CLI方式:基于路由建立保护IPv4报文的IPsec隧道典型配置(预共享密钥认证方式)
使用版本
本举例是在T5030的R9900版本版本上进行配置和验证的。
组网需求
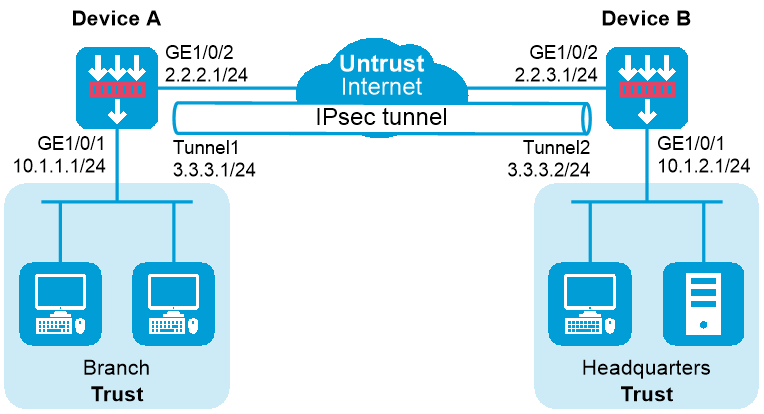
如下图所示,某企业分支和总部均使用固定的IP地址接入Internet。现有如下组网要求:
企业分支与企业总部之间的所有流量通过IPsec安全隧道进行传送;
当企业分支的私网IP地址段调整时,不需要改变企业总部网关的IPsec配置。
为实现如上组网需求,可采用如下配置思路实现:
在Device A和Device B之间使用IPsec隧道接口建立IPsec连接,将发送给对端私网的数据流路由到IPsec虚拟隧道接口上,由IPsec虚拟隧道接口上动态协商建立的IPsec安全隧道对分支子网(10.1.1.0/24)与总部子网(10.1.2.0/24)之间的所有数据流进行安全保护。
图-1 基于IPsec隧道建立保护IPv4报文的IPsec隧道配置组网图
配置步骤
配置Device A
配置接口IP地址
# 根据组网图中规划的信息,配置各接口的IP地址,具体配置步骤如下。
<DeviceA> system-view
[DeviceA] interface gigabitethernet 1/0/1
[DeviceA-GigabitEthernet1/0/1] ip address 10.1.1.1 255.255.255.0
[DeviceA-GigabitEthernet1/0/1] quit
请参考以上步骤配置其他接口的IP地址,具体配置步骤略。
配置IPsec隧道接口
[DeviceA] interface tunnel 1 mode ipsec
[DeviceA-Tunnel1] ip address 3.3.3.1 255.255.255.0
[DeviceA-Tunnel1] source 2.2.2.1
[DeviceA-Tunnel1] destination 2.2.3.1
[DeviceA-Tunnel1] quit
配置静态路由
本举例仅以静态路由方式配置路由信息。实际组网中,请根据具体情况选择相应的路由配置方式。
# 请根据组网图中规划的信息,配置静态路由,本举例假设下一跳IP地址为2.2.2.2,实际使用中请以具体组网情况为准,具体配置步骤如下。
[DeviceA] ip route-static 10.1.2.0 24 2.2.2.2
[DeviceA] ip route-static 2.2.3.1 24 2.2.2.2
# 请根据组网图中规划的信息,配置静态路由,将需要保护的流量引入IPsec隧道接口,本举例的IPsec隧道接口为Tunnel1,具体配置步骤如下。
[DeviceA] ip route-static 10.1.2.0 255.255.255.0 tunnel 1
配置接口加入安全域。
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[DeviceA] security-zone name trust
[DeviceA-security-zone-Trust] import interface gigabitethernet 1/0/1
[DeviceA-security-zone-Trust] quit
[DeviceA] security-zone name untrust
[DeviceA-security-zone-Untrust] import interface gigabitethernet 1/0/2
[DeviceA-security-zone-Untrust] import interface tunnel 1
[DeviceA-security-zone-Untrust] quit
配置安全策略
配置安全策略放行Untrust与Local安全域之间的流量,用于设备之间可以建立IPsec隧道。
# 配置名称为ipseclocalout的安全策规则,使Device A可以向Device B发送IPsec隧道协商报文,具体配置步骤如下。
[DeviceA] security-policy ip
[DeviceA-security-policy-ip] rule name ipseclocalout
[DeviceA-security-policy-ip-1-ipseclocalout] source-zone local
[DeviceA-security-policy-ip-1-ipseclocalout] destination-zone untrust
[DeviceA-security-policy-ip-1-ipseclocalout] source-ip-host 2.2.2.1
[DeviceA-security-policy-ip-1-ipseclocalout] destination-ip-host 2.2.3.1
[DeviceA-security-policy-ip-1-ipseclocalout] action pass
[DeviceA-security-policy-ip-1-ipseclocalout] quit
# 配置名称为ipseclocalin的安全策略规则,使Device A可以接收和处理来自Device B的IPsec隧道协商报文,具体配置步骤如下。
[DeviceA-security-policy-ip] rule name ipseclocalin
[DeviceA-security-policy-ip-2-ipseclocalin] source-zone untrust
[DeviceA-security-policy-ip-2-ipseclocalin] destination-zone local
[DeviceA-security-policy-ip-2-ipseclocalin] source-ip-host 2.2.3.1
[DeviceA-security-policy-ip-2-ipseclocalin] destination-ip-host 2.2.2.1
[DeviceA-security-policy-ip-2-ipseclocalin] action pass
[DeviceA-security-policy-ip-2-ipseclocalin] quit
配置安全策略放行Host A与Host B之间的流量
