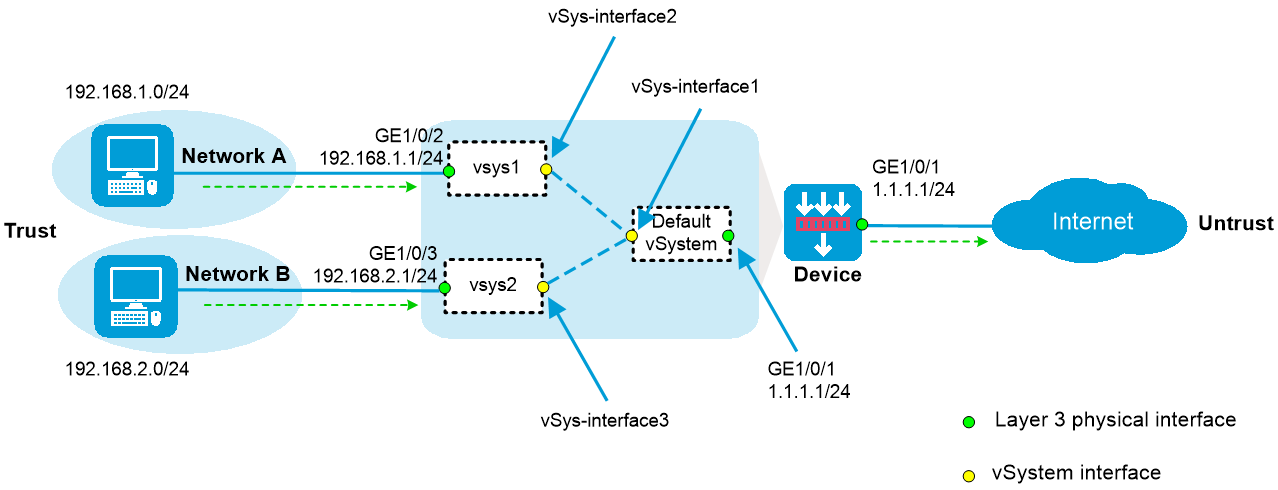
As shown in Figure 1:
The device acts as a security gateway.
The internal network is divided into Network A for the R&D department and Network B for non-R&D departments. Users in Network A and Network B are isolated.
In Network A, only users in subnet 192.168.1.128/25 can access the Internet. In Network B, all users can access the Internet.
This configuration example was created and verified on F9900 of the F5000-AI120 device.
1. Create vSystems and assign interfaces to the vSystems:
# Create vSystem vsys1 and configure a description for the vSystem.
<Device> system-view
[Device] vsys vsys1
[Device-vsys-2-vsys1] description vsys-1
# Assign interface GigabitEthernet 1/0/2 to vSystem vsys1.
[Device-vsys-2-vsys1] allocate interface gigabitethernet 1/0/2
Some configurations on the interface are removed.
[Device-vsys-2-vsys1] quit
# Create vSystem vsys2 and configure a description for the vSystem.
[Device] vsys vsys2
[Device-vsys-3-vsys2] description vsys-2
# Assign interface GigabitEthernet 1/0/3 to vSystem vsys2.
[Device-vsys-3-vsys2] allocate interface gigabitethernet 1/0/3
Some configurations on the interface are removed.
[Device-vsys-3-vsys2] quit
2. Assign IP addresses to interfaces and add interfaces to security zones:
# Assign IP addresses to interfaces.
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] ip address 1.1.1.1 24
[Device-GigabitEthernet1/0/1] quit
# Add interfaces to security zones.
[Device] security-zone name trust
[Device-security-zone-Trust] import interface vsys-interface 1
[Device-security-zone-Trust] quit
[Device] security-zone name untrust
[Device-security-zone-Untrust] import interface gigabitethernet 1/0/1
[Device-security-zone-Untrust] quit
3. Configure settings for routing. This example configures a static route. In the route, the next hop IP address is 1.1.1.2 for internal users to access the Internet through the default vSystem.
