CLI方式:主机与网关之间采用IKE方式建立保护IPv4报文的IPsec隧道典型配置(远程扩展认证方式)
使用版本
本举例是在F5000-AI-55-G的E9900版本上进行配置和验证的。
组网需求
如下图所示,用户主机Host和Device之间建立一个IPsec隧道,对用户主机和Device之间的数据流进行安全保护。
Host和Device之间采用IKE协商方式建立IPsec SA。
IKE第一阶段协商的认证方法为预共享密钥认证。
Device对Host进行IKE扩展认证,认证方式采用远程RADIUS认证。
图-1 IKE支持远程扩展认证配置组网图
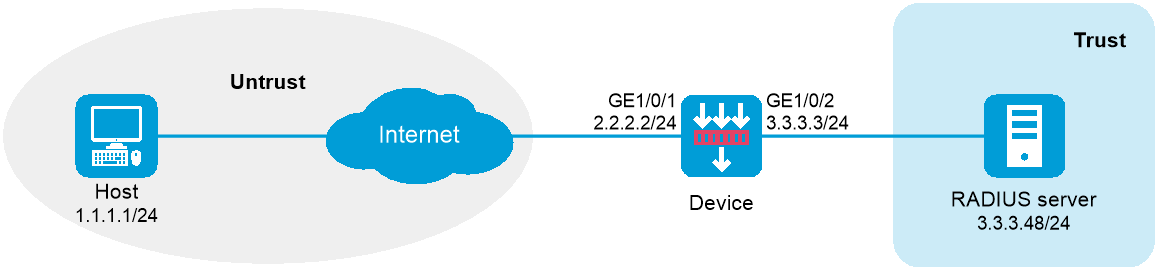

请保证Host与Device之间路由可达。
完成RADIUS服务器上的配置,保证Host使用指定的用户名和密码(本例中,用户名为test,密码为123456TESTplat&!)可以完成身份认证。
配置步骤
配置Device
配置接口IP地址
# 根据组网图中规划的信息,配置各接口的IP地址,具体配置步骤如下。
<Device> system-view
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] ip address 2.2.2.2 255.255.255.0
[Device-GigabitEthernet1/0/1] quit
[Device] interface GigabitEthernet1/0/2
[Device-GigabitEthernet1/0/2] ip address 3.3.3.3 255.255.255.0
[Device-GigabitEthernet1/0/2] quit
配置静态路由
本举例仅以静态路由方式配置路由信息。实际组网中,请根据具体情况选择相应的路由配置方式。
# 请根据组网图中规划的信息,配置静态路由,本举例假设到达Host所在网络的下一跳IP地址为2.2.2.3实际使用中请以具体组网情况为准,具体配置步骤如下。
[Device] ip route-static 1.1.1.1 24 2.2.2.3
配置接口加入安全域。
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[Device] security-zone name untrust
[Device-security-zone-Untrust] import interface gigabitethernet 1/0/1
[Device-security-zone-Untrust] quit
[Device] security-zone name trust
[Device-security-zone-Trust] import interface gigabitethernet 1/0/2
[Device-security-zone-Trust] quit
配置安全策略放行Untrust与Local安全域之间的流量,用于Host访问设备。
# 配置名称为ipseclocalout1的安全策规则,使Device可以向Host发送报文,具体配置步骤如下。
[Device] security-policy ip
[Device-security-policy-ip] rule name ipseclocalout1
[Device-security-policy-ip-1-ipseclocalout1] source-zone local
[Device-security-policy-ip-1-ipseclocalout1] destination-zone untrust
[Device-security-policy-ip-1-ipseclocalout1] source-ip-host 2.2.2.2
[Device-security-policy-ip-1-ipseclocalout1] destination-ip-host 1.1.1.1
[Device-security-policy-ip-1-ipseclocalout1] action pass
[Device-security-policy-ip-1-ipseclocalout1] quit
# 配置名称为ipseclocalin1的安全策略规则,使Host可以向Device发送报文,具体配置步骤如下。
[Device-security-policy-ip] rule name ipseclocalin1
[Device-security-policy-ip-2-ipseclocalin1] source-zone untrust
[Device-security-policy-ip-2-ipseclocalin1] destination-zone local
[Device-security-policy-ip-2-ipseclocalin1] source-ip-host 1.1.1.1
[Device-security-policy-ip-2-ipseclocalin1] destination-ip-host 2.2.2.2
[Device-security-policy-ip-2-ipseclocalin1] action pass
[Device-security-policy-ip-2-ipseclocalin1] quit