# 配置名称为trust-untrust的安全策略规则,使Host A访问Host B的报文可通,具体配置步骤如下。
[DeviceA-security-policy-ip] rule name trust-untrust
[DeviceA-security-policy-ip-3-trust-untrust] source-zone trust
[DeviceA-security-policy-ip-3-trust-untrust] destination-zone untrust
[DeviceA-security-policy-ip-3-trust-untrust] source-ip-subnet 10.1.1.0 24
[DeviceA-security-policy-ip-3-trust-untrust] destination-ip-subnet 10.1.2.0 24
[DeviceA-security-policy-ip-3-trust-untrust] action pass
[DeviceA-security-policy-ip-3-trust-untrust] quit
# 配置名称为untrust-trust的安全策略规则,使Host B访问Host A的报文可通,具体配置步骤如下。
[DeviceA-security-policy-ip] rule name untrust-trust
[DeviceA-security-policy-ip-4-untrust-trust] source-zone untrust
[DeviceA-security-policy-ip-4-untrust-trust] destination-zone trust
[DeviceA-security-policy-ip-4-untrust-trust] source-ip-subnet 10.1.2.0 24
[DeviceA-security-policy-ip-4-untrust-trust] destination-ip-subnet 10.1.1.0 24
[DeviceA-security-policy-ip-4-untrust-trust] action pass
[DeviceA-security-policy-ip-4-untrust-trust] quit
[DeviceA-security-policy-ip] quit
配置IPsec安全框架,建立IPsec隧道,保护需要防护的数据流
[DeviceA] ike keychain abc
[DeviceA-ike-keychain-abc] pre-shared-key address 2.2.3.1 255.255.255.0 key simple 123456TESTplat&!
[DeviceA-ike-keychain-abc] quit
[DeviceA] ike profile abc
[DeviceA-ike-profile-abc] keychain abc
[DeviceA-ike-profile-abc] local-identity address 2.2.2.1
[DeviceA-ike-profile-abc] match remote identity address 2.2.3.1 24
[DeviceA-ike-profile-abc] exchange-mode aggressive
[DeviceA-ike-profile-abc] quit
[DeviceA] ipsec transform-set abc
[DeviceA-ipsec-transform-set-abc] esp encryption-algorithm aes-cbc-128
[DeviceA-ipsec-transform-set-abc] esp authentication-algorithm sha1
[DeviceA-ipsec-transform-set-abc] quit
[DeviceA] ipsec profile abc isakmp
[DeviceA-ipsec-profile-isakmp-abc] transform-set abc
[DeviceA-ipsec-profile-isakmp-abc] ike-profile abc
[DeviceA-ipsec-profile-isakmp-abc] quit
配置IPsec隧道接口,用于对需要保护的流量进行IPsec封装
[DeviceA] interface tunnel 1
[DeviceA-Tunnel1] tunnel protection ipsec profile abc
[DeviceA-Tunnel1] quit
配置Device B
配置接口IP地址
# 根据组网图中规划的信息,配置各接口的IP地址,具体配置步骤如下。
<DeviceB> system-view
[DeviceB] interface gigabitethernet 1/0/1
[DeviceB-GigabitEthernet1/0/1] ip address 10.1.2.1 255.255.255.0
[DeviceB-GigabitEthernet1/0/1] quit
请参考以上步骤配置其他接口的IP地址,具体配置步骤略。
创建IPsec隧道接口
[DeviceB] interface tunnel 1 mode ipsec
[DeviceB-Tunnel1] ip address 3.3.3.2 255.255.255.0
[DeviceB-Tunnel1] source 2.2.3.1
[DeviceB-Tunnel1] destination 2.2.2.1
[DeviceB-Tunnel1] quit
配置静态路由
本举例仅以静态路由方式配置路由信息。实际组网中,请根据具体情况选择相应的路由配置方式。
# 请根据组网图中规划的信息,配置静态路由,本举例假设下一跳IP地址为2.2.3.2,实际使用中请以具体组网情况为准,具体配置步骤如下。
[DeviceB] ip route-static 10.1.1.0 24 2.2.3.2
[DeviceB] ip route-static 2.2.2.1 24 2.2.3.2
# 请根据组网图中规划的信息,配置静态路由,将需要保护的流量引入IPsec隧道接口,本举例的IPsec隧道接口为Tunnel1,具体配置步骤如下。
[DeviceA] ip route-static 10.1.1.0 255.255.255.0 tunnel 1
