本举例是在F1090的R8660P33版本上进行配置和验证的。
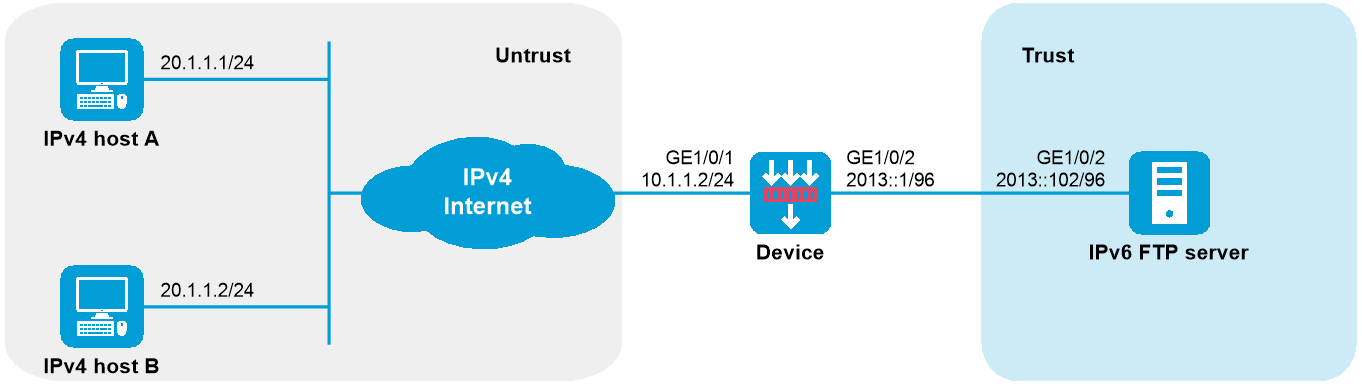
如下图所示,某公司将网络升级到了IPv6,此时Internet仍然是IPv4网络。该公司希望内部的FTP服务器能够继续为IPv4 Internet的用户提供服务。该公司拥有的IPv4地址为10.1.1.1。
为满足上述要求,本例实现方式如下:
使用IPv6侧服务器配置将IPv6内部服务器的地址及端口映射为IPv4地址及端口,Device收到来自IPv4 Internet的报文后,根据该配置策略将报文IPv4目的地址转换为IPv6地址;
使用NAT64前缀将报文源IPv4地址转换为IPv6地址。
图-1 IPv4 Internet访问IPv6网络内部服务器配置组网图
配置接口IP地址
# 根据组网图中规划的信息,配置各接口的IP地址,具体配置步骤如下。
<Device> system-view
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] ip address 10.1.1.2 24
[Device-GigabitEthernet1/0/1] quit
请参考以上步骤配置其他接口的IP地址,具体配置步骤略。
将接口加入安全域
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[Device] security-zone name trust
[Device-security-zone-Trust] import interface gigabitethernet 1/0/2
[Device-security-zone-Trust] quit
[Device] security-zone name untrust
[Device-security-zone-Untrust] import interface gigabitethernet 1/0/1
[Device-security-zone-Untrust] quit
配置安全策略
# 配置名称为aftlocalin的安全策略,使Device能对Host访问Server的报文进行AFT转换,具体配置步骤如下。
[Device] security-policy ip
[Device-security-policy-ip] rule name aftlocalin
[Device-security-policy-ip-1-aftlocalin] source-zone untrust
[Device-security-policy-ip-1-aftlocalin] destination-zone local
[Device-security-policy-ip-1-aftlocalin] destination-ip-host 10.1.1.1
[Device-security-policy-ip-1-aftlocalin] action pass
[Device-security-policy-ip-1-aftlocalin] quit
[Device-security-policy-ip] quit
# 配置名称为aftlocalout的安全策略,允许将AFT转换后的报文转发至Server,具体配置步骤如下。
[Device] security-policy ipv6
[Device-security-policy-ipv6] rule name aftlocalout
[Device-security-policy-ipv6-1-aftlocalout] source-zone local
[Device-security-policy-ipv6-1-aftlocalout] destination-zone trust
[Device-security-policy-ipv6-1-aftlocalout] source-ip-subnet 2012:: 96
[Device-security-policy-ipv6-1-aftlocalout] destination-ip-host 2013::102
[Device-security-policy-ipv6-1-aftlocalout] action pass
[Device-security-policy-ipv6-1-aftlocalout] quit
[Device-security-policy-ipv6] quit
配置AFT功能
# 配置IPv6侧服务器对应的IPv4地址及端口号。IPv4网络内用户通过访问该IPv4地址及端口即可访问IPv6服务器。
[Device] aft v6server protocol tcp 10.1.1.1 21 2013::102 21
# 报文的源地址将根据配置的NAT64前缀转换为IPv6地址。
[Device] aft prefix-nat64 2012:: 96
# 在设备IPv4侧和IPv6侧接口开启AFT。
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] aft enable
[Device-GigabitEthernet1/0/1] quit
[Device] interface gigabitethernet 1/0/2
[Device-GigabitEthernet1/0/2] aft enable
[Device-GigabitEthernet1/0/2] quit
# 以上配置完成后,IPv4 Host可以通过FTP协议访问IPv6 FTP Server。
# 通过查看AFT会话,可以看到创建了一个IPv4会话和IPv6会话,分别对应转换前和转换后的报文。
[Device] display aft session ipv4 verbose
Initiator:
Source IP/port: 20.1.1.1/11025
Destination IP/port: 10.1.1.1/21
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
Source security zone: Untrust
Responder:
Source IP/port: 10.1.1.1/21
Destination IP/port: 20.1.1.1/11025
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Source security zone: Local
State: TCP_ESTABLISHED
Application: FTP
Rule ID: -/-/-
Rule name:
Start time: 2014-03-13 09:07:30 TTL: 3577s
Initiator->Responder: 3 packets 124 bytes
Responder->Initiator: 2 packets 108 bytes
Total sessions found: 1
[Device] display aft session ipv6 verbose
Initiator:
Source IP/port: 2012::1401:0101/1029
Destination IP/port: 2013::102/21
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
Source security zone: Local
Responder:
Source IP/port: 2013::102/21
Destination IP/port: 2012::1401:0101/1029
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Source security zone: Trust
State: TCP_ESTABLISHED
Application: FTP
Rule ID: 0
Rule name: aftlocalout
Start time: 2014-03-13 09:07:30 TTL: 3582s
Initiator->Responder: 3 packets 184 bytes
Responder->Initiator: 2 packets 148 bytes
Total sessions found: 1
#
interface GigabitEthernet1/0/1
ip address 10.1.1.2 255.255.255.0
aft enable
#
interface GigabitEthernet1/0/2
aft enable
ipv6 address 2013::1/96
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
aft prefix-nat64 2012:: 96
aft v6server protocol tcp 10.1.1.1 21 2013::102 21
#
security-policy ip
rule 0 name aftlocalin
action pass
source-zone untrust
destination-zone local
destination-ip-host 10.1.1.1
#
security-policy ipv6
rule 0 name aftlocalout
action pass
source-zone local
destination-zone trust
source-ip-subnet 2012::/96
destination-ip-host 2013::102