[Device] ip route-static 0.0.0.0 0 1.1.1.2
4. Configure a rule named trust-untrust in the IPv4 security policy to allow internal users to access the Internet.
[Device] security-policy ip
[Device-security-policy-ip] rule name trust-untrust
[Device-security-policy-ip-1-trust-untrust] source-zone trust
[Device-security-policy-ip-1-trust-untrust] destination-zone untrust
[Device-security-policy-ip-1-trust-untrust] source-ip-subnet 192.168.1.128 25
[Device-security-policy-ip-1-trust-untrust] source-ip-subnet 192.168.2.0 24
[Device-security-policy-ip-1-trust-untrust] action pass
[Device-security-policy-ip-1-trust-untrust] quit
[Device-security-policy-ip] quit
5. Configure NAT:
# Configure ACL 2000, and create a rule to permit the packets only from 192.168.1.128/25 and 192.168.2.0/24 to be translated.
[Device] acl basic 2000
[Device-acl-ipv4-basic-2000] rule permit source 192.168.1.128 0.0.0.127
[Device-acl-ipv4-basic-2000] rule permit source 192.168.2.0 0.0.0.255
[Device-acl-ipv4-basic-2000] quit
# Enable outbound dynamic NAT with Easy IP on interface GigabitEthernet 1/0/1 so that NAT translates the source addresses of the packets matching the ACL and destined for the Internet into the IP address of interface GigabitEthernet 1/0/1.
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] nat outbound 2000
[Device-GigabitEthernet1/0/1] quit
1. Log in to vSystem vsys1, assign IP addresses to interfaces, and add interfaces to security zones:
# Log in to vSystem vsys1.
[Device] switchto vsys vsys1
<Device-vsys1> system-view
# Assign IP addresses to interfaces.
[Device-vsys1] interface gigabitethernet 1/0/1
[Device-vsys1-GigabitEthernet1/0/1] ip address 192.168.1.1 24
[Device-vsys1-GigabitEthernet1/0/1] quit
# Add interfaces to security zones.
[Device-vsys1] security-zone name trust
[Device-vsys1-security-zone-Trust] import interface gigabitethernet 1/0/2
[Device-vsys1-security-zone-Trust] quit
[Device-vsys1] security-zone name untrust
[Device-vsys1-security-zone-Untrust] import interface vsys-interface 2
[Device-vsys1-security-zone-Untrust] quit
2. Configure settings for routing. This example configures a static route. In the route, the next hop is the default vSystem for users in vSystem vsys1 to access the Internet.
[Device-vsys1] ip route-static 0.0.0.0 0 public
3. Configure a rule named trust-untrust in the IPv4 security policy to allow users in subnet 192.168.1.128/25 to access the Internet.
[Device-vsys1] security-policy ip
[Device-vsys1-security-policy-ip] rule name trust-untrust
[Device-vsys1-security-policy-ip-1-trust-untrust] source-zone trust
[Device-vsys1-security-policy-ip-1-trust-untrust] destination-zone untrust
[Device-vsys1-security-policy-ip-1-trust-untrust] source-ip-subnet 192.168.1.128 25
[Device-vsys1-security-policy-ip-1-trust-untrust] action pass
4. Return to the default vSystem from vSystem vsys1.
[Device-vsys1-security-policy-ip-1-trust-untrust] return
<Device-vsys1> quit
[Device]
1. Log in to vSystem vsys2, assign IP addresses to interfaces, and add interfaces to security zones:
# Log in to vSystem vsys2.
[Device] switchto vsys vsys2
<Device-vsys2> system-view
# Assign IP addresses to interfaces.
[Device-vsys2] interface gigabitethernet 1/0/3
[Device-vsys2-GigabitEthernet1/0/3] ip address 192.168.2.1 24
[Device-vsys2-GigabitEthernet1/0/3] quit
# Add interfaces to security zones.
[Device-vsys2] security-zone name trust
[Device-vsys2-security-zone-Trust] import interface gigabitethernet 1/0/3
[Device-vsys2-security-zone-Trust] quit
[Device-vsys2] security-zone name untrust
[Device-vsys2-security-zone-Untrust] import interface vsys-interface 3
[Device-vsys2-security-zone-Untrust] quit
2. Configure settings for routing. This example configures a static route. In the route, the next hop is the default vSystem for users in vSystem vsys2 to access the Internet.
