch B to provide connectivity for the VMs in the VXLANs across the network sites.
· Configure Switch A and Switch B as distributed EVPN gateways to provide gateway services in asymmetric IRB mode. Configure Switch C as a border gateway to provide access to the connected Layer 3 network.
· Configure Switch D as an RR to reflect BGP EVPN routes between Switch A, Switch B, and Switch C.
Procedure
1. Set the VXLAN hardware resource mode:
# Set the VXLAN hardware resource mode on Switch A and Switch B and reboot the switches for the mode to take effect. This step uses Switch A as an example.
<SwitchA> system-view
[SwitchA] hardware-resource vxlan l3gw16k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchA] quit
<SwitchA> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
# Set the VXLAN hardware resource mode on Switch C and reboot the switch for the mode to take effect.
<SwitchC> system-view
[SwitchC] hardware-resource vxlan border24k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchC] quit
<SwitchC> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
2. Specify 10.1.1.1, 10.1.2.1, 20.1.1.1, and 20.1.2.1 as the gateway addresses on VM 1, VM 2, VM 3, and VM 4, respectively. (Details not shown.)
3. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 23. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D) for them to reach one another. (Details not shown.)
4. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel arp-learning disable
# Enable asymmetric IRB mode for EVPN VXLAN.
[SwitchA] evpn irb asymmetric
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] evpn encapsulation vxlan
[SwitchA-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchA-vsi-vpnb] vxlan 20
[SwitchA-vsi-vpnb-vxlan-20] quit
[SwitchA-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 200
[SwitchA-bgp-default] peer 4.4.4.4 as-number 200
[SwitchA-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 2000 to match VLAN 3.
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 2000
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] encapsulation s-vid 3
# Map Ethernet service instance 2000 to VSI vpnb.
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] xconnect vsi vpnb
[SwitchA-Ten-GigabitEthernet1/0/1-srv2000] quit
[SwitchA-Ten-GigabitEthernet1/0/1] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchA] ip vpn-instance l3vpna
[SwitchA-vpn-instance-l3vpna] route-distinguisher 1:1
[SwitchA-vpn-instance-l3vpna] address-family ipv4
[SwitchA-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchA-vpn-ipv4-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] address-family evpn
[SwitchA-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchA-vpn-evpn-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchA-Vsi-interface1] mac-address 1-1-1
[SwitchA-Vsi-interface1] distributed-gateway local
[SwitchA-Vsi-interface1] local-proxy-arp enable
[SwitchA-Vsi-interface1] quit
# Configure VSI-interface 2.
[SwitchA] interface vsi-interface 2
[SwitchA-Vsi-interface2] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface2] ip address 10.1.2.1 255.255.255.0
[SwitchA-Vsi-interface2] mac-address 2-2-2
[SwitchA-Vsi-interface2] distributed-gateway local
[SwitchA-Vsi-interface2] local-proxy-arp enable
[SwitchA-Vsi-interface2] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchA] interface vsi-interface 3
[SwitchA-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface3] l3-vni 1000
[SwitchA-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] gateway vsi-interface 1
[SwitchA-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] gateway vsi-interface 2
[SwitchA-vsi-vpnb] quit
5. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel arp-learning disable
# Enable asymmetric IRB mode for EVPN VXLAN.
[SwitchA] evpn irb asymmetric
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] evpn encapsulation vxlan
[SwitchB-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchB-vsi-vpnb] vxlan 20
[SwitchB-vsi-vpnb-vxlan-20] quit
[SwitchB-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchB] bgp 200
[SwitchB-bgp-default] peer 4.4.4.4 as-number 200
[SwitchB-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchB-Ten-GigabitEthernet1/0/1] quit
# On Ten-GigabitEthernet 1/0/2, create Ethernet service instance 2000 to match VLAN 3.
[SwitchB] interface ten-gigabitethernet 1/0/2
[SwitchB-Ten-GigabitEthernet1/0/2] service-instance 2000
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] encapsulation s-vid 3
# Map Ethernet service instance 2000 to VSI vpnb.
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] xconnect vsi vpnb
[SwitchB-Ten-GigabitEthernet1/0/2-srv2000] quit
[SwitchB-Ten-GigabitEthernet1/0/2] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchB] ip vpn-instance l3vpna
[SwitchB-vpn-instance-l3vpna] route-distinguisher 1:2
[SwitchB-vpn-instance-l3vpna] address-family ipv4
[SwitchB-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchB-vpn-ipv4-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] address-family evpn
[SwitchB-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchB-vpn-evpn-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchB] interface vsi-interface 1
[SwitchB-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface1] ip address 20.1.1.1 255.255.255.0
[SwitchB-Vsi-interface1] mac-address 1-1-1
[SwitchB-Vsi-interface1] distributed-gateway local
[SwitchB-Vsi-interface1] local-proxy-arp enable
[SwitchB-Vsi-interface1] quit
# Configure VSI-interface 2.
[SwitchB] interface vsi-interface 2
[SwitchB-Vsi-interface2] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface2] ip address 20.1.2.1 255.255.255.0
[SwitchB-Vsi-interface2] mac-address 2-2-2
[SwitchB-Vsi-interface2] distributed-gateway local
[SwitchB-Vsi-interface2] local-proxy-arp enable
[SwitchB-Vsi-interface2] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchB] interface vsi-interface 3
[SwitchB-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface3] l3-vni 1000
[SwitchB-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] gateway vsi-interface 1
[SwitchB-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] gateway vsi-interface 2
[SwitchB-vsi-vpnb] quit
6. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchC] vxlan tunnel mac-learning disable
[SwitchC] vxlan tunnel arp-learning disable
# Configure BGP to advertise BGP EVPN routes.
[SwitchC] bgp 200
[SwitchC-bgp-default] peer 4.4.4.4 as-number 200
[SwitchC-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchC] ip vpn-instance l3vpna
[SwitchC-vpn-instance-l3vpna] route-distinguisher 1:3
[SwitchC-vpn-instance-l3vpna] address-family ipv4
[SwitchC-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchC-vpn-ipv4-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] address-family evpn
[SwitchC-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchC-vpn-evpn-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchC] interface vsi-interface 3
[SwitchC-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchC-Vsi-interface3] l3-vni 1000
[SwitchC-Vsi-interface3] quit
# Configure a default route. The next hop is the IP address of a device in the Layer 3 network.
[SwitchC] ip route-static vpn-instance l3vpna 0.0.0.0 0 20.1.1.100
# Import the default route to the BGP IPv4 unicast routing table of VPN instance l3vpna.
[SwitchC] bgp 200
[SwitchC-bgp-default] ip vpn-instance l3vpna
[SwitchC-bgp-default-l3vpna] address-family ipv4 unicast
[SwitchC-bgp-default-ipv4-l3vpna] default-route imported
[SwitchC-bgp-default-ipv4-l3vpna] import-route static
[SwitchC-bgp-default-ipv4-l3vpna] quit
[SwitchC-bgp-default-l3vpna] quit
[SwitchC-bgp-default] quit
# Associate VLAN-interface 20 with VPN instance l3vpna. VLAN-interface 20 provides access to the Layer 3 network connected to Switch C.
[SwitchC] interface vlan-interface 20
[SwitchC-Vlan-interface20] ip binding vpn-instance l3vpna
[SwitchC-Vlan-interface20] ip address 20.1.1.3 24
[SwitchC-Vlan-interface20] quit
7. Configure Switch D:
# Establish BGP connections with other transport network switches.
<SwitchD> system-view
[SwitchD] bgp 200
[SwitchD-bgp-default] group evpn
[SwitchD-bgp-default] peer 1.1.1.1 group evpn
[SwitchD-bgp-default] peer 2.2.2.2 group evpn
[SwitchD-bgp-default] peer 3.3.3.3 group evpn
[SwitchD-bgp-default] peer evpn as-number 200
[SwitchD-bgp-default] peer evpn connect-interface loopback 0
# Configure BGP to advertise BGP EVPN routes, and disable route target filtering for BGP EVPN routes.
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer evpn enable
[SwitchD-bgp-default-evpn] undo policy vpn-target
# Configure Switch D as an RR.
[SwitchD-bgp-default-evpn] peer evpn reflect-client
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
Verifying the configuration
1. Verify the distributed EVPN gateway settings on Switch A:
# Verify that Switch A has advertised the IP prefix advertisement routes for the gateways and the MAC/IP advertisement routes and IMET routes for each VSI. Verify that Switch A has received the IP prefix advertisement routes for the gateways and the MAC/IP advertisement routes and IMET routes for each VSI from Switch B. (Details not shown.)
# Verify that the VXLAN tunnel interfaces are up on Switch A. (This example uses Tunnel 0.)
[SwitchA] display interface tunnel 0
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.1.1.1, destination 2.2.2.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VSI interfaces are up on Switch A. (This example uses VSI-interface 1.)
[SwitchA] display interface vsi-interface 1
Vsi-interface1
Current state: UP
Line protocol state: UP
Description: Vsi-interface1 Interface
Bandwidth: 1000000 kbps
Maximum transmission unit: 1500
Internet address: 10.1.1.1/24 (primary)
IP packet frame type: Ethernet II, hardware address: 0003-0003-0003
IPv6 packet frame type: Ethernet II, hardware address: 0003-0003-0003
Physical: Unknown, baudrate: 1000000 kbps
Last clearing of counters: Never
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to the VXLANs, and that the VSI interfaces are the gateway interfaces of their respective VXLANs.
[SwitchA] display l2vpn vsi verbose
VSI Name: Auto_L3VNI1000_3
VSI Index : 1
VSI State : Down
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 3
VXLAN ID : 1000
Tunnel Statistics : Disabled
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 1
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
ACs:
AC Link ID State Type
XGE1/0/1 srv1000 0x0 Up Manual
VSI Name: vpnb
VSI Index : 2
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 2
VXLAN ID : 20
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
ACs:
AC Link ID State Type
XGE1/0/1 srv2000 0x0 Up Manual
# Verify that Switch A has created ARP entries for the VMs. (Details not shown.)
# Verify that Switch A has created EVPN ARP entries for the VMs.
[SwitchA] display evpn route arp
Flags: D - Dynamic B - BGP L - Local active
G - Gateway S - Static M - Mapping I - Invalid
E - Multihoming ES sync F - Leaf
VPN instance: l3vpna Interface: Vsi-interface1
IP address MAC address Router MAC VSI index Flags
10.1.1.1 0001-0001-0001 522b-3413-0200 0 GL
10.1.1.10 521f-b814-0106 522b-3413-0200 0 DL
20.1.1.20 522b-3c6a-0406 522b-38cd-0300 0 B
2. Verify that VM 1, VM 2, VM 3, and VM 4 can communicate with one another. (Details not shown.)
Example: Configuring communication between EVPN networks and the public network
Network configuration
As shown in Figure 24:
· Configure VXLAN 10, VXLAN 20, and VXLAN 30 on Switch A, Switch B, and Switch C to meet the following requirements:
¡ VXLAN 10 and VXLAN 20 are on the private network, and VXLAN 30 is on the public network.