配置接口加入安全域。
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[DeviceB] security-zone name trust
[DeviceB-security-zone-Trust] import interface gigabitethernet 1/0/1
[DeviceB-security-zone-Trust] quit
[DeviceB] security-zone name untrust
[DeviceB-security-zone-Untrust] import interface gigabitethernet 1/0/2
[DeviceA-security-zone-Untrust] import interface tunnel 1
[DeviceB-security-zone-Untrust] quit
配置安全策略
配置安全策略放行Untrust与Local安全域之间的流量,用于设备之间可以建立IPsec隧道。
# 配置名称为ipseclocalout的安全策规则,使Device B可以向Device A发送IPsec隧道协商报文,具体配置步骤如下。
[DeviceB] security-policy ip
[DeviceB-security-policy-ip] rule name ipseclocalout
[DeviceB-security-policy-ip-1-ipseclocalout] source-zone local
[DeviceB-security-policy-ip-1-ipseclocalout] destination-zone untrust
[DeviceB-security-policy-ip-1-ipseclocalout] source-ip-host 2.2.3.1
[DeviceB-security-policy-ip-1-ipseclocalout] destination-ip-host 2.2.2.1
[DeviceB-security-policy-ip-1-ipseclocalout] action pass
[DeviceB-security-policy-ip-1-ipseclocalout] quit
# 配置名称为ipseclocalin的安全策略规则,使Device B可以接收和处理来自Device A的IPsec隧道协商报文,具体配置步骤如下。
[DeviceB-security-policy-ip] rule name ipseclocalin
[DeviceB-security-policy-ip-2-ipseclocalin] source-zone untrust
[DeviceB-security-policy-ip-2-ipseclocalin] destination-zone local
[DeviceB-security-policy-ip-2-ipseclocalin] source-ip-host 2.2.2.1
[DeviceB-security-policy-ip-2-ipseclocalin] destination-ip-host 2.2.3.1
[DeviceB-security-policy-ip-2-ipseclocalin] action pass
[DeviceB-security-policy-ip-2-ipseclocalin] quit
配置安全策略放行Host B与Host A之间的流量
# 配置名称为trust-untrust的安全策略规则,使Host B访问Host A的报文可通,具体配置步骤如下。
[DeviceB-security-policy-ip] rule name trust-untrust
[DeviceB-security-policy-ip-3-trust-untrust] source-zone trust
[DeviceB-security-policy-ip-3-trust-untrust] destination-zone untrust
[DeviceB-security-policy-ip-3-trust-untrust] source-ip-subnet 10.1.2.0 24
[DeviceB-security-policy-ip-3-trust-untrust] destination-ip-subnet 10.1.1.0 24
[DeviceB-security-policy-ip-3-trust-untrust] action pass
[DeviceB-security-policy-ip-3-trust-untrust] quit
# 配置名称为untrust-trust的安全策略规则,使Host A访问Host B的报文可通,具体配置步骤如下。
[DeviceB-security-policy-ip] rule name untrust-trust
[DeviceB-security-policy-ip-4-untrust-trust] source-zone untrust
[DeviceB-security-policy-ip-4-untrust-trust] destination-zone trust
[DeviceB-security-policy-ip-4-untrust-trust] source-ip-subnet 10.1.1.0 24
[DeviceB-security-policy-ip-4-untrust-trust] destination-ip-subnet 10.1.2.0 24
[DeviceB-security-policy-ip-4-untrust-trust] action pass
[DeviceB-security-policy-ip-4-untrust-trust] quit
[DeviceB-security-policy-ip] quit
配置IPsec安全框架,建立IPsec隧道,保护需要防护的数据流
[DeviceB] ike keychain abc
[DeviceB-ike-keychain-abc] pre-shared-key address 2.2.2.1 255.255.255.0 key simple 123456TESTplat&!
