本举例是在M9000-AI-E8的R9071版本上进行配置和验证的。
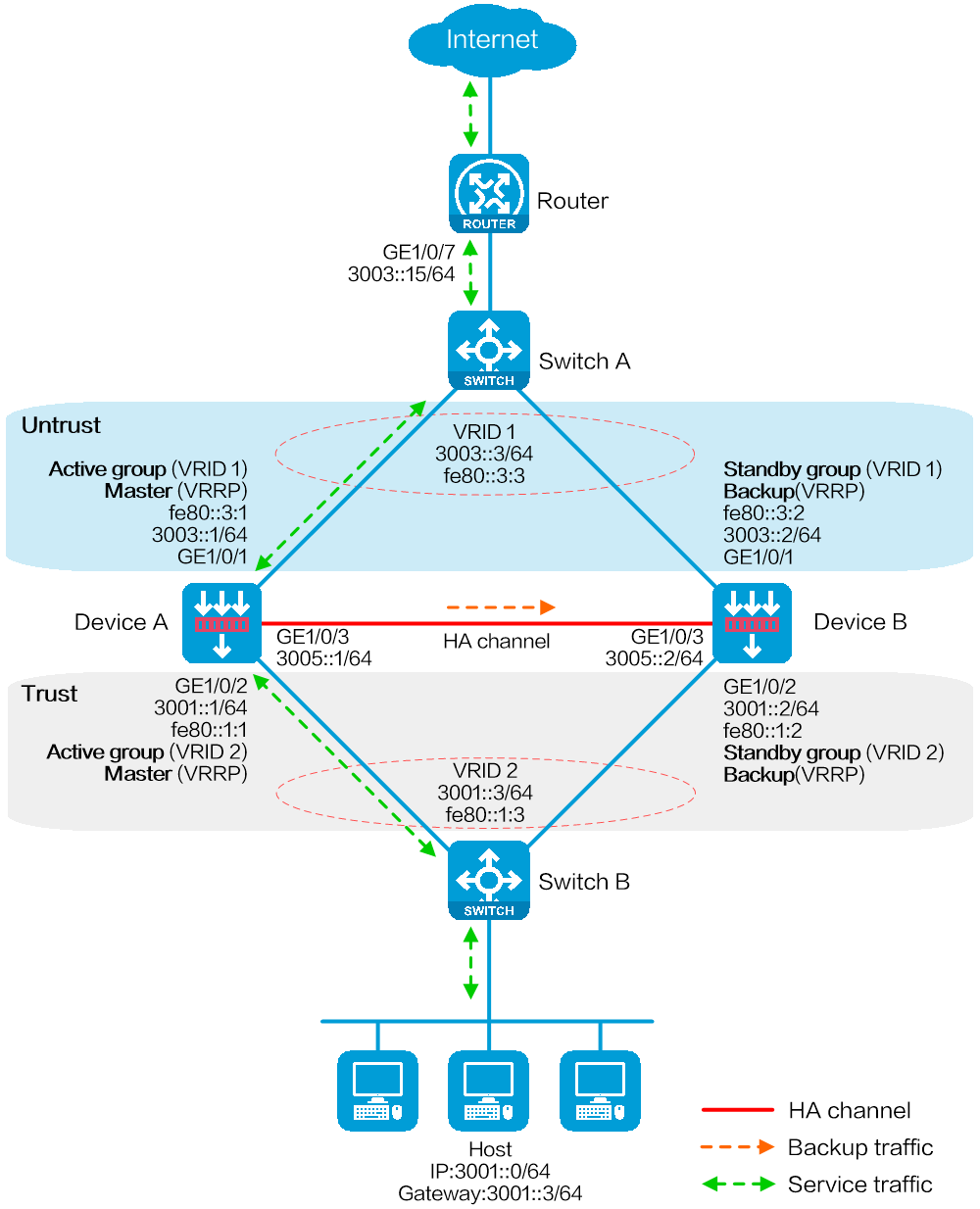
如下图所示,某公司以Device作为网络边界安全防护设备,连接公司内部网络和Internet。为提高业务稳定性,使用两台Device进行HA组网,Device A作为主设备,Device B作为备设备。当Device A或其链路发生故障时,由Device B接替Device A继续工作,保证业务不中断。
图-1 HA联动VRRP三层直连主备组网图(IPv6应用)
仅支持两台设备进行HA组网。
因为一台设备故障时另一台设备需要承担两台设备的流量,所以建议在正常情况下每台设备只负载各自实际能力50%的流量。
部署HA前,请先保证主/备设备硬件环境的一致性,具体要求如下:
主/备设备的型号必须一致。
主/备设备主控板的位置、数量和类型必须一致。
主/备设备业务板的位置、数量和类型必须一致。
主/备设备交换网板的位置、数量和类型必须一致。
主/备设备接口板的位置、数量和类型必须一致。
主/备设备上管理接口、业务接口、HA通道接口需要分别使用相互独立的接口,且所使用的接口编号和类型必须一致。
主/备设备上硬盘的位置、数量和类型建议一致。未安装硬盘的设备日志存储量将远低于安装了硬盘的设备,而且部分日志和报表功能不可用。
部署HA前,请先保证主/备设备软件环境的一致性,具体要求如下:
主/备设备的系统软件环境及其版本必须一致,如:Boot包、System包、Feature包和补丁包等等。
主/备设备上被授权的特征库和特性环境必须一致,如:特征库的种类,每类特征库的版本、授权时间范围、授权的资源数等等。
主/备设备的接口编号必须一致。
主/备设备之间建立HA通道的接口类型、速率和编号等信息必须一致,推荐使用聚合接口。
主/备设备上聚合接口的编号、成员接口编号必须一致。
主/备设备相同位置的接口必须加入到相同的安全域。
主/备设备的HASH选择CPU模式以及HASH因子都必须相同(即forwarding policy命令)。
配置接口IPv6地址
# 根据组网图中规划的信息,配置各接口的IPv6地址,具体配置步骤如下。
<Router> system-view
[Router] interface gigabitethernet 1/0/7
[Router-GigabitEthernet1/0/7] ipv6 address 3003::15/64
[Router-GigabitEthernet1/0/7] quit
请参考以上步骤配置其他接口的IP地址,具体配置步骤略。
配置静态路由,保证网络路由可达
本举例仅以静态路由方式配置路由信息。实际组网中,请根据具体情况选择相应的路由配置方式。
# 请根据组网图中规划的信息,配置静态路由。本举例假设去往内网流量的下一跳IPv6地址为VRRP备份组1的虚拟IPv6地址3003::3/64,去往Internet流量的下一跳IPv6地址为3007::15/64,实际环境中请以具体组网情况为准,具体配置步骤如下。
[Router] ipv6 route-static 3001::3 64 3003::3
[Router] ipv6 route-static 0::0 64 3007::15
在Switch A上创建VLAN 10,并将连接Device A、Device B和Router的接口链路类型设置为Access,并将接口加入VLAN 10。
# 根据组网图中规划的信息,配置各接口加入VLAN,并设置链路类型,具体配置步骤如下。
<SwitchA> system-view
[SwitchA] vlan 10
[SwitchA-vlan10] quit
[SwitchA] interface gigabitethernet 1/0/1
[SwitchA-GigabitEthernet1/0/1] port access vlan 10
[SwitchA-GigabitEthernet1/0/1] quit
[SwitchA] interface gigabitethernet 1/0/2
[SwitchA-GigabitEthernet1/0/2] port access vlan 10
[SwitchA-GigabitEthernet1/0/2] quit
[SwitchA] interface gigabitethernet 1/0/3
[SwitchA-GigabitEthernet1/0/3] port access vlan 10
[SwitchA-GigabitEthernet1/0/3] quit
# 在Switch B上创建VLAN 10,并将连接Device A、Device B和Host的接口设置成工作在二层模式,接口链路类型为Access,并将此接口加入VLAN 10。
# 根据组网图中规划的信息,配置各接口加入VLAN,并设置链路类型,具体配置步骤如下。
<SwitchB> system-view
[SwitchB] vlan 10
[SwitchB-vlan10] quit
[SwitchB] interface gigabitethernet 1/0/1
[SwitchB-GigabitEthernet1/0/1] port access vlan 10
[SwitchB-GigabitEthernet1/0/1] quit
[SwitchB] interface gigabitethernet 1/0/2
[SwitchB-GigabitEthernet1/0/2] port access vlan 10
[SwitchB-GigabitEthernet1/0/2] quit
[SwitchB] interface gigabitethernet 1/0/3