¡ VXLAN 10 can communicate with VXLAN 20 and VXLAN 30, and VXLAN 20 is isolated from VXLAN 30.
· Configure Switch A, Switch B, and Switch C as distributed EVPN gateways to provide gateway services for the VXLANs.
· Configure Switch D as an RR to reflect BGP EVPN routes between Switch A, Switch B, and Switch C.
|
|
NOTE: This example provides configuration of IPv4 sites over an IPv4 underlay network. The configuration procedure does not differ between IPv4 and IPv6 sites or underlay networks. |
Procedure
1. Set the VXLAN hardware resource mode on Switch A, Switch B, and Switch C and reboot the switches for the mode to take effect. This step uses Switch A as an example.
<SwitchA> system-view
[SwitchA] hardware-resource vxlan l3gw16k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchA] quit
<SwitchA> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
2. On VM 1, VM 2, and VM 3, specify 10.1.1.1, 10.1.2.1, and 10.1.3.1 as the gateway address, respectively. (Details not shown.)
3. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 24. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D) for them to reach one another. (Details not shown.)
4. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 200
[SwitchA-bgp-default] peer 4.4.4.4 as-number 200
[SwitchA-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 1.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 1
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchA] ip vpn-instance l3vpna
[SwitchA-vpn-instance-l3vpna] route-distinguisher 1:1
[SwitchA-vpn-instance-l3vpna] address-family ipv4
[SwitchA-vpn-ipv4-l3vpna] vpn-target 1:1
[SwitchA-vpn-ipv4-l3vpna] vpn-target 2:2 import-extcommunity
[SwitchA-vpn-ipv4-l3vpna] vpn-target 3:3 import-extcommunity
[SwitchA-vpn-ipv4-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] address-family evpn
[SwitchA-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchA-vpn-evpn-l3vpna] vpn-target 2:2 import-extcommunity
[SwitchA-vpn-evpn-l3vpna] vpn-target 3:3 import-extcommunity
[SwitchA-vpn-evpn-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchA-Vsi-interface1] distributed-gateway local
[SwitchA-Vsi-interface1] local-proxy-arp enable
[SwitchA-Vsi-interface1] quit
# Associate VSI-interface 2 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchA] interface vsi-interface 2
[SwitchA-Vsi-interface2] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface2] l3-vni 1000
[SwitchA-Vsi-interface2] quit
# Create VSI-interface 3 and configure its L3 VXLAN ID as 2000 for matching routes from Switch B.
[SwitchA] interface vsi-interface 3
[SwitchA-Vsi-interface3] l3-vni 2000
[SwitchA-Vsi-interface3] quit
# Create VSI-interface 4 and configure its L3 VXLAN ID as 3000 for matching routes from Switch C.
[SwitchA] interface vsi-interface 4
[SwitchA-Vsi-interface4] l3-vni 3000
[SwitchA-Vsi-interface4] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] gateway vsi-interface 1
[SwitchA-vsi-vpna] quit
5. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] evpn encapsulation vxlan
[SwitchB-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchB-vsi-vpnb] vxlan 20
[SwitchB-vsi-vpnb-vxlan-20] quit
[SwitchB-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchB] bgp 200
[SwitchB-bgp-default] peer 4.4.4.4 as-number 200
[SwitchB-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpnb.
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpnb
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchB-Ten-GigabitEthernet1/0/1] quit
# Configure RD and route target settings for VPN instance l3vpnb.
[SwitchB] ip vpn-instance l3vpnb
[SwitchB-vpn-instance-l3vpnb] route-distinguisher 2:2
[SwitchB-vpn-instance-l3vpnb] address-family ipv4
[SwitchB-vpn-ipv4-l3vpnb] vpn-target 2:2
[SwitchB-vpn-ipv4-l3vpnb] vpn-target 1:1 import-extcommunity
[SwitchB-vpn-ipv4-l3vpnb] quit
[SwitchB-vpn-instance-l3vpnb] address-family evpn
[SwitchB-vpn-evpn-l3vpnb] vpn-target 2:2
[SwitchB-vpn-evpn-l3vpnb] vpn-target 1:1 import-extcommunity
[SwitchB-vpn-evpn-l3vpnb] quit
[SwitchB-vpn-instance-l3vpnb] quit
# Configure VSI-interface 1.
[SwitchB] interface vsi-interface 1
[SwitchB-Vsi-interface1] ip binding vpn-instance l3vpnb
[SwitchB-Vsi-interface1] ip address 10.1.2.1 255.255.255.0
[SwitchB-Vsi-interface1] distributed-gateway local
[SwitchB-Vsi-interface1] local-proxy-arp enable
[SwitchB-Vsi-interface1] quit
# Create VSI-interface 2, and configure its L3 VXLAN ID as 1000 for matching routes from Switch A.
[SwitchB] interface vsi-interface 2
[SwitchB-Vsi-interface2] l3-vni 1000
[SwitchB-Vsi-interface2] qui
# Associate VSI-interface 3 with VPN instance l3vpnb, and configure the L3 VXLAN ID as 2000 for the VPN instance.
[SwitchB] interface vsi-interface 3
[SwitchB-Vsi-interface3] ip binding vpn-instance l3vpnb
[SwitchB-Vsi-interface3] l3-vni 2000
[SwitchB-Vsi-interface3] quit
# Create VSI-interface 4, and configure its L3 VXLAN ID as 3000 for matching routes from Switch C.
[SwitchB] interface vsi-interface 4
[SwitchB-Vsi-interface4] l3-vni 3000
[SwitchB-Vsi-interface4] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpnb.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] gateway vsi-interface 1
[SwitchB-vsi-vpnb] quit
6. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchC] vxlan tunnel mac-learning disable
[SwitchC] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpnc, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpnc
[SwitchC-vsi-vpnc] evpn encapsulation vxlan
[SwitchC-vsi-vpnc-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpnc-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpnc-evpn-vxlan] quit
# Create VXLAN 30.
[SwitchC-vsi-vpnc] vxlan 30
[SwitchC-vsi-vpnc-vxlan-30] quit
[SwitchC-vsi-vpnc] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchC] bgp 200
[SwitchC-bgp-default] peer 4.4.4.4 as-number 200
[SwitchC-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchC-bgp-default] address-family ipv4 unicast
[SwitchC-bgp-default-ipv4] quit
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Configure RD, route target, and L3 VXLAN ID settings for the public instance.
[SwitchC] ip public-instance
[SwitchC-public-instance] route-distinguisher 3:3
[SwitchC-public-instance] l3-vni 3000
[SwitchC-public-instance] address-family ipv4
[SwitchC-public-instance-ipv4] vpn-target 3:3
[SwitchC-public-instance-ipv4] vpn-target 1:1 import-extcommunity
[SwitchC-public-instance-ipv4] quit
[SwitchC-public-instance] address-family evpn
[SwitchC-public-instance-evpn]vpn-target 3:3
[SwitchC-public-instance-evpn] vpn-target 1:1 import-extcommunity
[SwitchC-public-instance-evpn] quit
[SwitchC-public-instance] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 3.
[SwitchC] interface ten-gigabitethernet 1/0/1
[SwitchC-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchC-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 3
# Map Ethernet service instance 1000 to VSI vpnc.
[SwitchC-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpnc
[SwitchC-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchC-Ten-GigabitEthernet1/0/1] quit
# Configure VSI-interface 1.
[SwitchC] interface vsi-interface 1
[SwitchC-Vsi-interface1] ip address 10.1.3.1 255.255.255.0
[SwitchC-Vsi-interface1] distributed-gateway local
[SwitchC-Vsi-interface1] local-proxy-arp enable
[SwitchC-Vsi-interface1] quit
# Create VSI-interface 2, and configure its L3 VXLAN ID as 1000 for matching routes from Switch A.
[SwitchC] interface vsi-interface 2
[SwitchC-Vsi-interface2] l3-vni 1000
[SwitchC-Vsi-interface2] quit
# Create VSI-interface 3, and configure its L3 VXLAN ID as 2000 for matching routes from Switch B.
[SwitchC] interface vsi-interface 3
[SwitchC-Vsi-interface3] l3-vni 2000
[SwitchC-Vsi-interface3] quit
# Create VSI-interface 4 for the public instance, and configure the L3 VXLAN ID as 3000 for the VSI interface.
[SwitchC] interface vsi-interface 4
[SwitchC-Vsi-interface4] l3-vni 3000
[SwitchC-Vsi-interface4] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpnc.
[SwitchC] vsi vpnc
[SwitchC-vsi-vpnc] gateway vsi-interface 1
[SwitchC-vsi-vpnc] quit
7. Configure Switch D:
# Establish BGP connections with other transport network switches.
<SwitchD> system-view
[SwitchD] bgp 200
[SwitchD-bgp-default] group evpn
[SwitchD-bgp-default] peer 1.1.1.1 group evpn
[SwitchD-bgp-default] peer 2.2.2.2 group evpn
[SwitchD-bgp-default] peer 3.3.3.3 group evpn
[SwitchD-bgp-default] peer evpn as-number 200
[SwitchD-bgp-default] peer evpn connect-interface loopback 0
# Configure BGP to advertise BGP EVPN routes, and disable route target filtering for BGP EVPN routes.
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer evpn enable
[SwitchD-bgp-default-evpn] undo policy vpn-target
# Configure Switch D as an RR.
[SwitchD-bgp-default-evpn] peer evpn reflect-client
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
Verifying the configuration
1. Verify the distributed EVPN gateway settings on Switch A:
# Verify that Switch A has advertised the IP prefix advertisement routes for the gateways and the MAC/IP advertisement routes and IMET routes for each VSI. Verify that Switch A has received the IP prefix advertisement routes for the gateways and the MAC/IP advertisement routes and IMET routes for each VSI from Switch B and Switch C. (Details not shown.)