# 配置名称为ipseclocalout2的安全策规则,使Device可以向RADIUS server发送报文,具体配置步骤如下。
[Device-security-policy-ip] rule name ipseclocalout2
[Device-security-policy-ip-3-ipseclocalout2] source-zone local
[Device-security-policy-ip-3-ipseclocalout2] destination-zone trust
[Device-security-policy-ip-3-ipseclocalout2] source-ip-host 3.3.3.3
[Device-security-policy-ip-3-ipseclocalout2] destination-ip-host 3.3.3.48
[Device-security-policy-ip-3-ipseclocalout2] action pass
[Device-security-policy-ip-3-ipseclocalout2] quit
# 配置名称为ipseclocalin2的安全策略规则,使RADIUS server可以向Device发送报文,具体配置步骤如下。
[Device-security-policy-ip] rule name ipseclocalin2
[Device-security-policy-ip-4-ipseclocalin2] source-zone trust
[Device-security-policy-ip-4-ipseclocalin2] destination-zone local
[Device-security-policy-ip-4-ipseclocalin2] source-ip-host 3.3.3.48
[Device-security-policy-ip-4-ipseclocalin2] destination-ip-host 3.3.3.3
[Device-security-policy-ip-4-ipseclocalin2] action pass
[Device-security-policy-ip-4-ipseclocalin2] quit
[Device-security-policy-ip] quit
配置RADIUS方案
# 创建RADIUS方案ike-scheme。
[Device] radius scheme ike-scheme
# 配置主RADIUS认证服务器IP地址为3.3.3.48,端口为1645。
[Device-radius-ike-scheme] primary authentication 3.3.3.48 1645
# 配置与认证服务器交互报文时的共享密钥为明文abc。
[Device-radius-ike-scheme] key authentication simple abc
# 配置向RADIUS服务器发送的用户名不携带域名。(此配置可根据服务器对用户名的要求调整)
[Device-radius-ike-scheme] user-name-format without-domain
[Device-radius-ike-scheme] quit
配置ISP域
# 配置ISP域ike,指定IKE用户的认证方法。
[Device] domain ike
[Device-isp-ike] authentication ike radius-scheme ike-scheme
[Device-isp-ike] quit
定义数据流
# 配置IPv4高级ACL 3101,定义要保护由2.2.2.2到1.1.1.1的数据流。
[Device] acl advanced 3101
[Device-acl-ipv4-adv-3101] rule permit ip source 2.2.2.2 0.0.0.0 destination 1.1.1.1 0.0.0.0
[Device-acl-ipv4-adv-3101] quit
配置IPsec安全提议,协商封装报文使用的各种安全协议
# 创建IPsec安全提议tran1,两端配置的安全提议参数需要完全相同,具体配置步骤如下。
[Device] ipsec transform-set tran1
[Device-ipsec-transform-set-tran1] encapsulation-mode transport
[Device-ipsec-transform-set-tran1] protocol esp
[Device-ipsec-transform-set-tran1] esp encryption-algorithm aes-cbc-128
[Device-ipsec-transform-set-tran1] esp authentication-algorithm sha1
[Device-ipsec-transform-set-tran1] quit
配置IKE keychain,约定通信双方使用的密钥信息
# 创建IKE keychain,名称为keychain1,协商双方配置的预共享密钥必须完全相同,具体配置步骤如下。
[Device] ike keychain keychain1
[Device-ike-keychain-keychain1] pre-shared-key address 1.1.1.1 255.255.255.255 key simple 123456TESTplat&!