[SwitchB-GigabitEthernet1/0/3] port access vlan 10
[SwitchB-GigabitEthernet1/0/3] quit
配置接口IPv6地址
# 根据组网图中规划的信息,配置各接口的IPv6地址,具体配置步骤如下。
<DeviceA> system-view
[DeviceA] interface gigabitethernet 1/0/1
[DeviceA-GigabitEthernet1/0/1] ipv6 address 3003::1/64
[DeviceA-GigabitEthernet1/0/1] ipv6 address fe80::3:1 link-local
[DeviceA-GigabitEthernet1/0/1] quit
[DeviceA] interface gigabitethernet 1/0/2
[DeviceA-GigabitEthernet1/0/2] ipv6 address 3001::1/64
[DeviceA-GigabitEthernet1/0/2] ipv6 address fe80::1:1 link-local
[DeviceA-GigabitEthernet1/0/2] undo ipv6 nd ra halt
[DeviceA-GigabitEthernet1/0/2] quit
[DeviceA] interface gigabitethernet 1/0/3
[DeviceA-GigabitEthernet1/0/3] ipv6 address 3005::1/64
[DeviceA-GigabitEthernet1/0/3] ipv6 address auto link-local
[DeviceA-GigabitEthernet1/0/3] quit
配置接口加入安全域。
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[DeviceA] security-zone name untrust
[DeviceA-security-zone-Untrust] import interface gigabitethernet 1/0/1
[DeviceA-security-zone-Untrust] quit
[DeviceA] security-zone name trust
[DeviceA-security-zone-Trust] import interface gigabitethernet 1/0/2
[DeviceA-security-zone-Trust] quit
配置静态路由,保证路由可达
本举例仅以静态路由方式配置路由信息。实际组网中,请根据具体情况选择相应的路由配置方式。
# 请根据组网图中规划的信息,配置静态路由使设备与内外网之间路由可达。本举例假设到达外网的下一跳IPv6地址为3003::15,实际环境中请以具体组网情况为准,具体配置步骤如下。
[DeviceA] ipv6 route-static 0::0 0 3003::15
配置安全策略,允许所需的业务报文通过
此部分安全策略只需在主管理设备配置,HA组网完成后,从管理设备会自动同步这些安全策略配置信息。
# 配置名称为trust-untrust的安全策略规则,使10.1.1.0/24网段的内网用户可以主动访问Internet,但是Internet上的用户不能访问内网,具体配置步骤如下。
[DeviceA] security-policy ipv6
[DeviceA-security-policy-ipv6] rule name trust-untrust
[DeviceA-security-policy-ipv6-0-trust-untrust] source-zone trust
[DeviceA-security-policy-ipv6-0-trust-untrust] destination-zone untrust
[DeviceA-security-policy-ipv6-0-trust-untrust] source-ip-subnet 3001::0 64
[DeviceA-security-policy-ipv6-0-trust-untrust] action pass
[DeviceA-security-policy-ipv6-0-trust-untrust] quit
# 配置安全策略规则,允许VRRP协议报文通过。当HA通道断开时,使Device A与Device B之间可以交换VRRP报文,进行VRRP角色竞选,保证网络互通。
[DeviceA-security-policy-ipv6] rule name vrrp1
[DeviceA-security-policy-ipv6-1-vrrp1] source-zone trust
[DeviceA-security-policy-ipv6-1-vrrp1] destination-zone local
[DeviceA-security-policy-ipv6-1-vrrp1] service vrrp
[DeviceA-security-policy-ipv6-1-vrrp1] action pass
[DeviceA-security-policy-ipv6-1-vrrp1] quit
[DeviceA-security-policy-ipv6] rule name vrrp2
[DeviceA-security-policy-ipv6-2-vrrp2] source-zone local
[DeviceA-security-policy-ipv6-2-vrrp2] destination-zone trust
[DeviceA-security-policy-ipv6-2-vrrp2] service vrrp
