CLI example: Configuring NAT Server for external-to-internal access through domain name (overlapping addresses)
Network configuration
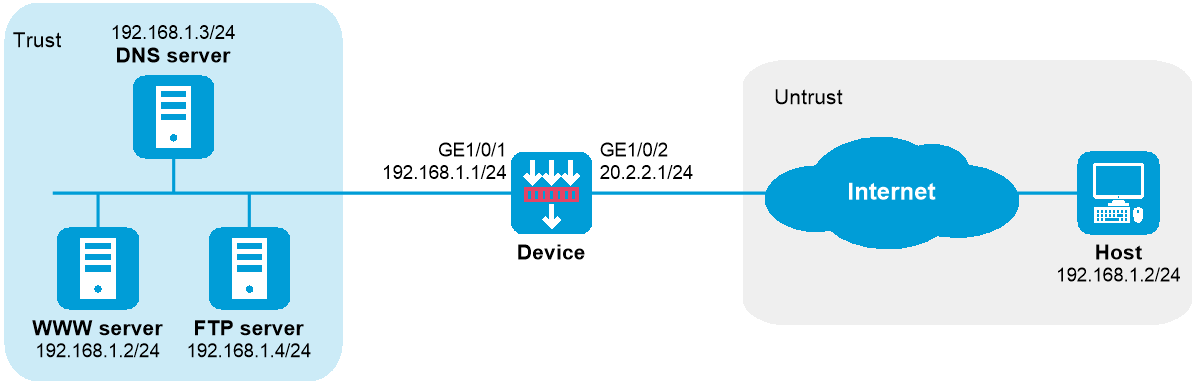
As shown in Figure-1, an intranet uses the subnet 192.168.1.0/24. The Web server at 192.168.1.2/24 provides Web services for external users and the DNS server at 192.168.1.3/24 resolves the domain name of the Web server. The company has three public addresses 202.38.1.2, 202.38.1.3, and 202.38.1.4.
Configure NAT to allow external host at 192.168.1.2 in the external network to use the domain name to access the internal Web server.
Requirements analysis
To meet the network requirements, you must perform the following tasks:
Configure a NAT server mapping to map the private IP address and port of the DNS server to a public IP address and port. NAT Server allows the external host to access the internal DNS server for domain name resolution.
Configure outbound dynamic NAT and enable NAT ALG for DNS. The Web server's IP address is the same as the external host's IP address. NAT ALG can translate the Web server's private address in the payload of the DNS response packet to a dynamically assigned public address.
Configure inbound dynamic NAT. The external host's IP address is the same as the Web server's IP address. Inbound dynamic NAT can translate the external host's IP address into a dynamically assigned public address.
Add a static route to the public IP address of the external host with GigabitEthernet 1/0/2 as the output interface.
Software versions used
This configuration example was created and verified on R9900P2705 of the F5000-AI-55-G device.
Procedures
# Assign IP addresses to interfaces and configure routes, security zones, zone pairs, and interzone policies. Make sure the network connections are available. (Details not shown.)
# Enable NAT ALG for DNS.
<Device> system-view
[Device] nat alg dns
# Configure ACL 2000 to identify packets from subnet 192.168.1.0/24.
[Device] acl basic 2000
[Device-acl-ipv4-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Device-acl-ipv4-basic-2000] quit
# Create address group 1.
[Device] nat address-group 1
# Add address 202.38.1.2 to the address group.
[Device-address-group-1] address 202.38.1.2 202.38.1.2
[Device-address-group-1] quit
# Create address group 2.
[Device] nat address-group 2
# Add address 202.38.1.3 to the address group.
[Device-address-group-2] address 202.38.1.3 202.38.1.3
[Device-address-group-2] quit
# Configure a NAT server mapping on GigabitEthernet 1/0/2 to allow external hosts to access the internal DNS server by using the address 202.38.1.4.
