The H3C SecPath M9000 series uses a fully distributed hardware architecture and a built-in modularized software system.
 The hardware architecture decouples the key system components to improve system reliability. The MPU, switching fabric modules, service engine, and interface unit have separate hardware, implementing the separation of control, service, and data.
The hardware architecture decouples the key system components to improve system reliability. The MPU, switching fabric modules, service engine, and interface unit have separate hardware, implementing the separation of control, service, and data.
 The hardware switching fabric modules is capable of processing and forwarding security services at a high speed.
The hardware switching fabric modules is capable of processing and forwarding security services at a high speed.
 The high-performance MPU implements unified system configuration management and security cluster.
The high-performance MPU implements unified system configuration management and security cluster.
 The service engine uses an updated multicore processor to provide 40G/100G processing capability for security services. It uses hardware TCAM to ensure high speed searching of a great number of policy entries.
The service engine uses an updated multicore processor to provide 40G/100G processing capability for security services. It uses hardware TCAM to ensure high speed searching of a great number of policy entries.
 The software system supports multi-process scheduling to improve system reliability. Processes are running separately. The failure of a single process does not affect other processes of the system.
The software system supports multi-process scheduling to improve system reliability. Processes are running separately. The failure of a single process does not affect other processes of the system.
 The software system supports privilege management to improve system security. It defines users read and write privileges based on features, command lines, system resources, and Web management levels.
The software system supports privilege management to improve system security. It defines users read and write privileges based on features, command lines, system resources, and Web management levels.
 The software system supports hot patching and ISSU to allow system upgrading without interrupting services, improving system usability. Carrier-level high availability
The software system supports hot patching and ISSU to allow system upgrading without interrupting services, improving system usability. Carrier-level high availability
 Uses H3C highly-available proprietary software and hardware platforms that have been proven by Telecom carriers and medium- to large-sized enterprises.
Uses H3C highly-available proprietary software and hardware platforms that have been proven by Telecom carriers and medium- to large-sized enterprises.
 Supports 1:1 stateful failover: active/active stateful failover for load sharing and active/standby stateful failover for backup.
Supports 1:1 stateful failover: active/active stateful failover for load sharing and active/standby stateful failover for backup.
 Supports N:N stateful failover, providing load sharing and service backup.
Supports N:N stateful failover, providing load sharing and service backup.
 Supports Security Cluster Framework (SCF), including multi-chassis cluster and heterogeneous cluster.
Supports Security Cluster Framework (SCF), including multi-chassis cluster and heterogeneous cluster.
Powerful security protection features
 Attack protection—Detects and prevents various attacks, including Land, Smurf, UDP Snork attack, UDP Chargen DoS attack (Fraggle), large ICMP packet, ping of death, tiny fragment, Tear Drop, IP spoofing, IP fragment, ARP spoofing, reverse ARP lookup, invalid TCP flag, IP/port scanning, and common DDoS attacks such as SYN flood, UDP flood, ICMP flood, DNS flood, and CC.
Attack protection—Detects and prevents various attacks, including Land, Smurf, UDP Snork attack, UDP Chargen DoS attack (Fraggle), large ICMP packet, ping of death, tiny fragment, Tear Drop, IP spoofing, IP fragment, ARP spoofing, reverse ARP lookup, invalid TCP flag, IP/port scanning, and common DDoS attacks such as SYN flood, UDP flood, ICMP flood, DNS flood, and CC.
 Unified management—Manages the host and service modules as a single network element. You do not need to plan IP addresses for each card. This function saves IP addresses, facilitates deployment, and realizes comprehensive configuration management, performance monitoring, and log auditing.
Unified management—Manages the host and service modules as a single network element. You do not need to plan IP addresses for each card. This function saves IP addresses, facilitates deployment, and realizes comprehensive configuration management, performance monitoring, and log auditing.
 IFF—Intelligent Flow Forwarding, which balances traffic on the deployed service engines to implement distributed traffic processing.
IFF—Intelligent Flow Forwarding, which balances traffic on the deployed service engines to implement distributed traffic processing.
 SCF——Supports multi-chassis cluster, which simplifies management and deployment, and implements resilient extensions of security services and security performances. Supports heterogeneous cluster, making the cluster system more flexible. For example, M9006, M9010, and M9014 can form a cluster.
SCF——Supports multi-chassis cluster, which simplifies management and deployment, and implements resilient extensions of security services and security performances. Supports heterogeneous cluster, making the cluster system more flexible. For example, M9006, M9010, and M9014 can form a cluster.
 SOP—Security ONE platform. It implements the virtual firewall function by using the container based virtualization technology.
SOP—Security ONE platform. It implements the virtual firewall function by using the container based virtualization technology.
 SOP implement process-based isolation.
SOP implement process-based isolation.
