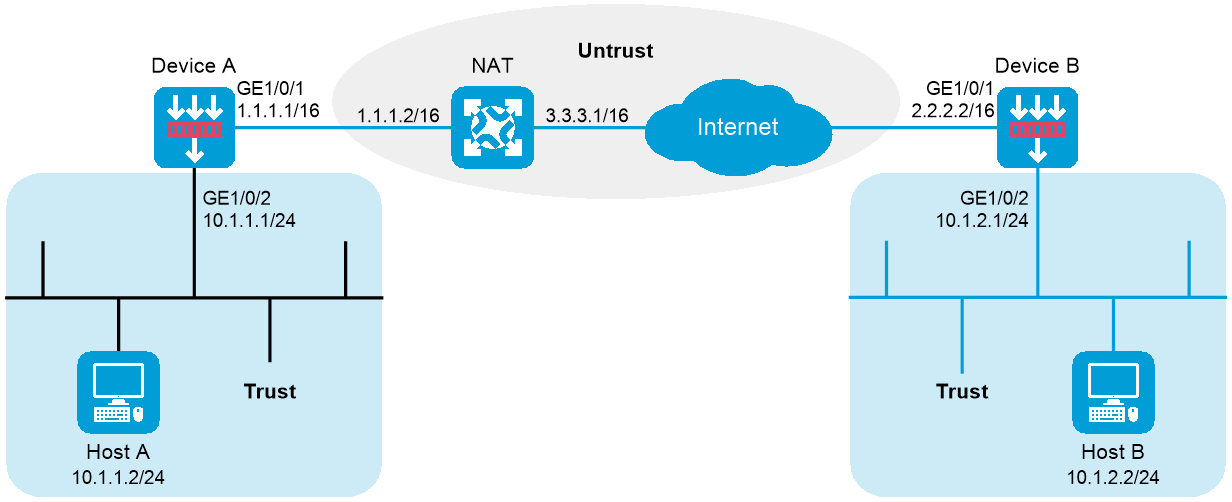
Device A is behind the NAT device. Hosts behind Device A use public IP address 3.3.3.1 to access the external network.
Configure an IKE-based IPsec tunnel between Device A and Device B to secure the communication between subnet 10.1.1.0/24 and subnet 10.1.2.0/24.
Configure Device A and Device B to use the default IKE proposal for the aggressive IKE negotiation to set up the IPsec SAs.
Configure the two devices to use the preshared key authentication method for the IKE negotiation phase 1.
Figure 1 Network diagram
This configuration example was created and verified on E8371 of the F5000-AI160 device.
1. Assign IP addresses to interfaces:
# Assign an IP address to interface GigabitEthernet 1/0/1.
<DeviceA> system-view
[DeviceA] interface gigabitethernet 1/0/1
[DeviceA-GigabitEthernet1/0/1] ip address 1.1.1.1 255.255.0.0
[DeviceA-GigabitEthernet1/0/1] quit
# Assign IP addresses to other interfaces in the same way. (Details not shown.)
2. Configure settings for routing.
This example configures static routes, and the next hop in the routes is 1.1.1.2.
[DeviceA] ip route-static 10.1.2.0 24 1.1.1.2
[DeviceA] ip route-static 2.2.2.2 16 1.1.1.2
3. Add interfaces to security zones.
[DeviceA] security-zone name trust
[DeviceA-security-zone-Trust] import interface gigabitethernet 1/0/2
[DeviceA-security-zone-Trust] quit
[DeviceA] security-zone name untrust
[DeviceA-security-zone-Untrust] import interface gigabitethernet 1/0/1
[DeviceA-security-zone-Untrust] quit
4. Configure a security policy:
Configure rules to permit traffic between the Untrust and Local security zones, so the devices can set up an IPsec tunnel:
# Configure a rule named ipseclocalout to allow Device A to send IPsec negotiation packets to Device B.
[DeviceA] security-policy ip
[DeviceA-security-policy-ip] rule name ipseclocalout
[DeviceA-security-policy-ip-1-ipseclocalout] source-zone local
[DeviceA-security-policy-ip-1-ipseclocalout] destination-zone untrust
[DeviceA-security-policy-ip-1-ipseclocalout] source-ip-host 1.1.1.1
[DeviceA-security-policy-ip-1-ipseclocalout] destination-ip-host 2.2.2.2
[DeviceA-security-policy-ip-1-ipseclocalout] action pass
[DeviceA-security-policy-ip-1-ipseclocalout] quit
# Configure a rule named ipseclocalin to allow Device A to receive the IPsec negotiation packets sent from Device B.
[DeviceA-security-policy-ip] rule name ipseclocalin
[DeviceA-security-policy-ip-2-ipseclocalin] source-zone untrust
[DeviceA-security-policy-ip-2-ipseclocalin] destination-zone local
[DeviceA-security-policy-ip-2-ipseclocalin] source-ip-host 2.2.2.2
[DeviceA-security-policy-ip-2-ipseclocalin] destination-ip-host 1.1.1.1
[DeviceA-security-policy-ip-2-ipseclocalin] action pass
[DeviceA-security-policy-ip-2-ipseclocalin] quit
Configure rules to permit the traffic between Host A and Host B:
# Configure a rule named trust-untrust to permit the packets from Host A to Host B.
[DeviceA-security-policy-ip] rule name trust-untrust
[DeviceA-security-policy-ip-3-trust-untrust] source-zone trust
[DeviceA-security-policy-ip-3-trust-untrust] destination-zone untrust
[DeviceA-security-policy-ip-3-trust-untrust] source-ip-subnet 10.1.1.0 24
[DeviceA-security-policy-ip-3-trust-untrust] destination-ip-subnet 10.1.2.0 24
[DeviceA-security-policy-ip-3-trust-untrust] action pass
[DeviceA-security-policy-ip-3-trust-untrust] quit
# Configure a rule named untrust-trust to permit the packets from Host B to Host A.
[DeviceA-security-policy-ip] rule name untrust-trust
[DeviceA-security-policy-ip-4-untrust-trust] source-zone untrust
[DeviceA-security-policy-ip-4-untrust-trust] destination-zone trust
[DeviceA-security-policy-ip-4-untrust-trust] source-ip-subnet 10.1.2.0 24
[DeviceA-security-policy-ip-4-untrust-trust] destination-ip-subnet 10.1.1.0 24
[DeviceA-security-policy-ip-4-untrust-trust] action pass
[DeviceA-security-policy-ip-4-untrust-trust] quit
[DeviceA-security-policy-ip] quit
5. Define the data flows to be protected:
# Configure IPv4 advanced ACL 3000 to identify traffic from subnet 10.1.1.0/24 to subnet 10.1.2.0/24.
[DeviceA] acl advanced 3000
[DeviceA-acl-ipv4-adv-3000] rule 0 permit ip source 10.1.1.0 0.0.0.255 destination 10.1.2.0 0.0.0.255
[DeviceA-acl-ipv4-adv-3000] quit
6. Configure an IPsec transform set to specify the packet encapsulation mode, security protocols, and algorithms.
The IPsec transform set settings at both sides of the IPsec tunnel must be the same.
[DeviceA] ipsec transform-set transform1
[DeviceA-ipsec-transform-set-transform1] protocol esp
[DeviceA-ipsec-transform-set-transform1] esp encryption-algorithm 3des-cbc
[DeviceA-ipsec-transform-set-transform1] esp authentication-algorithm md5
[DeviceA-ipsec-transform-set-transform1] quit
7. Configure an IKE keychain to specify the key information used for IKE communication.
The preshared key used by both sides of the communication must be the same.
[DeviceA] ike keychain keychain1
[DeviceA-ike-keychain-keychain1] pre-shared-key address 2.2.2.2 255.255.0.0 key simple 12345zxcvb!@#$%ZXCVB