[DeviceA-security-policy-ipv6-2-vrrp2] action pass
[DeviceA-security-policy-ipv6-2-vrrp2] quit
[DeviceA-security-policy-ipv6] rule name vrrp3
[DeviceA-security-policy-ipv6-3-vrrp3] source-zone untrust
[DeviceA-security-policy-ipv6-3-vrrp3] destination-zone local
[DeviceA-security-policy-ipv6-3-vrrp3] service vrrp
[DeviceA-security-policy-ipv6-3-vrrp3] action pass
[DeviceA-security-policy-ipv6-3-vrrp3] quit
[DeviceA-security-policy-ipv6] rule name vrrp4
[DeviceA-security-policy-ipv6-4-vrrp4] source-zone local
[DeviceA-security-policy-ipv6-4-vrrp4] destination-zone untrust
[DeviceA-security-policy-ipv6-4-vrrp4] service vrrp
[DeviceA-security-policy-ipv6-4-vrrp4] action pass
[DeviceA-security-policy-ipv6-4-vrrp4] quit
[DeviceA-security-policy-ipv6] quit
配置高可靠性
# 使用两台Device进行HA组网,Device A作为主设备,Device B作为备设备。当Device A或其链路发生故障时,由Device B接替Device A继续工作,保证业务不中断。
[DeviceA] remote-backup group
[DeviceA-remote-backup-group] remote-ipv6 3005::2
[DeviceA-remote-backup-group] local-ipv6 3005::1
[DeviceA-remote-backup-group] data-channel interface gigabitethernet 1/0/3
[DeviceA-remote-backup-group] device-role primary
RBM_P[DeviceA-remote-backup-group] undo backup-mode
RBM_P[DeviceA-remote-backup-group] hot-backup enable
RBM_P[DeviceA-remote-backup-group] configuration auto-sync enable
RBM_P[DeviceA-remote-backup-group] configuration sync-check interval 12
RBM_P[DeviceA-remote-backup-group] quit
# 配置VRRP备份组,并与HA关联,实现HA对VRRP备份组的统一管理和流量引导。配置IPv6 VRRP备份组时配置的第一个虚拟IPv6地址必须是链路本地地址。
RBM_P[DeviceA] interface gigabitethernet 1/0/1
RBM_P[DeviceA-GigabitEthernet1/0/1] vrrp ipv6 vrid 1 virtual-ip fe80::3:3 link-local active
RBM_P[DeviceA-GigabitEthernet1/0/1] vrrp ipv6 vrid 1 virtual-ip 3003::3
RBM_P[DeviceA-GigabitEthernet1/0/1] quit
RBM_P[DeviceA] interface gigabitethernet 1/0/2
RBM_P[DeviceA-GigabitEthernet1/0/2] vrrp ipv6 vrid 2 virtual-ip fe80::1:3 link-local active
RBM_P[DeviceA-GigabitEthernet1/0/2] vrrp ipv6 vrid 2 virtual-ip 3001::3
RBM_P[DeviceA-GigabitEthernet1/0/2] quit
配置安全业务
# 以上有关HA的配置部署完成后,可以配置各种安全业务。对于HA支持配置信息备份的功能模块仅需要在此主管理设备上(Device A)进行配置即可。
配置接口IPv6地址
# 根据组网图中规划的信息,配置各接口的IPv6地址,具体配置步骤如下。
<DeviceB> system-view
[DeviceB] interface gigabitethernet 1/0/1
[DeviceB-GigabitEthernet1/0/1] ipv6 address 3003::2/64
[DeviceB-GigabitEthernet1/0/1] ipv6 address fe80::3:2 link-local
[DeviceB-GigabitEthernet1/0/1] quit
[DeviceB] interface gigabitethernet 1/0/2
[DeviceB-GigabitEthernet1/0/2] ipv6 address 3001::2/64
[DeviceB-GigabitEthernet1/0/2] ipv6 address fe80::1:2 link-local