[Device-ike-keychain-keychain1] quit
配置IKE profile,约定建立IKE SA所需的安全参数
[Device] ike profile profile1
[Device-ike-profile-profile1] keychain keychain1
[Device-ike-profile-profile1] local-identity address 2.2.2.2
[Device-ike-profile-profile1] match remote identity address 1.1.1.1 255.255.255.255
[Device-ike-profile-profile1] client-authentication xauth
[Device-ike-profile-profile1] quit
配置IPsec安全策略,建立IPsec隧道,保护需要防护的数据流
# 创建一条IKE协商方式的IPsec安全策略,名称为map1,顺序号为10。
[Device] ipsec policy map1 10 isakmp
[Device-ipsec-policy-isakmp-map1-10] remote-address 1.1.1.1
[Device-ipsec-policy-isakmp-map1-10] security acl 3101
[Device-ipsec-policy-isakmp-map1-10] transform-set tran1
[Device-ipsec-policy-isakmp-map1-10] ike-profile profile1
[Device-ipsec-policy-isakmp-map1-10] quit
在接口上应用IPsec安全策略
# 在接口GigabitEthernet1/0/1上应用IPsec安全策略map1。
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] ipsec apply policy map1
[Device-GigabitEthernet1/0/1] quit
配置Host
Host上需要完成IPsec VPN客户端的如下主要配置,并保证与Device端的相关配置相匹配:
IPsec隧道对端的安全网关IP地址
IKE第一阶段认证采用的预共享密钥
扩展认证采用的用户名和密码
IPsec安全协议,以及采用的加密算法、认证算法
IKE协商参数
本地及远端的ID类型与取值
验证配置
以上配置完成后,Host和Device之间如果有1.1.1.1与2.2.2.2之间的报文通过,将触发IKE协商。
# 可通过如下显示信息查看到Device上IKE第一阶段协商成功后生成的IKE SA的详细信息,并可查看到对客户端的扩展认证处于开启状态。
[Device] display ike sa verbose remote-address 1.1.1.1
-----------------------------------------------
Connection ID: 18
Outside VPN:
Inside VPN:
Profile: profile1
Transmitting entity: Initiator
-----------------------------------------------
Local IP/port: 2.2.2.2/500
Local ID type: IPV4_ADDR
Local ID: 2.2.2.2
Remote IP/port: 1.1.1.1/500
Remote ID type: IPV4_ADDR
Remote ID: 1.1.1.1
Authentication-method: PRE-SHARED-KEY
Authentication-algorithm: SHA1
Encryption-algorithm: DES-CBC
Life duration(sec): 86400
Remaining key duration(sec): 84565
Exchange-mode: Aggressive
Diffie-Hellman group: Group 1
NAT traversal: Detected
Extend authentication: Enabled
Assigned IP address:
若Host端提供了正确的用户名和密码,将能够与Device之间成功建立IPsec隧道。在Device上可以通过display ipsec sa命令查看到生成的IPsec SA信息。
配置文件
Device
#
interface GigabitEthernet1/0/1
ip address 2.2.2.2 255.255.255.0
ipsec apply policy map1
#
interface GigabitEthernet1/0/2
ip address 3.3.3.3 255.255.255.0
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
ip route-static 1.1.1.0 24 2.2.2.3
#
acl advanced 3101
rule 0 permit ip source 2.2.2.2 0 destination 1.1.1.1 0
#
radius scheme ike-scheme
primary authentication 3.3.3.48 1645
key authentication simple abc
user-name-format without-domain
#
domain ike
authentication ike radius-scheme ike-scheme
#
ipsec transform-set tran1
encapsulation-mode transport
protocol esp
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy map1 10 isakmp
transform-set tran1
security acl 3101
remote-address 1.1.1.1
ike-profile profile1
#
ike profile profile1
keychain keychain1
local-identity address 2.2.2.2
match remote identity address 1.1.1.1 255.255.255.255
client-authentication xauth
#
ike keychain keychain1
pre-shared-key address 1.1.1.1 255.255.255.255 key simple 123456TESTplat&!
#
security-policy ip
rule 0 name ipseclocalout1
action pass
source-zone local
destination-zone untrust
source-ip-host 2.2.2.2
destination-ip-host 1.1.1.1
rule 1 name ipseclocalin1
action pass
source-zone untrust
destination-zone local
source-ip-host 1.1.1.1
destination-ip-host 2.2.2.2
rule 2 name ipseclocalout2
action pass
source-zone local
destination-zone trust
source-ip-host 3.3.3.3
destination-ip-host 3.3.3.48
rule 3 name ipseclocalin2
action pass
source-zone trust
destination-zone local
source-ip-host 3.3.3.48
destination-ip-host 3.3.3.3
#