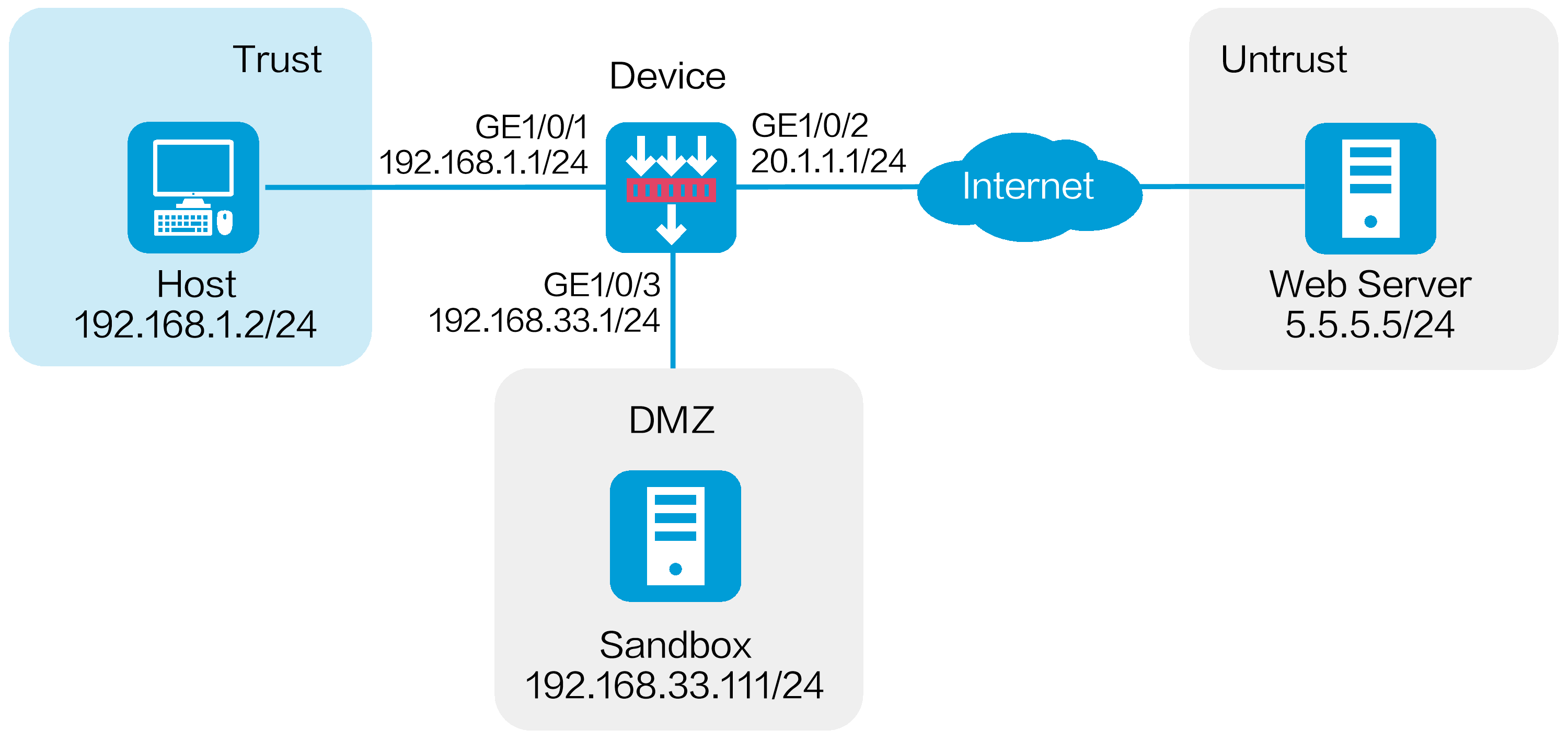
As shown in Figure 1, a security gateway device is deployed at the border of the enterprise network. A sandbox is deployed in the enterprise network. The sandbox and device are reachable to each other. Configure the collaboration between the device and the sandbox to protect the internal users against APT attacks.
This configuration example was created and verified on E9671 of the M9000-X06 device.
To block the APT attacks detected by the APT defense feature, you must configure the anti-virus feature. When the subsequent malicious traffic passes through the device, the device can identify the application layer protocol of the malicious traffic and take actions specified in the anti-virus profile on the malicious traffic.