 SOP can divide static and dynamic system resources at a high level of granularity based on the unified OS kernel.
SOP can divide static and dynamic system resources at a high level of granularity based on the unified OS kernel.
 The number of SOP can be adjusted according to system requirements.
The number of SOP can be adjusted according to system requirements.
 The SOP capabilities can be adjusted according to user requirements.
The SOP capabilities can be adjusted according to user requirements.
 Security zone—Allows you to configure security zones based on interfaces and VLANs.
Security zone—Allows you to configure security zones based on interfaces and VLANs.
 Packet filtering—Allows you to apply standard or advanced ACLs between security zones to filter packets based on information contained in the packets, such as UDP and TCP port numbers. You can also configure time ranges during which packet filtering will be performed.
Packet filtering—Allows you to apply standard or advanced ACLs between security zones to filter packets based on information contained in the packets, such as UDP and TCP port numbers. You can also configure time ranges during which packet filtering will be performed.
 ASPF—Dynamically determines whether to forward or drop a packet by checking its application layer protocol information and state (such as RAWIP, ICMP, ICMPv6, UDP-LITE, SCTP, and other application layer protocols based on TCP/UDP).
ASPF—Dynamically determines whether to forward or drop a packet by checking its application layer protocol information and state (such as RAWIP, ICMP, ICMPv6, UDP-LITE, SCTP, and other application layer protocols based on TCP/UDP).
 AAA—Supports authentication based on RADIUS/HWTACACS+/LDAP(AD), CHAP, and PAP.
AAA—Supports authentication based on RADIUS/HWTACACS+/LDAP(AD), CHAP, and PAP.
 Blacklist—Supports static blacklist and dynamic blacklist.
Blacklist—Supports static blacklist and dynamic blacklist.
 NAT—Supports static NAT, source address NAT, destination address NAT, static CGN NAT, dynamic CGN NAT, and NAT ALG.
NAT—Supports static NAT, source address NAT, destination address NAT, static CGN NAT, dynamic CGN NAT, and NAT ALG.
 P2P traversal—Supports Fullcone and Hairpin.
P2P traversal—Supports Fullcone and Hairpin.
 VPN—Supports L2TP, IPsec/IKE, GRE, and MPLS VPN.
VPN—Supports L2TP, IPsec/IKE, GRE, and MPLS VPN.
 Routing—Supports IPv4 and IPv6 static routing, ECMP routing, policy-based routing, IPv4 routing protocols (such as BGP, RIPv2, OSPF, and ISIS), and IPv6 routing protocols (such as BGP4+, OSPFv3, and ISISv6).
Routing—Supports IPv4 and IPv6 static routing, ECMP routing, policy-based routing, IPv4 routing protocols (such as BGP, RIPv2, OSPF, and ISIS), and IPv6 routing protocols (such as BGP4+, OSPFv3, and ISISv6).
 Multicasting—Supports IGMP v1/v2/v3, PIM-SM, and PIM-DM.
Multicasting—Supports IGMP v1/v2/v3, PIM-SM, and PIM-DM.
 Security logs—Supports operation logs, interzone policy matching logs, attack protection logs, DS-LITE logs, and NAT444 logs.
Security logs—Supports operation logs, interzone policy matching logs, attack protection logs, DS-LITE logs, and NAT444 logs.
 Traffic monitoring, statistics, and management.
Traffic monitoring, statistics, and management.
 Industry-leading protection—ICSA validated security and performance.
Industry-leading protection—ICSA validated security and performance.
Industry-leading IPv6 features
 Basic IPv6 protocols, including TCP6, UDP6, RAWIP6, ICMPV6, PPPoEv6, DHCPV6 Server, DHCPv6 Client, DHCPV6 Relay, DNSv6, and RADIUS6.
Basic IPv6 protocols, including TCP6, UDP6, RAWIP6, ICMPV6, PPPoEv6, DHCPV6 Server, DHCPv6 Client, DHCPV6 Relay, DNSv6, and RADIUS6.
 IPv6 routing protocols, including IPv6 static routing, IPv6 dynamic routing (BGP4+\OSPFv3\ISISV6), policy-based routing, and routing policy.
IPv6 routing protocols, including IPv6 static routing, IPv6 dynamic routing (BGP4+\OSPFv3\ISISV6), policy-based routing, and routing policy.
 IPv6 ASPF.
IPv6 ASPF.
 IPv6 attack protection.
IPv6 attack protection.
 IPv6 multicast.
IPv6 multicast.
 IPv6 transition technologies, including NAT-PT, IPv6 over IPv4 GRE tunnel, manual tunnel, 6to4 tunnel, automatic IPv4-compatible IPv6 tunnel, ISATAP tunnel, NAT444, and DS-Lite.