# Verify that the VXLAN tunnel interfaces are up on Switch A.
[SwitchA] display interface tunnel
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.1.1.1, destination 2.2.2.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 15 packets, 1470 bytes, 0 drops
Output: 15 packets, 1470 bytes, 0 drops
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.1.1.1, destination 3.3.3.3
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 22 packets, 2156 bytes, 0 drops
Output: 23 packets, 2254 bytes, 0 drops
# Verify that the VSI interfaces are up on Switch A.
[SwitchA] display interface vsi-interface brief
Brief information on interfaces in route mode:
Link: ADM - administratively down; Stby - standby
Protocol: (s) - spoofing
Interface Link Protocol Primary IP Description
Vsi1 UP UP 10.1.1.1
Vsi2 UP UP --
Vsi3 UP UP --
Vsi4 UP UP --
# Verify that the VXLAN tunnels have been assigned to the VXLANs, and that the VSI interfaces are the gateway interfaces of their respective VXLANs.
[SwitchA] display l2vpn vsi verbose
VSI Name: Auto_L3VNI1000_2
VSI Index : 1
VSI State : Down
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 2
VXLAN ID : 1000
VSI Name: Auto_L3VNI2000_3
VSI Index : 2
VSI State : Down
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 3
VXLAN ID : 2000
VSI Name: Auto_L3VNI3000_4
VSI Index : 3
VSI State : Down
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 4
VXLAN ID : 3000
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 1
VXLAN ID : 10
ACs:
AC Link ID State Type
XGE1/0/1 srv1000 0 Up Manual
# Verify that Switch A has created ARP entries for the VMs. (Details not shown.)
2. Verify that VM 1 can communicate with VM 2 and VM 3, and VM 2 cannot communicate with VM 3. (Details not shown.)
Example: Configuring IPv4 EVPN M-LAG with a direct peer link
Network configuration
As shown in Figure 25, perform the following tasks to make sure the VMs can communicate with one another:
· Configure VXLAN 10 on Switch A and Switch B, and configure VXLAN 20 on Switch D.
· Configure EVPN M-LAG on Switch A and Switch B to virtualize them into one VTEP. The switches use a direct peer link.
· Configure Switch C as a centralized EVPN gateway and RR.
|
|
NOTE: This example provides configuration of IPv4 sites extended by an IPv4 underlay network. The configuration procedure does not differ between site or underlay network types. |
Procedure
1. Set the VXLAN hardware resource mode on Switch C and reboot the switch for the mode to take effect.
<SwitchC> system-view
[SwitchC] hardware-resource vxlan l3gw16k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchC] quit
<SwitchC> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
2. On VM 1 and VM 2, specify 10.1.1.1 as the gateway address. On VM 3, specify 10.1.2.1 as the gateway address. (Details not shown.)
3. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces (including loopback interfaces), as shown in Figure 25. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D) for them to reach one another. (Details not shown.)
# Execute the ospf peer hold-max-cost duration command on the interfaces used for setting up OSPF neighbor relationships. (Details not shown.)
4. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC learning and remote ARP learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel arp-learning disable
# Choose one of the following frame match criterion creation methods for dynamic ACs:
¡ Enable the device to create frame match criteria based on VXLAN IDs for the dynamic ACs on the peer link.
[SwitchA] l2vpn m-lag peer-link ac-match-rule vxlan-mapping
¡ Use the default setting for dynamic ACs on the peer link to use frame match criteria identical to those of site-facing ACs.
# Enable EVPN M-LAG, and specify the virtual VTEP address as 1.2.3.4.
[SwitchA] evpn m-lag group 1.2.3.4
# Configure M-LAG system parameters.
[SwitchA] m-lag system-mac 0001-0001-0001
[SwitchA] m-lag system-number 1
[SwitchA] m-lag system-priority 10
[SwitchA] m-lag keepalive ip destination 60.1.1.2 source 60.1.1.1
[SwitchA] m-lag restore-delay 180
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 3.
[SwitchA] interface bridge-aggregation 3
[SwitchA-Bridge-Aggregation3] link-aggregation mode dynamic
[SwitchA-Bridge-Aggregation3] quit
# Assign Ten-GigabitEthernet 1/0/3 to link aggregation group 3.
[SwitchA] interface ten-gigabitethernet 1/0/3
[SwitchA-Ten-GigabitEthernet1/0/3] port link-aggregation group 3
[SwitchA-Ten-GigabitEthernet1/0/3] quit
# Specify Bridge-Aggregation 3 as the peer-link interface.
[SwitchA] interface bridge-aggregation 3
[SwitchA-Bridge-Aggregation3] port m-lag peer-link 1
[SwitchA-Bridge-Aggregation3] quit
# Configure routing settings for Switch A and Switch B to have Layer 3 connectivity.
[SwitchA] vlan 100
[SwitchA-vlan100] quit
[SwitchA] interface Vlan-interface 100
[SwitchA-Vlan-interface100] ip address 100.1.1.1 255.255.255.0
[SwitchA-Vlan-interface100] ospf 1 area 0.0.0.0
[SwitchA-Vlan-interface100] quit
# Disable spanning tree on Ten-GigabitEthernet 1/0/5.
[SwitchA] interface ten-gigabitethernet 1/0/5
[SwitchA-Ten-GigabitEthernet1/0/5] undo stp enable
[SwitchA-Ten-GigabitEthernet1/0/5] quit
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 4.
[SwitchA] interface bridge-aggregation 4
[SwitchA-Bridge-Aggregation4] link-aggregation mode dynamic
[SwitchA-Bridge-Aggregation4] quit
# Assign Ten-GigabitEthernet 1/0/1 to link aggregation group 4.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] port link-aggregation group 4
[SwitchA-Ten-GigabitEthernet1/0/1] quit
# Assign Bridge-Aggregation 4 to M-LAG group 4.
[SwitchA] interface bridge-aggregation 4
[SwitchA-Bridge-Aggregation4] port m-lag group 4
[SwitchA-Bridge-Aggregation4] quit
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 5.
[SwitchA] interface bridge-aggregation 5
[SwitchA-Bridge-Aggregation5] link-aggregation mode dynamic
[SwitchA-Bridge-Aggregation5] quit
# Assign Ten-GigabitEthernet 1/0/2 to link aggregation group 5.
[SwitchA] interface ten-gigabitethernet 1/0/2
[SwitchA-Ten-GigabitEthernet1/0/2] port link-aggregation group 5
[SwitchA-Ten-GigabitEthernet1/0/2] quit
# Assign Bridge-Aggregation 5 to M-LAG group 5.
[SwitchA] interface bridge-aggregation 5
[SwitchA-Bridge-Aggregation5] port m-lag group 5
[SwitchA-Bridge-Aggregation5] quit
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] arp suppression enable
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 200
[SwitchA-bgp-default] peer 3.3.3.3 as-number 200
[SwitchA-bgp-default] peer 3.3.3.3 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On Bridge-Aggregation 4, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface bridge-aggregation 4
[SwitchA-Bridge-Aggregation4] service-instance 1000
[SwitchA-Bridge-Aggregation4-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Bridge-Aggregation4-srv1000] xconnect vsi vpna
[SwitchA-Bridge-Aggregation4-srv1000] quit
# On Bridge-Aggregation 5, create Ethernet service instance 1000 to match VLAN 3.
[SwitchA] interface bridge-aggregation 5
[SwitchA-Bridge-Aggregation5] service-instance 1000
[SwitchA-Bridge-Aggregation5-srv1000] encapsulation s-vid 3
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Bridge-Aggregation5-srv1000] xconnect vsi vpna
[SwitchA-Bridge-Aggregation5-srv1000] quit
# Exclude interfaces from the shutdown action by M-LAG MAD.
[SwitchA] m-lag mad exclude interface loopback 0
[SwitchA] m-lag mad exclude interface loopback 1
[SwitchA] m-lag mad exclude interface ten-gigabitethernet 1/0/4
[SwitchA] m-lag mad exclude interface ten-gigabitethernet 1/0/5
[SwitchA] m-lag mad exclude interface vlan-interface 11
[SwitchA] m-lag mad exclude interface vlan-interface 100
5. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC learning and remote ARP learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel arp-learning disable
# Choose one of the following frame match criterion creation methods for dynamic ACs:
¡ Enable the device to create frame match criteria based on VXLAN IDs for the dynamic ACs on the peer link.
[SwitchB] l2vpn m-lag peer-link ac-match-rule vxlan-mapping
¡ Use the default setting for dynamic ACs on the peer link to use frame match criteria identical to those of site-facing ACs.
# Enable EVPN M-LAG, and specify the virtual VTEP address as 1.2.3.4.
[SwitchB] evpn m-lag group 1.2.3.4
# Configure M-LAG system parameters.
[SwitchB] m-lag system-mac 0001-0001-0001
[SwitchB] m-lag system-number 2
[SwitchB] m-lag system-priority 10
[SwitchB] m-lag keepalive ip destination 60.1.1.1 source 60.1.1.2
[SwitchB] m-lag restore-delay 180
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 3.
[SwitchB] interface bridge-aggregation 3
[SwitchB-Bridge-Aggregation3] link-aggregation mode dynamic
[SwitchB-Bridge-Aggregation3] quit
# Assign Ten-GigabitEthernet 1/0/3 to aggregation group 3.
[SwitchB] interface ten-gigabitethernet 1/0/3
[SwitchB-Ten-GigabitEthernet1/0/3] port link-aggregation group 3
[SwitchB-Ten-GigabitEthernet1/0/3] quit
# Specify Bridge-Aggregation 3 as the peer-link interface.
[SwitchB] interface bridge-aggregation 3
[SwitchB-Bridge-Aggregation3] port m-lag peer-link 1
[SwitchB-Bridge-Aggregation3] quit
# Configure routing settings for Switch A and Switch B to have Layer 3 connectivity.
[SwitchB] vlan 100
[SwitchB-vlan100] quit
[SwitchB] interface Vlan-interface 100
[SwitchB-Vlan-interface100] ip address 100.1.1.2 255.255.255.0
[SwitchB-Vlan-interface100] ospf 1 area 0.0.0.0
[SwitchB-Vlan-interface100] quit
# Disable spanning tree on Ten-GigabitEthernet 1/0/5.
[SwitchB] interface ten-gigabitethernet 1/0/5
[SwitchB-Ten-GigabitEthernet1/0/5] undo stp enable
[SwitchB-Ten-GigabitEthernet1/0/5] quit
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 4.