Assign IP addresses to interfaces and add the interfaces to security zones:
# On the top navigation bar, click Network.
# From the navigation pane, select Interface Configuration > Interfaces.
# Click the Edit icon for GE 1/0/1.
# In the dialog box that opens, configure the interface:
Select the Trust security zone.
Click the IPv4 Address tab, and then enter the IP address and mask length of the interface. In this example, use 192.168.1.1/24.
Use the default settings for other parameters.
Click OK.
# Add GE 1/0/2 to the Untrust security zone and set its IP address to 20.1.1.1/24 in the same way you configure GE 1/0/1.
# Add GE 1/0/3 to the DMZ security zone and set its IP address to 192.168.33.1/24 in the same way you configure GE 1/0/1.
Configure settings for routing:
This example configures a static route. If dynamic routes are used, configure a routing protocol.
# On the top navigation bar, click Network.
# From the navigation pane, select Routing > Static Routing.
# On the IPv4 Static Routing tab, click Create.
# In the dialog box that opens, create an IPv4 static route:
Enter destination address 5.5.5.0.
Enter mask length 24.
Enter next hop address 20.1.1.2.
Use the default settings for other parameters.
# Click OK.
Configure the collaboration between the device and the sandbox:
# On the top navigation bar, click Objects.
# From the navigation pane, select APP Security > APT Defense > Sandbox.
Enable sandbox collaboration.
Enter sandbox address 192.168.33.111.
Enter username admin.
Enter password 123456abc.
Use the default settings for other parameters
Click Apply.
Figure 2 Configuring the sandbox
Configure an APT defense profile.
# On the top navigation bar, click Objects.
# From the navigation pane, select APP Security > APT Defense > Profile.
# Click Create.
# In the dialog box that opens, configure APT defense profile apt1 and then click OK.
Figure 3 Creating an APT defense profile
Configure an anti-virus profile. (Details not shown.)
To block packets, use the APT defense feature in collaboration with the anti-virus feature. When you configure an anti-virus profile, set the action to Block for specific protocols as needed.
This example uses the default anti-virus profile default.
Configure security policies:
# On the top navigation bar, click Policies.
# From the navigation pane, select Security Policies > Security Policies.
# Click Create, and then click Create a policy.
# In the dialog box that opens, configure a security policy:
Enter policy name untrust-trust.
Select source zone Untrust.
Select destination zone Trust.
Select type IPv4.
Select action Permit.
Select destination IP address 192.168.1.0/24.
Select APT defense profile apt1 in the Content security area.
Select anti-virus profile default in the Content security area. This document uses the default anti-virus profile as an example.
# Click OK.
# Create security policy trust-untrust in the same way you create security policy untrust-trust:
Enter policy name trust-untrust.
Select source zone Trust.
Select destination zone Untrust.
Select type IPv4.
Select action Permit.
Select source IP address 192.168.1.0/24.
Select APT defense profile apt1 in the Content security area.
Select anti-virus profile default in the Content security area. This document uses the default anti-virus profile as an example.
# Click OK.
# Create security policy local-dmz in the same way you create security policy untrust-trust:
Enter policy name local-dmz.
Select source zone Local.
Select destination zone DMZ.
Select type IPv4.
Select action Permit.
Select source IP address 192.168.1.0/24.
# Click OK.
# Create security policy dmz-local in the same way you create security policy untrust-trust:
Enter policy name dmz-local.
Select source zone DMZ.
Select destination zone Local.
Select type IPv4.
Select action Permit.
Select destination IP address 192.168.1.0/24.
# Click OK.
Activate the security policy configuration:
# On the Security Policies > Security Policies page, click Submit to make the anti-virus profile take effect.
# Click Activate to immediately activate acceleration for the security policies.
Enable the log collection feature:
# On the top navigation bar, click System.
# From the navigation pane, select Log Settings > Basic Settings.
# Click the Storage Space Settings tab.
# Select the check box next to sandbox-log | log to enable log collection for sandbox logs.
Verify that the device can collaborate with the sandbox and anti-virus feature to protect the internal users against APT attacks. To view sandbox logs, click Monitor on the top navigation bar, and then select Security Logs > Sandbox Logs from the navigation pane.