IPv6 transition technologies, including NAT-PT, IPv6 over IPv4 GRE tunnel, manual tunnel, 6to4 tunnel, automatic IPv4-compatible IPv6 tunnel, ISATAP tunnel, NAT444, and DS-Lite.
Intelligent management
 Support for SNMPv3, which is backward compatible with SNMPv1 and SNMPv2.
Support for SNMPv3, which is backward compatible with SNMPv1 and SNMPv2.
 CLI-based configuration and management.
CLI-based configuration and management.
 Unified management functions provided by the H3C iMC, which can collect and analyze security information, and offer an intuitive view into network and security conditions, saving management efforts and improving management efficiency.
Unified management functions provided by the H3C iMC, which can collect and analyze security information, and offer an intuitive view into network and security conditions, saving management efforts and improving management efficiency.
 Centralized log management functions based on advanced data drill-down and analysis technology. It can request and receive information to generate logs, compile different types of logs (such as syslogs and binary stream logs) in the same format, and compress and store large amounts of logs. You can encrypt and export saved logs to external storage devices such as DAS, NAS, and SAN to avoid loss of important security logs.
Centralized log management functions based on advanced data drill-down and analysis technology. It can request and receive information to generate logs, compile different types of logs (such as syslogs and binary stream logs) in the same format, and compress and store large amounts of logs. You can encrypt and export saved logs to external storage devices such as DAS, NAS, and SAN to avoid loss of important security logs.
 Abundant reports, including application-based reports and stream-based analysis reports.
Abundant reports, including application-based reports and stream-based analysis reports.
 Export of reports in different formats, such as PDF, HTML, word, and txt.
Export of reports in different formats, such as PDF, HTML, word, and txt.
 Report customization through the Web interface. Customizable contents include time range, data source device, generation period, and export format.
Report customization through the Web interface. Customizable contents include time range, data source device, generation period, and export format.
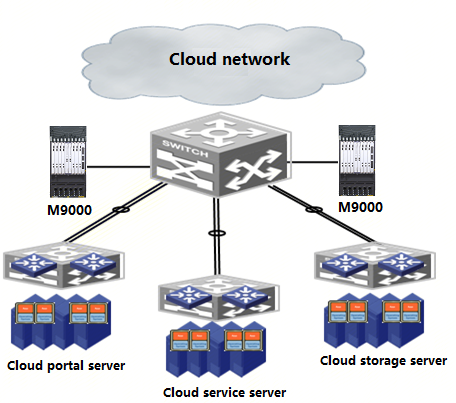
![]() Attack protection, access control, security zone, blacklist, traffic monitoring, mail filtering, webpage filtering, and application layer filtering, which effectively ensure the network security.
Attack protection, access control, security zone, blacklist, traffic monitoring, mail filtering, webpage filtering, and application layer filtering, which effectively ensure the network security.![]() Application Specific Packet Filter (ASPF), which can inspect the connection status and detect exceptional commands.
Application Specific Packet Filter (ASPF), which can inspect the connection status and detect exceptional commands.![]() VPN services, including L2TP VPN, GRE VPN, IPsec VPN, and MPLS VPN.
VPN services, including L2TP VPN, GRE VPN, IPsec VPN, and MPLS VPN. ![]() Carrier Grade NAT services.
Carrier Grade NAT services. ![]() Routing capabilities, including static routing, dynamic routing (RIP/OSPF/BGP/ISIS), policy-based routing, and routing policies.
Routing capabilities, including static routing, dynamic routing (RIP/OSPF/BGP/ISIS), policy-based routing, and routing policies.![]() IPv4 and IPv6 dual stacks.
IPv4 and IPv6 dual stacks.![]() Uses multi-core, fully distributed hardware architecture.
Uses multi-core, fully distributed hardware architecture. ![]() The MPUs provide 1+1 redundancy, unified configuration management for the entire device, and security cluster support. The fan trays provide redundancy. The fan trays support fan status monitoring. The fans support stepless speed regulation, which can automatically adjust the fan speed according to the environment temperature and card configuration.
The MPUs provide 1+1 redundancy, unified configuration management for the entire device, and security cluster support. The fan trays provide redundancy. The fan trays support fan status monitoring. The fans support stepless speed regulation, which can automatically adjust the fan speed according to the environment temperature and card configuration. ![]() The power modules support M+N backup. AC and DC power modules support hot swapping and load sharing. You can configure the power modules according to the system power consumption.
The power modules support M+N backup. AC and DC power modules support hot swapping and load sharing. You can configure the power modules according to the system power consumption. ![]() The service engine and interface units support mix insertion. You can deploy them as needed to meet various performance requirements.
The service engine and interface units support mix insertion. You can deploy them as needed to meet various performance requirements. ![]() All units of the device support hot swapping.
All units of the device support hot swapping.

 Products and Solutions
Products and Solutions