CLI方式:IPsec over L2TP典型配置(国密算法)
使用版本
本举例是在F5000-AI-55-G的E9900版本上进行配置和验证的。
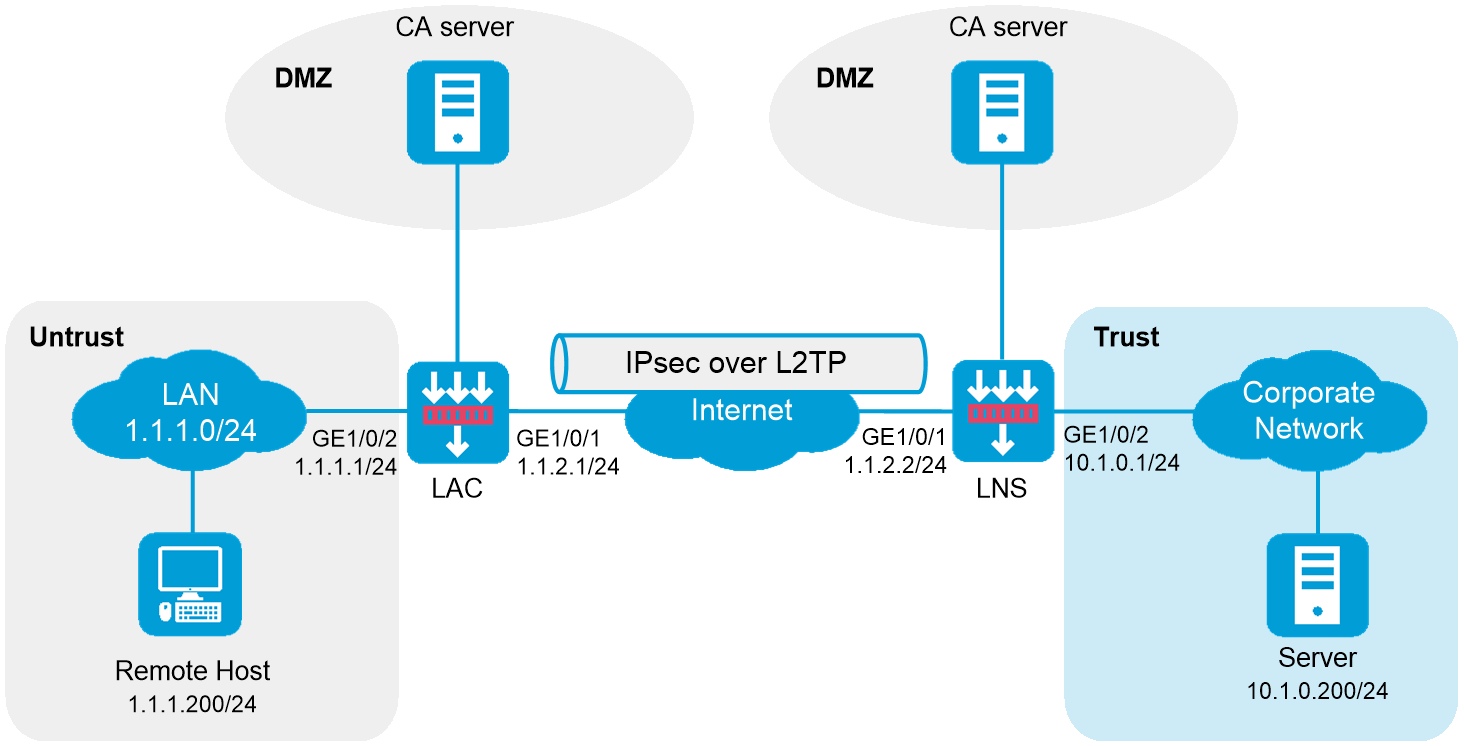
组网需求
如下图所示,用户接入之前,在LAC和LNS之间采用LAC-Auto-Initiated模式建立L2TP隧道。用户接入后,通过已经建立的L2TP隧道访问公司总部。同时在LAC和LNS之间建立一个IPsec隧道,对数据流进行IPsec安全保护。
图-1 IPsec over L2TP典型配置组网图
配置步骤
配置LAC
| 在开始下面的配置之前,假设已完成如下配置:LAC已获取到CA证书ca.cer和服务器证书server.pfx。 |
配置接口IP地址
# 根据组网图中规划的信息,配置各接口的IP地址,具体配置步骤如下。
<LAC> system-view
[LAC] interface gigabitethernet 1/0/1
[LAC-GigabitEthernet1/0/1] ip address 1.1.2.1 255.255.255.0
[LAC-GigabitEthernet1/0/1] quit
请参考以上步骤配置其他接口的IP地址,具体配置步骤略。
定义需要保护的数据流
# 配置IPv4高级ACL 3101,定义要保护由1.1.1.200去往10.1.0.200的数据流。
[LAC] acl advanced 3101
[LAC-acl-ipv4-adv-3101] rule permit ip source 1.1.1.200 0.0.0.0 destination 10.1.0.200 0.0.0.0
[LAC-acl-ipv4-adv-3101] quit
配置IPsec安全提议,协商封装报文使用的各种安全协议
# 创建IPsec安全提议,两端配置的安全提议参数需要完全相同,具体配置步骤如下。
[LAC] ipsec transform-set tran1
[LAC-ipsec-transform-set-tran1] encapsulation-mode tunnel
[LAC-ipsec-transform-set-tran1] protocol esp
[LAC-ipsec-transform-set-tran1] esp encryption-algorithm sm4-cbc
[LAC-ipsec-transform-set-tran1] esp authentication-algorithm sm3
[LAC-ipsec-transform-set-tran1] quit
配置PKI实体,设置PKI实体的身份信息
[LAC] pki entity entity1
[LAC-pki-entity-entity1] common-name lac
[LAC-pki-entity-entity1] quit
配置PKI域,约定PKI证书申请的相关信息
[LAC] pki domain domain1
[LAC-pki-domain-domain1] public-key rsa general name sm2-1
[LAC-pki-domain-domain1] undo crl check enable
[LAC-pki-domain-domain1] quit
[LAC] pki import domain domain1 der ca filename ca.cer
[LAC] pki import domain domain1 p12 local filename server.pfx
配置IKE提议,定义双方进行IKE协商所需的安全参数
[LAC] ike proposal 10
[LAC-ike-proposal-10] authentication-method sm2-de
[LAC-ike-proposal-10] authentication-algorithm sm3
[LAC-ike-proposal-10] encryption-algorithm sm4-cbc
[LAC-ike-proposal-10] quit
配置IKE profile,约定建立IKE SA所需的安全参数
[LAC] ike profile profile1
[LAC-ike-profile-profile1] exchange-mode gm-main
[LAC-ike-profile-profile1] certificate domain domain1
[LAC-ike-profile-profile1] proposal 10
[LAC-ike-profile-profile1] local-identity address 192.168.0.10
[LAC-ike-profile-profile1] match remote identity address 192.168.0.1 255.255.255.0
[LAC-ike-profile-profile1] quit
配置IPsec安全策略,建立IPsec隧道,保护需要防护的数据流
# 创建一条手工方式的IPsec安全策略,引用需要保护数据流的ACL和所需的IPsec安全提议,指定对端的IP地址,具体配置步骤如下。
[LAC] ipsec policy map1 10 isakmp
[LAC-ipsec-policy-isakmp-map1-10] remote-address 192.168.0.1
[LAC-ipsec-policy-isakmp-map1-10] security acl 3101
[LAC-ipsec-policy-isakmp-map1-10] transform-set tran1
[LAC-ipsec-policy-isakmp-map1-10] ike-profile profile1
[LAC-ipsec-policy-isakmp-map1-10] quit
创建虚拟PPP接口Virtual-PPP 1,配置PPP用户的用户名为vpdnuser、密码为Hello,并配置PPP验证方式为PAP。同时在接口上应用IPsec安全策略,对接口上的流量进行保护
[LAC] interface virtual-ppp 1
[LAC-Virtual-PPP1] ip address ppp-negotiate
[LAC-Virtual-PPP1] ppp pap local-user vpdnuser password simple Hello
