CLI方式:在安全策略中引用APT防御策略典型配置
使用版本
本举例是在T5030的R9900版本版本上进行配置和验证的。
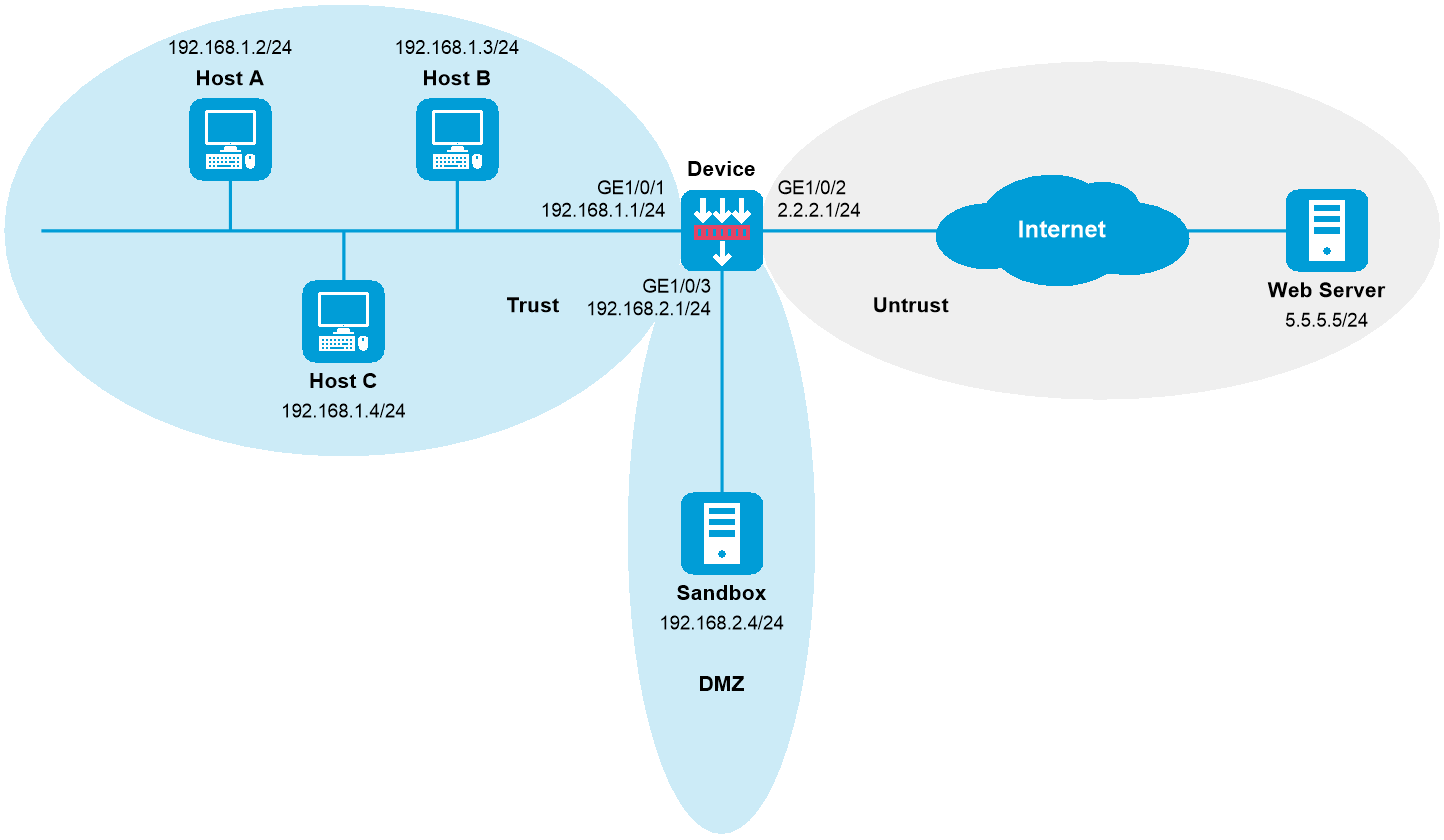
组网需求
如下图所示,Device分别通过Trust安全域和Untrust安全域与局域网和Internet相连。企业内网中部署了沙箱,且沙箱与Device路由可达。现需要Device与沙箱联动,保护内网用户免受APT攻击,当沙箱检测到APT攻击时,对攻击流量执行阻断操作。
注意事项
APT防御业务会占用较多的系统资源,仅建议内存在2GB以上的设备启用,其他设备请谨慎启用。
配置步骤
配置接口IP地址
# 根据组网图中规划的信息,配置各接口的IP地址,具体配置步骤如下。
<Device> system-view
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] ip address 192.168.1.1 255.255.255.0
[Device-GigabitEthernet1/0/1] quit
请参考以上步骤配置其他接口的IP地址,具体配置步骤略。
配置静态路由
本举例仅以静态路由方式配置路由信息。实际组网中,请根据具体情况选择相应的路由配置方式。
# 请根据组网图中规划的信息,配置静态路由,本举例假设到达外网Web Server的下一跳IP地址为2.2.2.2,实际使用中请以具体组网情况为准,具体配置步骤如下。
[Device] ip route-static 5.5.5.0 24 2.2.2.2
配置接口加入安全域
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[Device] security-zone name trust
[Device-security-zone-Trust] import interface gigabitethernet 1/0/1
[Device-security-zone-Trust] quit
[Device] security-zone name untrust
[Device-security-zone-Untrust] import interface gigabitethernet 1/0/2
[Device-security-zone-Untrust] quit
[Device] security-zone name dmz
[Device-security-zone-DMZ] import interface gigabitethernet 1/0/3
[Device-security-zone-DMZ] quit
配置沙箱联动功能
[Device] sandbox
[Device-sandbox] sandbox-address 192.168.2.4
[Device-sandbox] username admin
[Device-sandbox] password simple 123456abc
[Device-sandbox] linkage enable
[Device-sandbox] linkage try
配置APT防御策略
# 创建一个名称为apt1的APT防御策略,并配置需要送往沙箱检测的应用层协议为HTTP、文件类型为PE、文件传输方向为upload。
[Device] apt policy apt1
[Device-apt-policy-apt1] application type http
[Device-apt-policy-apt1] file-type pe
[Device-apt-policy-apt1] file-direction upload
[Device-apt-policy-apt1] quit
配置DPI应用profile引用APT防御策略和防病毒策略,具体配置步骤如下(本举例假设设备上已经配置了名称为antivirus1的防病毒策略,策略中将所有传输病毒文件的协议报文的动作设置为阻断。)
# 创建名为sec的DPI应用profile,并在其中引用名称为apt1的APT防御策略和名称为antivirus1的防病毒策略。
[Device] app-profile sec
[Device-app-profile-sec] apt apply policy apt1
[Device-app-profile-sec] anti-virus apply policy antivirus1 mode protect
[Device-app-profile-sec] quit
配置安全策略
配置名称为trust-untrust的安全策略规则,使内网用户可以访问外网,并对交互报文进行APT防御
[Device] security-policy ip
[Device-security-policy-ip] rule name trust-untrust
[Device-security-policy-ip-10-trust-untrust] source-zone trust
[Device-security-policy-ip-10-trust-untrust] source-ip-subnet 192.168.1.0 24
[Device-security-policy-ip-10-trust-untrust] destination-zone untrust
[Device-security-policy-ip-10-trust-untrust] action pass
[Device-security-policy-ip-10-trust-untrust] profile sec