[DeviceB-ike-keychain-abc] quit
[DeviceB] ike profile abc
[DeviceB-ike-profile-abc] keychain abc
[DeviceB-ike-profile-abc] local-identity address 2.2.3.1
[DeviceB-ike-profile-abc] match remote identity address 2.2.2.1 24
[DeviceB-ike-profile-abc] exchange-mode aggressive
[DeviceB-ike-profile-abc] quit
[DeviceB] ipsec transform-set abc
[DeviceB-ipsec-transform-set-abc] esp encryption-algorithm aes-cbc-128
[DeviceB-ipsec-transform-set-abc] esp authentication-algorithm sha1
[DeviceB-ipsec-transform-set-abc] quit
[DeviceB] ipsec profile abc isakmp
[DeviceB-ipsec-profile-isakmp-abc] transform-set abc
[DeviceB-ipsec-profile-isakmp-abc] ike-profile abc
[DeviceB-ipsec-profile-isakmp-abc] quit
配置IPsec隧道接口,用于对需要保护的流量进行IPsec封装
[DeviceB] interface tunnel 1
[DeviceB-Tunnel1] tunnel protection ipsec profile abc
[DeviceB-Tunnel1] quit
验证配置
以上配置完成后,Device A会自动与Device B进行IKE协商。当IKE协商完成后,Device A和Device B上的IPsec 虚拟隧道接口都将up,即可以满足上述组网需求,对总部和分支的数据流进行安全保护。
# 通过display ip interface brief命令可查看接口状态如下:
<DeviceA> display ip interface brief
*down: administratively down
(s): spoofing (l): loopback
Interface Physical Protocol IP address/Mask VPN instance Description
GE1/0/1 up up 10.1.1.1/24 -- --
GE1/0/2 up up 2.2.2.1/24 -- --
Tun1 up up 3.3.3.1/24 -- --
# 通过display interface tunnel命令可查看隧道状态如下:
<DeviceA> display interface Tunnel 1
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1444
Internet address: 3.3.3.1/24 (primary)
Tunnel source 2.2.2.1, destination 2.2.3.1
Tunnel TTL 255
Tunnel protocol/transport IPsec/IP
Output queue - Urgent queuing: Size/Length/Discards 0/100/0
Output queue - Protocol queuing: Size/Length/Discards 0/500/0
Output queue - FIFO queuing: Size/Length/Discards 0/75/0
Last clearing of counters: Never
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# 通过display ipsec sa命令查看协商生成的IPsec SA:
<DeviceA> display ipsec sa
-------------------------------
Interface: Tunnel1
-------------------------------
-----------------------------
IPsec profile: abc
Alias: profile-abc
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Transmitting entity: Initiator
Path MTU: 1388
Tunnel:
local address/port: 2.2.2.1/500
remote address/port: 2.2.3.1/500
Flow:
sour addr: 0.0.0.0/0.0.0.0 port: 0 protocol: ip
dest addr: 0.0.0.0/0.0.0.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 2701952073 (0xa10c8449)
Connection ID: 4294967296
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3180
Max received sequence-number: 0
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 3607077598 (0xd6ffa2de)
Connection ID: 12884901889
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3180
Max sent sequence-number: 0
UDP encapsulation used for NAT traversal: N
Status: Active
# 在Device A上用私网地址可以Ping通Device B连接的私网地址:
<DeviceA> ping -a 10.1.1.1 10.1.2.1
Ping 10.1.2.1 (10.1.2.1) from 10.1.1.1: 56 data bytes, press CTRL_C to break
56 bytes from 10.1.2.1: icmp_seq=0 ttl=255 time=1.000 ms
56 bytes from 10.1.2.1: icmp_seq=1 ttl=255 time=1.000 ms
56 bytes from 10.1.2.1: icmp_seq=2 ttl=255 time=0.000 ms
56 bytes from 10.1.2.1: icmp_seq=3 ttl=255 time=1.000 ms
56 bytes from 10.1.2.1: icmp_seq=4 ttl=255 time=0.000 ms
--- Ping statistics for 10.1.2.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 0.000/0.600/1.000/0.490 ms