[LAC-Virtual-PPP1] ipsec apply policy map1
[LAC-Virtual-PPP1] quit
开启L2TP功能
[LAC] l2tp enable
创建LAC模式的L2TP组1,配置隧道本端名称为LAC,并指定LNS地址为1.1.2.2
[LAC] l2tp-group 1 mode lac
[LAC-l2tp1] tunnel name LAC
[LAC-l2tp1] lns-ip 1.1.2.2
启用隧道验证功能,并设置隧道验证密钥为example
[LAC-l2tp1] tunnel authentication
[LAC-l2tp1] tunnel password simple example
[LAC-l2tp1] quit
触发LAC发起L2TP隧道建立请求
[LAC] interface virtual-ppp 1
[LAC-Virtual-PPP1] l2tp-auto-client l2tp-group 1
[LAC-Virtual-PPP1] quit
配置接口加入安全域
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[LAC] security-zone name untrust
[LAC-security-zone-Untrust] import interface virtual-ppp 1
[LAC-security-zone-Untrust] import interface gigabitethernet 1/0/2
[LAC-security-zone-Untrust] import interface gigabitethernet 1/0/1
[LAC-security-zone-Untrust] quit
配置安全策略
配置安全策略放行Untrust与Local安全域之间的流量
# 配置名称为localout的安全策略规则,使LAC可以向LNS发送报文,具体配置步骤如下。
[LAC] security-policy ip
[LAC-security-policy-ip] rule name localout
[LAC-security-policy-ip-1-localout] source-zone local
[LAC-security-policy-ip-1-localout] destination-zone untrust
[LAC-security-policy-ip-1-localout] source-ip-host 1.1.2.1
[LAC-security-policy-ip-1-localout] destination-ip-host 1.1.2.2
[LAC-security-policy-ip-1-localout] action pass
[LAC-security-policy-ip-1-localout] quit
# 配置名称为localin的安全策略规则,使LAC可以接收和处理来自LNS的报文,具体配置步骤如下。
[LAC-security-policy-ip] rule name localin
[LAC-security-policy-ip-2-localin] source-zone untrust
[LAC-security-policy-ip-2-localin] destination-zone local
[LAC-security-policy-ip-2-localin] source-ip-host 1.1.2.2
[LAC-security-policy-ip-2-localin] destination-ip-host 1.1.2.1
[LAC-security-policy-ip-2-localin] action pass
[LAC-security-policy-ip-2-localin] quit
配置安全策略放行Host与Server之间的流量
# 配置名称为untrust的安全策略规则,使Host访问Server和Server访问Host的报文可通,具体配置步骤如下。
[LAC-security-policy-ip] rule name untrust
[LAC-security-policy-ip-3-untrust] source-zone untrust
[LAC-security-policy-ip-3-untrust] destination-zone untrust
[LAC-security-policy-ip-3-untrust] action pass
[LAC-security-policy-ip-3-untrust] quit
[LAC-security-policy-ip] quit
请根据组网图中规划的信息,配置静态路由
本举例仅以静态路由方式配置路由信息。实际组网中,请根据具体情况选择相应的路由配置方式。配置静态路由,访问公司总部的报文将通过L2TP隧道转发,具体配置步骤如下。
[LAC] ip route-static 10.1.0.0 24 virtual-ppp 1
配置LNS
| 在开始下面的配置之前,假设已完成如下配置:LNS已获取到CA证书ca.cer和服务器证书server.pfx。 |
配置接口IP地址
# 根据组网图中规划的信息,配置各接口的IP地址,具体配置步骤如下。
<LNS> system-view
[LNS] interface gigabitethernet 1/0/1
[LNS-GigabitEthernet1/0/1] ip address 1.1.2.2 255.255.255.0
[LNS-GigabitEthernet1/0/1] quit
请参考以上步骤配置其他接口的IP地址,具体配置步骤略。
定义需要保护的数据流
# 配置IPv4高级ACL 3101,定义要保护由10.1.0.200去往1.1.1.200的数据流。
[LNS] acl advanced 3101
[LNS-acl-ipv4-adv-3101] rule permit ip source 10.1.0.200 0.0.0.0 destination 1.1.1.200 0.0.0.0
[LNS-acl-ipv4-adv-3101] quit
配置IPsec安全提议,协商封装报文使用的各种安全协议
[LNS] ipsec transform-set tran1