[Device-security-policy-ip-10-trust-untrust] quit
配置名称为sandboxlocalout的安全策略规则,使设备可将待检测流量上送到沙箱服务器进行检测
[Device-security-policy-ip] rule name sandboxlocalout
[Device-security-policy-ip-11-sandboxlocalout] source-zone local
[Device-security-policy-ip-11-sandboxlocalout] destination-zone dmz
[Device-security-policy-ip-11-sandboxlocalout] destination-ip-subnet 192.168.2.0 24
[Device-security-policy-ip-11-sandboxlocalout] action pass
[Device-security-policy-ip-11-sandboxlocalout] quit
配置名称为sandboxlocalin的安全策略规则,使沙箱服务器可将检测结果下发到设备
[Device-security-policy-ip] rule name sandboxlocalin
[Device-security-policy-ip-12-sandboxlocalin] source-zone dmz
[Device-security-policy-ip-12-sandboxlocalin] destination-zone local
[Device-security-policy-ip-12-sandboxlocalin] source-ip-subnet 192.168.2.0 24
[Device-security-policy-ip-12-sandboxlocalin] action pass
[Device-security-policy-ip-12-sandboxlocalin] quit
# 激活安全策略配置。
[Device-security-policy-ip] accelerate enhanced enable
[Device-security-policy-ip] quit
验证配置
以上配置生效后,Device将与沙箱联动,保护内网用户免受APT攻击,当沙箱检测到APT攻击时,对后续攻击流量执行阻断操作。
配置文件
Device
#
interface GigabitEthernet1/0/1
ip address 192.168.1.1 255.255.255.0
#
interface GigabitEthernet1/0/2
ip address 2.2.2.1 255.255.255.0
#
interface GigabitEthernet1/0/3
ip address 192.168.2.1 255.255.255.0
#
security-zone name Trust
import interface GigabitEthernet1/0/1
#
security-zone name DMZ
import interface GigabitEthernet1/0/3
#
security-zone name Untrust
import interface GigabitEthernet1/0/2
#
ip route-static 5.5.5.0 24 2.2.2.2
#
apt policy apt1
application type http
file-direction upload
file-type pe
#
app-profile sec
anti-virus apply policy antivirus1 mode protect
apt apply policy apt1
#
sandbox
sandbox-address 192.168.2.4
username admin
password simple 123456abc
linkage enable
file exe max-size 2048
file zip max-size 2048
file office max-size 2048
file pdf max-size 2048
file picture max-size 500
file web max-size 500
file video max-size 2048
file other max-size 2048
#
security-policy ip
accelerate enhanced enable
rule 0 name trust-untrust
action pass
profile sec
source-zone trust
destination-zone untrust
source-ip-subnet 192.168.1.0 255.255.255.0
rule 1 name sandboxlocalout
action pass
source-zone local
destination-zone dmz
destination-ip-subnet 192.168.2.0 255.255.255.0
rule 2 name sandboxlocalin
action pass
source-zone dmz
destination-zone local
source-ip-subnet 192.168.2.0 255.255.255.0
#