[Device] interface gigabitethernet 1/0/2
[Device-GigabitEthernet1/0/2] nat server protocol udp global 202.38.1.4 inside 192.168.1.3 dns
# Enable outbound NO-PAT on GigabitEthernet 1/0/2 to translate IP address of the Web server in the DNS response payload into the address in address group 1, and allow reversible NAT.
[Device-GigabitEthernet1/0/2] nat outbound 2000 address-group 1 no-pat reversible
# Enable inbound PAT on interface GigabitEthernet 1/0/2 to translate the source address of packets going to the internal network to the address in address group 2.
[Device-GigabitEthernet1/0/2] nat inbound 2000 address-group 2
# Configure a static route to 202.38.1.3 with GigabitEthernet 1/0/2 as the output interface and 20.2.2.2 as the next hop. (The next hop address varies by network.)
[Device] ip route-static 202.38.1.3 32 gigabitethernet 1/0/2 20.2.2.2
Verifying the configuration
# Verify that the host on the external network can use the domain name to access the internal Web server whose address is the same as the host. (Details not shown.)
# Display all NAT configuration and statistics.
[Device] display nat all
NAT address group information:
Totally 2 NAT address groups.
Address group ID: 1
Port range: 1-65535
Address information:
Start address End address
202.38.1.2 202.38.1.2
Exclude address information:
Start address End address
--- ---
Address group ID: 2
Port range: 1-65535
Address information:
Start address End address
202.38.1.3 202.38.1.3
Exclude address information:
Start address End address
--- ---
NAT inbound information:
Totally 1 NAT inbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: 2
Add route: N NO-PAT: N Reversible: N
Config status: Active
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: 1
Port-preserved: N
Config status: Active
NAT internal server information:
Totally 1 internal servers.
Interface: GigabitEthernet1/0/2
Protocol: 17(UDP)
Global IP/port: 202.38.1.4/53
Local IP/port : 200.1.1.3/53
Rule name : ServerRule_1
NAT counting : 0
Config status : Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Disabled
ICMP-ERROR : Enabled
ILS : Disabled
MGCP : Disabled
NBT : Disabled
PPTP : Enabled
RTSP : Enabled
RSH : Disabled
SCCP : Disabled
SCTP : Disabled
SIP : Disabled
SQLNET : Disabled
TFTP : Disabled
XDMCP : Disabled
Static NAT load balancing: Disabled
NAT link-switch recreate-session: Disabled
NAT configuration-for-new-connection: Disabled
# Display NAT sessions that are generated when Host accesses the Web server.
[Device] display nat session verbose
Slot 1:
Initiator:
Source IP/port: 192.168.1.2/1694
Destination IP/port: 202.38.1.2/8080
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Source security zone: Untrust
Responder:
Source IP/port: 192.168.1.2/8080
Destination IP/port: 202.38.1.3/1025
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
Source security zone: Trust
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: -/-/-
Rule name:
Start time: 2017-06-15 14:53:29 TTL: 3597s
Initiator->Responder: 7 packets 308 bytes
Responder->Initiator: 5 packets 312 bytes
Total sessions found: 1
Configuration files
#
nat address-group 1
address 202.38.1.2 202.38.1.2
#
nat address-group 2
address 202.38.1.3 202.38.1.3
#
interface GigabitEthernet1/0/1
ip address 192.168.1.1 255.255.255.0
#
interface GigabitEthernet1/0/2
ip address 20.2.2.1 255.255.255.0
nat inbound 2000 address-group 2
nat outbound 2000 address-group 1 no-pat reversible
nat server protocol udp global 202.38.1.4 53 inside 192.168.1.3 53
#
security-zone name Trust
import interface GigabitEthernet1/0/1
#
security-zone name Untrust
import interface GigabitEthernet1/0/2
#
ip route-static 202.38.1.3 32 GigabitEthernet1/0/2 20.2.2.2
#
acl basic 2000
rule 0 permit source 192.168.1.0 0.0.0.255
#
security-policy ip
rule 0 name trust-untrust
action pass
source-zone trust
destination-zone untrust
rule 1 name untrust-trust
action pass
source-zone untrust
destination-zone trust
#