[LNS-ipsec-transform-set-tran1] encapsulation-mode tunnel
[LNS-ipsec-transform-set-tran1] protocol esp
[LNS-ipsec-transform-set-tran1] esp encryption-algorithm sm4-cbc
[LNS-ipsec-transform-set-tran1] esp authentication-algorithm sm3
[LNS-ipsec-transform-set-tran1] quit
配置PKI实体,设置PKI实体的身份信息
[LNS] pki entity entity2
[LNS-pki-entity-entity2] common-name lns
[LNS-pki-entity-entity2] quit
配置PKI域,约定PKI证书申请的相关信息
[LNS] pki domain domain2
[LNS-pki-domain-domain2] public-key rsa general name sm2-1
[LNS-pki-domain-domain2] undo crl check enable
[LNS-pki-domain-domain2] quit
[LNS] pki import domain domain2 der ca filename ca.cer
[LNS] pki import domain domain2 p12 local filename server.pfx
配置IKE提议,定义双方进行IKE协商所需的安全参数
[LNS] ike proposal 10
[LNS-ike-proposal-10] authentication-method sm2-de
[LNS-ike-proposal-10] authentication-algorithm sm3
[LNS-ike-proposal-10] encryption-algorithm sm4-cbc
[LNS-ike-proposal-10] quit
配置IKE profile,约定建立IKE SA所需的安全参数
[LNS] ike profile profile1
[LNS-ike-profile-profile1] exchange-mode gm-main
[LNS-ike-profile-profile1] certificate domain domain2
[LNS-ike-profile-profile1] proposal 10
[LNS-ike-profile-profile1] local-identity address 192.168.0.1
[LNS-ike-profile-profile1] match remote identity address 192.168.0.10 255.255.255.0
[LNS-ike-profile-profile1] quit
配置IPsec安全策略,建立IPsec隧道,保护需要防护的数据流
# 创建一条手工方式的IPsec安全策略,引用需要保护数据流的ACL和所需的IPsec安全提议,指定对端的IP地址,具体配置步骤如下。
[LNS] ipsec policy use1 10 isakmp
[LNS-ipsec-policy-isakmp-use1-10] remote-address 192.168.0.10
[LNS-ipsec-policy-isakmp-use1-10] security acl 3101
[LNS-ipsec-policy-isakmp-use1-10] transform-set tran1
[LNS-ipsec-policy-isakmp-use1-10] ike-profile profile1
[LNS-ipsec-policy-isakmp-use1-10] quit
创建接口Virtual-Template1,配置VT口IP地址,PPP认证方式为PAP,并指定为Client端分配IP地址为192.168.0.10。同时在接口上应用IPsec安全策略,对接口上的流量进行保护
[LNS] interface virtual-template 1
[LNS-Virtual-Template1] ip address 192.168.0.1 24
[LNS-Virtual-Template1] ppp authentication-mode pap
[LNS-Virtual-Template1] remote address 192.168.0.10
[LNS-Virtual-Template1] ipsec apply policy use1
[LNS-Virtual-Template1] quit
创建本地PPP用户vpdnuser,设置密码为Hello
[LNS] local-user vpdnuser class network
[LNS-luser-network-vpdnuser] password simple Hello
[LNS-luser-network-vpdnuser] service-type ppp
[LNS-luser-network-vpdnuser] quit
配置ISP域system对PPP用户采用本地验证
[LNS] domain system
[LNS-isp-system] authentication ppp local
[LNS-isp-system] quit
开启L2TP功能
[LNS] l2tp enable
创建LNS模式的L2TP组1,配置隧道本端名称为LNS,指定接收呼叫的虚拟模板接口为VT1,并配置隧道对端名称为LAC
[LNS] l2tp-group 1 mode lns
[LNS-l2tp1] tunnel name LNS
[LNS-l2tp1] allow l2tp virtual-template 1 remote LAC
启用隧道验证功能,并设置隧道验证密钥为example
[LNS-l2tp1] tunnel authentication
[LNS-l2tp1] tunnel password simple example
[LNS-l2tp1] quit
配置接口加入安全域
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[LNS] security-zone name trust