配置文件
Device A
#
interface GigabitEthernet1/0/1
ip address 10.1.1.1 255.255.255.0
#
interface GigabitEthernet1/0/2
ip address 2.2.2.1 255.255.255.0
#
interface Tunnel1 mode ipsec
ip address 3.3.3.1 255.255.255.0
source 2.2.2.1
destination 2.2.3.1
tunnel protection ipsec profile abc
#
security-zone name Trust
import interface GigabitEthernet1/0/1
#
security-zone name Untrust
import interface GigabitEthernet1/0/2
import interface Tunnel1
#
ip route-static 2.2.3.0 24 2.2.2.2
ip route-static 10.1.2.0 24 2.2.2.2
ip route-static 10.1.2.0 24 Tunnel1
#
ipsec transform-set abc
encapsulation-mode tunnel
protocol esp
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec profile abc isakmp
transform-set abc
ike-profile abc
#
ike profile abc
keychain abc
exchange-mode aggressive
local-identity address 2.2.2.1
match remote identity address 2.2.3.1 255.255.255.0
#
ike keychain abc
pre-shared-key address 2.2.3.1 255.255.255.0 key simple 123456TESTplat&!
#
security-policy ip
rule 0 name ipseclocalout
action pass
source-zone local
destination-zone untrust
source-ip-host 2.2.2.1
destination-ip-host 2.2.3.1
rule 1 name ipseclocalin
action pass
source-zone untrust
destination-zone local
source-ip-host 2.2.3.1
destination-ip-host 2.2.2.1
rule 2 name trust-untrust
action pass
source-zone trust
destination-zone untrust
source-ip-subnet 10.1.1.0 255.255.255.0
destination-ip-subnet 10.1.2.0 255.255.255.0
rule 3 name untrust-trust
action pass
source-zone untrust
destination-zone trust
source-ip-subnet 10.1.2.0 255.255.255.0
destination-ip-subnet 10.1.1.0 255.255.255.0
#
Device B
#
interface GigabitEthernet1/0/1
ip address 10.1.2.1 255.255.255.0
#
interface GigabitEthernet1/0/2
ip address 2.2.3.1 255.255.255.0
#
interface Tunnel1 mode ipsec
ip address 3.3.3.2 255.255.255.0
source 2.2.3.1
destination 2.2.2.1
tunnel protection ipsec profile abc
#
security-zone name Trust
import interface GigabitEthernet1/0/1
#
security-zone name Untrust
import interface GigabitEthernet1/0/2
import interface Tunnel1
#
ip route-static 2.2.2.0 24 2.2.3.2
ip route-static 10.1.1.0 24 2.2.3.2
ip route-static 10.1.1.0 24 tunnel1
#
ipsec transform-set abc
encapsulation-mode tunnel
protocol esp
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec profile abc isakmp
transform-set abc
ike-profile abc
#
ike profile abc
keychain abc
exchange-mode aggressive
local-identity address 2.2.3.1
match remote identity address 2.2.2.1 255.255.255.0
#
ike keychain abc
pre-shared-key address 2.2.2.1 255.255.255.0 key simple 123456TESTplat&!
#
security-policy ip
rule 0 name ipseclocalout
action pass
source-zone local
destination-zone untrust
source-ip-host 2.2.3.1
destination-ip-host 2.2.2.1
rule 1 name ipseclocalin
action pass
source-zone untrust
destination-zone local
source-ip-host 2.2.2.1
destination-ip-host 2.2.3.1
rule 2 name trust-untrust
action pass
source-zone trust
destination-zone untrust
source-ip-subnet 10.1.2.0 255.255.255.0
destination-ip-subnet 10.1.1.0 255.255.255.0
rule 3 name untrust-trust
action pass
source-zone untrust
destination-zone trust
source-ip-subnet 10.1.1.0 255.255.255.0
destination-ip-subnet 10.1.2.0 255.255.255.0
#