[DeviceA-ike-keychain-keychain1] quit
8. Configure an IKE profile to specify the security parameters used for setting up IKE SAs.
[DeviceA] ike profile profile1
[DeviceA-ike-profile-profile1] keychain keychain1
[DeviceA-ike-profile-profile1] exchange-mode aggressive
[DeviceA-ike-profile-profile1] local-identity fqdn www.devicea.com
[DeviceA-ike-profile-profile1] match remote identity address 2.2.2.2 255.255.0.0
[DeviceA-ike-profile-profile1] quit
9. Configure an IPsec policy to establish an IPsec tunnel to protect the specified data.
[DeviceA] ipsec policy policy1 1 isakmp
[DeviceA-ipsec-policy-isakmp-policy1-1] remote-address 2.2.2.2
[DeviceA-ipsec-policy-isakmp-policy1-1] transform-set transform1
[DeviceA-ipsec-policy-isakmp-policy1-1] security acl 3000
[DeviceA-ipsec-policy-isakmp-policy1-1] ike-profile profile1
[DeviceA-ipsec-policy-isakmp-policy1-1] quit
10. Apply the IPsec policy to GigabitEthernet 1/0/1 to protect the traffic on the interface.
[DeviceA] interface gigabitethernet 1/0/1
[DeviceA-GigabitEthernet1/0/1] ipsec apply policy policy1
[DeviceA-GigabitEthernet1/0/1] quit
1. Assign IP addresses to interfaces:
# Assign an IP address to interface GigabitEthernet 1/0/1.
<DeviceB> system-view
[DeviceB] interface gigabitethernet 1/0/1
[DeviceB-GigabitEthernet1/0/1] ip address 2.2.2.2 255.255.0.0
[DeviceB-GigabitEthernet1/0/1] quit
# Assign IP addresses to other interfaces in the same way. (Details not shown.)
2. Configure settings for routing.
This example configures static routes, and the next hop in the routes is 2.2.2.1.
[DeviceB] ip route-static 10.1.1.0 24 2.2.2.1
[DeviceB] ip route-static 1.1.1.1 16 2.2.2.1
3. Add interfaces to security zones.
[DeviceB] security-zone name trust
[DeviceB-security-zone-Trust] import interface gigabitethernet 1/0/2
[DeviceB-security-zone-Trust] quit
[DeviceB] security-zone name untrust
[DeviceB-security-zone-Untrust] import interface gigabitethernet 1/0/1
[DeviceB-security-zone-Untrust] quit
4. Configure a security policy:
Configure rules to permit traffic between the Untrust and Local security zones, so the devices can set up an IPsec tunnel:
# Configure a rule named ipseclocalout to allow Device B to send IPsec negotiation packets to Device A.
[DeviceB] security-policy ip
[DeviceB-security-policy-ip] rule name ipseclocalout
[DeviceB-security-policy-ip-1-ipseclocalout] source-zone local
[DeviceB-security-policy-ip-1-ipseclocalout] destination-zone untrust
[DeviceB-security-policy-ip-1-ipseclocalout] source-ip-host 2.2.2.2
[DeviceB-security-policy-ip-1-ipseclocalout] destination-ip-host 3.3.3.1
[DeviceB-security-policy-ip-1-ipseclocalout] action pass
[DeviceB-security-policy-ip-1-ipseclocalout] quit
# Configure a rule named ipseclocalin to allow Device B to receive the IPsec negotiation packets sent from Device A.
[DeviceB-security-policy-ip] rule name ipseclocalin
[DeviceB-security-policy-ip-2-ipseclocalin] source-zone untrust
[DeviceB-security-policy-ip-2-ipseclocalin] destination-zone local
[DeviceB-security-policy-ip-2-ipseclocalin] source-ip-host 3.3.3.1
[DeviceB-security-policy-ip-2-ipseclocalin] destination-ip-host 2.2.2.2
[DeviceB-security-policy-ip-2-ipseclocalin] action pass
[DeviceB-security-policy-ip-2-ipseclocalin] quit
Configure rules to permit traffic between Host B and Host A:
# Configure a rule named trust-untrust to permit the packets from Host B to Host A.
[DeviceB-security-policy-ip] rule name trust-untrust
[DeviceB-security-policy-ip-3-trust-untrust] source-zone trust
[DeviceB-security-policy-ip-3-trust-untrust] destination-zone untrust
[DeviceB-security-policy-ip-3-trust-untrust] source-ip-subnet 10.1.2.0 24
[DeviceB-security-policy-ip-3-trust-untrust] destination-ip-subnet 10.1.1.0 24
[DeviceB-security-policy-ip-3-trust-untrust] action pass
[DeviceB-security-policy-ip-3-trust-untrust] quit
# Configure a rule named untrust-trust to permit the packets from Host A to Host B.
[DeviceB-security-policy-ip] rule name untrust-trust
[DeviceB-security-policy-ip-4-untrust-trust] source-zone untrust
[DeviceB-security-policy-ip-4-untrust-trust] destination-zone trust
[DeviceB-security-policy-ip-4-untrust-trust] source-ip-subnet 10.1.1.0 24
[DeviceB-security-policy-ip-4-untrust-trust] destination-ip-subnet 10.1.2.0 24
[DeviceB-security-policy-ip-4-untrust-trust] action pass
[DeviceB-security-policy-ip-4-untrust-trust] quit
[DeviceB-security-policy-ip] quit
5. Configure an IPsec transform set to specify the packet encapsulation mode, security protocols, and algorithms.
[DeviceB] ipsec transform-set transform1
[DeviceB-ipsec-transform-set-transform1] protocol esp
[DeviceB-ipsec-transform-set-transform1] esp encryption-algorithm 3des-cbc
[DeviceB-ipsec-transform-set-transform1] esp authentication-algorithm md5
[DeviceB-ipsec-transform-set-transform1] quit
6. Configure an IKE keychain to specify the key information used for IKE communication.
This example specifies 12345zxcvb!@#$%ZXCVB in plain text as the preshared key to be used with the remote peer at 1.1.1.1. The source address of packets from 1.1.1.1 is translated into 3.3.3.1 by the NAT device, so IP address of the remote peer is specified as 3.3.3.1.
[DeviceB]ike keychain keychain1
[DeviceB-ike-keychain-keychain1] pre-shared-key address 3.3.3.1 255.255.0.0 key simple 12345zxcvb!@#$%ZXCVB
[DeviceB-ike-keychain-keychain1] quit
7. Configure an IKE profile to specify the security parameters used for setting up IKE SAs.
[DeviceB] ike profile profile1
[DeviceB-ike-profile-profile1] keychain keychain1
[DeviceB-ike-profile-profile1] exchange-mode aggressive
[DeviceB-ike-profile-profile1] match remote identity fqdn www.devicea.com
[DeviceB-ike-profile-profile1] quit
8. Configure an IPsec policy template, which is used to create an IPsec policy.
[DeviceB] ipsec policy-template template1 1
[DeviceB-ipsec-policy-template-template1-1] transform-set transform1
[DeviceB-ipsec-policy-template-template1-1] local-address 2.2.2.2
[DeviceB-ipsec-policy-template-template1-1] ike-profile profile1
[DeviceB-ipsec-policy-template-template1-1] quit
9. Create an IKE-based IPsec policy entry by using IPsec policy template template1, so as to establish an IPsec tunnel to protect the specified data.
[DeviceB] ipsec policy policy1 1 isakmp template template1
10. Apply the IPsec policy to GigabitEthernet 1/0/1 to protect the traffic on the interface.
[DeviceB] interface gigabitethernet 1/0/1
[DeviceB-GigabitEthernet1/0/1] ipsec apply policy policy1
[DeviceB-GigabitEthernet1/0/1] quit
# Initiate a connection from subnet 10.1.1.0/24 to subnet 10.1.2.0/24 to trigger IKE negotiation. After IPsec SAs are successfully negotiated by IKE, traffic between the two subnets is IPsec-protected.
# Display the IKE SA on Device A.
[DeviceA] display ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
13 2.2.2.2/500 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
[DeviceA] display ike sa verbose
-----------------------------------------------
Connection ID: 13
Outside VPN:
Inside VPN:
Profile: profile1
Transmitting entity: Initiator
Initiator cookie: 1bcf453f0a217259
Responder cookie: 5e32a74dfa66a0a4
-----------------------------------------------
Local IP/port: 1.1.1.1/500
Local ID type: FQDN
Local ID: www.devicea.com
Remote IP/port: 2.2.2.2/500
Remote ID type: IPV4_ADDR
Remote ID: 2.2.2.2
Authentication-method: PRE-SHARED-KEY
Authentication-algorithm: SHA1
Encryption-algorithm: DES-CBC
Life duration(sec): 86400
Remaining key duration(sec): 84565
Exchange-mode: Aggressive
Diffie-Hellman group: Group 1
NAT traversal: Detected
Extend authentication: Disabled
Assigned IP address:
Vendor ID index: 0xa1d
Vendor ID sequence number: 0x0
# Display the IPsec SAs generated on Device A.
[DeviceA] display ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/1
-------------------------------
-----------------------------
IPsec policy: policy1
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Transmitting entity: Initiator
Path MTU: 1435
Tunnel:
local address/port: 1.1.1.1/500
remote address/port: 2.2.2.2/500
Flow:
sour addr: 10.1.1.0/255.255.255.0 port: 0 protocol: ip
dest addr: 10.1.2.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 830667426 (0x3182faa2)
Connection ID: 90194313219
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/2313
Max received sequence-number:
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: Y
Status: Active
[Outbound ESP SAs]
SPI: 3516214669 (0xd1952d8d)
Connection ID: 64424509441
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/2313
Max sent sequence-number:
UDP encapsulation used for NAT traversal: Y
Status: Active
Device A
#
interface GigabitEthernet1/0/1
ip address 1.1.1.1 255.255.0.0
ipsec apply policy policy1
#
interface GigabitEthernet1/0/2
ip address 10.1.1.1 255.255.255.0
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
ip route-static 2.2.0.0 16 1.1.1.2
ip route-static 10.1.2.0 24 1.1.1.2
#
acl advanced 3000
rule 0 permit ip source 10.1.1.0 0.0.0.255 destination 10.1.2.0 0.0.0.255
#
ipsec transform-set transform1
encapsulation-mode tunnel
protocol esp
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy policy1 1 isakmp
transform-set transform1
security acl 3000
remote-address 2.2.2.2
ike-profile profile1
#
ike profile profile1
keychain keychain1
exchange-mode aggressive
local-identity fqdn www.devicea.com
match remote identity address 2.2.2.2 255.255.0.0
#
ike keychain keychain1
pre-shared-key address 2.2.2.2 255.255.0.0 key simple 12345zxcvb!@#$%ZXCVB
#
security-policy ip
rule 0 name ipseclocalout
action pass
source-zone local
destination-zone untrust
source-ip-host 1.1.1.1
destination-ip-host 2.2.2.2
rule 1 name ipseclocalin
action pass
source-zone untrust
destination-zone local
source-ip-host 2.2.2.2
destination-ip-host 1.1.1.1
rule 2 name trust-untrust
action pass
source-zone trust
destination-zone untrust
source-ip-subnet 10.1.1.0 255.255.255.0
destination-ip-subnet 10.1.2.0 255.255.255.0
rule 3 name untrust-trust
action pass
source-zone untrust
destination-zone trust
source-ip-subnet 10.1.2.0 255.255.255.0
destination-ip-subnet 10.1.1.0 255.255.255.0
#
Device B
#
interface GigabitEthernet1/0/1
ip address 2.2.2.2 255.255.0.0
ipsec apply policy policy1
#
interface GigabitEthernet1/0/2
ip address 10.1.2.1 255.255.255.0
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
ip route-static 1.1.0.0 16 2.2.2.1
ip route-static 10.1.1.0 24 2.2.2.1
#
ipsec transform-set transform1
encapsulation-mode tunnel
protocol esp
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy-template template1 1
transform-set transform1
local-address 2.2.2.2
ike-profile profile1
#
ipsec policy policy1 1 isakmp template template1
#
ike profile profile1
keychain keychain1
exchange-mode aggressive
match remote identity fqdn www.devicea.com
#
ike keychain keychain1
pre-shared-key address 3.3.3.1 255.255.0.0 key simple 12345zxcvb!@#$%ZXCVB
#
security-policy ip
rule 0 name ipseclocalout
action pass
source-zone local
destination-zone untrust
source-ip-host 2.2.2.2
destination-ip-host 3.3.3.1
rule 1 name ipseclocalin
action pass
source-zone untrust
destination-zone local
source-ip-host 3.3.3.1
destination-ip-host 2.2.2.2
rule 2 name trust-untrust
action pass
source-zone trust
destination-zone untrust
source-ip-subnet 10.1.2.0 255.255.255.0
destination-ip-subnet 10.1.1.0 255.255.255.0
rule 3 name untrust-trust
action pass
source-zone untrust
destination-zone trust
source-ip-subnet 10.1.1.0 255.255.255.0
destination-ip-subnet 10.1.2.0 255.255.255.0