[LNS-security-zone-Trust] import interface gigabitethernet 1/0/2
[LNS-security-zone-Trust] quit
[LNS] security-zone name untrust
[LNS-security-zone-Untrust] import interface Virtual-Template 1
[LNS-security-zone-Untrust] import interface gigabitethernet 1/0/1
[LNS-security-zone-Untrust] quit
配置安全策略
配置安全策略放行Untrust与Local安全域之间的流量
# 配置名称为localout的安全策略规则,使LNS可以向LAC发送报文,具体配置步骤如下。
[LNS] security-policy ip
[LNS-security-policy-ip] rule name localout
[LNS-security-policy-ip-1-localout] source-zone local
[LNS-security-policy-ip-1-localout] destination-zone untrust
[LNS-security-policy-ip-1-localout] source-ip-host 1.1.2.2
[LNS-security-policy-ip-1-localout] destination-ip-host 1.1.2.1
[LNS-security-policy-ip-1-localout] action pass
[LNS-security-policy-ip-1-localout] quit
# 配置名称为localin的安全策略规则,使LNS可以接收和处理来自LAC、Host的报文,具体配置步骤如下。
[LNS-security-policy-ip] rule name localin
[LNS-security-policy-ip-2-localin] source-zone untrust
[LNS-security-policy-ip-2-localin] destination-zone local
[LNS-security-policy-ip-2-localin] destination-ip-host 1.1.2.2
[LNS-security-policy-ip-2-localin] action pass
[LNS-security-policy-ip-2-localin] quit
配置安全策略放行Server与Host 之间的流量
# 配置名称为trust-untrust的安全策略规则,使Server与Host的报文可通,具体配置步骤如下。
[LNS-security-policy-ip] rule name trust-untrust
[LNS-security-policy-ip-3-trust-untrust] source-zone trust
[LNS-security-policy-ip-3-trust-untrust] source-zone untrust
[LNS-security-policy-ip-3-trust-untrust] destination-zone trust
[LNS-security-policy-ip-3-trust-untrust] destination-zone untrust
[LNS-security-policy-ip-3-trust-untrust] action pass
[LNS-security-policy-ip-3-trust-untrust] quit
[LNS-security-policy-ip] quit
请根据组网图中规划的信息,配置静态路由
本举例仅以静态路由方式配置路由信息。实际组网中,请根据具体情况选择相应的路由配置方式。
请根据组网图中规划的信息,配置静态路由,本举例假设到达远端主机网络下一跳IP地址为192.168.0.10,实际使用中请以具体组网情况为准,具体配置步骤如下。
[LNS] ip route-static 1.1.1.0 24 192.168.0.10
Remote host侧的配置
Remote host上应将LAC设置为网关。
验证配置
IPsec验证
可通过如下显示信息查看到LAC和LNS上的IKE提议
[LAC] display ike proposal
Priority Authentication Authentication Encryption Diffie-Hellman Duration
method algorithm algorithm group (seconds)
----------------------------------------------------------------------------
10 SM2-DE SM3 SM4-CBC Group 1 86400
default PRE-SHARED-KEY SHA1 DES-CBC Group 1 86400
[LNS] display ike proposal
Priority Authentication Authentication Encryption Diffie-Hellman Duration
method algorithm algorithm group (seconds)
----------------------------------------------------------------------------
10 SM2-DE SM3 SM4-CBC Group 1 86400
default PRE-SHARED-KEY SHA1 DES-CBC Group 1 86400
可通过如下显示信息查看到LAC上IKE第一阶段协商成功后生成的IKE SA
[LAC] display ike sa
RD--READY RL--REPLACED FD-FADING RK-REKEY
ID Profile Remote Flag Remote-Type Remote-ID
--------------------------------------------------------------------------------