[DeviceB-GigabitEthernet1/0/2] undo ipv6 nd ra halt
[DeviceB-GigabitEthernet1/0/2] quit
[DeviceB] interface gigabitethernet 1/0/3
[DeviceB-GigabitEthernet1/0/3] ipv6 address 3005::2/64
[DeviceB-GigabitEthernet1/0/3] ipv6 address auto link-local
[DeviceB-GigabitEthernet1/0/3] quit
配置接口加入安全域。
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[DeviceB] security-zone name untrust
[DeviceB-security-zone-Untrust] import interface gigabitethernet 1/0/1
[DeviceB-security-zone-Untrust] quit
[DeviceB] security-zone name trust
[DeviceB-security-zone-Trust] import interface gigabitethernet 1/0/2
[DeviceB-security-zone-Trust] quit
配置静态路由,保证路由可达
本举例仅以静态路由方式配置路由信息。实际组网中,请根据具体情况选择相应的路由配置方式。
# 请根据组网图中规划的信息,配置静态路由使设备与内外网之间路由可达。本举例假设到达外网的下一跳IPv6地址为3003::15,实际环境中请以具体组网情况为准,具体配置步骤如下。
[DeviceB] ipv6 route-static 0::0 0 3003::15
配置高可靠性
# 使用两台Device进行HA组网,Device A作为主设备,Device B作为备设备。当Device A或其链路发生故障时,由Device B接替Device A继续工作,保证业务不中断。
[DeviceB] remote-backup group
[DeviceB-remote-backup-group] remote-ipv6 3005::1
[DeviceB-remote-backup-group] local-ipv6 3005::2
[DeviceB-remote-backup-group] data-channel interface gigabitethernet 1/0/3
[DeviceB-remote-backup-group] device-role secondary
RBM_S[DeviceB-remote-backup-group] undo backup-mode
RBM_S[DeviceB-remote-backup-group] hot-backup enable
RBM_S[DeviceB-remote-backup-group] configuration auto-sync enable
RBM_S[DeviceB-remote-backup-group] configuration sync-check interval 12
RBM_S[DeviceB-remote-backup-group] quit
# 配置VRRP备份组,并与HA关联,实现HA对VRRP备份组的统一管理和流量引导。配置IPv6 VRRP备份组时配置的第一个虚拟IPv6地址必须是链路本地地址。
RBM_S[DeviceB] interface gigabitethernet 1/0/1
RBM_S[DeviceB-GigabitEthernet1/0/1] vrrp ipv6 vrid 1 virtual-ip fe80::3:3 link-local standby
RBM_S[DeviceB-GigabitEthernet1/0/1] vrrp ipv6 vrid 1 virtual-ip 3003::3
RBM_S[DeviceB-GigabitEthernet1/0/1] quit
RBM_S[DeviceB] interface gigabitethernet 1/0/2
RBM_S[DeviceB-GigabitEthernet1/0/2] vrrp ipv6 vrid 2 virtual-ip fe80::1:3 link-local standby
RBM_S[DeviceB-GigabitEthernet1/0/2] vrrp ipv6 vrid 2 virtual-ip 3001::3
RBM_S[DeviceB-GigabitEthernet1/0/2] quit
# 配置Host的默认网关为VRRP备份组2的虚拟IPv6地址3001::3。
# 以上配置完成后,通过执行以下显示命令可查看HA配置是否生效,HA通道是否建立。
RBM_P[DeviceA] display remote-backup-group status
Remote backup group information:
Backup mode: Active/standby
Device management role: Primary
Device running status: Active
Data channel interface: GigabitEthernet1/0/3
Local IPv6: 3005::1
Remote IPv6: 3005::2 Destination port: 60064
Control channel status: Connected
