本举例是在M9000-AI-E8的R9071版本上进行配置和验证的。
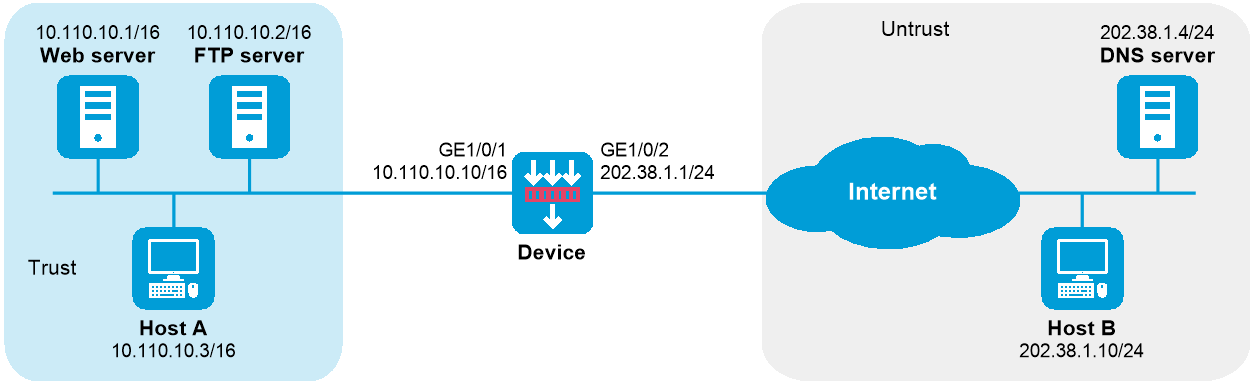
如下图所示,某公司内部对外提供Web和FTP服务。公司内部网址为10.110.0.0/16。其中,Web服务器地址为10.110.10.1/16,FTP服务器地址为10.110.10.2/16。公司具有202.38.1.1至202.38.1.3三个公网IP地址。另外公司在外网有一台DNS服务器,IP地址为202.38.1.4。
需要实现如下功能:
选用202.38.1.2作为公司对外提供服务的IP地址。
外网用户可以通过域名或IP地址访问内部服务器。
内网用户可以通过域名访问内部服务器。
图-1 NAT DNS mapping配置组网图
内网服务器对外提供服务,需要配置NAT内部服务器将各服务器的内网IP地址和端口映射为一个外网地址和端口。
内网主机通过域名访问内网服务器时,首先需要通过出接口地址转换分配的外网地址访问外网的DNS服务器,并获取内网服务器的内网IP地址。由于DNS服务器向内网主机发送的响应报文中包含的是内网服务器的外网地址,因此NAT设备需要将DNS报文载荷内的外网地址转换为内网地址,这可以通过查找DNS mapping映射表配合DNS ALG功能实现。DNS mapping映射表用于实现根据“域名+外网IP地址+外网端口号+协议类型”查找到对应的“内网IP+内网端口号”。
# 配置接口IP地址、路由、安全域及域间策略保证网络可达,具体配置步骤略。
# 开启DNS的NAT ALG功能。
<Device> system-view
[Device] nat alg dns
# 进入接口GigabitEthernet1/0/2。
[Device] interface gigabitethernet 1/0/2
# 配置NAT内部Web服务器,允许外网主机使用地址202.38.1.2访问内网Web服务器。
[Device-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.2 inside 10.110.10.1 http
# 配置NAT内部FTP服务器,允许外网主机使用地址202.38.1.2访问内网FTP服务器。
[Device-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.2 inside 10.110.10.2 ftp
# 在接口GigabitEthernet1/0/2上配置Easy IP方式的出方向动态地址转换。
[Device-GigabitEthernet1/0/2] nat outbound
[Device-GigabitEthernet1/0/2] quit
# 配置两条DNS mapping表项:Web服务器的域名www.example.com对应IP地址202.38.1.2;FTP服务器的域名ftp.example.com对应IP地址202.38.1.2。
[Device] nat dns-map domain www.example.com protocol tcp ip 202.38.1.2 port http
[Device] nat dns-map domain ftp.example.com protocol tcp ip 202.38.1.2 port ftp
# 以上配置完成后,内网主机和外网主机均可以通过域名访问内网服务器。通过查看如下显示信息,可以验证以上配置成功。
[Device] display nat all
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: ---
Address group ID: ---
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
NAT internal server information:
Totally 2 internal servers.
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.2/21
Local IP/port : 10.110.10.2/21
Rule name : ServerRule_2
NAT counting : 0
Config status : Active
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.2/80
Local IP/port : 10.110.10.1/80
Rule name : ServerRule_1
NAT counting : 0
Config status : Active
NAT DNS mapping information:
Totally 2 NAT DNS mappings.
Domain name: ftp.example.com
Global IP : 202.38.1.2
Global port: 21
Protocol : TCP(6)
Config status: Active
Domain name: www.example.com
Global IP : 202.38.1.2
Global port: 80
Protocol : TCP(6)
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Disabled
ICMP-ERROR : Enabled
ILS : Disabled
MGCP : Disabled
NBT : Disabled
PPTP : Enabled
RTSP : Enabled
RSH : Disabled
SCCP : Disabled
SCTP : Disabled
SIP : Disabled
SQLNET : Disabled
TFTP : Disabled
XDMCP : Disabled
Static NAT load balancing: Disabled
NAT link-switch recreate-session: Disabled
NAT configuration-for-new-connection: Disabled
# 通过以下显示命令,可以看到外网主机访问内网Web Server时生成NAT会话信息。
[Device] display nat session verbose
Slot 1:
Initiator:
Source IP/port: 202.38.1.10/63593
Destination IP/port: 202.38.1.2/80
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Source security zone: Untrust
Responder:
Source IP/port: 10.110.10.1/80
Destination IP/port: 202.38.1.10/63593
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
Source security zone: Trust
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: -/-/-
Rule name:
Start time: 2017-05-21 15:09:11 TTL: 11s
Initiator->Responder: 5 packets 1145 bytes
Responder->Initiator: 3 packets 1664 bytes
Total sessions found: 1
#
nat dns-map domain ftp.example.com protocol tcp ip 202.38.1.2 port 21
nat dns-map domain www.example.com protocol tcp ip 202.38.1.2 port 80
#
interface GigabitEthernet1/0/1
ip address 10.110.10.10 255.255.0.0
#
interface GigabitEthernet1/0/2
ip address 202.38.1.1 255.255.255.0
nat outbound
nat server protocol tcp global 202.38.1.2 21 inside 10.110.10.2 21
nat server protocol tcp global 202.38.1.2 80 inside 10.110.10.1 80
#
security-zone name Trust
import interface GigabitEthernet1/0/1
#
security-zone name Untrust
import interface GigabitEthernet1/0/2
#
security-policy ip
rule 0 name trust-untrust
action pass
source-zone trust
destination-zone untrust
rule 1 name untrust-trust
action pass
source-zone untrust
destination-zone trust