1 profile1 192.168.0.1 RD IPV4_ADDR 192.168.0.1
可通过如下显示信息查看到IKE第二阶段协商生成的IPsec SA
[LAC] display ipsec sa
-------------------------------
Interface: Virtual-PPP1
-------------------------------
-----------------------------
IPsec policy: map1
Sequence number: 10
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1456
Tunnel:
local address/port: 192.168.0.10/500
remote address/port: 192.168.0.1/500
Flow:
sour addr: 1.1.1.200/255.255.255.0 port: 0 protocol: ip
dest addr: 10.1.0.200/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 1451246811 (0x568044db)
Connection ID: 90194313219
Transform set: ESP-ENCRYPT-SM4-CBC ESP-AUTH-SM3
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3484
Max received sequence-number:
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 2692887942 (0xa0823586)
Connection ID: 64424509441
Transform set: ESP-ENCRYPT-SM4-CBC ESP-AUTH-SM3
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3484
Max sent sequence-number:
UDP encapsulation used for NAT traversal: N
Status: Active
LNS上也会产生相应的IKE SA和IPsec SA,查看方式与LAC相同,此处略
L2TP验证
在LNS侧,通过命令display l2tp tunnel可查看建立的L2TP隧道
[LNS] display l2tp tunnel
LocalTID RemoteTID State Sessions RemoteAddress RemotePort RemoteName
52525 33375 Established 1 1.1.2.1 1701 LAC
在LNS侧,通过命令display l2tp session可查看建立的L2TP会话
[LNS] display l2tp session
LocalSID RemoteSID LocalTID State
21073 11183 52525 Established
在Remote host上Ping公司总部内的服务器10.1.0.200,可以成功Ping通
C:\> ping 10.1.0.200
Pinging 10.1.0.200 with 32 bytes of data:
Reply from 10.1.0.200: bytes=32 time<1ms TTL=253
Reply from 10.1.0.200: bytes=32 time<1ms TTL=253
Reply from 10.1.0.200: bytes=32 time<1ms TTL=253
Reply from 10.1.0.200: bytes=32 time<1ms TTL=253
Ping statistics for 10.1.0.200:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 0ms, Maximum = 0ms, Average = 0ms
配置文件
LAC
#
interface Virtual-PPP1
ppp pap local-user vpdnuser password simple Hello
ip address ppp-negotiate
l2tp-auto-client l2tp-group 1
ipsec apply policy map1
#
interface GigabitEthernet1/0/1
port link-mode route
ip address 1.1.2.1 255.255.255.0
#
interface GigabitEthernet1/0/2
port link-mode route
ip address 1.1.1.1 255.255.255.0
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
import interface GigabitEthernet1/0/2
import interface virtual-ppp1
#
ip route-static 10.1.0.0 24 virtual-ppp 1
#
acl advanced 3101
rule 0 permit ip source 1.1.1.200 0 destination 10.1.0.200 0
#
pki domain domain1
public-key rsa general name sm2-1
undo crl check enable
#
pki import domain domain1 der ca filename ca.cer
pki import domain domain1 p12 local filename server.pfx
#
pki entity entity1
common-name lac
#
ipsec transform-set tran1
encapsulation-mode tunnel
protocol esp
esp encryption-algorithm sm4-cbc
esp authentication-algorithm sm3
#
ipsec policy map1 10 isakmp