[SwitchB] interface bridge-aggregation 4
[SwitchB-Bridge-Aggregation4] link-aggregation mode dynamic
[SwitchB-Bridge-Aggregation4] quit
# Assign Ten-GigabitEthernet 1/0/1 to aggregation group 4.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] port link-aggregation group 4
[SwitchB-Ten-GigabitEthernet1/0/1] quit
# Assign Bridge-Aggregation 4 to M-LAG group 4.
[SwitchB] interface bridge-aggregation 4
[SwitchB-Bridge-Aggregation4] port m-lag group 4
[SwitchB-Bridge-Aggregation4] quit
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 5.
[SwitchB] interface bridge-aggregation 5
[SwitchB-Bridge-Aggregation5] link-aggregation mode dynamic
[SwitchB-Bridge-Aggregation5] quit
# Assign Ten-GigabitEthernet 1/0/2 to aggregation group 5.
[SwitchB] interface ten-gigabitethernet 1/0/2
[SwitchB-Ten-GigabitEthernet1/0/2] port link-aggregation group 5
[SwitchB-Ten-GigabitEthernet1/0/2] quit
# Assign Bridge-Aggregation 5 to M-LAG group 5.
[SwitchB] interface bridge-aggregation 5
[SwitchB-Bridge-Aggregation5] port m-lag group 5
[SwitchB-Bridge-Aggregation5] quit
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] arp suppression enable
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchB] bgp 200
[SwitchB-bgp-default] peer 3.3.3.3 as-number 200
[SwitchB-bgp-default] peer 3.3.3.3 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# On Bridge-Aggregation 4, create Ethernet service instance 1000 to match VLAN 2.
[SwitchB] interface bridge-aggregation 4
[SwitchB-Bridge-Aggregation4] service-instance 1000
[SwitchB-Bridge-Aggregation4-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-Bridge-Aggregation4-srv1000] xconnect vsi vpna
[SwitchB-Bridge-Aggregation4-srv1000] quit
# On Bridge-Aggregation 5, create Ethernet service instance 1000 to match VLAN 3.
[SwitchB] interface bridge-aggregation 5
[SwitchB-Bridge-Aggregation5] service-instance 1000
[SwitchB-Bridge-Aggregation5-srv1000] encapsulation s-vid 3
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-Bridge-Aggregation5-srv1000] xconnect vsi vpna
[SwitchB-Bridge-Aggregation5-srv1000] quit
# Exclude interfaces from the shutdown action by M-LAG MAD.
[SwitchB] m-lag mad exclude interface loopback 0
[SwitchB] m-lag mad exclude interface loopback 1
[SwitchB] m-lag mad exclude interface ten-gigabitethernet 1/0/4
[SwitchB] m-lag mad exclude interface ten-gigabitethernet 1/0/5
[SwitchB] m-lag mad exclude interface vlan-interface 12
[SwitchB] m-lag mad exclude interface vlan-interface 100
6. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Disable remote MAC address learning.
[SwitchC] vxlan tunnel mac-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] evpn encapsulation vxlan
[SwitchC-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] evpn encapsulation vxlan
[SwitchC-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchC-vsi-vpnb] vxlan 20
[SwitchC-vsi-vpnb-vxlan-20] quit
[SwitchC-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes, and configure Switch C as an RR.
[SwitchC] bgp 200
[SwitchC-bgp-default] group evpn
[SwitchC-bgp-default] peer 1.1.1.1 group evpn
[SwitchC-bgp-default] peer 2.2.2.2 group evpn
[SwitchC-bgp-default] peer 4.4.4.4 group evpn
[SwitchC-bgp-default] peer evpn as-number 200
[SwitchC-bgp-default] peer evpn connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer evpn enable
[SwitchC-bgp-default-evpn] undo policy vpn-target
[SwitchC-bgp-default-evpn] peer evpn reflect-client
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Create VSI-interface 1 and assign it an IP address. The IP address is the gateway address of VXLAN 10.
[SwitchC] interface vsi-interface 1
[SwitchC-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchC-Vsi-interface1] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] gateway vsi-interface 1
[SwitchC-vsi-vpna] quit
# Create VSI-interface 2 and assign it an IP address. The IP address is the gateway address of VXLAN 20.
[SwitchC] interface vsi-interface 2
[SwitchC-Vsi-interface2] ip address 10.1.2.1 255.255.255.0
[SwitchC-Vsi-interface2] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] gateway vsi-interface 2
[SwitchC-vsi-vpnb] quit
7. Configure Switch D:
# Enable L2VPN.
<SwitchD> system-view
[SwitchD] l2vpn enable
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchD] vsi vpnb
[SwitchD-vsi-vpnb] arp suppression enable
[SwitchD-vsi-vpnb] evpn encapsulation vxlan
[SwitchD-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchD-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchD-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchD-vsi-vpnb] vxlan 20
[SwitchD-vsi-vpnb-vxlan-20] quit
[SwitchD-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchD] bgp 200
[SwitchD-bgp-default] peer 3.3.3.3 as-number 200
[SwitchD-bgp-default] peer 3.3.3.3 connect-interface loopback 0
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 4.
[SwitchD] interface ten-gigabitethernet 1/0/1
[SwitchD-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchD-Ten-GigabitEthernet1/0/1] encapsulation s-vid 4
# Map Ethernet service instance 1000 to VSI vpnb.
[SwitchD-Ten-GigabitEthernet1/0/1] xconnect vsi vpnb
[SwitchD-Ten-GigabitEthernet1/0/1] quit
Verifying the configuration
1. Verify the centralized EVPN gateway settings on Switch C:
# Verify that Switch C has advertised MAC/IP advertisement routes and IMET routes of the gateway to other devices. Verify that Switch C has received MAC/IP advertisement routes and IMET routes from Switch A, Switch B, and Switch D. (Details not shown.)
# Verify that the VXLAN tunnel to Switch A and Switch B is up, and the tunnel destination address is the virtual VTEP address.
[SwitchC] display interface tunnel
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 3.3.3.3, destination 1.2.3.4
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 4 bytes/sec, 32 bits/sec, 0 packets/sec
Input: 2 packets, 340 bytes, 0 drops
Output: 16 packets, 2793 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to the VXLANs, and that the VSI interfaces are the gateway interfaces of their respective VXLANs.
¡ For dynamic ACs whose frame match criteria are generated based on VXLAN IDs:
[SwitchA] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 1
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Statistics : Disabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
ACs:
AC Link ID State Type
BAGG3 srv1 0 Up Dynamic (M-LAG)
BAGG4 srv1000 1 Up Manual
BAGG5 srv1000 2 Up Manual
¡ For dynamic ACs whose frame match criteria are identical to those of site-facing ACs:
[SwitchC] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 1
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
VSI Name: vpnb
VSI Index : 1
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 2
VXLAN ID : 20
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel1 0x5000001 UP Auto Disabled
2. Verify the M-LAG settings on Switch A:
# Verify that Switch A has BGP EVPN routes.
[SwitchA] display bgp l2vpn evpn
BGP local router ID is 1.2.3.4
Status codes: * - valid, > - best, d - dampened, h - history,
s - suppressed, S - stale, i - internal, e - external
a - additional-path
Origin: i - IGP, e - EGP, ? - incomplete
Total number of routes from all PEs: 5
Route distinguisher: 1:100
Total number of routes: 5
* > Network : [2][0][48][0800-2700-400e][0][0.0.0.0]/104
NextHop : 1.2.3.4 LocPrf : 100
PrefVal : 32768 OutLabel : NULL
MED : 0
Path/Ogn: i
* >i Network : [2][0][48][46b2-aea0-0101][0][0.0.0.0]/104
NextHop : 3.3.3.3 LocPrf : 100
PrefVal : 0 OutLabel : NULL
MED : 0
Path/Ogn: i
* > Network : [2][0][48][ac1e-24e3-0201][0][0.0.0.0]/104
NextHop : 3.3.3.3 LocPrf : 100
PrefVal : 0 OutLabel : NULL
MED : 0
Path/Ogn: i
* >i Network : [3][0][32][1.2.3.4]/80
NextHop : 1.2.3.4 LocPrf : 100
PrefVal : 32768 OutLabel : NULL
MED : 0
Path/Ogn: i
* >i Network : [3][0][32][3.3.3.3]/80
NextHop : 3.3.3.3 LocPrf : 100
PrefVal : 0 OutLabel : NULL
MED : 0
Path/Ogn: i
# Verify that the VXLAN tunnel to Switch C is up, and the tunnel source address is the virtual VTEP address.
[SwitchA] display interface tunnel
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.2.3.4, destination 3.3.3.3
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 1 bytes/sec, 8 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 33 packets, 6121 bytes, 0 drops
# Verify that ACs are automatically created on the peer link and assigned to VSIs.
¡ For dynamic ACs whose frame match criteria are generated based on VXLAN IDs:
[SwitchA] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 1
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
ACs:
AC Link ID State Type
BAGG3 srv1 0 Up Dynamic (M-LAG)
BAGG4 srv1000 1 Up Manual
BAGG5 srv1000 2 Up Manual
¡ For dynamic ACs whose frame match criteria are identical to those of site-facing ACs:
[SwitchA] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 1
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Statistics : Disabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
ACs:
AC Link ID State Type
BAGG4 srv1000 0 Up Manual
BAGG3 srv2 1 Up Dynamic (M-LAG)
BAGG5 srv1000 2 Up Manual
BAGG3 srv3 3 Up Dynamic (M-LAG)
3. Verify network connectivity for the VMs:
# Verify that VM 1, VM 2, and VM 3 can communicate when both Switch A and Switch B are operating correctly. (Details not shown.)
# Verify that VM 1, VM 2, and VM 3 can communicate when Switch A's or Switch B's links to the local site are disconnected. (Details not shown.)
Example: Configuring IPv4 EVPN M-LAG with a tunnel peer link
Network configuration
As shown in Figure 26, perform the following tasks to make sure the VMs can communicate with one another:
· Configure VXLAN 10 on Switch A, Switch B, and Switch C, and configure VXLAN 20 on Switch C and Switch D.
· Configure EVPN M-LAG on Switch A and Switch B to virtualize them into one VTEP. The switches use a tunnel peer link.
· Create a monitor link group on Switch A and Switch B. Configure the transport-facing interfaces of Switch A and Switch B as uplink interfaces for the monitor link group, and member interfaces of M-LAG interfaces as downlink interfaces.
· Configure Switch C as a centralized EVPN gateway and RR.
|
|
NOTE: This example provides configuration of IPv4 sites extended by an IPv4 underlay network. The configuration procedure does not differ between site or underlay network types. |
Procedure
1. Set the VXLAN hardware resource mode on Switch C and reboot the switch for the mode to take effect.
<SwitchC> system-view
[SwitchC] hardware-resource vxlan l3gw16k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchC] quit
<SwitchC> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
2. On VM 1 and VM 2, specify 10.1.1.1 as the gateway address. On VM 3, specify 10.1.2.1 as the gateway address. (Details not shown.)
3. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces (including loopback interfaces), as shown in Figure 26. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D) for them to reach one another. (Details not shown.)
# Execute the ospf peer hold-max-cost duration command on the interfaces used for setting up OSPF neighbor relationships. (Details not shown.)
4. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC learning and remote ARP learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel arp-learning disable
# Enable EVPN M-LAG, and specify the virtual VTEP address as 1.2.3.4.
[SwitchA] evpn m-lag group 1.2.3.4
# Specify the reserved VXLAN as VXLAN 1234.
[SwitchA] reserved vxlan 1234
# Configure M-LAG system parameters.
[SwitchA] m-lag system-mac 0001-0001-0001
[SwitchA] m-lag system-number 1
[SwitchA] m-lag system-priority 10
[SwitchA] m-lag restore-delay 180
# Create a tunnel to Switch B, and set the ToS of tunneled packets to 100.
[SwitchA] interface tunnel 1 mode vxlan
[SwitchA-Tunnel1] source 1.1.1.1
[SwitchA-Tunnel1] destination 2.2.2.2
[SwitchA-Tunnel1] tunnel tos 100
[SwitchA-Tunnel1] quit
# Exclude Tunnel 1 from the shutdown action by M-LAG MAD.
[SwitchA] m-lag mad exclude interface tunnel 1
# Specify Tunnel 1 as the peer-link interface.
[SwitchA] interface tunnel 1
[SwitchA-Tunnel1] port m-lag peer-link 1
[SwitchA-Tunnel1] quit
# Disable spanning tree on Ten-GigabitEthernet 1/0/4.
[SwitchA] interface ten-gigabitethernet 1/0/4
[SwitchA-Ten-GigabitEthernet1/0/4] undo stp enable
[SwitchA-Ten-GigabitEthernet1/0/4] quit
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 4.
[SwitchA] interface bridge-aggregation 4
[SwitchA-Bridge-Aggregation4] link-aggregation mode dynamic
[SwitchA-Bridge-Aggregation4] quit
# Assign Ten-GigabitEthernet 1/0/1 to link aggregation group 4.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] port link-aggregation group 4
[SwitchA-Ten-GigabitEthernet1/0/1] quit
# Assign Bridge-Aggregation 4 to M-LAG group 4.
[SwitchA] interface bridge-aggregation 4
[SwitchA-Bridge-Aggregation4] port m-lag group 4
[SwitchA-Bridge-Aggregation4] quit
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 5.
[SwitchA] interface bridge-aggregation 5
[SwitchA-Bridge-Aggregation5] link-aggregation mode dynamic
[SwitchA-Bridge-Aggregation5] quit
# Assign Ten-GigabitEthernet 1/0/2 to link aggregation group 5.
[SwitchA] interface ten-gigabitethernet 1/0/2
[SwitchA-Ten-GigabitEthernet1/0/2] port link-aggregation group 5
[SwitchA-Ten-GigabitEthernet1/0/2] quit
# Assign Bridge-Aggregation 5 to M-LAG group 5.
[SwitchA] interface bridge-aggregation 5
[SwitchA-Bridge-Aggregation5] port m-lag group 5
[SwitchA-Bridge-Aggregation5] quit
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] arp suppression enable
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 200
[SwitchA-bgp-default] peer 3.3.3.3 as-number 200
[SwitchA-bgp-default] peer 3.3.3.3 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On Bridge-Aggregation 4, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface bridge-aggregation 4
[SwitchA-Bridge-Aggregation4] service-instance 1000
[SwitchA-Bridge-Aggregation4-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Bridge-Aggregation4-srv1000] xconnect vsi vpna
[SwitchA-Bridge-Aggregation4-srv1000] quit
# On Bridge-Aggregation 5, create Ethernet service instance 1000 to match VLAN 3.
[SwitchA] interface bridge-aggregation 5
[SwitchA-Bridge-Aggregation5] service-instance 1000
[SwitchA-Bridge-Aggregation5-srv1000] encapsulation s-vid 3
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Bridge-Aggregation5-srv1000] xconnect vsi vpna
[SwitchA-Bridge-Aggregation5-srv1000] quit
# Create monitor link group 1 and assign uplink and downlink interfaces to it.
[SwitchA] monitor-link group 1
[SwitchA-mtlk-group1] port ten-gigabitethernet 1/0/1 downlink
[SwitchA-mtlk-group1] port ten-gigabitethernet 1/0/2 downlink
[SwitchA-mtlk-group1] port ten-gigabitethernet 1/0/4 uplink
[SwitchA-mtlk-group1] quit
# Exclude the interfaces used by EVPN from the shutdown action by M-LAG MAD, except the aggregation member ports.
[SwitchA] m-lag mad exclude interface loopback 0
[SwitchA] m-lag mad exclude interface loopback 1
[SwitchA] m-lag mad exclude interface ten-gigabitethernet 1/0/4
[SwitchA] m-lag mad exclude interface vlan-interface 11
5. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC learning and remote ARP learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel arp-learning disable
# Enable EVPN M-LAG, and specify the virtual VTEP address as 1.2.3.4.
[SwitchB] evpn m-lag group 1.2.3.4
# Specify the reserved VXLAN as VXLAN 1234.
[SwitchB] reserved vxlan 1234
# Configure M-LAG system parameters.
[SwitchB] m-lag system-mac 0001-0001-0001
[SwitchB] m-lag system-number 2
[SwitchB] m-lag system-priority 10
[SwitchB] m-lag restore-delay 180
# Create a tunnel to Switch A, and set the ToS of tunneled packets to 100.
[SwitchB] interface tunnel 1 mode vxlan
[SwitchB-Tunnel1] source 2.2.2.2
[SwitchB-Tunnel1] destination 1.1.1.1
[SwitchB-Tunnel1] tunnel tos 100
[SwitchB-Tunnel1] quit
# Exclude Tunnel 1 from the shutdown action by M-LAG MAD.
[SwitchB] m-lag mad exclude interface tunnel 1
# Specify Tunnel 1 as the peer-link interface.
[SwitchB] interface tunnel 1
[SwitchB-Tunnel1] port m-lag peer-link 1
[SwitchB-Tunnel1] quit
# Disable spanning tree on Ten-GigabitEthernet 1/0/4.
[SwitchB] interface ten-gigabitethernet 1/0/4
[SwitchB-Ten-GigabitEthernet1/0/4] undo stp enable
[SwitchB-Ten-GigabitEthernet1/0/4] quit
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 4.
[SwitchB] interface bridge-aggregation 4
[SwitchB-Bridge-Aggregation4] link-aggregation mode dynamic
[SwitchB-Bridge-Aggregation4] quit
# Assign Ten-GigabitEthernet 1/0/1 to aggregation group 4.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] port link-aggregation group 4
[SwitchB-Ten-GigabitEthernet1/0/1] quit
# Assign Bridge-Aggregation 4 to M-LAG group 4.
[SwitchB] interface bridge-aggregation 4
[SwitchB-Bridge-Aggregation4] port m-lag group 4
[SwitchB-Bridge-Aggregation4] quit
# Create Layer 2 dynamic aggregate interface Bridge-Aggregation 5.
[SwitchB] interface bridge-aggregation 5
[SwitchB-Bridge-Aggregation5] link-aggregation mode dynamic
[SwitchB-Bridge-Aggregation5] quit
# Assign Ten-GigabitEthernet 1/0/2 to aggregation group 5.
[SwitchB] interface ten-gigabitethernet 1/0/2
[SwitchB-Ten-GigabitEthernet1/0/2] port link-aggregation group 5
[SwitchB-Ten-GigabitEthernet1/0/2] quit
# Assign Bridge-Aggregation 5 to M-LAG group 5.
[SwitchB] interface bridge-aggregation 5
[SwitchB-Bridge-Aggregation5] port m-lag group 5
[SwitchB-Bridge-Aggregation5] quit
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] arp suppression enable
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchB] bgp 200
[SwitchB-bgp-default] peer 3.3.3.3 as-number 200
[SwitchB-bgp-default] peer 3.3.3.3 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# On Bridge-Aggregation 4, create Ethernet service instance 1000 to match VLAN 2.
[SwitchB] interface bridge-aggregation 4
[SwitchB-Bridge-Aggregation4] service-instance 1000
[SwitchB-Bridge-Aggregation4-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-Bridge-Aggregation4-srv1000] xconnect vsi vpna
[SwitchB-Bridge-Aggregation4-srv1000] quit
# On Bridge-Aggregation 5, create Ethernet service instance 1000 to match VLAN 3.
[SwitchB] interface bridge-aggregation 5
[SwitchB-Bridge-Aggregation5] service-instance 1000
[SwitchB-Bridge-Aggregation5-srv1000] encapsulation s-vid 3
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-Bridge-Aggregation5-srv1000] xconnect vsi vpna
[SwitchB-Bridge-Aggregation5-srv1000] quit
# Create monitor link group 1 and assign uplink and downlink interfaces to it.
[SwitchB] monitor-link group 1
[SwitchB-mtlk-group1] port ten-gigabitethernet 1/0/1 downlink
[SwitchB-mtlk-group1] port ten-gigabitethernet 1/0/2 downlink
[SwitchB-mtlk-group1] port ten-gigabitethernet 1/0/4 uplink
[SwitchB-mtlk-group1] quit
# Exclude the interfaces used by EVPN from the shutdown action by M-LAG MAD, except the aggregation member ports.
[SwitchB] m-lag mad exclude interface loopback 0
[SwitchB] m-lag mad exclude interface loopback 1
[SwitchB] m-lag mad exclude interface ten-gigabitethernet 1/0/4
[SwitchB] m-lag mad exclude interface vlan-interface 12
6. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Disable remote MAC address learning.
[SwitchC] vxlan tunnel mac-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] evpn encapsulation vxlan
[SwitchC-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] evpn encapsulation vxlan
[SwitchC-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchC-vsi-vpnb] vxlan 20
[SwitchC-vsi-vpnb-vxlan-20] quit
[SwitchC-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes, and configure Switch C as an RR.