Keepalive interval: 1s
Keepalive count: 10
Configuration consistency check interval: 12 hour
Configuration consistency check result: Not Performed
Configuration backup status: Auto sync enabled
Session backup status: Hot backup enabled
Uptime since last switchover: 0 days, 3 hours, 11 minutes
Switchover records:
Time Status change Cause
2021-06-22 13:33:33 Initial to Active Local device rebooted
# 以上配置完成后,通过执行以下显示命令可查看VRRP备份组的状态信息。
RBM_P[DeviceA] display vrrp ipv6
IPv6 Virtual Router Information:
Running mode : Standard
RBM control channel is established
IPv6 VRRP active group status : Master
IPv6 VRRP standby group status: Master
Total number of virtual routers : 2
Interface VRID State Running Adver Auth Virtual
Pri Timer Type IP
---------------------------------------------------------------------
GE1/0/1 1 Master 100 100 None FE80::3:3
GE1/0/2 2 Master 100 100 None FE80::1:3
# 在安全域Trust与Untrust的安全策略上开启安全策略规则匹配统计功能后,当内网Host与Internet之间有流量经过时,Device A上可以看到处理过的流量信息,而Device B上没有。
# 以上配置完成后,通过执行以下显示命令可查看HA配置是否生效,HA通道是否建立。
RBM_S[DeviceB] display remote-backup-group status
Remote backup group information:
Backup mode: Active/standby
Device management role: Secondary
Device running status: Standby
Data channel interface: GigabitEthernet1/0/3
Local IPv6: 3005::2
Remote IPv6: 3005::1 Destination port: 60064
Control channel status: Connected
Keepalive interval: 1s
Keepalive count: 10
Configuration consistency check interval: 12 hour
Configuration consistency check result: Not Performed
Configuration backup status: Auto sync enabled
Session backup status: Hot backup enabled
Uptime since last switchover: 0 days, 3 hours, 11 minutes
Switchover records:
Time Status change Cause
2021-06-22 13:33:33 Initial to Standby Local device rebooted
# 以上配置完成后,通过执行以下显示命令可查看VRRP备份组的状态信息。
RBM_S[DeviceB] display vrrp ipv6
IPv6 Virtual Router Information:
Running mode : Standard
RBM control channel is established
IPv6 VRRP active group status : Backup
IPv6 VRRP standby group status: Backup
Total number of virtual routers : 2
Interface VRID State Running Adver Auth Virtual
Pri Timer Type IP
---------------------------------------------------------------------
GE1/0/1 1 Backup 100 100 None FE80::3:3
GE1/0/2 2 Backup 100 100 None FE80::1:3
# 在安全域Trust与Untrust的安全策略上开启安全策略规则匹配统计功能后,当内网Host与Internet之间有流量经过时,Device A上可以看到处理过的流量信息,而Device B上没有。
Router
#
interface GigabitEthernet1/0/7
port link-mode route
ipv6 address 3003::15/64
#
interface GigabitEthernet1/0/8
port link-mode route