transform-set tran1
security acl 3101
remote-address 192.168.0.1
ike-profile profile1
#
l2tp enable
#
l2tp-group 1 mode lac
lns-ip 1.1.2.2
tunnel name LAC
tunnel authentication
tunnel password simple example
#
ike profile profile1
certificate domain domain1
exchange-mode gm-main
local-identity address 192.168.0.10
match remote identity address 192.168.0.1 255.255.255.0
proposal 10
#
ike proposal 10
authentication-method sm2-de
encryption-algorithm sm4-cbc
authentication-algorithm sm3
#
security-policy ip
rule 0 name localout
action pass
source-zone local
destination-zone untrust
source-ip-host 1.1.2.1
destination-ip-host 1.1.2.2
rule 1 name localin
action pass
source-zone untrust
destination-zone local
source-ip-host 1.1.2.2
destination-ip-host 1.1.2.1
rule 2 name untrust
action pass
source-zone untrust
destination-zone untrust
#
LNS
#
interface Virtual-Template1
ppp authentication-mode pap
remote address 192.168.0.10
ip address 192.168.0.1 255.255.255.0
ipsec apply policy use1
#
interface GigabitEthernet1/0/1
port link-mode route
ip address 1.1.2.2 255.255.255.0
#
interface GigabitEthernet1/0/2
port link-mode route
ip address 10.1.0.1 255.255.255.0
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
import interface Virtual-Template1
#
ip route-static 1.1.1.0 24 192.168.0.10
#
acl advanced 3101
rule 0 permit ip source 10.1.0.200 0 destination 1.1.1.200 0
#
local-user vpdnuser class network
password simple Hello
service-type ppp
#
pki domain domain2
public-key rsa general name sm2-1
undo crl check enable
#
pki import domain domain2 der ca filename ca.cer
pki import domain domain2 p12 local filename server.pfx
#
pki entity entity2
common-name lns
#
ipsec transform-set tran1
encapsulation-mode tunnel
protocol esp
esp encryption-algorithm sm4-cbc
esp authentication-algorithm sm3
#
ipsec policy use1 10 isakmp
transform-set tran1
security acl 3101
remote-address 192.168.0.10
ike-profile profile1
#
l2tp enable
#
l2tp-group 1 mode lns
allow l2tp virtual-template 1 remote LAC
tunnel name LNS
tunnel authentication
tunnel password simple example
#
ike profile profile1
certificate domain domain2
exchange-mode gm-main
local-identity address 192.168.0.1
match remote identity address 192.168.0.10 255.255.255.0
proposal 10
#
ike proposal 10
authentication-method sm2-de
encryption-algorithm sm4-cbc
authentication-algorithm sm3
#
security-policy ip
rule 0 name localout
action pass
source-zone local
destination-zone untrust
source-ip-host 1.1.2.2
destination-ip-host 1.1.2.1
rule 1 name localin
action pass
source-zone untrust
destination-zone local
destination-ip-host 1.1.2.2
rule 2 name trust-untrust
action pass
source-zone trust
source-zone untrust
destination-zone untrust
destination-zone trust
#
domain system
authentication ppp local
#