[SwitchC] bgp 200
[SwitchC-bgp-default] group evpn
[SwitchC-bgp-default] peer 1.1.1.1 group evpn
[SwitchC-bgp-default] peer 2.2.2.2 group evpn
[SwitchC-bgp-default] peer 4.4.4.4 group evpn
[SwitchC-bgp-default] peer evpn as-number 200
[SwitchC-bgp-default] peer evpn connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer evpn enable
[SwitchC-bgp-default-evpn] undo policy vpn-target
[SwitchC-bgp-default-evpn] peer evpn reflect-client
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Create VSI-interface 1 and assign it an IP address. The IP address is the gateway address of VXLAN 10.
[SwitchC] interface vsi-interface 1
[SwitchC-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchC-Vsi-interface1] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] gateway vsi-interface 1
[SwitchC-vsi-vpna] quit
# Create VSI-interface 2 and assign it an IP address. The IP address is the gateway address of VXLAN 20.
[SwitchC] interface vsi-interface 2
[SwitchC-Vsi-interface2] ip address 10.1.2.1 255.255.255.0
[SwitchC-Vsi-interface2] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] gateway vsi-interface 2
[SwitchC-vsi-vpnb] quit
7. Configure Switch D:
# Enable L2VPN.
<SwitchD> system-view
[SwitchD] l2vpn enable
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchD] vsi vpnb
[SwitchD-vsi-vpnb] arp suppression enable
[SwitchD-vsi-vpnb] evpn encapsulation vxlan
[SwitchD-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchD-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchD-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchD-vsi-vpnb] vxlan 20
[SwitchD-vsi-vpnb-vxlan-20] quit
[SwitchD-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchD] bgp 200
[SwitchD-bgp-default] peer 3.3.3.3 as-number 200
[SwitchD-bgp-default] peer 3.3.3.3 connect-interface loopback 0
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 4.
[SwitchD] interface ten-gigabitethernet 1/0/1
[SwitchD-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchD-Ten-GigabitEthernet1/0/1] encapsulation s-vid 4
# Map Ethernet service instance 1000 to VSI vpnb.
[SwitchD-Ten-GigabitEthernet1/0/1] xconnect vsi vpnb
[SwitchD-Ten-GigabitEthernet1/0/1] quit
Verifying the configuration
1. Verify the centralized EVPN gateway settings on Switch C:
# Verify that Switch C has advertised MAC/IP advertisement routes and IMET routes of the gateway to other devices. Verify that Switch C has received MAC/IP advertisement routes and IMET routes from Switch A, Switch B, and Switch D. (Details not shown.)
# Verify that the VXLAN tunnels to Switch A and Switch B are up, and the device has established a VXLAN tunnel to Switch A and Switch B with the destination address as the virtual VTEP address.
[SwitchC] display interface tunnel
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 3.3.3.3, destination 4.4.4.4
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 2 packets, 84 bytes, 0 drops
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 3.3.3.3, destination 1.1.1.1
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 2 packets, 84 bytes, 0 drops
Tunnel2
Current state: UP
Line protocol state: UP
Description: Tunnel2 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 3.3.3.3, destination 1.2.3.4
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 1 packets, 42 bytes, 0 drops
Tunnel3
Current state: UP
Line protocol state: UP
Description: Tunnel3 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 3.3.3.3, destination 2.2.2.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 1 packets, 42 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to the VXLANs, and that the VSI interfaces are the gateway interfaces of their respective VXLANs.
[SwitchC] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 1
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel1 0x5000001 UP Auto Disabled
Tunnel2 0x5000002 UP Auto Disabled
Tunnel3 0x5000003 UP Auto Disabled
VSI Name: vpnb
VSI Index : 1
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
Gateway Interface : VSI-interface 2
VXLAN ID : 20
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
2. Verify the M-LAG settings on Switch A:
# Verify that Switch A has BGP EVPN routes.
[SwitchA] display bgp l2vpn evpn
BGP local router ID is 1.2.3.4
Status codes: * - valid, > - best, d - dampened, h - history,
s - suppressed, S - stale, i - internal, e - external
a - additional-path
Origin: i - IGP, e - EGP, ? - incomplete
Total number of routes from all PEs: 3
Route distinguisher: 1:10
Total number of routes: 5
* >i Network : [2][0][48][7e9a-48e9-0100][32][10.1.1.1]/136
NextHop : 3.3.3.3 LocPrf : 100
PrefVal : 0 OutLabel : NULL
MED : 0
Path/Ogn: i
* > Network : [3][0][32][1.1.1.1]/80
NextHop : 1.1.1.1 LocPrf : 100
PrefVal : 32768 OutLabel : NULL
MED : 0
Path/Ogn: i
* > Network : [3][0][32][1.2.3.4]/80
NextHop : 1.2.3.4 LocPrf : 100
PrefVal : 32768 OutLabel : NULL
MED : 0
Path/Ogn: i
* >i Network : [3][0][32][3.3.3.3]/80
NextHop : 3.3.3.3 LocPrf : 100
PrefVal : 0 OutLabel : NULL
MED : 0
Path/Ogn: i
* >i Network : [3][0][32][2.2.2.2]/80
NextHop : 2.2.2.2 LocPrf : 100
PrefVal : 0 OutLabel : NULL
MED : 0
Path/Ogn: i
# Verify that the VXLAN tunnel to Switch C is up, and the tunnel source address is the virtual VTEP address.
[SwitchA] display interface tunnel
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.2.3.4, destination 3.3.3.3
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.1.1.1, destination 2.2.2.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 12 bytes/sec, 96 bits/sec, 0 packets/sec
Last 300 seconds output rate: 12 bytes/sec, 96 bits/sec, 0 packets/sec
Input: 239 packets, 25558 bytes, 0 drops
Output: 1241 packets, 109811 bytes, 0 drops
# Verify that ACs are automatically created on the peer link and assigned to VSIs.
[SwitchA] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : Unlimited
Broadcast Restrain : Unlimited
Multicast Restrain : Unlimited
Unknown Unicast Restrain: Unlimited
MAC Learning : Enabled
MAC Table Limit : Unlimited
MAC Learning rate : -
Drop Unknown : Disabled
Flooding : Enabled
Statistics : Disabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
Tunnel1 0x5000001 UP Manual Disabled
ACs:
AC Link ID State Type
BAGG4 srv1000 0 Down Manual
BAGG5 srv1000 1 Down Manual
3. Verify network connectivity for the VMs:
# Verify that VM 1, VM 2, and VM 3 can communicate when both Switch A and Switch B are operating correctly. (Details not shown.)
# Verify that VM 1, VM 2, and VM 3 can communicate when Switch A's or Switch B's links to the local site are disconnected. (Details not shown.)
Example: Configuring IPv4 EVPN multihoming
|
IMPORTANT: This configuration example is not supported by the S6800 switches labeled with the following product codes: · LS-6800-2C. · LS-6800-32Q. · LS-6800-4C. |
Network configuration
As shown in Figure 27:
· Configure VXLANs as follows:
¡ Configure VXLAN 10 on Switch A, Switch B, and Switch C. Configure Switch A and Switch B as redundant VTEPs for Server 2, and configure Switch B and Switch C as redundant VTEPs for Server 3.
¡ Configure VXLAN 20 on Switch C.
· Configure Switch A, Switch B, and Switch C as distributed EVPN gateways.
· Configure Switch D as an RR to reflect BGP EVPN routes between Switch A, Switch B, and Switch C.
Procedure
1. Set the VXLAN hardware resource mode on Switch A, Switch B, and Switch C and reboot the switches for the mode to take effect. This step uses Switch A as an example.
<SwitchA> system-view
[SwitchA] hardware-resource vxlan l3gw16k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchA] quit
<SwitchA> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
2. On VM 1, VM 2, and VM 3, specify 10.1.1.1 as the gateway address. On VM 4, specify 20.1.1.1 as the gateway address. (Details not shown.)
3. Configure IP addresses and unicast routing settings:
# Assign IP addresses to the interfaces, as shown in Figure 27. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D) for them to reach one another. (Details not shown.)
4. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto router-id
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 200
[SwitchA-bgp-default] peer 4.4.4.4 as-number 200
[SwitchA-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchA-Ten-GigabitEthernet1/0/1] quit
# Assign an ESI to Ten-GigabitEthernet 1/0/2.
[SwitchA] interface ten-gigabitethernet 1/0/2
[SwitchA-Ten-GigabitEthernet1/0/2] esi 0.0.0.0.1
# On Ten-GigabitEthernet 1/0/2, create Ethernet service instance 2000 to match VLAN 2.
[SwitchA-Ten-GigabitEthernet1/0/2] service-instance 2000
[SwitchA-Ten-GigabitEthernet1/0/2-srv2000] encapsulation s-vid 2
# Map Ethernet service instance 2000 to VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/2-srv2000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/2-srv2000] quit
[SwitchA-Ten-GigabitEthernet1/0/2] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchA] ip vpn-instance l3vpna
[SwitchA-vpn-instance-l3vpna] route-distinguisher 1:1
[SwitchA-vpn-instance-l3vpna] address-family ipv4
[SwitchA-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchA-vpn-ipv4-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] address-family evpn
[SwitchA-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchA-vpn-evpn-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchA-Vsi-interface1] mac-address 1-1-1
[SwitchA-Vsi-interface1] distributed-gateway local
[SwitchA-Vsi-interface1] local-proxy-arp enable
[SwitchA-Vsi-interface1] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchA] interface vsi-interface 3
[SwitchA-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface3] l3-vni 1000
[SwitchA-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] gateway vsi-interface 1
[SwitchA-vsi-vpna] quit
5. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto router-id
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchB] bgp 200
[SwitchB-bgp-default] peer 4.4.4.4 as-number 200
[SwitchB-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# Assign an ESI to Ten-GigabitEthernet 1/0/1.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] esi 0.0.0.0.1
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 2000 to match VLAN 2.