[Device-vsys2] ip route-static 0.0.0.0 0 public
3. Configure a rule named trust-untrust in the IPv4 security policy to allow users in subnet 192.168.2.0/24 to access the Internet.
[Device-vsys2] security-policy ip
[Device-vsys2-security-policy-ip] rule name trust-untrust
[Device-vsys2-security-policy-ip-1-trust-untrust] source-zone trust
[Device-vsys2-security-policy-ip-1-trust-untrust] destination-zone untrust
[Device-vsys2-security-policy-ip-1-trust-untrust] source-ip-subnet 192.168.2.0 24
[Device-vsys2-security-policy-ip-1-trust-untrust] action pass
4. Return to the default vSystem from vSystem vsys2.
[Device-vsys2-security-policy-ip-1-trust-untrust] return
<Device-vsys2> quit
[Device]
# Verify that the vSystems are running correctly on the device. The device has three active vSystems.
[Device] display vsys
ID Name Status Description
1 Admin Active Default
2 vsys1 Active vsys-1
3 vsys2 Active vsys-2
# Verify that users in subnet 192.168.1.128/25 can access the Internet.
C:\> ping 3.3.3.3
Pinging 3.3.3.3 with 32 bytes of data:
Reply from 3.3.3.3: bytes=32 time=51ms TTL=255
Reply from 3.3.3.3: bytes=32 time=44ms TTL=255
Reply from 3.3.3.3: bytes=32 time=1ms TTL=255
Reply from 3.3.3.3: bytes=32 time=1ms TTL=255
Ping statistics for 3.3.3.3:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 1ms, Maximum = 51ms, Average = 24ms
# Verify that users in subnet 192.168.2.0/24 can access the Internet.
C:\> ping 3.3.3.3
Pinging 3.3.3.3 with 32 bytes of data:
Reply from 3.3.3.3: bytes=32 time=25ms TTL=255
Reply from 3.3.3.3: bytes=32 time=36ms TTL=255
Reply from 3.3.3.3: bytes=32 time=1ms TTL=255
Reply from 3.3.3.3: bytes=32 time=1ms TTL=255
Ping statistics for 3.3.3.3:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 1ms, Maximum = 36ms, Average = 16ms
#
vsys vsys1 id 2
description vsys-1
allocate interface GigabitEthernet1/0/2
#
vsys vsys2 id 3
description vsys-2
allocate interface GigabitEthernet1/0/3
#
interface GigabitEthernet1/0/1
ip address 1.1.1.1 255.255.255.0
nat outbound 2000
#
interface GigabitEthernet1/0/2
ip address 192.168.1.1 255.255.255.0
#
interface GigabitEthernet1/0/3
ip address 192.168.2.1 255.255.255.0
#
security-zone name Trust
import interface vSys-interface1
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
ip route-static 0.0.0.0 0 1.1.1.2
#
acl basic 2000
rule 0 permit source 192.168.1.128 0.0.0.127
rule 5 permit source 192.168.2.0 0.0.0.255
#
security-policy ip
rule 0 name trust-untrust
action pass
source-zone trust
destination-zone untrust
source-ip-subnet 192.168.1.128 255.255.255.128
source-ip-subnet 192.168.2.0 255.255.255.0
#
switchto vsys vsys1
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface vSys-interface2
#
ip route-static 0.0.0.0 0 public
#
security-policy ip
rule 0 name trust-untrust
action pass
source-zone trust
destination-zone untrust
source-ip-subnet 192.168.1.128 255.255.255.128
#
switchto vsys vsys2
#
security-zone name Trust
import interface GigabitEthernet1/0/3
#
security-zone name Untrust
import interface vSys-interface3
#
ip route-static 0.0.0.0 0 public
#
security-policy ip
rule 0 name trust-untrust
action pass