ipv6 address 3007::14/64
#
ipv6 route-static :: 64 3007::15
ipv6 route-static 3001:: 64 3003::3
SwitchA
#
vlan 10
#
interface GigabitEthernet1/0/1
port access vlan 10
#
interface GigabitEthernet1/0/2
port access vlan 10
#
interface GigabitEthernet1/0/3
port access vlan 10
SwitchB
#
vlan 10
#
interface GigabitEthernet1/0/1
port access vlan 10
#
interface GigabitEthernet1/0/2
port access vlan 10
#
interface GigabitEthernet1/0/3
port access vlan 10
DeviceA
#
interface GigabitEthernet1/0/1
port link-mode route
ipv6 address FE80::3:1 link-local
ipv6 address 3003::1/64
vrrp ipv6 vrid 1 virtual-ip FE80::3:3 link-local active
vrrp ipv6 vrid 1 virtual-ip 3003::3
#
interface GigabitEthernet1/0/2
port link-mode route
ipv6 address FE80::1:1 link-local
ipv6 address 3001::1/64
undo ipv6 nd ra halt
vrrp ipv6 vrid 2 virtual-ip FE80::1:3 link-local active
vrrp ipv6 vrid 2 virtual-ip 3001::3
#
interface GigabitEthernet1/0/3
port link-mode route
ipv6 address 3005::1/64
ipv6 address auto link-local
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
ipv6 route-static :: 0 3003::15
#
security-policy ipv6
rule 0 name trust-untrust
action pass
counting enable
source-zone trust
destination-zone untrust
source-ip-subnet 3001::/64
rule 1 name vrrp1
action pass
source-zone trust
destination-zone local
service vrrp
rule 2 name vrrp2
action pass
source-zone local
destination-zone trust
service vrrp
rule 3 name vrrp3
action pass
source-zone untrust
destination-zone local
service vrrp
rule 4 name vrrp4
action pass
source-zone local
destination-zone untrust
service vrrp
#
remote-backup group
data-channel interface GigabitEthernet1/0/3
configuration sync-check interval 12
local-ipv6 3005::1
remote-ipv6 3005::2
device-role primary
DeviceB
#
interface GigabitEthernet1/0/1
port link-mode route
ipv6 address FE80::3:2 link-local
ipv6 address 3003::2/64
vrrp ipv6 vrid 1 virtual-ip FE80::3:3 link-local standby
vrrp ipv6 vrid 1 virtual-ip 3003::3
#
interface GigabitEthernet1/0/2
port link-mode route
ipv6 address FE80::1:2 link-local
ipv6 address 3001::2/64
undo ipv6 nd ra halt
vrrp ipv6 vrid 2 virtual-ip FE80::1:3 link-local standby
vrrp ipv6 vrid 2 virtual-ip 3001::3
#
interface GigabitEthernet1/0/3
port link-mode route
ipv6 address 3005::2/64
ipv6 address auto link-local
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
ipv6 route-static :: 0 3005::15
#
remote-backup group
data-channel interface GigabitEthernet1/0/3
configuration sync-check interval 12
local-ipv6 3005::2
remote-ipv6 3005::1