[SwitchB-Ten-GigabitEthernet1/0/1] service-instance 2000
[SwitchB-Ten-GigabitEthernet1/0/1-srv2000] encapsulation s-vid 2
# Map Ethernet service instance 2000 to VSI vpna.
[SwitchB-Ten-GigabitEthernet1/0/1-srv2000] xconnect vsi vpna
[SwitchB-Ten-GigabitEthernet1/0/1-srv2000] quit
[SwitchB-Ten-GigabitEthernet1/0/1] quit
# Assign an ESI to Ten-GigabitEthernet 1/0/2.
[SwitchB] interface ten-gigabitethernet 1/0/2
[SwitchB-Ten-GigabitEthernet1/0/2] esi 0.0.0.0.2
# On Ten-GigabitEthernet 1/0/2, create Ethernet service instance 3000 to match VLAN 2.
[SwitchB-Ten-GigabitEthernet1/0/2] service-instance 3000
[SwitchB-Ten-GigabitEthernet1/0/2-srv3000] encapsulation s-vid 2
# Map Ethernet service instance 3000 to VSI vpna.
[SwitchB-Ten-GigabitEthernet1/0/2-srv3000] xconnect vsi vpna
[SwitchB-Ten-GigabitEthernet1/0/2-srv3000] quit
[SwitchB-Ten-GigabitEthernet1/0/2] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchB] ip vpn-instance l3vpna
[SwitchB-vpn-instance-l3vpna] route-distinguisher 2:2
[SwitchB-vpn-instance-l3vpna] address-family ipv4
[SwitchB-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchB-vpn-ipv4-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] address-family evpn
[SwitchB-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchB-vpn-evpn-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchB] interface vsi-interface 1
[SwitchB-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchB-Vsi-interface1] mac-address 1-1-1
[SwitchB-Vsi-interface1] distributed-gateway local
[SwitchB-Vsi-interface1] local-proxy-arp enable
[SwitchB-Vsi-interface1] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchB] interface vsi-interface 3
[SwitchB-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface3] l3-vni 1000
[SwitchB-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] gateway vsi-interface 1
[SwitchB-vsi-vpna] quit
6. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchC] vxlan tunnel mac-learning disable
[SwitchC] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] evpn encapsulation vxlan
[SwitchC-vsi-vpna-evpn-vxlan] route-distinguisher auto router-id
[SwitchC-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Create an EVPN instance on VSI vpnb, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] evpn encapsulation vxlan
[SwitchC-vsi-vpnb-evpn-vxlan] route-distinguisher auto router-id
[SwitchC-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20.
[SwitchC-vsi-vpnb] vxlan 20
[SwitchC-vsi-vpnb-vxlan-20] quit
[SwitchC-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchC] bgp 200
[SwitchC-bgp-default] peer 4.4.4.4 as-number 200
[SwitchC-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Assign an ESI to Ten-GigabitEthernet 1/0/1.
[SwitchC] interface ten-gigabitethernet 1/0/1
[SwitchC-Ten-GigabitEthernet1/0/1] esi 0.0.0.0.2
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 3000 to match VLAN 2.
[SwitchC-Ten-GigabitEthernet1/0/1] service-instance 3000
[SwitchC-Ten-GigabitEthernet1/0/1-srv3000] encapsulation s-vid 2
# Map Ethernet service instance 3000 to VSI vpna.
[SwitchC-Ten-GigabitEthernet1/0/1-srv3000] xconnect vsi vpna
[SwitchC-Ten-GigabitEthernet1/0/1-srv3000] quit
[SwitchC-Ten-GigabitEthernet1/0/1] quit
# On Ten-GigabitEthernet 1/0/2, create Ethernet service instance 4000 to match VLAN 3.
[SwitchC] interface ten-gigabitethernet 1/0/2
[SwitchC-Ten-GigabitEthernet1/0/2] service-instance 4000
[SwitchC-Ten-GigabitEthernet1/0/2-srv4000] encapsulation s-vid 3
# Map Ethernet service instance 4000 to VSI vpnb.
[SwitchC-Ten-GigabitEthernet1/0/2-srv4000] xconnect vsi vpnb
[SwitchC-Ten-GigabitEthernet1/0/2-srv4000] quit
[SwitchC-Ten-GigabitEthernet1/0/2] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchC] ip vpn-instance l3vpna
[SwitchC-vpn-instance-l3vpna] route-distinguisher 3:3
[SwitchC-vpn-instance-l3vpna] address-family ipv4
[SwitchC-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchC-vpn-ipv4-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] address-family evpn
[SwitchC-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchC-vpn-evpn-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchC] interface vsi-interface 1
[SwitchC-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchC-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchC-Vsi-interface1] mac-address 1-1-1
[SwitchC-Vsi-interface1] distributed-gateway local
[SwitchC-Vsi-interface1] local-proxy-arp enable
[SwitchC-Vsi-interface1] quit
# Configure VSI-interface 2.
[SwitchC] interface vsi-interface 2
[SwitchC-Vsi-interface2] ip binding vpn-instance l3vpna
[SwitchC-Vsi-interface2] ip address 20.1.1.1 255.255.255.0
[SwitchC-Vsi-interface2] mac-address 2-2-2
[SwitchC-Vsi-interface2] distributed-gateway local
[SwitchC-Vsi-interface2] local-proxy-arp enable
[SwitchC-Vsi-interface2] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchC] interface vsi-interface 3
[SwitchC-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchC-Vsi-interface3] l3-vni 1000
[SwitchC-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] gateway vsi-interface 1
[SwitchC-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] gateway vsi-interface 2
[SwitchC-vsi-vpnb] quit
7. Configure Switch D:
# Establish BGP connections with other transport network switches.
<SwitchD> system-view
[SwitchD] bgp 200
[SwitchD-bgp-default] group evpn
[SwitchD-bgp-default] peer 1.1.1.1 group evpn
[SwitchD-bgp-default] peer 2.2.2.2 group evpn
[SwitchD-bgp-default] peer 3.3.3.3 group evpn
[SwitchD-bgp-default] peer evpn as-number 200
[SwitchD-bgp-default] peer evpn connect-interface loopback 0
# Configure BGP to advertise BGP EVPN routes, and disable route target filtering for BGP EVPN routes.
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer evpn enable
[SwitchD-bgp-default-evpn] undo policy vpn-target
# Configure Switch D as an RR.
[SwitchD-bgp-default-evpn] peer evpn reflect-client
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
Verifying the configuration
1. Verify the EVPN multihoming configuration on Switch C.
# Verify that Switch C has advertised and received the following BGP EVPN routes (details not shown):
¡ IP prefix advertisement routes for the gateways.
¡ IMET routes for VSIs.
¡ MAC/IP advertisement routes.
¡ Ethernet auto-discovery routes and Ethernet segment routes.
# Verify that Switch C has ECMP routes to VM 2.
<SwitchC> display evpn routing-table vpn-instance l3vpna
Flags: E - with valid ESI A - AD ready L - Local ES exists
VPN instance:l3vpna Local L3VNI:1000
IP address Next hop Outgoing interface NibID Flags
10.1.1.10 1.1.1.1 Vsi-interface3 0x18000001 -
10.1.1.20 2.2.2.2 Vsi-interface3 0x18000000 EA
1.1.1.1 Vsi-interface3 0x18000001 EA
# Verify that Switch C has equal-cost L2VPN MAC address entries for VM 2.
<SwitchC> display l2vpn mac-address
* - The output interface is issued to another VSI
MAC Address State VSI Name Link ID/Name Aging
0001-0001-0010 EVPN vpna Tunnel0 NotAging
0001-0001-0020 EVPN vpna Tunnel0 NotAging
Tunnel1 NotAging
0001-0001-0030 Dynamic vpna XGE1/0/1 Aging
0002-0001-0010 Dynamic vpnb XGE1/0/2 Aging
--- 4 mac address(es) found ---
# Verify that Switch C has EVPN MAC address entries for VM 2.
<SwitchC> display evpn route mac
Flags: D - Dynamic B - BGP L - Local active
G - Gateway S - Static M - Mapping I - Invalid
A - MAC-authentication P – Multiport/Multicast
VSI name: vpna
EVPN instance: -
MAC address Link ID/Name Flags Encap Next hop
0001-0001-0030 0 DL VXLAN -
0001-0001-0010 Tunnel0 B VXLAN 1.1.1.1
0001-0001-0020 Tunnel0 B VXLAN 1.1.1.1
Tunnel1 B VXLAN 2.2.2.2
VSI name: vpnb
EVPN instance: -
MAC address Link ID/Name Flags Encap Next hop
0002-0001-0010 0 DL VXLAN -
# Verify that Switch C has information about local and remote ESs.
<SwitchC> display evpn es local
Redundancy mode: A - All active, S - Single active
VSI name : vpna
EVPN instance: -
ESI Tag ID DF address Mode State ESI label
0000.0000.0000.0000.0002 - 2.2.2.2 A Up -
<SwitchC> display evpn es remote
Control Flags: P – Primary, B – Backup, C - Control word
VSI name : vpna
EVPN instance: -
ESI : 0000.0000.0000.0000.0001
A-D per ES routes :
Peer IP Remote Redundancy mode
1.1.1.1 All active
2.2.2.2 All active
A-D per EVI routes :
Tag ID Peer IP
- 1.1.1.1
- 2.2.2.2
ESI : 0000.0000.0000.0000.0002
Ethernet segment routes :
2.2.2.2
A-D per ES routes :
Peer IP Remote Redundancy mode
2.2.2.2 All active
A-D per EVI routes :
Tag ID Peer IP
- 2.2.2.2
2. Verify that the VMs can communicate with one another. (Details not shown.)
Example: Configuring EVPN multicast
|
IMPORTANT: This configuration example is not supported by the S6800 switches labeled with the following product codes: · LS-6800-2C. · LS-6800-32Q. · LS-6800-4C. |
Network configuration
As shown in Figure 28:
· Enable multicast on Switch A, Switch B, and Switch C.
· Configure VXLAN 10 on Switch A, Switch B, and Switch C. Configure Switch A and Switch B as redundant VTEPs for Server 2, and configure Switch B and Switch C as redundant VTEPs for Server 3.
· Configure Switch A, Switch B, and Switch C as distributed EVPN gateways.
· Configure Switch D as an RR to reflect BGP EVPN routes between Switch A, Switch B, and Switch C.
Procedure
1. Set the VXLAN hardware resource mode on Switch A, Switch B, and Switch C and reboot the switches for the mode to take effect. This step uses Switch A as an example.
<SwitchA> system-view
[SwitchA] hardware-resource vxlan l3gw16k
Do you want to change the specified hardware resource working mode? [Y/N]:y
The hardware resource working mode is changed, please save the configuration and
reboot the system to make it effective.
[SwitchA] quit
<SwitchA> reboot
Start to check configuration with next startup configuration file, please wait..
.......DONE!
Current configuration may be lost after the reboot, save current configuration?
[Y/N]:y
This command will reboot the device. Continue? [Y/N]:y
2. On VM 1, VM 2, and VM 3, specify 10.1.1.1 as the gateway address. (Details not shown.)
3. Configure IP addresses and unicast routing settings:
# Assign IP addresses to the interfaces, as shown in Figure 28. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D) for them to reach one another. (Details not shown.)
4. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto router-id
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 200
[SwitchA-bgp-default] peer 4.4.4.4 as-number 200
[SwitchA-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchA-Ten-GigabitEthernet1/0/1] quit
# Assign an ESI to Ten-GigabitEthernet 1/0/2.
[SwitchA] interface ten-gigabitethernet 1/0/2
[SwitchA-Ten-GigabitEthernet1/0/2] esi 0.0.0.0.1
# On Ten-GigabitEthernet 1/0/2, create Ethernet service instance 2000 to match VLAN 2.
[SwitchA-Ten-GigabitEthernet1/0/2] service-instance 2000
[SwitchA-Ten-GigabitEthernet1/0/2-srv2000] encapsulation s-vid 2
# Map Ethernet service instance 2000 to VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/2-srv2000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/2-srv2000] quit
[SwitchA-Ten-GigabitEthernet1/0/2] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchA] ip vpn-instance l3vpna
[SwitchA-vpn-instance-l3vpna] route-distinguisher 1:1
[SwitchA-vpn-instance-l3vpna] address-family ipv4
[SwitchA-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchA-vpn-ipv4-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] address-family evpn
[SwitchA-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchA-vpn-evpn-l3vpna] quit
[SwitchA-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchA-Vsi-interface1] mac-address 1-1-1
[SwitchA-Vsi-interface1] distributed-gateway local
[SwitchA-Vsi-interface1] local-proxy-arp enable
[SwitchA-Vsi-interface1] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchA] interface vsi-interface 3
[SwitchA-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchA-Vsi-interface3] l3-vni 1000
[SwitchA-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] gateway vsi-interface 1
[SwitchA-vsi-vpna] quit
# Enable IGMP snooping globally.
[SwitchA] igmp-snooping
[SwitchA-igmp-snooping] quit
# Enable IGMP snooping, IGMP snooping proxying, and dropping unknown multicast data on VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] igmp-snooping enable
[SwitchA-vsi-vpna] igmp-snooping proxy enable
[SwitchA-vsi-vpna] igmp-snooping drop-unknown
# Set the IGMP snooping version and enable the IGMP snooping querier on VSI vpna.
[SwitchA-vsi-vpna] igmp-snooping version 3
[SwitchA-vsi-vpna] igmp-snooping querier
[SwitchA-vsi-vpna] quit
5. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto router-id
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchB-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchB] bgp 200
[SwitchB-bgp-default] peer 4.4.4.4 as-number 200
[SwitchB-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# Assign an ESI to Ten-GigabitEthernet 1/0/1.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] esi 0.0.0.0.1
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 2000 to match VLAN 2.
[SwitchB-Ten-GigabitEthernet1/0/1] service-instance 2000
[SwitchB-Ten-GigabitEthernet1/0/1-srv2000] encapsulation s-vid 2
# Map Ethernet service instance 2000 to VSI vpna.
[SwitchB-Ten-GigabitEthernet1/0/1-srv2000] xconnect vsi vpna
[SwitchB-Ten-GigabitEthernet1/0/1-srv2000] quit
[SwitchB-Ten-GigabitEthernet1/0/1] quit
# Assign an ESI to Ten-GigabitEthernet 1/0/2.
[SwitchB] interface ten-gigabitethernet 1/0/2
[SwitchB-Ten-GigabitEthernet1/0/2] esi 0.0.0.0.2
# On Ten-GigabitEthernet 1/0/2, create Ethernet service instance 3000 to match VLAN 2.
[SwitchB-Ten-GigabitEthernet1/0/2] service-instance 3000
[SwitchB-Ten-GigabitEthernet1/0/2-srv3000] encapsulation s-vid 2
# Map Ethernet service instance 3000 to VSI vpna.
[SwitchB-Ten-GigabitEthernet1/0/2-srv3000] xconnect vsi vpna
[SwitchB-Ten-GigabitEthernet1/0/2-srv3000] quit
[SwitchB-Ten-GigabitEthernet1/0/2] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchB] ip vpn-instance l3vpna
[SwitchB-vpn-instance-l3vpna] route-distinguisher 2:2
[SwitchB-vpn-instance-l3vpna] address-family ipv4
[SwitchB-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchB-vpn-ipv4-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] address-family evpn
[SwitchB-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchB-vpn-evpn-l3vpna] quit
[SwitchB-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchB] interface vsi-interface 1
[SwitchB-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchB-Vsi-interface1] mac-address 1-1-1
[SwitchB-Vsi-interface1] distributed-gateway local
[SwitchB-Vsi-interface1] local-proxy-arp enable
[SwitchB-Vsi-interface1] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchB] interface vsi-interface 3
[SwitchB-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchB-Vsi-interface3] l3-vni 1000
[SwitchB-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] gateway vsi-interface 1
[SwitchB-vsi-vpna] quit
# Enable IGMP snooping globally.
[SwitchB] igmp-snooping
[SwitchB-igmp-snooping] quit
# Enable IGMP snooping, IGMP snooping proxying, and dropping unknown multicast data on VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] igmp-snooping enable
[SwitchB-vsi-vpna] igmp-snooping proxy enable
[SwitchB-vsi-vpna] igmp-snooping drop-unknown
# Set the IGMP snooping version and enable the IGMP snooping querier on VSI vpna.
[SwitchB-vsi-vpna] igmp-snooping version 3
[SwitchB-vsi-vpna] igmp-snooping querier
[SwitchB-vsi-vpna] quit
6. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchC] vxlan tunnel mac-learning disable
[SwitchC] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpna, and configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] evpn encapsulation vxlan
[SwitchC-vsi-vpna-evpn-vxlan] route-distinguisher auto router-id
[SwitchC-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchC-vsi-vpna-evpn-vxlan] quit
# Create VXLAN 10.
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchC] bgp 200
[SwitchC-bgp-default] peer 4.4.4.4 as-number 200
[SwitchC-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Assign an ESI to Ten-GigabitEthernet 1/0/1.
[SwitchC] interface ten-gigabitethernet 1/0/1
[SwitchC-Ten-GigabitEthernet1/0/1] esi 0.0.0.0.2
# On Ten-GigabitEthernet 1/0/1, create Ethernet service instance 3000 to match VLAN 2.
[SwitchC-Ten-GigabitEthernet1/0/1] service-instance 3000
[SwitchC-Ten-GigabitEthernet1/0/1-srv3000] encapsulation s-vid 2
# Map Ethernet service instance 3000 to VSI vpna.
[SwitchC-Ten-GigabitEthernet1/0/1-srv3000] xconnect vsi vpna
[SwitchC-Ten-GigabitEthernet1/0/1-srv3000] quit
[SwitchC-Ten-GigabitEthernet1/0/1] quit
# Configure RD and route target settings for VPN instance l3vpna.
[SwitchC] ip vpn-instance l3vpna
[SwitchC-vpn-instance-l3vpna] route-distinguisher 3:3
[SwitchC-vpn-instance-l3vpna] address-family ipv4
[SwitchC-vpn-ipv4-l3vpna] vpn-target 2:2
[SwitchC-vpn-ipv4-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] address-family evpn
[SwitchC-vpn-evpn-l3vpna] vpn-target 1:1
[SwitchC-vpn-evpn-l3vpna] quit
[SwitchC-vpn-instance-l3vpna] quit
# Configure VSI-interface 1.
[SwitchC] interface vsi-interface 1
[SwitchC-Vsi-interface1] ip binding vpn-instance l3vpna
[SwitchC-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchC-Vsi-interface1] mac-address 1-1-1
[SwitchC-Vsi-interface1] distributed-gateway local
[SwitchC-Vsi-interface1] local-proxy-arp enable
[SwitchC-Vsi-interface1] quit
# Associate VSI-interface 3 with VPN instance l3vpna, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchC] interface vsi-interface 3
[SwitchC-Vsi-interface3] ip binding vpn-instance l3vpna
[SwitchC-Vsi-interface3] l3-vni 1000
[SwitchC-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] gateway vsi-interface 1
[SwitchC-vsi-vpna] quit
# Enable IGMP snooping globally.
[SwitchC] igmp-snooping
[SwitchC-igmp-snooping] quit
# Enable IGMP snooping, IGMP snooping proxying, and dropping unknown multicast data on VSI vpna.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] igmp-snooping enable
[SwitchC-vsi-vpna] igmp-snooping proxy enable
[SwitchC-vsi-vpna] igmp-snooping drop-unknown
# Set the IGMP snooping version and enable the IGMP snooping querier on VSI vpna.
[SwitchC-vsi-vpna] igmp-snooping version 3
[SwitchC-vsi-vpna] igmp-snooping querier
[SwitchC-vsi-vpna] quit
7. Configure Switch D:
# Establish BGP connections with other transport network switches.
<SwitchD> system-view
[SwitchD] bgp 200
[SwitchD-bgp-default] group evpn
[SwitchD-bgp-default] peer 1.1.1.1 group evpn
[SwitchD-bgp-default] peer 2.2.2.2 group evpn
[SwitchD-bgp-default] peer 3.3.3.3 group evpn
[SwitchD-bgp-default] peer evpn as-number 200
[SwitchD-bgp-default] peer evpn connect-interface loopback 0
# Configure BGP to advertise BGP EVPN routes, and disable route target filtering for BGP EVPN routes.
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer evpn enable
[SwitchD-bgp-default-evpn] undo policy vpn-target
# Configure Switch D as an RR.
[SwitchD-bgp-default-evpn] peer evpn reflect-client
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
Verifying the configuration
1. On Server 1, send an IGMP membership report to multicast group address 225.0.0.1.
2. Verify that Switch B has received the SMET route advertised by Switch A and created a multicast forwarding entry.
<SwitchB> display evpn route smet
VSI name: vpna
Source address : 0.0.0.0
Group address : 225.0.0.1
Local version : -
Peers :
Nexthop Tunnel name Link ID Remote version
1.1.1.1 Tunnel0 0x5000000 v3(E)
<SwitchB> display igmp-snooping evpn-group
Total 1 entries.
VSI vpna: Total 1 entries.
(0.0.0.0, 225.0.0.1)
Host ports (1 in total):
Tun0 (VXLAN ID 10)
3. Verify that Switch B has received the IGMP join synch route advertised by Switch A.
<SwitchB> display evpn route igmp-js
VSI name: vpna
Source address : 0.0.0.0
Group address : 225.0.0.1
Local version : -
Remote version : v3(E)
ESI : 0000.0000.0000.0000.0001
Ethernet tag ID : 2
Interface : XGE1/0/1 srv2000
Peers : 1.1.1.1